Barbarians in the Throne Room

Show transcript [en]
now to give you our first speaker and the fellow Canadian who is living proof that you can actually work in InfoSec for what several decades and not become an empty hollow husk of a of a human well let's not get ahead of ourselves okay all right thanks David thank you very much and thank you all for being here this is actually a great privilege for me to be able to be here for your first 'besides I have been well first off let me introduce myself I have been in InfoSec now for about 25 plus years and I have been doing this long enough that yeah I am actually a bit of a jaded empty husk
now but it doesn't have to be that way for you when I started out there were no masters of information security courses there were no textbooks that we really could rely on in a big way we had to go through and read our FCS and just poke things to see how they would go until they actually broke and it was really interesting in that regard I have been in all sorts of roles I've been a firewall that men write through being a CSO for a power company and all points in between and it's absolutely amazing how much you learn along the way simply by interacting with others now I've been very fortunate in my career that a lot
of what I've got to do is I on the board of directors for besides Las Vegas I helped found Toronto's b-sides and I helped work on besides London this is something that all of you can contribute because this is your conference this is your ability to share information I was talking to somebody this morning where they said you know a lot of conferences out there it's very expensive for people to go to and that's true something like this is community driven and this is something that you benefit from by what you give into it don't think about what you can take away from it you can contribute to so let's do this really quick I know
I've gone on a bit of a tangent here but a show of hands how many people here have ever given a security talk before ok the ones that didn't put up your hands I hope you're gonna apply next year I really do sincerely so as I said I've been doing this for quite a long time and I personally identify myself as a hacker and if you quickly go through and check out on Google people as much but we're really there to help and being Canadian we tend to like really like to help because that's what we do when we're not drinking beer and eating bacon but the easiest way to spot a Canadian is look at us in our natural
habitat we're usually dressed like a homicidal maniac going across a sheet of ice I work for do security as a global security ad sorry global advisory see so and that means I just run around talked to people in a lot of ways and this has been a really amazing opportunity for me because it gets me to events like this where I can talk to you and share the lessons learned and think mistakes I've made along the way now back in October Cisco came along and bought us up and I'll be honest I was nervous at first honestly this has actually turned out to be a really beneficial thing we went from a 700 person shop to 80,000 people
overnight and he's actually working so that's kind of cool and one of the really interesting things is we've helped build ourselves a lingua franca between the two organizations as we went along and this is something that tends to be overlooked when you're talking about data breaches and there's gonna be a few companies that I mentioned during the course of this no none of them from Norway that have had data breaches and this is by no means to make them look bad this is to work about talking about lessons learned and sharing the information from these data breaches in such a way that we can constructively move forward so one of the things that I did when I first started building out
this talk is I went through and I read all of the publicly available data breach disclosures for two years ago and then again last year and if you ever have trouble sleeping this is a great solution but the really funny thing is is I went through all of these data breach notifications I really found that there was no common lingua franca there was no common understanding as to how to explain this to a wider audience because in a lot of cases these organizations don't want to share too much and I understand that because there's legal liability and things to that effect but this would help us in a bigger way if they could share more information in a
sanitized fashion to protect the guilty parties now the security paradigm that we tend to operate on is having a perimeter having a castle walls having a moat but back in 410 AD we found that demonstrably to be a broken security paradigm before I ever got into security at all I was doing a degree in I apologize for my thick Canadian accent I one of the things I was doing is I was doing a degree in classical studies in archeology long story how I got here but one of the stories that I took away from that was the sack of Rome in 410 AD and this is when the Visigoths showed up they sealed off the city from any in
anything coming in or out and over time the Romans ran out of food they ran out of supplies eventually they gave up and opened the doors so the attackers were able to use their own security paradigm against them in such a way that they were able to be defeated and that's just it we have to constantly look at how we're doing security our organizations and to the wider field at large so that we make sure that we're adapting to things like this that we've known about for several thousand years couple thousand years yeah so data breaches that this is not something new this is something that I you know follow myself or other religiously so for here you
know we had back in 2005 there 40 million records were to him out this was huge news at the time to be followed on by Heartland Payment Systems in 2009 this was another massive data breach and this was really amazing because at that time these were big numbers we flash-forward today this is not even something that people would consider newsworthy so this was a lot of the problem as to why a lot of data breach data breaches databases rather had XP command shell was something that was built in as a script that would allow remote management of a database this was something that was built with all the right intentions but the law of unintended consequences being what they
are a lot of these databases had this enabled and they were publicly accessible so data breach after data breach started to happen and one power company that was working at I had sat there while we're having a penetration test on and I saw them trying to do this and I had actually disabled that I called them up and I said you had a nice try and they're like who told you that we were doing that they were actually shocked that we were checking our IDs system to see that something was actually happening that was more telling than anything else that their customers usually didn't monitor their own systems and we've seen other companies that will remain
nameless over the years that weren't actually monitoring the systems they had in place and this is something that we can fix it's within our power so XP command shell was a big thing back in the day but if we jump forward to today we're thinking we're talking about things like s3 buckets so on AWS they have thing called s3 how many people here by a show of hands are familiar with s3 buckets okay cool for those that you don't know please look it up this is really interesting it's a data repository that you can spin up through a web interface you can put image files you can put text files whatever it happens to be into that
repository but unfortunately a lot of times people are putting it up there in such a way that is publicly accessible because it's easier for them to get their applications working a bit of a problem because those things can be iterated there are scanners that are freely available on github you can download and you can run them against AWS not that I recommend that but you can find open resources all over the place and a lot of data breaches in the last year have centered around this the really interesting thing about this is with regards to these AWS s3 buckets is that they are locked down by default they are private by default I don't say
that again private by default unfortunately people enable them because they don't quite know how to put in the proper rules and whose fault is that as security practitioners it's our fault this is one of those moments where you have to take that sword and put it against the tip of our ear put the tip of the sword against our chest rather and lean forward because we need to own that mistake because we need to do a better job of educating those who are enabling these things because I guarantee you nine times out of 10 those aren't security people that are allowing that access and the breaches just keep coming there's all sorts of these not to
say that this was a sequel injection attack or anything like that but this was just an example of this can happen to literally anyone but the funny thing is is with the data breaches we tend not to pay attention to it until it affects us personally this is really an amazing thing when you think about it so for example if you are out and about and you leave your door open because you're used to doing that and wherever it happens to be that you live and somebody breaks in steals your stuff all of a sudden you feel violated at that point what would you do put an alarm put in all kinds of different controls why weren't those controls in
place before I'm not saying you have to go out and put an alarm on your house but at least lock the door these are you know the risk discussions you have to have because the data breaches are going to continue to happen much like home invasions and all the rest of it it's not something to be afraid of some to be aware of something to be dealt with in a proper fashion because data is no longer or other currency is no longer anything other than data data has become the currency of the day and what slide presentation would be complete without you know the requisite AI nonsense so this is really interesting because there has been so much discussion around AI
and how it can be used by attackers but the funny thing is the attackers don't need to use it because we continually leave vulnerable systems exposed to the internet we're continually leaving systems with default credentials that are freely available and easy to find this is something that we can collectively do a better job to help mitigate but that being said the problem is going to happen so a few years ago I like one of the things I do is I work on speaker operations for DEFCON and we were trying to get set up for a DEFCON into the day before we had the DARPA cyber Grand Challenge was on the stage at the same time so each one of these
systems across here was a supercomputer and liquid-cooled you should have seen these huge cables behind it was absolutely massive so we had to pick our way across the back of that but each one of these systems was attacking each other one of these systems created an exploit to use against the other systems that nobody had seen before so the ability for a supercomputer to cause real problems yes AI to cause real problems yes it does exist but honestly we're not at the point where we need to worry about that yet most AI systems or most companies that say they have an AI systems tends to be it will glorify it if-then-else statement but you know I
might be jaded yeah and case in point when the Equifax data breach happened this was really amazing everybody was going on about the vulnerability and the system that oh they got exploited that uh Brian Krebs went out and found this this was a web interface that was available and I believe it was 26 different countries with default username and password where you could get in you could get all the exact same data you didn't have to run any exploit you didn't have to drop any zero-day there it was this is one of those things the law of unintended consequence is a rather remarkable animal so when we're talking about security related issues we are looking
at unauthorized access insider threats and yeah everybody likes to go on about that web breaches and oh right what's the one thing that we never really talked about too much is the missing patches so a great example Oracle databases when's the last time you placed a hat or your organization installed Oracle database patches security patches so this is one of those things a lot of the organizations I worked at over the years we come up and have that question whenever we had a penetration test done and they say oh yeah we got we really own about two years behind it this would absolutely drive me to distraction but it can be better than that but one of the things I
really do enjoy is a lot of popular culture so one movie rogue one that came out and if you haven't already seen it there's some spoilers in here and it's been a while so I imagine everybody's seen it so this was a great movie for talking about data breaches so in one scene we have the firewall admin here he's trying to gauge whether or not the rebel ship that's trying to gain access into their planet is legitimate like wait a second that's an older code why are you here you're not scheduled to be here and they're like yeah no no it's cool we got redirected so you know we're supposed to be here we got to pick up
you know something for Bob okay well then they said send the legitimate code so there goes the sequel injection and then oh they popped the box they have now gained access but once they've gained access the attacker really has to go okay how can we go beyond what we already have so they have to escalate privilege and as they're going through and they're gaining the extra information they are really doing a lot of damage to that organization and it's not until it's too late that we see the indicator to compromise once the bombs start going off across the base then that's a real problem seriously get that but by that point the damage is already done and the data is
already leaving the building but what was the ultimate lesson from all of this oh there it goes what was the ultimate lesson for all of this encrypt your data so all of this data they had for this mass of Death Star was not in an encrypted state but data breaches have been something that I have been rather passionate about for a very long time so back in 2012 I started tracking them on my own site liquid matrix and I went through and this was really amazing at that time LinkedIn as an example of 6.5 million records were exposed this was big news back then today we have orders of magnitude of a billion records what does this tell you
one we need to do a whole lot better job at securing our data but to static usernames and passwords it really something that is a something that we have to move beyond and I know what I'm talking about years ago I was part of a company that we got breached I came into work in the morning and I sat down at my desk I had my coffee and I went what's this there was a stack of notes on my desk for various media companies that had called talk to me about the data breach and I was like what data breach looked at my phone 27 missed calls fantastic this was really disconcerting now this was a system that was a
deprecated system it was running an old vulnerable version of WordPress and the funny thing was is two weeks before this data breach we had to talk with a group that was managing and we said could you please do something about there's either Patchett or take it offline they're all it's a deprecated system we were actually retiring it and we're like fantastic two weeks later the funny thing about this was it wasn't I don't blame them for not taking it offline I blame myself and my own team for not following up and with security you have to constantly be following up trust but verify and then verify again because the attackers are going to keep coming in my
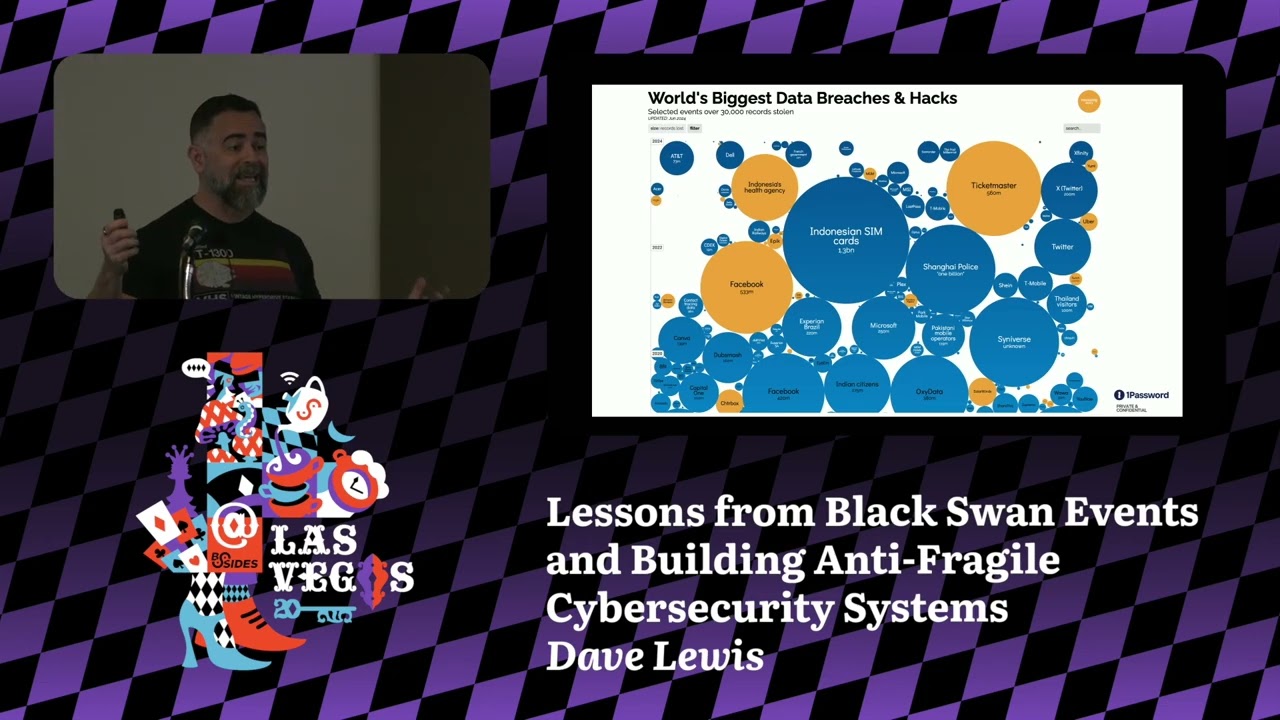
previous job one of the things that we did we did a state of the Internet report that we go through and look at all the data for all the different types of web attacks and quarter-over-quarter these three were always the same sequel injection local file inclusion cross-site scripting we're always the top three attacks why because they worked specifically sequel injection work time and time again now this is from a site called information is beautiful net if you're not familiar with it I definitely suggest checking it out if you're into data visualization like myself so this was two years ago this was their graphical representation of various data breaches the colors just indicate you know big stories of the day
now we jump to just a couple months ago and now we have this and the reason they did this is because they couldn't fit it all on the page anymore they had to change the way they were representing the data disconcerting no and it really feels like almost everybody out there wants to have a data breach and this is troubling on many ways because I do some work on the side with a company a boutique firm called psyche osis and we went through that we looked at data breaches and a lot of the companies that were reached actually almost exclusively all of them saw a bump in their stock price after the data breach happened
that was a bit disconcerting and I don't know if it was people figure out lightning can't strike twice or what the kind of logic was there but it was really odd to see that data in front of us now you want to make sure that you're having proper security controls in place you want to make sure that you're limiting access to resources you want to look at network zone segmentation this is something we have been doing for years or should have been doing for years I worked in one organization about 10 ish years ago we had a flat network with MPLS circuits spanning the globe I could sit at my desk in Toronto and I
could query systems in Kuala Lumpur and nobody knew that I was doing it because they didn't know logging turned on we fixed that rather quickly thankfully but you want to make sure you have the proper security controls in place not all security controls are created equal and we have to look at the things that we should have been doing all along because bad things can happen this is a great example all of these systems compromised using a vulnerability we had known about for 10 plus years here's a pop quiz Oh wasp top 10 how many people here can tell me how long sequel injection has been on the top 10 there are no wrong answers you can just shout
them out anybody I heard something over there but I'll go with forever yes from day one basically why is this happening this is something we have within our ability to fix if you sanitize your inputs and you sanitize your outputs that problem goes away or at least is mitigated I should say so how much is it gonna cost the reality is is you're going through and if you have a data breach in your systems there are costs involved the cost of investigating the incident look at the number of people that you are committing to tracking down the information to remediating the issues to going through and saying what actually happened there is a cost for
each one of those employees that are spending their time when they could have been doing something else to remediate some organizations that is not a cheap thing to do one power company that I worked at quite a few years ago we had one volunteer we found well they had hard-coded usernames and passwords in their human interface HHMI this was absolutely maddening we asked them to fix it they said sure there'll be $250,000 it's like wow that is a Canadian dollar so it's a little bit funny money but there is a absolute cost to recovering your systems look at Sony Pictures in an example they had their system compromised all of their systems were wiped they
went down to bare metal they had white boards in order to get work done can you imagine that happening in your own organization that you were reduced to using white boards and typewriters now you got to communicate with the external audience when a data breach happens if you're a publicly traded company you have a fiduciary responsibility to communicate with your stockholders there is a cost to having that communication set up external PR firms internal PR firms all of that sort of thing what are the legal costs gb PR is always a fun one but I'm not going to go there and compliance penalties in some organizations out there they find it cheaper to pay the penalty than it is to
fix the problem I'm not going to name anyone but this is another thing where we have to look at and go this is a problem you got to worry about the loss of revenue so in one organization I was working at where we had that data breach luckily that particular data breach only had 192 accounts on it and thankfully none of them were on the rest of the network but still the reputational damage was done that same company we had an email go out that should never have left the organization it even said on the email do not share this externally within two minutes of that email being sent around externally it had left the
building 27 times our stock price dipped and it cost the company millions of dollars in a space of five minutes you got to worry about customer attrition are you gonna lose customers because of a data breach something consider and like I said your stock could be affected and there's other costs too so for example here Verizon was going to buy Yahoo and they Yahoo had not been 100% forthcoming with regards to their own data breach once this came to light that took 350 million u.s. off the price tag they said no we're just going to drop the price and they said yeah we got us we can't do anything about that this is a real danger and there's other
companies do that'll say oh we don't have to do encryption because we are not legally mandated to do it or you could do the right thing and not have to worry about it after the fact when the lawyers show up with their pointy teeth so in the sari jetlag just caught me there in the Equifax data breach this was amazing who got the pink slip in that particular scenario let's go through the seaso who have made 11 million dollars in four years I'm in the wrong business was retired the CIO I'm sure CIO was fine nope CIO retired well I'm sure the CEO was able to take over and have no problem their help CEO
retired with a 90 million dollar u.s. parachute now imagine for a second if your entire C suite was wiped out just like that how would your organization be able to recover this is the thing when we talk about data breaches it's not just a case of haha they got popped that doesn't do anybody any good you have to look at the bigger picture how is that going to affect your organization how is it gonna affect your customers your end-users your citizens whatever it happens to be and it's not just Equifax to balance it out here's an example and hopefully this works yes TransUnion they're one of their competitors the next day was trying to install flash on
systems but it wasn't flash it can happen to anyone so one of the things that in all the roles that I've been in over my career I have had the benefit of doing different types of jobs I have worked as a penetration tester I've worked as a C so I've even done compliance now the really interesting thing is compliance can be a friend for you in your organization I know most people roll their eyes in the back of their skulls until they crack but they can often be a balance and that's just that you want to work within the different groups within your organization in order to achieve a common goal and if you can get them on
your side this is a great idea often compliance is the adult in the room so I remember one time years and years ago I went into the CEOs office I said we have a problem this Euler system can be remotely routed and we got to buy this particular tool in order to fix this issue bla bla and the CIO looked at me and he said well what's this going to cost anyone I didn't know how to answer it and that's just it it's incumbent upon us and security practitioners to learn how to speak to senior management in terms they understand they want to know about risk they want to know about costs these are the things that are going to resonate
with the senior management now mistakes can often happen now back in the 90s I was working for a defense contractor in the US which is odd and that was a Canadian but there's nothing entirely so in one particular scenario the customer that I was working at was under attack over and over again and I kind of lost my cool and I hit back the organization I went after I got into their system I left a note I didn't destroy anything I didn't take anything down but I left a note on the desktop of the particular system and I said these are the issues if you want to drop me here's a burner email address you can
send me a line two days later I got an email it said hey really sorry about that but that wasn't us that being said thank you for pointing out the various vulnerabilities and cataloging for them in there's no we were able to remedy that and we really do appreciate it to this day I still cringe when I tell that story because that could have gone so much worse I had gotten one of the octet sin the IP address wrong when I went after the system I screwed up bad I got away with it I'm lucky never think about hitting back because it doesn't work because mistakes can easily happen and it literally isn't result like it isn't
just you vendors can do this too so one organization I was working at we had a vendor come in they were a vulnerability scanning vendor still around today and leave it at that they said look we have this great tool we'd love you to try it out we'll do a scan of your systems for free just so you can see in inventory and let us know how it goes sure no problem here's a Class B they want what well we're a power company we just have class B's in there ha damn it so off they went they scanned the Class B came back with report and they were good enough to print it out because they
wanted to kill trees report was about this thick and I was like wow that's crazy I started flipping it through and I'm like Shanghai Chongqing Beijing hold on we don't have any operations in China printer printer there's a lot of printers available in China and then it hit me they had done the exact same thing that I did years earlier working for a defense countered that one of the IP address part wrong they got an octet wrong they scanned an entire class P in China and like oh you may have just committed an act of war congratulations they were so embarrassed they were bending over backwards of like please don't say anything about this don't blog
about this I'm like no I'm not gonna do that because why I've done the same thing this can happen to anyone that's why you have to be really careful and you also have to be careful to help educate people on how to do things properly when you're talking about teams in your own organization you want to make sure that you're sharing information with them in a sane fashion or things like this will happen this was one organization a another power company I was working at they had an app that went live and they said they had bypass security entirely we hadn't had a chance to do a review and they came to us about an hour after it went live and they said
look we'd love it if you could do a security review okay sure no problem we'll go first thing I did is I opened up a web page this is not the web page I did view source right there see that one right there that right there I did view source [Music] can you imagine what I found commented out in the HTML the person who yelled password is correct not only a password username admin password password I'm like are you kidding me right now and then I went wait we hadn't had to talk before they went live I'm not gonna beat him up too badly so we sat down myself to see so and the program lead that was dealing with this
and this was his reaction you hacked my application okay let's go back just a second here I did view source on a web page and apparently I hacked his application and I was about to go off I was about to be this guy and then it really hit me at no point had he ever had a conversation with us about what our expectations were what our requirements were what security should be like so rather than blowing my foot off I sat down and had a reasonable conversation with him and he got it over much gnashing of teeth but that was just it my initial reaction was you [ __ ] no that helps no one that absolutely
does nothing to further the conversation now sometimes even when you fix an application even time when you fix things in your own organization they can become unfixed so that organization that I got the data breach notice that was pop we had one server that we got them the lock down that was unrelated to that and one said okay great we it was such a huge fight it was months the rhythm to secure the system two weeks after I left I got an email from a co-worker former coworker and said you're not gonna believe this so the developer site and then the command at the end was slash Etsy password had complete accident well complete visibility to all the accounts on the
system they had undone everything we had gone through to help them fix now when you're dealing with users when you're dealing with organizations in your own company you have to understand that people are going to use tools in ways you never imagined and sometimes they'll ask for tools that do absolutely nothing at all they look pretty but you want to make sure that you're making effective decisions for your organization and the wider public at large because bad things can happen this is not to beat up on this company but the first time I ever did this talk this happened this is a kept site called your data is secured calm they had their entire sequel
database on their front page this was two hours before I gave this talk I was like screencap now my friend Bob Lord he now works for the the Democrats in the United States he used to work for Yahoo and several other but he was there during the exposure of the data breach and he had to live through that and ultimately got hosted and hosted on his own petard but he just happened to be the poor guy that was left to hold in the bulding the bag at the end and he said going through a data breach feels like vertigo and he's right when I went through the data breach where we only had one hundred ninety two
accounts exposed I felt horrible I didn't sleep for days the real effect of the organization II not really there but you take it personally and sometimes things happen and you don't expect them to happen like when the Morris worm got out this was never supposed to do what it did it caused all sorts of damage and we tend to look at things in a very much in an adversarial array is like oh it must have been an attack and when we tend to look at everything as a nail and we only have a hammer it tends to be a really bad thing but as security practitioners we have a really bad habit of becoming our own worst enemy we tend to eat our
own and as a community and building a community much like we have here this is something where you help to build each other up because it can be so much better when you're looking through the types of things that you need to deal with in a data breach there are all these different types of groups and organizations that you can work with to build out you don't want to be that individual standing there with a flaming sword of justice saying the answer is no you don't want to be the person with the mantra of how do we get to no because that doesn't work now the other organization you really want to deal with audit nobody tends to
like audit very much I worked in one financial organization institution rather we had 55,000 employees and we had an audit team of seven people and they I swear they just wanted to have my Pelt hanging on a wall because they were never trying to help further the goals they were always trying to take me and my team out and I found this very disconcerting and then I went away and I thought about it for a while and I thought how do I make this better so I took the lead from that audit team and I went out and had a coffee with him and we sat down we talked and after a while I realized the way to
work with them is to work with them as opposed to an adversarial relationship which had done no good up into this point and I said look how do we do a better job at our job he looked at me and he was so incredible that he actually rolled back in a seat and thought about it for a second and then he can started coming up with ideas and that helped build that dialogue where we were able to improve things because as you're going through this you want to have allies within your organization to help better secure that organization because when the bad news comes you want to be able to better communicate it internally as well as externally as
required the vulnerabilities are going to keep coming making sure that you have something along the lines of either zero trust infrastructure to help mitigate that great I'm not caring about a zero-day I'll be honest when you hear news about a zero-day it's amazing how much churn happens as a result of it how many see executive suite executives are saying okay I need a meeting with you to discuss this understand the risks and all the rest of it we're great okay well we don't have that particular software anywhere in our organization oh yeah but we still need to talk about it because we need to have visibility we need to understand in case the board asks okay
that's a lot of waste of time the thing that I'm worried about is the hundred a vulnerabilities the database patches that have not been applied for two years these are the concerns that I have and these are the things that we need to help better address so a lot of the questions that I get when I have this sort of conversation is where do we start and most people don't know where to begin honestly you start where you are do you have a risk register within your organization that is a simple one tracking the vulnerabilities the exposures in your organization and having some sort of plan in place in order to address them this is remarkably
absent in a lot of organizations you want to look at how are you doing patching within your organization are you worried about a low level patch or are you worried about a critical patch or what is your risk appetite are you doing regression test matches my favorite are the individuals out there they like oh we got to patch it right now and I'm like okay wait that is a power system that has been in the field for 30 years and order to patch it we have to take it offline for six weeks yeah it doesn't quite work out that way you have to have some sort of compensating end rolls as well as a plan
on how you're going to mitigate that because not all systems are created equally you want to figure out how to stop the threats earlier you want to have some sort of anomaly detection in place to look for these individual threats and how are you going to address them how are you gonna even know that they're there I love this cool breezes coming through the window right now sorry sidebar thank you for the person who opened the window a lot of times in organizations they people keep saying you want to innovate you want to innovate you want to innovate but how do you innovate if the plane isn't already built yet how are you going to deliver
that if you don't have that structure in place security isn't there to stop people from doing things badly we're here there to help secure the business to do things in a safe and secure fashion and you want to do it in such a way that you're seen as a value add as opposed to detractor because historically too often we were seen as the flaming sort of Justice the detractor the one that was saying no to everybody that doesn't help we can do a better job than that we also want to make sure that we're managing the narrative the media loves to take hackers and that term rather and smear through as you know these horrible
horrible people people but sometimes we really got to stand up and say something because this was a few years back where CNN went on and talked about a hacker named 4chan that had compromised that excuse me a hacker named 4chan that had gone through and caused all the trouble things like no that's not how this works all right so in as I started winding down I'm gonna talk a couple of war stories in one that one organization I mentioned earlier we had this global network that was MPLS circuits as far as the eye could see and we got a notice from an American organization call the NPA and also another one called RIA and they
said that we were illegally downloading music as well as movies and we went what on earth are you talking about we have no interest in this whatsoever and they screamed up and down and their lawyers for causing us all sorts of heartache and we're like okay there's something very wrong here this couldn't be happening we are looking at her firewall logs there was nothing to show any of this sort of traffic in a certain country in Southeast Asia we had a facility where we had one of our team was there and we had him do a physical walk-around what did he find he found a subnetwork off the core router that the locals had built so that
they could bypass all the controls so we were looking at the logs for the firewall which was fantastic but we weren't looking at the edge routers epic fail on our part and this is one of those things you want to make sure you're looking at the right things you're learning from the right information sometimes things that look good can also be a curse intends to how you're gonna balance that out another Power Company they worked at years ago this was a great one we had this bizarre routing error that was happening we couldn't figure out why we went through we started going okay enough finally we have to go out to the floor and start
lifting tiles so tile number one got my tile lifter nothing there tail number dude okay this is an all in front of all of the networking racks title number three oh hello there was a Cisco 1750 under the floor going high nobody knew why that was there nobody knew what it was connected to within a couple of hours we were able to figure out that this was part of another company now backing up one step our company used to be part of a larger organization that was split into five separate companies one of those companies was sort of a competitor and that was a direct connection back to that company Wow we lost sleep that day
but the really interesting thing is we talked to our friends over at that organization and they didn't know it was there either they found a similar 17:50 onto the floor and they went okay let's just unplug this and make sure that goes away constantly have to be looking for where these issues can crop up security issues can find you in the most unbelievable waves and not because of any malicious intent that was something that was put in place I'm sure for a logical reason years ago but when the company is all divested each other nobody caught that part you want to make sure you document everything you want to make sure you're clearly communicating with everything everyone and you want to
make sure that you're working with other organizations within your company or your education or government whatever it happens to be to make sure that you're sharing that information much like you have here today with b-sides you have an ability to interact with your peers take full advantage of that contribute back to this because this is something that can grow these sites Toronto started in a horrible greasy bar near one this I would have loved to have had this when we started that being said I would like to say very much Chuck and thank you very much for taking the time to listen and thank you for having me [Applause] and a huge thanks to the b-sides
organizers and if there's any questions yeah there any questions all right I have one question for you you mentioned that there's a lot of the communication and we wait for something to happen rather than act proactively we want to breach it would seem to to the alien observer who understands IT but mouths humans it would seem that we want breaches to happen so do you think that if we if we could find better ways to quantify risk maybe instead of using something like a risk matrix would that help or yes I would absolutely help you want to have a way to communicate to the wider audience because we got to stop assuming that everybody not in security
understands what we're talking about we're very good about talking amongst ourselves in our own lingua franca but we're very poor at communicating it to a wider audience that does not understand what does zero day is or anything to that effect anybody else better question any question no okay oh oh there's one all right coming down and also if you don't want to ask a question in person you can always email me I'm totally up for that so you said ten years ago we were talking about millions of Records breached and that was scary now we're talking about billions do you think at some point of time in the future there will be so many data breaches that
nobody would care anymore I honestly worried that we were at that point we are now getting numb to it and that does really concern me static usernames and passwords are something that you know for all intents and purposes started in 1962 with a program called CT SS at MIT they were using it to help control people's access to super computing time so that people wouldn't steal time from each other because each student had four hours allotted to them and that was a reactive control today we're still using passwords as a default method to help secure things and we also do a poor job of securing our infrastructure large because we want to do everything faster
better all the rest of it but often security gets overlooked so yes I think we are at that point where you're now starting to get numb to it and I also think it's time for us to get rid of static usernames and passwords and to a far better job of getting back to the core fundamentals to secure our organization I hope that answers what you're out I think bus cordless is a future absolutely web authentic uppal weeks ago if you don't actually that's a great example if you are not familiar web off n go look it up this is a great standard this is the next step for password list authentication and no I didn't pay him to say that yes we have
sorry we have somebody over here hi thank you very much for the talk I'm a developer so I'm approaching this from a developer perspective and when we develop applications we often add security as an afterthought so we develop it first we ship it and then someone says hey like you said this s3 bucket is publicly accessible so how do you sort of change that mentality so did we develop with security first instead of after I completely agree so caveat I'm not an example for me my first job in IT was actually a rapid application developer so I started out that but on the side when I was at home at night I was breaking into systems because you
know that was the thing to do the thing that I realized is people were not communicating with developers what security was and I sort of bridge both worlds so that I had some inkling towards it and I started doing more investigation into that and that was one of those things where yes developers we have to stop beating up on them because we often don't share what we expect in advance and that's just it when something goes wrong we're like what you should have fixed that that doesn't help so yes we as a security community need to do a better job of communicating what we expect of them and what those standards are to better secure them I
hope that answer okay great yeah all right wanna make sure there's time for the next speaker to cut up yeah sure we have a small token of our appreciation on behalf of the besides organizers and everybody here I'm sure as a foreigner you get our special gift which is is a a book written by Norway's favorite Canadian actually Julian s Braille so from from two Canadians to another there you go thank you very much unfortunately since you're leaving at the 1:30 you won't get to see any Norwegians smiling well oddly enough they resent they resemble Canadians thank you very much [Applause]