The Need for Application Security

Show original YouTube description
Show transcript [en]
nearly 10 o'clock we're about to get going um sean is pretty standard guy a pretty cool guy in the industry he's done some amazing work and um have i seen your slides i think i think i may have no i didn't actually i didn't manage to actually grab those um but honestly sean runs like streams all the time like the box streams and like the box kind of like hack it like i guess community hacks i guess and it's just really really cool to join in those sit there with him watch him struggle over things but struggle with everybody else and go do you know what i'm not giving up in this where i would
have just went no too much screw that i'm not doing it going yeah awesome uh well we're sorry with that it is ten o'clock so let's introduce y'all i just did a great job of doing so sean are you there my friend um thank you for having me awesome the floor is yours awesome let me get my screenshot going um awesome so i'm hoping that is sharing um great well thank you for having me i'm really excited to be here um this is an awesome event some amazing talks through yesterday and some excellent talks lined up today so i encourage everyone to get so viewing the talks that are coming out um so with that
let me get on with my talk um so a little bit about myself um as if you watched yesterday you probably know that i'm part of the beer farmers the performers for those who don't know is a collection of just a bunch of people um interested in infosec we want to try and jack some humor and get like serious messages across but in a a more humorous manner um sometimes emphasis can be a bit too serious so trying to break down barriers through humor and get that across um i'm also a co-leader of the scotland chapter been doing that for a few years our wasp is an amazing community um and charity there's some amazing
stuff coming out of it not just from the events being run by it but also some of the tuning that's coming out of it so if you don't know us i highly encourage you to to at least look it up um you can't mention application security without mentioning os as you'll see later [Music] i'm also a work at immersive labs i'm responsible for running out our application security offering and that will be coming very shortly um i'm really excited about it some excellent stuff going on there and then finally uh that's myself on twitter true not sick so if you want to follow me mute me block me whatever um there it is there also shout out to hacks shax who came up
with that logo um he's done some amazing logos for those within the community all right so i went to the the content of the talk today um vulnerabilities are for a kind of a cornerstone of application security um the real premise of application security is making sure that you prevent vulnerabilities in your system detect them and fix them and i found this on wikipedia and i think it's a very true reflection of the vulnerability the area that i like the most is the hostile environment if you think about it most applications are internet facing and internet facing is predominantly where most of your attacks are going to come from so that's the hostile environment um
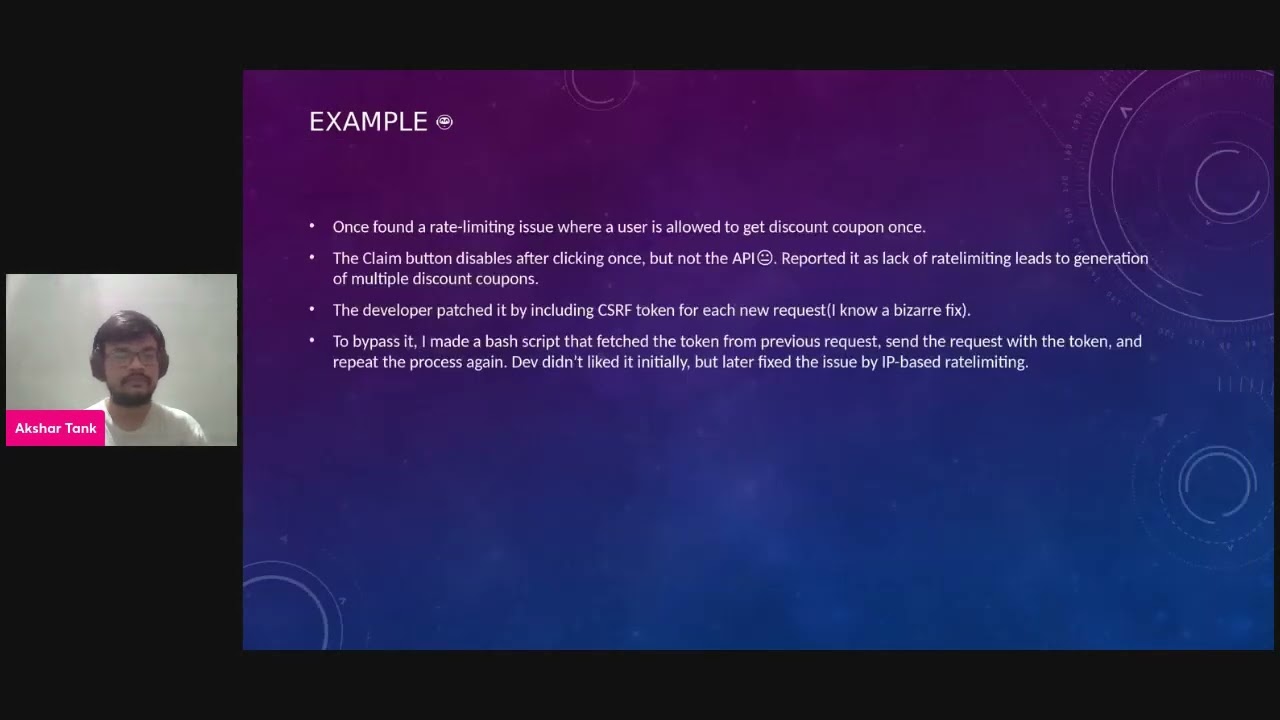
but narrowing it down and just taking it down to a simplest form vulnerabilities really are just a special form of a software bug it's some sort of flaw in the system that's been unaccounted for um and that's leveraged to gain um other access or leak data and that so when you take a step back and look at vulnerabilities themselves um there's different types of vulnerabilities so they in my view fall into two categories the software and the known software vulnerabilities and the non-software vulnerabilities can be things like hardware vulnerabilities so we saw a few few years ago spectre and meltdown there's new sort of research going on and publications around different types of hardware type attacks that you can do
i'm not a hardware guru i think giles is doing a workshop later so i thoroughly uh highly encourage you to uh um attend that if you are interested in that sort of thing um start vulnerability so this is more around like physical top um access and all that kind of thing and then your employees humans or personnel um but if you go look at things like cve um most of the vulnerabilities you'll find there are software-based and i did put a poll out on twitter on this quite some a few days ago and i was actually quite surprised by the the results it was almost 50 50 but a bit more edge towards saying that most vulnerabilities aren't
software-based um i think it's important to call out the vulnerabilities of the floor it's not things being exploited so there are things like misconfigurations and that and that's i don't really view that as a vulnerability i view that as just something maybe if you're going to call it vulnerability maybe human vulnerability but it's a human error not an error in the actual software so having said that obviously software forms a very large part of the vulnerabilities and that's why you need application security so thanks for attending the end no it's obviously not as simple as that so first we look okay if you who are going to blame for all these software areas like there's so many
software errors out there who we're going to blame and no it's not about blaming we need to start looking at why there's so many of these vulnerabilities out there and what we can do to help and help those who are introducing these vulnerabilities or not detecting them so one thing that's been grabbing me for quite some time is if you go look at some of the degrees or training courses and that you do um there there's very little embedded in terms of security so what this is here is a redacted transcript of my university degree and what i try to do is highlight the subjects that had some relation to infosec um so what i had in terms of my degree
is a bachelor of science and then i did a postgrad a fourth year bachelor of science honors in computer science and the thing that really grasped me is we had to do mandatory maths we had i had choices of different subjects such as economics um information securities sorry information systems technology that small business side and in reality those are very um kind of niche things um personally i've never really had to use any of the mathematics i was joking yesterday saying hey okay well we're gonna design this web page let's get together and start forming our logarithm for this new page that we're designing no what i would like to see is let's start taking some of that out that's not
necessary if you're going to go down the mass route you want to do things like cryptography cryptography and all that kind of thing then sure make it an option but don't make it mandatory instead put things that are going to matter like information security so there are three courses they highlighted the first one i did in second year was in from information security and operations research that touched on cryptography nothing on actual raw application security and then in my only in my honors i did um cryptography and network security that was more focused around network security not much around application security and cryptography again cryptography focused on encryption side of things but learning really the mathematics behind it
it is helpful but for a real world real day-to-day job it's questionable whether it is actually beneficial over something else so what i've done here is i've taken the current os top 10 and i've uh sorry this was i was top 10 from 2003 um and i took this and tried to relate it to those courses that i was doing um and seeing out of those courses which ones would have helped me prevent these sort of issues so in my computer science uh course three years standard bachelor of science degree the only thing that was really covered was improper error handling and this wasn't and i highlighted in um orange or yellow here because it wasn't
really focused on the security aspect but more the usability aspect so while that obviously does help in cases where there's improper error handling and you're handling errors there was never a focus on you need to do this because of security it's what was more about you need to do this for usability and then going on to the the fourth year um again because i did that natural course i did cover a bit more but again it wasn't focused a lot on um application security so we did cover buffer overflows um so i kind of granted that one that we covered that off um improper error handling insecure storage so and so forth vaguely never really focused on application
security in fact we were only learning about things like html and xml in fourth year owners now i have to say this was a good few years ago so i don't know what the university curriculum looks like today as far as i know it hasn't changed much i could be entirely wrong but there's also security focused courses or degrees which i will call out so there is that but if you're doing a stock standard bachelor science um degree um this is where it matters you're getting people who are doing this bachelor of science degrees going straight into a job and have never known anything about securing an application the vulnerabilities that they can introduce and this becomes important because
if you look at it we we're now in an era where there's so many technologies been thrown at you there's no new technologies all the time um and trying to keep up with this is just really really difficult um and it's something that i've really battled with myself um there's these new shiny things uh graphql mongodb i'm probably showing my age but they're all things that i've had to learn on the fly and getting up to speed and unless you know the ins and outs of them often you're not going to be able to prevent security issues and prevent security vulnerabilities things like configurations and and so on and so forth and this kind of goes on to a point of
a lack of understanding and knowledge so i've seen this so many times um certificates are really like this mythical beast um really complicated and all that until you start breaking it down and really understanding it but i've dealt with this i've been in the scenario where's oh you have to create a csr and then you have to send it to the the ca and watch the ca or you have to import into a key store and then you have to get the private key and it's like all mambo jumbo um you have no clue what's going on and you just want to get it to work and then once you've put it in then you
start getting all these errors like the certificate's not trusted because you're using a internal ca or something like that um you put in the error you go on stack overflow and you get an answer like this now granted at the bottom it says for testing purposes only but how many people actually will read that i know personally myself i may or may not read that i'm normally just looking for the answer that's gonna solve what i need to get accomplished and that's to get the system working no longer have the error and what is shown there is that that piece of code is telling the system to trust any certificate obviously this is the problem because
um this will allow things like men in the middle attacks and this gets copied um i've seen it systems where someone's done something like this and like fix it like yeah yeah uh this is how you fix this error and they'll give it to the um teammates or someone else who asked the question and next thing you know you got about five or six systems with uh this code in it and it's not their fault they just don't understand it they don't understand the repercussions of that and this happens time and time again so we see scenarios um i remember doing some courses on application security and they were pointing out some flaws within example code
in some training material now you could question whether that's a responsibility on the trainer to make sure that they fix those things but it also comes back to the point like you can't moan at someone about sql injection if they don't know that it exists so we we have to start addressing this um and by tackling that as you'll see later we can hopefully help reduce these issues i just saw in the previous slide incorrect solutions from forums this is a really common one even incorrect solutions from existing code or libraries developers rightly so when you reuse code really use solutions and that's awesome but it can also be a problem um if that if there's a flaw in that
they'll just take the floor and multiply it another problem and i've been down this road is you can't fix the problem you want to fix the problem there's a problem you've identified it you and then you try to get by and to fix it and it's no we don't have time or we don't have resources or it's not a priority once in a company that i was working at i found a floor um well there was a vulnerability out that essentially killed any linux system as soon as you ran this the denial service for exploits the entire system froze you could only restart the system by doing a hard reset in other words going to the system
pushing the power button on and off yeah anna was a local exploit so you had to run it locally on the box doesn't sound bad but i injected it into the scripts that these point of sale terminals used to pull down their software so every time they restarted they pulled down their software injected the script into that script so it pulled down the software and then ran this exploit so what would happen is every time the terminal restarted it run this exports and the terminal will just hang you do that to every single terminal in a retail company what happens that retail company cannot trade and the answer i got was yeah should i go to the shoulders
so yeah we need to change that so xss and sql injection these are definitely not new things we are still battling the same issues even in 2020. um xss i've been reviewing some of the cbes lately and it's still very prevalent in there um sql injection are kind of highlighted in orange it is still an issue today but it's becoming less and less of an issue i don't think it's becoming as a mess of an issue because people are getting better at fixing it i think it's becoming less and less of an issue because less people are using uh traditional databases a lot of things are moving things to like or no moving thing to technologies like nosql
um so things like mongodb elasticsearch and that kind of thing i think that's why that's no longer as big as it was but it's still an issue and these things are old in terms of age f sql injection xss were a human they would be old enough to drive and old enough to drink
and this so as i mentioned you've probably already seen the 2003 um os top 10 and when i was uh comparing my university degree to what was being solved but i thought i'd compare this with the 2017 one this is the 2017 is the current list so for those who don't know os top 10 is a a list of the top 10 vulnerability types or causes of vulnerabilities in software and this is produced by os they do it on a periodic basis um the last one was in 2017 i think 2003 was the first one or um i could be wrong um and i think the next one they're planning is next year so it's a periodic review of the common
causes of security vulnerabilities in software and the thing that struck me is half of the list from 2013 oh sorry 2003 still remains today so we're still facing the same issues so what people are going on about zero days and all that kind of thing the reality is that we are still tackling the same issues that we have known about for decades um i think crosstalk scripting and sql injection were around in the late 90s so 98 in that so they're 20 years old now two decades old and yet they're still so prevalent today so switching gears a little bit and also covering um where development is and where sorry where development was and where
it's going um so if you take a step back and look where development has come from traditionally in the past we used to develop things from the ground up everything was pretty much everything if not everything was developed in-house at the organization and all the building blocks and all of that were built from the ground up and you have your system also deployments or releases were done in big monolithic chunks and that's important from a security point of view because yes while it is a lot more work to review a big massive release you had periodic points in time where you could do that you could allocate resources like say okay great our abstract team is going to spend a
month on pen testing release xyz fast forward to today things have changed we're no longer developing things from the ground up we're taking chunks from outside the organization and i'd like to think of them as building blocks um to different libraries uh different frameworks and using that to develop a system so systems are no longer like bulbs they are rather maybe glued together and then in terms of releases there's no longer these big monolithic releases it's the constant stream of release so you're talking about probably a weekly maybe even daily release cycle whereas in the past you maybe have a quarterly release cycle this makes it tremendously difficult from a security point of view because you can't you'll have to have
someone pan testing 24 7 in order to validate and check everything everything that's going out the window and that's just not going to scale also it's always someone else's thing so cloud computing at someone else's computer or open source i've mentioned open source libraries or frameworks it's someone else's code and i did mention this in the token steel coin if you think about it an open source library or the framework or whatever is literally someone coding some code in your system if you take it and i did ask the question would you allow anyone to code take anyone off the street and code something on your system and most people say no but that's what we're essentially doing
when we're taking these open source libraries now some of them we can trust but there are times where there are these libraries that are by an author that we don't know about thankfully most by far are doing a legitimate um job and uh have legitimate aims of releasing their open source code but there are um cases where that's not quite the case so this is an area i i'm really passionate about and i think it's going to become a big target area for attackers and then lastly we're also doing on someone else's system and software so sas based solutions all your data results somewhere else and and you just kind of hook into that now that's not saying this is all bad i
mean there's good and bad things to come from this so like sas is great i cannot just offload all this work to someone else and get them to do it or offload some of the responsibility especially things like um performance and uptime and availability all that kind of thing but it can also be a problem when it comes to security now who owns that data what happens if you do everything right and they don't do things right um you also don't at times have visibility into what they're doing you have to place a lot of trust in them and yes there are contracts on that but i hate using contracts as a means of security
it's all very well saying yes to the contract but it's always after the fact when they get breached your customers don't care that you sign the contract saying that the vendor must do x y and z the customer is only going to care that your their data was breached so funny it was covering the kind of problems that we're or the changes that we are facing the need for speed um things are moving faster and faster and faster as i kind of touched on this with the constant release cycles and the constant stream businesses are getting more and more competitive and in order to stay competitive and get above the competitor they're going to have to move faster and
release things quicker they're going to have to innovate faster and that's all great but at times that can have a serious risk in terms of security so what is actually what is application security um there's often a misconception that application security is just focused on the code and that's not application security is a whole process and last cycle so if you look at a very basic high level view of a life cycle of application you have your design and planning hopefully um then the development happens so that's where the coding bit comes building it then you test it make sure everything's working and then you finally release it and that's going to involve different people at different stages so
you're going to hopefully have some architects providing input into the design um planning so you have your product as well um you'll probably have some maybe some developers or lead developers um trying to morph what it is they're trying to build or develop then you ain't actually have the coders or developers um develop the system your qa um test it and validate everything's working and meets the requirements and then finally like your operations uh deploy it um maintain that's in a production environment touching on this this it was very solid in the past maybe in the past your developers and qas would work closely together but your operations team was kind of separate there's a model called the
squad model um and that's a self-contained unit where there is no operations team and qa team and the team is the squad and that consists of everyone that's responsible for that entire life cycle of the application guess what you're going to have to include security in there somewhere and that's why you're going gonna have to start enabling people so i think it's also important to take a step back and look at who we are actually protecting our applications from so in the past the way i traditionally look at um the threats where things like those inquisitive so much like a cats trying to figure out what the lizard's doing was people if you go back to real
hacking it was just people trying to figure out how things work what happened if i change this how does it react that's what i view hacking like the traditional hacking way is um there's also pranks done in a way to play pranks on one another or organizations there wasn't really a malicious intent behind it um and then like foreign freaking and that kind of stuff yeah you could argue there was some financial impact in that but then the reality is is more about being inquisitive finally now things are working maybe doing one over the big corporate person or whatever but there wasn't much in terms of financial gain and all that kind of thing but you go to today and that's
completely changed so you've got things like organized chrome um that is obviously massive it i don't know the figures but it's multi billions um and that's a large driving force in the criminal activity that we face today we have hacktivism so we have things like anonymous and then we have nation states i'm not going to mention any nation states but those are kind of countries competing against one another finding things about maybe cyber warfare is starting to pick up but maybe intelligence about other countries and that kind of thing so let's look at the the threat actors that have formed parts of these they they're all you know they're the guys that sit with the balakov in front of the computer
or hoodie or that right like this guy right no so often threat actors are typical human beings like me and you um and at times they're even kids go look at the recent twitter hack it wasn't some guy no hoodie and all that so nation states and massive threat actors they're basically kids okay maybe not kids but they're in the 20s and that's um and i think some even younger the point being is um this whole stereotypical thing that some advanced people on that it you're more likely to be targets by a kid than some really advanced person typical um companies one thing i love to do is give some real world context behind it
some of the things i'm talking about so f5 now f5 for those who don't know i'm so much would know but those who don't know f5 is a security firm that will focus around more network peripherals like things like web application and last year there was a vulnerability in their tmur management interface and this allowed um remote code execution on a their fr firewall and this was important because that device by its very nature is trying to prevent attack is coming in so it's going to be sitting on the external interface of whatever you're protecting i.e the internet over time we've seen companies been a bit sluggish in terms of patching things this has now been actively uh exploited
um to uh use the mirror botnet to to target these um this here is the baby camera monitor and i actually have this in my house and when i found this vulnerability i never heard the end of it because i said oh it's cool shiny toy let me buy it and my other horse says no we that i don't trust that russian butt and get low and behold i never heard the end of it when i did find vulnerabilities in it but what was actually found in this was uh i had uh i think at the time alien volts that was doing scans and i noticed some directory traversal and i thought hmm that's curious wonder
what this is and i led me down this whole rabbit hole from that single directory traversal i found that i was able to get the wifi credentials so the the ssid as well as the passphrase for that wireless network i could control the camera i could view the video feed so control the camera view the video field all without authentication i just had to be on the same network i could upload firmware again unauthenticated just have to be on the same network um and okay this is on a private network most will be on a private network but some of these um some people put these wide open on the internet and the most shocking of all
is when i was doing my write-up on this i decided to just google it and lo and behold all the stuff was found years prior i think it was like two or three years prior to when i found it and nothing was fixed even though they said they would fix it and this goes kind of related because that is iit so iit is software still it has software running on it so in that case of that baby monitor it had things like a web server with cgi scripts and that kind of thing running in it so it's still software and we see it time and time again this iot device has this vulnerability etc etc so at the moment
i think iot in terms of software security is in a really bad way also updates how do you get updates to some of these devices it's sure if it's internet connected it's a lot easier but what about devices that aren't always connected to the internet so uh another example british airways um between august and september and 2018 um mage courts attacked this corporation um and mage card is a criminal group so that's going to that organized chrome um that install uh virtual card skimmers or web skimmers i think that's the correct term um and what what the attempts to do is it's still uh payment information so credit card details when you enter it online to pay
for your flags and they manage this by modifying a javascript library now it's not clear whether this was like open source or where it was but it doesn't really matter they've attacked the javascript library that was running on the british airways website the most frustrating part about this is this could have been prevented by a existing control called content security policy and that i've kind of viewed like a firewall to a web application it defines the browser what resources can load on that page so there's an existing control that wouldn't have cost the company any money to implement other than human time and resources they are now facing a fine of around 183 million pounds because of gdpr um in the
past would probably be a maximum at which was 500 000 because of gdpr that suddenly ramped up to 183 it's a potential fund it's was issue with intent to find we still have to see if that's going to actually happen and incidentally that amount equates to a 747 800. so i lost a 747 potentially my favorite example and i never get tired of or using this as an example not because i hate equifax and all that kind of thing i think this example just illustrates why applications security is so important and how things can go really badly if you don't do it properly um so in september 2017 equifax announced that they had a breach uh this affected around
145 million u.s citizens there's estimates it's not really clear how many british but estimates are so ranging from 400 000 to 44 million and one time was termed one of the biggest breaches in history um a credit company got a negative credit rating because of this breach uh estimated costs of the breach were about 1.4 billion that's 14.4 billion with a b um now that was a i think last year sometime so it might have gone up um i've not heard much more on that so the important thing to note about this whole fiasco was it was a vulnerability and apache stretch which is an open source framework um that's used to create websites um and the attackers managed to exploit
the skid remote code execution and work the way and get exfoliate the data theoretically i'm not saying this is the case but theoretically this could have been a one-line change if you're doing dependency management properly it's literally changing the version number and they could have saved themselves 1.4 billion as well as all the negative price and all that kind of stuff associated with it um i will admit that at times it's not as simple as simply changing the version number sometimes if you change versions things can break and all that that's why you need appropriate testing and and that in place so you can do that with confidence and relatively quickly because this was a
severe vulnerability this is a bit of a segway because out of these breaches and all these incidents that we see happen and i guess my graph that's not really related to infosec but i thought it's still worth mentioning um we we see the same phrase over and over we take your security seriously and in some cases it does relate to uh application security because if you really did would my details have ended up in that breach would you have had a breach now granted not everyone is or no one is ever safe from a breach uh often it's a case of when not if but probably i would say if you have a breach notification
it's maybe not the best time to mention how great your security is um or how how much you take security um rather stop mentioning things about how you can improve your security that's maybe a better way of approaching it for those who don't know there's a site called why the f was breached.com and this comes up with a list of excuses i just threw the same because i thought this is just um pretty clever and um entertaining so some of we've seen some other excuses being used and really i think often it comes down not all not all the time but many times it does come down to just the lack of security awareness and even some maybe sometimes
you could even say uh caring about security not all the time but maybe in some cases you can so been waffling on that a lot about the um problems that we see and all of that but now let's start focusing on what we can do to make things better how we're going to fix this so first thing as you reflect right to the i think the first slide i did stop blaming people stop blaming your developers stop blaming your users stop blaming your employees blaming people on that is not going to help anyone if you have a security incident don't shift the blame take responsibility it's it's not going to help shift the the issue away you are seeing
cases where someone finds a vulnerability or something announces it's the company and the company tries to sue them that how's that going to make the vulnerability go away or be fixed it's not so stop their culture the other thing is we we need to stop security being seen as a a roadblock um often security folk are referred to as the no people we always say no in fact recently um our security team was helpful in saying like look we're gonna help free up some resources because we need to start prioritizing security bugs and we can use that to help free up resources instead of just dropping everything and immediately running to to um bugs um and it's about doing things sensibly
there's always going to be risks but in my view security is about managing risks so let's start making the security teams be seen as a team that's going to help the company rather than prevent you from doing your job and one way we can do that is around security and awareness so i kind of touched this on the beginning how can we expect someone to not do a crossout scripting or a sql injection or a server-side request forgery if they don't even know it exists personally when i left university i didn't know most of that stuff existed it's only because i had an interest in security i found out about it many are leaving universities and coding
centers and training centers um without any of this knowledge so we can't blame them for not uh well for not preventing these sort of uh issues if they're not even aware about it so the very first step is making them aware about it um and there's different tools that we can use for this gamification is a really big thing let's start making like little competitive so things like cts so i come from a development background and traditionally development teams that i've worked in the past are competitive i want to do a release quicker before year now so let's leverage that um let's use that to our advantage and get teams competing against one another um have a leaderboard have a team
leaderboard the other important thing is don't make it something mandatory that end of year you know you have to complete this massive powerpoint slide or presentation or whatever and then answer a bit of questions um tell you what many people do click click click click click go through answers abc uh try different answers and yeah i've done the mandatory training we need to do it so we engage them we have it at their own pace that way they can fit it in when they need to um and it's going to be something that they hopefully enjoy doing team base is another good way of doing things getting people to work together i often find that i really enjoy trying to
tackle training or things like cts so scott mentioned at the beginning hack the box i personally try avoid doing things like hack the box on my own i enjoy doing it as a team based event or trying to take a vulnerable web app and trying to uh tackle that as a team humans by the very nature of a sociable species and this kind of comes to the whole community verb we get a community going together so already like besides is a awesome example of this it's started off uh in one thing in las vegas and it's now grown all over the globe probably thousands of talks um sharing the knowledge helping one another out sharing the awareness often
it's one thing to fix something but it's another thing just to be at least aware of it so you can put things in place or have something to say okay you know what there's this new vulnerability tab i'm gonna go learn it in the next five weeks whatever i don't have time right now but at least i know it's there um things like os that are producing amazing tools uh and there's so many good things coming out of other groups again don't pull things from the ground up leverage things that are there i know i did say about someone else's code but if you do it correctly and choose the right tools and frameworks and that the
reputable reputable um the developers and organizations such as owasp [Music] then that can really strengthen your security uh i've done power tests on things like a python app that the team didn't know anything about security but because they used a really good framework go i could find really nothing the only flaws were business logic flaws there was no sequel injection there was no cross-site scripting i couldn't get any of that it was in some sense a dull test but that's a good pro that is a good problem to have um especially when you're talking about complex things like crypto you know does that say don't roll your own crypto there's a reason for that it is extremely complicated
leverage things that a people who know what they're talking about and doing have implemented it and b if there's if it's a popular library guess what it's been tested thousands of times um okay not all the time so we've got things like heartbleed and that but it's taken years to find it but the point being is if there's anything really like what's termed low-hanging fruit like really easy to find vulnerabilities those should hopefully be found really quickly tooling this is something that's going to become more and more important as i mentioned things are going faster and faster and faster we're going to have to start using tooling to help us enable um our security when we're developing
and maintaining these apps so i've already touched on things like using builds and tuning so use things like csp it's there it's free it doesn't cost you anything it can save you loads of hassle if something bad goes wrong yes there are pain to me put in sometimes but that pain is worth it it's going to be a lot less than 184 million pounds um another thing is if you or hopefully are using tooling don't just throw the tool in there put the defaults on and awesome sorted it's going to solve all my security problems it's not you're going to have to put work in you're going to have to cast customize that tuning uh tweak the
settings especially things like dynamic application scanners which scan web applications you're going to have to make sure that it's a scanning everything because guess what they're often modern web apps are really complicated you need to click here click there and then you get to that page well make sure you do that and feed that into the tool so i can get to that page some of these tools are also not aware of the business logic so if you think about a scanning tool how does it know this user should be able to access this you can't so you're going to have to have different scans with different users and then see the results and see where
this user's maybe got access to this page and it shouldn't have and make sure you keep these tools up to date some of these tools i just saw with f5 have vulnerabilities themselves or there's no rule sets new kind of technologies being brought up so make sure you're keeping them up to date and from experience avoid building your own it's just another thing to maintain um it might seem cheaper but in the longer run it can cost you more in fact and then finally it's all very well having all these tools running in that but you need to make sure those using that actually know how to use it how do they interpret the results what
the results mean for them we see in a case i think it was uh targets but they actually saw the the incidents or the attackers in the logs but because no one was really using that or maybe didn't know how to interpret the results they didn't catch it and this kind of goes on top of tooling so automation is going to be really key um we can't keep up with things uh this constant stream of releases is just probably going to get more and more continuous integration continuous delivery click a button or test pause great automatically deploy into production um so you might not even have a chance to test it before it goes into
production so you're going to have to build security within this whole deployment and lifecycle and the only way you're going to be able to do that is via automation so again make use of existing tooling don't try to write your own there's a load of stuff out there um the other nice thing about this unlucky human it can work 24 7. so if you want to do a scan every hour guess what you can whereas a human you might be a hard pressed to say hey joe or jim or jane or whatever can you run this can you do a pen test every two hours for the next week it's not gonna work but it's important to note that the
automation the tooling does not replace humans you're still going to need humans a involved in the setup and configuration and main maintenance of these tools but also for some of the periodic testing that you should be doing pen testing is still very very important i've done pan tests in the past where i've passed the first time found some things great brand scans all that nothing second time i did it i found a whole bunch of other different pretty severe flaws um different people different set of eyes different knowledge that's all good and that's why we need humans involved so if we come to uh and um i think these next set of slides are probably going to be the most important
when you talk talking about application security and maybe even security in general it's your shared responsibility now i know it's corky security is everyone's responsibility it's a cliche but it really is um be it your developer qa all that you all have an important part to play in security any one of you can find a security vulnerability any one of you can help prevent a organization be breached um so i think this is really important and this all builds that security culture if there's one thing that you can do to help improve your security is this security culture because guess what as soon as you have the security culture the other things just will start falling into place um
and zoom is a really good example of this and i know a lot of people probably don't like zoom and still think it's a joke and whatever but i completely disagree yeah certainly at the beginning of the pandemic they had many security flaws and i don't disagree with that i totally agree they were found wanting but guess what they decided that they were going to change their attitude and culture towards security and i think that took like three months just to focus on security and i think if we can get more companies to do this we'll find less and less of you know like the top five falling into the house top ten i was sorry five of those top
uh 10 from 2003 coming into the 2017 list like i can't stress like security culture and attitude makes the all the difference in the world and how you're going to get this things like training awareness uh don't finger points and that and then once you have that you're going to have a much better robust product like zoom today i'm not saying it's perfect nothing's perfect but if you compare it to where they've come from it is completely different it is almost an entirely different product and they've done an amazing job and other companies out there have done an amazing job as well so any questions uh i don't have any questions from the slider uh
there is two um so anonymous viewer or anonymous has asked amazing content sean which one of these observations suggestions do you wish you had known 15 years ago you only get one tricky word um i i'd say probably the os top ten like and it comes around that awareness and training and that kind of thing like if i know in our top 10 10 years ago up i probably wrote code with a lot of those things in it um and if i had known that 10 years ago i probably could have also helped people share that knowledge and say like hey or if i'm re-encoded like hey you don't want to do this because of x y
is that and it's all about that sharing knowledge culture well answered if someone says to me you can only pick one i panic so very well answered uh i've got something but i'll use the audience questions first uh libraries or plugins changing owner slash maintainer could be a vulnerability as you're now running running a new someone else's code how can we mitigate this yeah that certainly is a very real risk and it i think it has happened in the past where a owner gave up ownership and someone has to occurred over [Music] how we mitigate that it's it's a really difficult one um i forgot the figures but if you look at the the library management and how many
libraries that we are using in our code it's just staggering the numbers and that's just like doing that so trying to tackle this manually and vet every library that you're doing it's just not going to scale so it's it's a really difficult one um and i'm not entirely sure of the answer perhaps some things like some of the the public repository managers they might do a better job saying hey um if the ownership changes well we won't allow ownership change unless you go through a stringent security review process maybe that's one way of tackling that but yeah i i don't really have a concrete answer to that we we obviously saw the fallout i think
it was was it left pads um just this really simple nodes node package or was it a node package i think it was yes something like that yeah the the owner removed it and as a result and it was a really simple package it was something you could have written yourself but there was thousands if not hundreds of thousands of applications out there that use this which broke okay not not a vulnerability per se but what happened next was very interesting and it happens every single time that i guess tick tock gets banned or something gets banned as our flappy bird gets removed from the app store we suddenly get the clones of those people panic the developers are really
moving quick because they're getting breathed on by all sorts of managers they try and change it they just grab the first package to see and it turns out later that it's got a a ransomware a crypto oh would you call it a crypto currency miner that's one i can find my words but a crypto miner in it and you know all of a sudden we've got uh big big industry names who should know better running crypto miners on their main site because of one simple package that has just disappeared um yeah and and this is why i think it's a really important area and something i think and like okay i have no intention of
ever doing this for making that yeah clear but if i were attacker that's exactly where i would look um why try break through the front door when you can just get neatly inserted inside and then you can break out and you have access to so many things um also the other thing to consider is like even though you might include package xyz that in itself has a whole load of dependencies so how do you make sure it's just like yeah it gets really hairy really quickly yeah i can imagine uh we did get another question in from euless who um by the way if anybody's watching on stream uh you can absolutely tune into his
workshop it's for hardware hacking i think he mentioned earlier he feels as if he feels seen he feels as if he's the hardware guy you're the software guy and you guys are twins but his question was what is your view on inspiring kids as early as an elementary school to make them security aware yeah i think it's impact um one of the things that i'm really um strong about and that's why i include things like the real world examples is it's all very well saying hey he has these security vulnerabilities like take across the description for example um often training material just shows that is like hey you can show this pretty alert box yay
wow um versus maybe showing something like a b [ __ ] okay well you've now got this crosstalk scripting in a beef which is browser exploitation framework i suddenly have access to your browser i can start injecting things in your web page and all of that that suddenly sparks something like okay well this can suddenly affect me let's take like tls for example i did a demo with the wi-fi pan apple saying hey you connect to those hotspots and suddenly i can start viewing all your traffic as well as modifying it unless you using tls so trying to hammer home how it can impact them hopefully that will suddenly make them like oh okay so this can suddenly make a big
difference to me so this is why i should be worried about it honestly just yeah no honestly just showing showing anybody a wi-fi pineapple is like magic i mean the only time it ever gets brought out is for like demonstration i i've bought one it sits in a drawer i never use it i i i've promised it to someone that's i mean how many of us have done that they've just bought a ton of hack five stuff never used it but it's there and that gets people interested the other thing about that is also the kids like the cool wow factor it's cool so leveraging that as well yeah it helps as well if someone cool is
giving it like yourself like you can actually like get no i mean that in a positive way like you're actually getting really excited about what you're talking about rather than droning on and uh do you remember where it was like when you're younger and you know you've got a mobile phone that's a brick and someone comes out to the school and teaches you how you know you shouldn't use a mobile phone because it's dangerous and the guy's like average age of 90 to 150 and you're looking at that going you don't know what you're talking about but when you see someone like yourself giving a really energetic like you know this is really cool and
look at the cool look at the cool stuff we can break and here's how we can fix it and here's all the cool stuff we can do in between honestly man i love your work and loved your presentation yeah cool if anybody wants to catch sean he will absolutely be he'll absolutely be hanging around on slack but do go follow me on twitter at sean wrightsick not sean wright something else that's someone else entirely but no go and follow sean on twitter he's absolutely brilliant he just tweets some good stuff and genuinely um you can you can see why i i think sean's awesome so thank you sean