GT - Adversary Intelligence From Conflict to Consensus - Alex Valdeia & Rich Barger
Show transcript [en]
all right guys hey everyone I'm Alex Bolivia I'm on their research team at
for those you guys want to stick with us we yeah sure so we know that there's a stigma with the c-word not not that C word but the other C word so we're going to try to keep those non-existent not even took whoa oh oh gotcha thank you um came to a minimum but you guys can keep us in check keep us honest is there a volume setting up this mike
so you know obviously there's a lot of controversy around absolutely televisions and attribution right it's a really hot complicated it really just because you know a lot of folks will argue oh you know we shouldn't be doing it it's too hard you know we don't have the right authorities you know you can acknowledge that you know that that's probably true in some cases but you know at the end of the day you know it's important that we are able to kind of understand especially technical capabilities in the necessary are and apply some context to what they're trying to accomplish and do it so a lot of folks are like I don't care necessarily to get me you know and that
doesn't necessarily stay on i mean if you're walking down the street if someone just all this up and punched you in the back of the head like you know are you going to just cup your hands over your eyes you go to the helmet store to avoid you head again or are you going to turn around and kind of size up you just knock your lights out and so it's really important this day and age of some kind of thing about we're absolutely telligence fits into the intelligence life cycle and understanding how that applies to conventional threats so just because something isn't his controversial it really that argument doesn't scale especially with some of the threats that
precede play so obviously in our position our subject is that more information spider make better decisions i understand risks a little bit better versus kind of putting your head in the sand and oestrogen just kind of ignoring various aspects of threat I'm only going to focus on the technical analysis like what the instruction does it really does I don't care anything about specific individual or organization smiles reviews TV what you're trying to accomplish and I just just really doesn't apply so lluvia pig's ear so credit back to what we're saying right so there's like look at different threats today it's really important to understate really the loop because it's going to drive drive risk your interview palette in that
perception is also going to drive response to what sort of threat feeling part of your reaction so yeah if excited that doesn't you to you right usually when we approach a decision-maker within the business about an incident or some sort of head you're going to already have some sort of detail the one stop unauthorized activity these were the details just to be how they got in logs and game and using you already developed some sort of needs a picture about what details is that fan art and usually leaders some degree are going to ask good and so this really doesn't give you a problem you know you can't sidestep you know the who question what's their
attack where they out how does the leadership is going to want to know that and that has to kind of reach a process you know continuum of tactical operational elements of you know security ops all the way up to the season so the boss is always going to want to know so as you start to build that picture happening technical to the geopolitical social political is very important so I don't know if you guys like history but Socrates definitely applied research networks usually threat intelligence analysis it's true it's true you can extreme you this completely so so one of the things that we have developed Trek next these implemented one of our order or founders is the
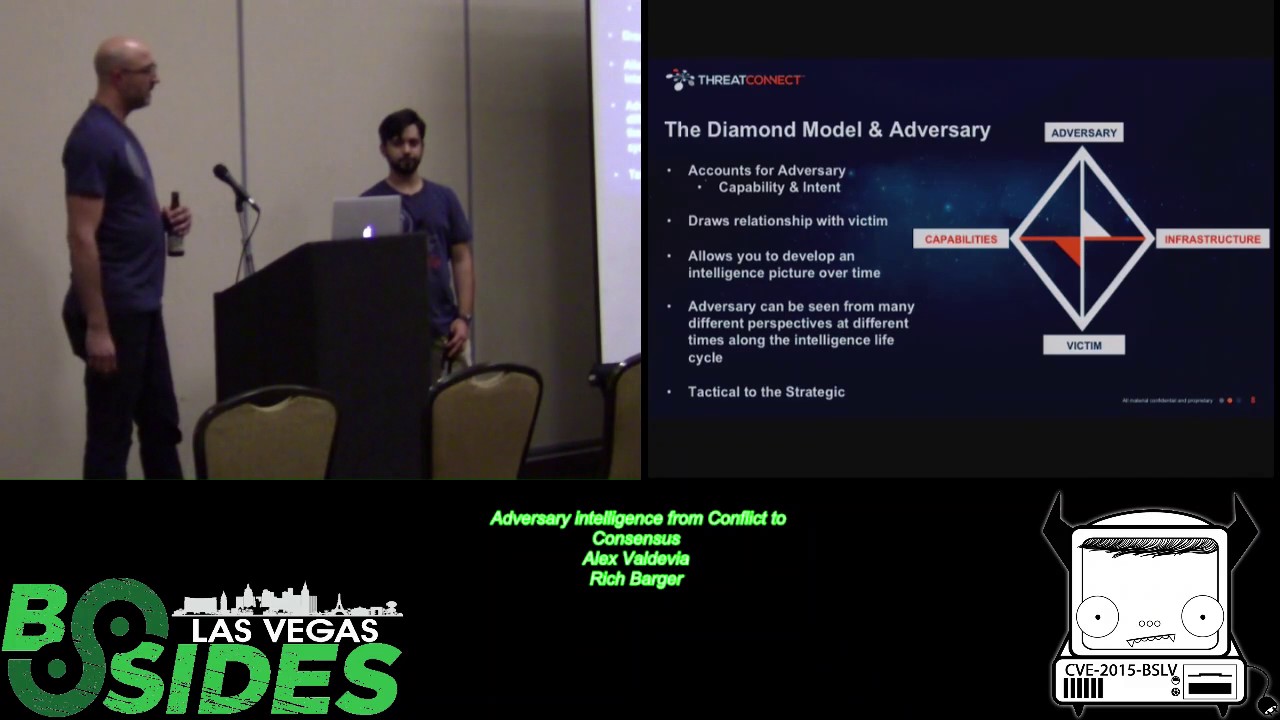
author to to the dog model of truth analysis which is built with way that counts were housed there and as part of that that methodology it's fixed route for understanding what and adversaries capabilities are their intent is behind leveraging the relationship of this technical access between capabilities and infrastructure and so over time once you sit on one of these vertices long enough and you will be able to learn about the other health so you're sitting at the big pond a pic of hop you're going to be able to see what and how Sarah uses in terms of their River shop you're going to be able to monitor certain capabilities they might have upload or download it so has
a magical around us and not wear enough people share information off the same power threat he'll start to build out a picture of that adversary they'll eventually screw up we will talk about that here towards yet so it again maybe perceptions change like you'll have that amazing picture but over time as you develop more confident more information synthesized against this model you can begin to make follow-on positions around and this applies the wolf talk through was like how about some very nascent tactical details ultimately bottle of juice of strategic decision support so yeah right so in case anybody's eyes are glazing over or you know you want to put this in a different context the shirts
we're wearing the backs have this depiction of the diamond model right so tell it to me in Star Wars so you have an adversary in this case it's Luke Skywalker you're looking at it from the perspective of the Empire right so the victim is the Empire capabilities proton torpedoes infrastructure 265 x-wing although the graphic has some more detailed stuff like the force is a capability right and the Luke Skywalker is able to target womp rats right right so I mean we can kind of walk through the different sorts of capabilities that has you know throughout the movie and how he projects those sorts of capabilities against his target in terms of his infrastructure technical but that's all much risk behind the
intent right to destroy the Empire right so there's a socio-political aspect to disruption of seats right so you know we can kind of map the thought of Joker's if the if the victim here view the adversary have a certain tgp he would have responded to that risk of him so stepping back here we just kind of wanted to set the scene right so we go back in two thousand five you know your admin or network security engineer like that you know you seem up you two years worth target after some time you know all the open source information on this essay this risk is low or working on this is a big deal but you know you what
you see inside your enterprise is a little bit different you're seeing like this is the target attacks maybe there's some folks in same vertical are seeing some of the safety GPAs or city capabilities like against you and so this point it's you know what over what do I perceive this start to be but I can really only understand what they do in terms of actions on objective its impact to my organization and so this is kind of that Mason picture so we start to model that within a diamond model and we can start to kind of fill out these little buckets if you will and sort kind of our knowledge so we can see you know
specific sample is you know spearfish do leadership it calls is configured to call back to a certain location we can map that over time we can find overlaps in terms of infrastructure in terms of actions on objective new we have laws that say a this is a password that they use of that has remove see who it is is that something other folks to see the news so as we go around this diamond and there's other folks that have their own time as we confuse you see this lattice or this graph of like diamonds begin to emerge around this threat and so you know go back to like I said this is like 2005 time frame you had who is
protections on this on the zipper structure so within you know you know month later write the story changes a little bit so you know the October time rank who is service falls that's c2 we start to say okay here's some new you know so you've got a points here that we can add to that developing picture we have this reference to the hub saw reference to Shanghai oh by the way this ugly gorilla 163 what's that about right so maybe some of the folks that are in our scene you know circles have said a you know we suspect associated with a specific Chinese et thread or certain espionage we can begin to kind of respond in a way that's
commensurate with that type of fat versus a financially motivator to top her I'd illogical go to the attack and start putting together correct type of response that is going to be the best use of your time talent treasure so um alright so as we begin to kind of flush this out we get a glimpse of an adversary property details right so this gives us even some opportunities using basically open source it like I've highlighted about the times before is that view takes a couple trips around the diamond stuff stuff doesn't come overnight so being able aurealis information over time apply it to a model and understand the relationships between these different data points in scaling across other folks that might
have similar data points isn't perfect so information that we identified back 2005 time frame open source you know an individual claiming obviously task capabilities speak in our read Chinese tonight or you know according to claims to be in a certain region or claims to be in a certain professor profession begins to klein up with what we see ten years later when you see the FBI deliver indictments against this individual and even within the indictment you can see you know certain details about things that apply to us in in the use case and we highlighted earlier with regard to hospitals but we can begin to understand that that haba sary it compasses are encapsulated more than just losing your
body behind keyboard but the benefactor how the information in which they're harder so have a better way to understand that is you know if we map the content from the indictment to some of these tactical details that we developed over time we can see that the state-owned enterprises were holding the benefactors from an organization that had more bodies conducting these activities against victims leveraging what you see in tap that the tactical asset circle tech costs so it's notice such as russell sure takes place like wow right hope your slide with you I'm going to stay away yeah yeah so um you know in this case we have you know kind of the bottom we have our ops in our
Intel right that both folks both organizations are playing off of another can enable security operations or the stock to the c-suite hopefully hey but there's perceptions of risk right so the malware analyst is going to look at a sample of malware completely different then assist so it's going to have completely different meetings between the two types of Kennedy's just because of where they sit and what they perceive to be rich so it's also important to as we go from like top-down is that decisions that obviously emmc sweet makes is going to impact how the rest of the folks the chain of the operational tactical levels we have to you nor merger acquisition you know what are the
sorts of operational changes so that they're going to have to make ultimately order some of the tactical implementations there were to see and enterprise the liver is supportive carrying out that business operation small so so kind of a way to kind of understand it with newer content would be on going back to the daytime ring with the Robert is right so this second use case it's a great example of that idea of perception right and how it affects how your organization or how a security organization would react to a threat in early May Robert ich the self destructing her kamikaze malware was sensational eyes by the media we had headlines like this terrifying malware destroys your PC you've detected right a
deadly virus suicide bomber so this was a sample somebody analyzed it and then the media took the information and disseminated like the most sort of worst-case scenario and this was a widespread message right and certainly it was received and reacted you know people reacted to it in a way that affected their decisions you know stop stop what you're doing let's focus on this is was that the right decision and you know what could have been done to help shave those perceptions so that someone could have known that hey I'm not going to invest my time people focusing on battery so we're gonna kind of walk right so we are our research team happened to look at this blog post
and the right up and it was a it was a great write-up about the technical capabilities of this malware writer of this sample that was caught our friends at tell us and they were able to identify a capability they were able to identify infrastructure that was tied to it right so this malware was calling out to this domain Santoso zorb Dutton so yeah spot on the interpretation of how the capability knew the capability of being so we'll we'll kind of explore that a little right right so it kind of left this gap of who the adversary is or what the intent might be and we wanted to answer that question right glad I make some
connections on that so we took a closer look at that domain name which was registered to the email address Jen host k at disposable calm if anyone is familiar with disposable it's a free email service that has no password right so all you need to know about a disposable account is the email address itself and then you can go into the inbox and there is all the mail right step 3 so one of the emails in this account happened to be addressed to not only the email address that the adversary was using for his see to infrastructure but also to what looked like a personal email address Callie sky at yahoo com so that stuck out right one
investigate that yeah we also started like a nerd that this is just kind of one example robot but I mean we can even kind of double check through also someone paddle with midst of this content registered computer structure it just also happen to be levers within Zeus Zeus samples so it was consistent with other things that were keeping her prime where I actually motivated threat and they're working distances do this within the data aggregate right so the email address led to cali sky right just google cali sky and we found a treasure trove of information we had a facebook account we had a twitter account we had a linkedin account the best of all we
had a youtube account with a lot a lot of videos and tutorials on some of these tools that kelly sky was using so just somebody share its individual especially responsible for this capability it was really poor in terms of their operational security like they've just really didn't care were really good evening ladies and so it wasn't now to stay the sort of thing comes to overnight but it's not as hard as a lot of those and once you've seen this level of information didn't really help you understand what a level of resistance play that in 12 area all right let's end though I do a pull each other than it stops everything to the service let's try that one more time I
know it was on that sorry ladies and gentlemen that's pretty soft my name is chaya d AKA Kanishka the internet was intense and I do a bunch of until it stops alright so did it song it's very soft but in case you can hear it he says hello ladies and gentlemen my name is coyote ecouter a cali sky the internet consultant i do a bunch of internet stuffs right um yeah this is the guy we're dealing with right so what is some of the internet stuffs that coyotes talking about logging in to your personal Facebook account while recording a Zeus botnet tutorial and then posting it to YouTube this was actually a video that we found on his
account on his YouTube account and he's going through this tutorial on how to use criminal software and he just switches tabs over to his facebook account and there's his picture and there's his real name and there's all his connections for OPSEC to say the least another internet stuff that kelly sky is a capable of is exposing his passwords and it you know from his browser history during his tutorials he just clicks on it they all drop down right and he reuses passwords that's for sure so I mean so basically we started to kind of develop a picture of how the ability you don't have a super positive person starting to get yours you can have this area that was potentially
leveraging that infrastructure and so we started to see it in congruence with Lou was essentially responsible for a zipper trucker and the capability that we saw so just really did it it's like so as we started to look at an hour again visit it wasn't all about conscience what what I was put out was technically correct it wasn't that our world nation comic panels that was looking at involved in the case of an operator tribal review two different origin so that capability wasn't delivered to austin to the enterprise and who's delivered yes to cybercrime know where there's no honor among teens because of that was key was missing money and we could figure out outputs
hug how many recently announced how much wasted time not even spent focusing on the wrong day did it development have certain robot that find out yeah well we have drinks in our hands right in like with this will email you guys later yeah so I mean it's obviously like I said is controversy online people say should I don't have time do it sometime we disagree and so I just wanted to kind of throw it out there I'm sure in some cases have you doesn't want properly she was like you should never be your starting should be definitely really leveraging your own internal occasion this is more of something that we have line it support hub so Jesus is not
evidence mind such a task is carrying the paddle haast pass rusher revisiting it over time as we see this example dignity one that had monetary her data over and over and over as things change I met new contacts so they said a one's got me a question makes her yeah it's a you know obviously certain certain countries obviously grown seat happy as necessary dissipated same statement very hostile right I don't really went away and drag-drop new hobbies Lee it goes back trying to do something to be a bizarre hurt somebody or feel something at the end of the day is almost you know days of pavement right here going throws it enters this is really kind of medium
to marry office so you know I fear it makes sense updated left you don't fill your blessing so there's absolutely there was no need to login anything everything was publicly available he was hard you know that was what they know and he certainly didn't see what he was doing has probably illegal I mean he's probably very hard up a password to that top tonight on the same opportunities are here so you getting all sorts of London kind of social that is and today as a security practitioner he have and his likeness doing sorts of things you need to be kind of ready to feed least have some processes about really reader that look really sorts of mistakes as they're
there it's just how i know i mean it's called up there you know this is probably the best thing you did like yeah an eclipse great man yeah it's like i said there's all sorts of opportunities to see marking word and it has a long memory and so as practitioners is really good leverage that long memory
corso this is a one-of-a-kind shirt there are no other shirts or no other shirts like this you know thanks for the question Oh one morning yo yo yo what shirts that's cheating it really depends on who you are like I mean is is your leadership does that sort of thing you really that's up here you probably have a corona process really yep that's that has evos no no patent but if you're you know they look large you know even Resources Agency that all you care about are you know making sure the networks are often records are working mailable you probably aren't as understanding those sorts of flips the risk is light specific any physical not really the
wrong reason wait so um yeah and just its mortal mind set this isn't stuff and you compile shop it's really adopting mindset that yes there is answers will know how I could attend intended the investment on fire control but I get money bro I'm not really no threat to politician so it's really culturally about accepting that you know the addition case and looking through by that contact to your three hours
alright thanks a lot for coming out [Applause]





