Titanics Of Security: Users Aren't The Only Problem
Show transcript [en]
right that's let's get going so I was I was I was in I was in work after having we were having a conversation when about when we found out that that 'besides was gonna be in the Titanic building this year and a colleague turned her and says to me I bet you someone's going to do a talk about the Titanic's of security yes yes that's right hi I'm doing a talk about the Titanic's of security it's me but and some of you might think that what you've what you see today would be similar to what you might have heard from from Brian this morning in the keynote but hopefully I've got a more positive outlook on this it's my first
talk can you tell so who on earth who on earth am i my name is Jason Holley I'm a third year undergrad at Napier doing cyber security in forensics on my year out at the minute working in threat intelligence at a security company I am a new guy in four SEC you know first job still at uni all that sort of stuff but I'm getting jumping in at the deep end is it worth being at a conference like this and yes I'm originally from northern and so this is a home conference for me if you if you feel like follow me on Twitter it's at set Comet there'll be there'll be a feedback thing going up after there hopefully so
we all know about the story of the Titanic when the Titanic sank in 1912 after strike striking an iceberg on its maiden voyage it was the deadliest marine disaster to happen in peacetime to this day I believe and the deaths depending on what source you look at anywhere between 15 1600 it was a horrible tragedy as we know in fact the the experience downstairs in this building is dedicated to to the history in the memory of of that tragedy and it was a tragedy but we investigated and we discovered why it happened and here are some of the reasons ice warnings that were given to the crew weren't heeded they decided to plow full speed straight
through the straight through the ice field instead of going around it there was only one life book drill that was carried out in Southampton the lifeboat numbers at the time on most ships were dependent on the fact that there would be other ships nearby to shuttle those passengers to the radio officer on a nearby ship the californium was off duty meaning that they didn't receive the the message that satanic was was in need of help the lifeboats weren't fully stocked and there was a belief as we know that the revolutionary technology meant that the the ship was unsinkable does that remind you of anything so yes it was a tragedy and we found out why but when we found
out why we fixed those problems after that Titanic sank we got an international treaty the International Convention for the safety of life at sea and I'm going to look briefly at chapter chapter 5 which is the only one that applies to all vessels and most of the decisions put into that were as a result of the Titanic's in sinking there must be a lifeboat place for everyone onboard the radio must be manned 24 hours a day so you're gonna have to have a rotation of people Manning it the crew must take heed of any of those danger warnings that they receive and the Masters of all vessels must offer assistance to any ship in distress you'll see that with
Somali piracy even if the Pirates get shipped gets disabled the navies have to help them they can't leave them a sea that may have seen off topic but the question I'm asking is what is the InfoSec equivalent of so last what is more is that requirement that we implement those lessons that we've learned across the entire industry and across the world I'd argue there isn't some of you might be saying to me well what about GDP our GDP ours good legislation I'm not going to knock it but the issue being that it only applies where EU citizens are concerned and you will not know you'll all too often find especially in America that websites will
simply block EU citizens from accessing their website in order to get around the requirement to to comply with gdpr which isn't great because they should be complying with every good that if good legislation comes out whether or not you're required to comply with it music because we should all be invested in making security better but unfortunately some people prefer the bottom line over everything else audience interaction question number one can we prevent every cyberattack who thinks we can good good yes of course we can't we can't prevent every cyberattack there are an unknown amount of unknowns that will prevent us from from seeing from detecting and stopping any attack launched against you wore your the
company that you work for so we're never going to be able to stop them all but when they have happened we can investigate and we can discover why and sometimes it genuinely users can be somewhat at fault whether it's through having weak passwords or falling for for phishing and that's not exactly great but they put their trust in us in security professionals if you like when they upload their data to two websites on unto your to your system and we should and if we are supposedly the experts then we should not be so we should not be putting all of our trust in them not to fall for phishing or have a weak password we can advise we you
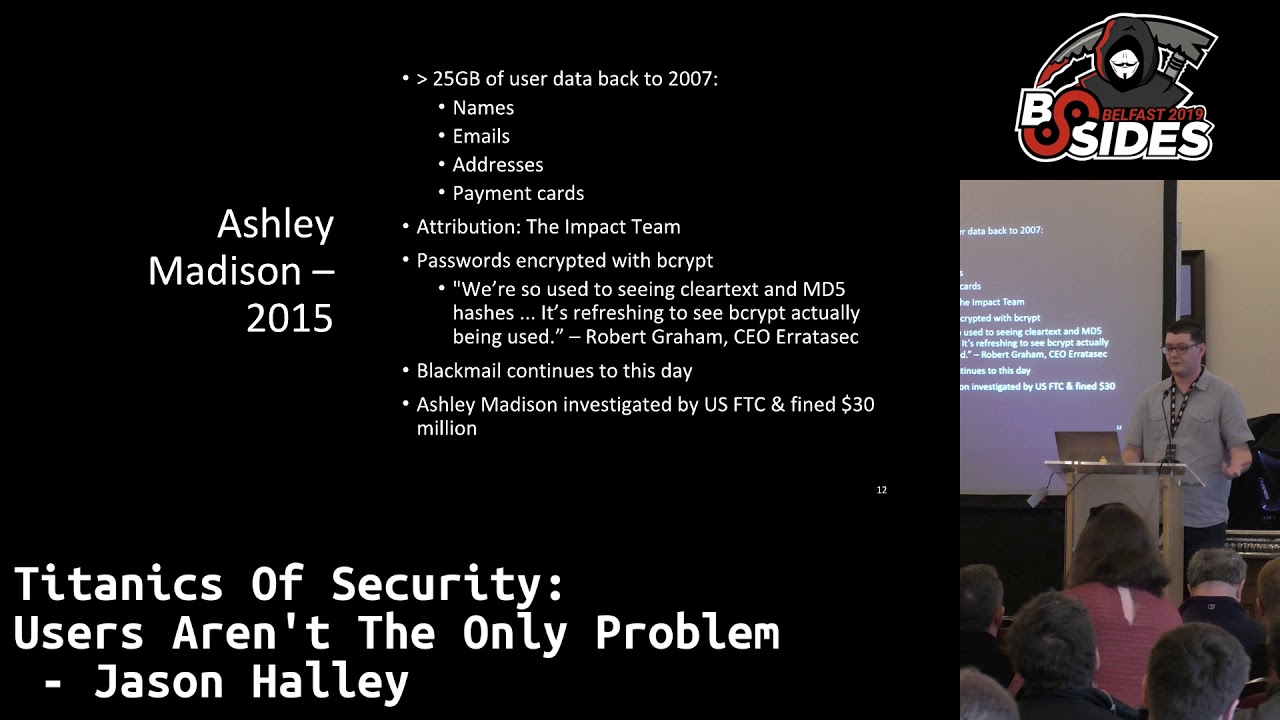
know we can suggest to people that this is the way you should do it but we should always take the worst-case scenario that people won't so what I'm gonna do is I'm going to look at three cyber attacks that have happened and an establish for you that we can detect what happened so Ashley Madison the data breach that happened in 2015 and I know that's gonna be a bit controversial but at the end of the day regardless of whether you think the service should exist or not it does exist it's storing personal information and therefore they should be doing so in as secure a way as they can which as it turns out they weren't necessarily doing there was
there was 125 gigabytes of user data dating back as far as 2007 that was that was released to the public including names emails addresses and credit cards it was attributed to a group called the impact team the odds they'd stolen the data they actually essentially ransomed Ashley Madison and their parent company demanding that if the website and the service wasn't shut down then they would release the data Ashley Madison didn't do that and the data got released the passwords that were were stolen were encrypted with beef a relatively secure way of storing of storing passwords and in fact Robert Graham CEO an errata SEC said at the time we're so used to seeing clear text
and md5 hashes it's refreshing to see bcrypt actually being used we'll come back to this later blackmail of individuals who were whose data was released in this hack that continues actually to this day and on a slightly sadder note there are reports that there were individuals who were so ashamed once their families discovered that their they'd been using the service that they actually took their own lives which just goes to show that yeah we think that sometimes a cyber crime is being victimless but it very much isn't Ashley Madison were investigated by the US Federal Trade Commission and they were fined thirty million dollars essentially for their negligence so what went wrong here with Ashley Madison well for a start
if you'd been using the service and you decided I don't want to do this anymore I don't like what they're doing and you want to delete your account you have to pay them to do so you can deactivate your account for free but if you want to if you want to actually get them to remove your data you have to pay them 15 pounds in the UK which which is it's a nonzero amount of money and most people aren't gonna want to be paying that and even in the cases where people did hand over that money and a lot in a lot of those cases Ashley Madison just did the account deactivation and actually didn't
delete those people's data which which would GDP are enforced nowadays would be a big deal oh another big problem was the fact that there was no email verification when you were creating an account if you if you put in you know John at Smith comm is your email address when signing up it would accept that and not only that there were even if you did put in a real email address there was no requirement to confirm that you own that address before setting up your account so I could set up an account in the name of anybody in this room if I felt like it and then you would have to not only if you wanted your data to then be
removed you would have to get into that account that I've created and then pay to delete it and as we've seen even then they may not actually delete your data and you have to ask yourself if if that if that was you and your date your data your name and your email address ended up being in the in the list of data that was compromised would anyone close to you actually believe that it wasn't your account I don't think they would we we generally accept that if your emails on it it's it's your account and then there's the fact that that users I said we're not trying to blame users entirely which we're not but users were using the
same sort of weak passwords as on other websites except for number nine on that list which I'm not going to read out I said we'd come back to this because if those passwords have encrypted with with bcrypt it still would have been very difficult to reverse them to get your your password back but as it turns out when Ashley Madison had moved from using md5 to using bcrypt their md5 hashing and storage remained active so md5 hashes of people's passwords were being stored right alongside the the bcrypt hash meaning and obviously with these then weaker passwords that's a lot easier for for the user I'm sorry for the attacker to compromised that password and okay you may have all the
user data anyway but users tend to reuse passwords between different services so they're likely just going so they're likely going to then stuff using your email and that cracked password against every website they can find to see if you've been involved so all in all not a great day for users of Ashley Madison let's let's move on and look at a watercraft in 2017 ransomware as I'm sure you know that encrypted your files demanded payment in Bitcoin which used to exploits eternal blue and double pulsar which were developed by the NSA who didn't inform Microsoft that they you were had these vulnerabilities and then were eventually leaked that stone slash stolen depending on who you want
to believe an estimated 200,000 computers in over 150 countries were affected so it's clear at this point that SCI attackers don't care about international borders or jurisdictions they're just going to attack you wherever you happen to be it was in tributed to a group called the Lazarus the largest group who are believed to be to have originated from North Korea and it wasn't only individuals that were affected but some rather large businesses the NHS in the UK was affected of the Nissan production plant in Sunderland actually had to stop production for a time because all the computers will be having their data encrypted and not being able to work properly and even the German National
Railway Deutsche Bahn they had to their services were affected when they were then when they were hit the kills there was a kill switch in the initial initial version of wanna cry discovered my Marcus Hutchins but eventually there were there were different kill switches that were were implemented in your variants that that were discovered and registered and then that kill switch was was being used and then eventually a variant was released that just didn't bother with kill switches at all you could argue that one a cry wasn't a very effective because the ransoms that were paid only totaled around $100,000 whereas the economic impact was up to four billion dollars so depends how the how the enemy was I'm sorry how the
attacker wanted to affect us whether it was through economic impact or through actually making money arguably they succeeded better in that in in causing economic impact than making their own money so one of the big issues with warrior cry is the NSA the NSA were developing exploits in-house finding vulnerabilities in the Windows operating system developing an exploit for it not to a Microsoft about it because they didn't want it to be patched they wanted a chance to to use those and and who knows who they were trying to use them against an argument and arguably they they shouldn't have been doing that but Microsoft did eventually discover those vulnerabilities on their own and release patches but as usual a lot of
organizations were either using operating systems over end-of-life or they weren't updating their systems because they were too worried about breaking core functionality and that could be the case with feature updates sometimes anyone who uses Windows 10 will know that you update and everything's broken or all your files are gone and it's not a fun time but with security updates you would like to hope that more people would be more that people would be more responsive although it isn't always the case the kill switches were were found and registered which is really a case of six of one and half a dozen of the other because you either don't register the kill switch and it doesn't do anything or you
register the kill switch and the hackers just go and change the kill switch or eventually just remove the kill switch entirely so now you have no way to stop it but you would also have no way to stop it if you chose not to register your kill switch so that really is a case of six and one and a half a dozen and the other there isn't no win in that situation and some people didn't keep data backups they weren't they weren't keeping backups of the critical data so if they were hit with one a cry and their data was encrypted they the data wasn't was genuinely at risk whereas if you've got backups you just we re image
from your backup job done and you're back up and running another issue is that people actually paid the ransom that was being demanded which if you ask anyone who works in in law enforcement they'll generally tell you that in a ransom situation paying it is sometimes the worst thing you can do when you're demanding payment in Bitcoin particularly there's no way to track where that money is going to so there's there's no chance of you identifying who's who's it who's to blame or or getting your money back you could easily be targeted again you could pay the ransom say for example your files actually get decrypted which there's no guarantee and then you go connect to a
network and the computer spreads want to cry back to you and then you're in the same situation again and you're open you're marking yourself essentially as vulnerable or willing to compromise you know oh if I if I blackmail this person for money that they're going to they're going to pay up and you open yourself up potentially to further attacks there were actually people afterward after wanna cry were sending out emails to as many people just as they could find saying I am the creator of one to wanna cry if you do not give me money I will delete all your files this time and you will never get them back who knows if they were actually those
individuals are not so so ransomware is is no different to any other physical ransom situation you should under no circumstances pay up let's move on to two Equifax in 2017 a data breach of 146 million records that's basically half of the u.s. population which which is a lot of people and not only that but the data data lead was very was was critical if you've if you if you know anyone in America they have the social security number which has no security features built in and with just name birth date and social security number you can do a lot you can get credit in someone's name you could get medical treatment under their name and take their records you
could steal their their benefits or their tax refunds from the IRS and you can commit crimes and mix up criminal records which could be very difficult to fix afterwards Equifax came about from essentially just individuals scanning the web and saying oh we know there's a vulnerability let's scan the web to see if we can find any servers that have that are vulnerable to it and they did they found three that belong to Equifax and were able to get the credentials to these the service which were promptly then used against every other Equifax own server they could find and it worked for another 48 servers so clearly credential reuse was involved here an arguable and arguably
these these hackers were were smart because they exposed rated their data slowly knowing that if they tried to bring it out all in one big lump they were almost certain to be detected and potentially stopped but by doing it more slowly they bought themselves time to get all the data out without being detected so updates are rearing their ugly head again when it comes to Equifax the the vulnerability that was used had a patch released by Apache on March 8 2017 and the attack didn't start to March 10th you might say well that's not a long a lot that's not very long and if you had a large amount of large amount of service like Equifax do to update you
might not get round to getting them all done in time but in but when it comes to Equifax they only had to update those three and the attack may have been stopped in its entirety password reuse was also a problem like I said the the hackers only got the credentials for three service but these ended up being valid for another forty eight service we can all do Matson and that's that's fifty one servers in total there you go access to only from from compromising come from comprising two three directly if Equifax have been using unique credentials and passwords for every server that they had then the data stolen may have only been the data from those three servers rather
than the 48 others a lot of people never gave their data to Equifax as a credit monitoring firm they buy data from God knows how many different sources and then it's it's all stored there and you may not know that they've ever obtained your data which isn't great and in fact in the you arguably it's unlawful now because you need and you need individuals to opt in to their data being collected by third parties before it you can actually do so lawfully whenever facts discovered that they've been hacked there was a period of about six weeks where they kept it to themselves they didn't release that information publicly which argue which is not a good idea when the the those
individuals affected their data was was already in the wild and excuse me they were they were hiding essentially the fact that they had been breached rather than allowing those people to to fix or to at least know that their data might be out there and to look for suspicious activity and arguably this was done to give Equifax executives time to sell their stocks because they knew that as soon as that news of the attack went there their stock would just go through the floor although they claimed it was it was time that they used to conduct an investigation arguably both are true the the website that they then set up to tell individuals if they've been
affected because remember not everyone whose data was in that breach actually gave it to Equifax in the first place was was poor not only was the the web address they used sounded like a fish an account an actual phishing website with a similar name but with the word swat round was set up an E and the official Equifax Twitter started tweeting about that so essentially Equifax were were promoting fishing against their own data subjects and not only that but the system itself was was poorly constructed depending on what device you used or what browser you used or even just randomly from from check to check it would change its mind between you've been involved you've not been involved
which isn't great so we've established that we can't we can always investigate after these attacks happen and we can determine for the most part the the reasons why they happened the causes and what we could have done in hindsight which is of course 20/20 that we could have we could have done and if we had done would have prevented or minimize the effect of those attacks that happened so if we can do that why the similar attacks still happen you know why do we see companies soaring our hashing passwords with md5 reusing credentials not updating their servers when security vulnerabilities come out arguably it's because that point of view that we have where we're all in our own
little box and we don't want to to share anything because we're afraid of either letting out intellectual property or afraid that we we are going to embarrass ourselves either to to the customers of of your organization or or to to rival organizations and despite the fact that despite the fact that these individuals still despite the fact that they they don't share and it leads to this this issue of hiding ourselves away rather than sharing and trying to make security better for everyone and those those really are two different cultures of the blame culture and the just culture and at the minute to insecurity the vast majority of organizations are in this blame culture where they're focused on concealing
their mistakes or blaming those mistakes entirely on one individual and saying you know it's your fault you're fired get rid of that person we fix the problem well probably haven't it's in a blown culture you're going to be more focused on protecting the bottom line rather than protecting your data and it does lead to this this security theater an illusion that you've got effective security when if you you look deep you know if you ask yourself honestly that there is there are going to be holes in your security there are going to be ways in but you pretend oh yes we're we're a Basti and no one's no one's getting into our system and if you're pretending like
that's the case someone's probably already in your system well we should be doing is we should be focusing more on on shipping and aviation and having this just culture of saying okay we messed up what could we have done let's implement that and arguably let's then share that to the world and say look we have made a mistake but we know how to stop this mistake happening for everyone here is how to do it you know you install this patch you you stop doing this or you stop hashing your passwords with md5 arguably that's an obvious lesson but I keep coming back to it as an example and that will that will lead over time to a
sharing of security best practice among everyone where because everyone is sharing none of us are particularly shamed or embarrassed to say look I made a mistake or we've made a mistake rather as an organization but we're fixing it just like every other organization is doing and here is some information on how you could prevent this happening to yourselves in the future rather the minute where if an organization gets compromised all the rivals just go ha ha ha they got hacked which is which is not the not the ideal solution because likely if they've already been compromised in a particular manner that attacker is coming after everyone in that in that business area and as I mentioned and as
you would have heard from as you would have heard from Brian this morning that's used more commonly in aviation and indeed also in shipping which is which is hopefully gives reason to to my lecturing on the Titanic earlier by the way go downstairs if you want more more more on the Titanic you won't get that much from me but but other industries have learnt this already they've like shipping in aviation and others they've learned that it's better to say okay we made a mistake we have found out exactly what happened and then tell everyone here is how you stop this from happening ever again and for the motifs alting in the most part you don't see the same
shipping disaster or the same aviation disaster happening more than once ideally or certainly no more than a couple of times you know we don't hear of aircraft running out of fuel constantly we don't hear of ships hitting icebergs down the side and destroying all our wats tight compartments happening every every time so I guess what I'm saying is that we should move to this just culture and in some ways some parts of cybersecurity are already doing this a lot of organizations are putting security text information on their web sites where if you if you know of a problem in our organization a security issue you go to their website slash security text and there's all the information you need to
contact them and report that rather than hiding themselves away and going we're not telling you anything you know we're a bastion we're invulnerable they're saying okay we might be vulnerable if we are please tell us we want to know I'm bug bounties are another good way of doing that and put offering a financial reward for through doing it now we're not going to solve every problem just with a text file or with always bug bounties but already in the UK at least we the national cybersecurity center who will get involved with liaison with organizations who are either in the middle of an attack or whether an attack has happened to help them in whatever way they can and they can glean bits of
information that from that that can then be anonymized and shared with other organizations and arguably this is the way aviation works as well each country having its own organization that deals with the the aftermath the discovering why or how and then sharing that although arguably there's less anonymizing of the data there because you can't really conceal the fact that your ship sank or your plane crashed but we could do more we're not perfect at all and in fact what we are dealing here or what I think we ideally need is some sort of equivalent of Solace a global requirement to implement lesson the lessons that we've learned from previous attacks so we don't see them happening
again we need that that global essentially legislation you know a convention whatever you want to call it to say that yes in our country when we find out this has happened we are going or we find out that there's a particular particular way that organization can be attacked we are going to require every organization that does business in our country to fix it and and you might think you know what I'm dreaming but well if we're if we're dreaming then you know the sky is the limit and I'd say we we should we should be aiming as usual for the best possible security that we can I would love to if if they decide to
have me back to say to be back at a besides Belfast in in five years time saying you know what guys we've done it we found and we found an equivalent of solace for cybersecurity and it's implemented across most of the world and that would be that would that would be great I'd love to I'd be I'd be happy to see that and I hope you would too so essentially what I'm saying is that within within the future I want to be able say that you know what security within just about every organization is built from disaster and I'm that hopefully positive forward-looking thought I think yeah we're coming to the end of the time
so that's all thank you very much for your time and if you have any questions feel free thank you Jason we will hope to see you back in five years any questions come on people we have some time ah you were very very clear sorry tell us about solace is up to do with ships's look yes so it's an international convention for safety of life at sea as its called I think so 99% of shipping by tonnage is registered to a a nation that has agreed to it and it sets out safety standards that are mostly come from lessons learned in in tragedies and if you are if you're if you register your ship say
in the UK which is a nation that has signed up to so lass there are these minimum standards of safety that you must adhere to which would ideally lead to so it would mean that the the incidence and the tragedies that have happened in the past would hopefully not occur in the future I was reading the pan test partners find a box attached to a ship's network and no one knew what it was but they worked out advanced-level it was the owners didn't order was it was no and then trade medicine for it I mean is it that good service so so less focused more on on on safety rather that than cybersecurity if you could argue that
that global emphasis of cybersecurity that I would ideally like to see would be what would prevent that sort of that sort of cyber incident from happening another question yep so I worked in an industry in which most of our revenue comes from maritime customers and we do specifically connectivity for the maritime sector and aviation as well and yes as as our lovely speaker said a lot of those regulations are based mostly around safety and my particular company not to put in a plug but we are looking to increase our security at the edge so that way the connectivity that goes through to ships and not just for safety purposes but also for just end-user connectivity for crew members or for the
business capabilities there is a lot of research and funding and development going into that because there are vulnerabilities there and that's something that it's definitely in need of being addressed and is being addressed if that helps any Cheers any more yep next time you sit somewhere up front the season Thanks so one of the big drivers for adopting aviation safety standards was the use of shared resources like airports you went to lighty an airline wasn't allowed to use an airport unless it was signed up to the standard do you think there's any equivalent for IT and so on that we could use to drive something like those standards arguably arguably the cloud would could be that
that requirement you know Google Cloud or Azure AWS could could be it could be game changes and drive forward this by introducing a stand a standard of security within your organization and say hey if you want to use our service you have to comply with this standard and if you don't well then our doors are closed to you all right any more no okay we have short lunch break sorry coffee break and we will be back here at 11:45 for the next speaker and thank you again Jason and thanks guys