A few tricks to Anonymizing your Red Team
Show original YouTube description
Show transcript [en]
uh welcome to my talk where I'll present some ways to anonymize and improve your testing I want to thank the team here at b-sides MRC for not only giving me a chance to speak but organizing this conference technical teacher all right the agenda this talk is going to cover uh things both from the threat hunters and attackers can do can use to do their jobs better the agenda will talk about the basic building blocks to get an honest infrastructure uh testing active tests that can be anonymized such as dropboxes that give IR nightmares unmenable side channels for those dropboxes social uh engineering with breach data burn sites and avoidance then VPN and tour signature avoidance
and then we're going to do a quick Story Time as a quick way to walk through highlighting the items that we talked about today first of all no companies were harmed in the making of this talk no security vulnerabilities are exploited or discussed these are just the things the way they are in the public domain completely accessible completely passive no active reconnaissance was done no penetration testing at all right who am I I've held numerous roles in I.T which in general helps me and my current role as a penetration tester uh since you really can't be a good penetration tester without knowing other aspects of it I hold a number of Industry certificates which so that I
can improve impress no one in this room I'm a hobby farmer beekeeper and overall I try just to be a force of chaotic good all right uh this talk will help you with a zeroscope in engagement that is an open scope engagement that places all employees infrastructure and third-party vendors as possible Tax Services this is against a client that has a more advanced capacities for Discovery and detection uh or any security job that needs a level of anonymous between you and the targets uh for later in the talk our fictional client will be a the energy Supply Group as we know critical infrastructure is under increased threat actor pressure so it's a good one to
look at but where to start oh I said this right because this is going to be important later on that you remember yes all right uh back in 2019 I spoke about how to create Anonymous companies and profiles by abusing the broken trust model of the internet a lot of those methods and comments still work today that talk looked in detail about the creation of the anonymous proxy accounts infrastructure services and companies foreign engagement uh you can look at iron geek's website for that talk uh where I can't go into details here you'll notice between that talk and this talk I still need help with memes and coloring but it is what it is before we look at active attacks that
can be anonymized I'm going to summarize the three key components that you're going to need to anonymize your infrastructure and first of all we can have this conversation later at the after party but cryptocurrency is not anonymous anything with an open registry is not Anonymous so but essentially prepaid debit cards are the internet's version of cash uh the cards that you want to avoid um are the ones that say verify ID those are normally the rechargeable ones um so if they say rechargeable or verify ID they're going to want your SS number so don't use them so any other kind of gift card will work you use services that you can use prepaid debit cards
with or anything that's a prepaid service and that's Services where you pay up front and then your usage takes away from the balance you can acquire email vmcs vpcs voice over IP Services all using the prepaid debit cards um they say you cannot purchase monthly services like Gmail or business Gmail or 0365 that's not true um I don't really do I get blocked every once in a while you do uh AWS and azure the last time I did it it was tricky and it required breaking actually the payment flow uh so really don't try it well you can try it but it may not work uh other major vpcs uh you know digital ocean Etc they all work with prepaid debit
cards so no problem there stick with them uh just have enough balance on the pre-card for the length of the engagement or you're going to have to swap out cards and that can get messy normally I find 100 to 200 on these cards are good uh because of the fact that it should get burnt 200 isn't really a big thing I got this one actually from The Talented guys at Black Hills from a talk earlier about a month ago or so the AmEx cards actually are a closed Network I completely forgot about that uh so it's less likely to get flagged by fraud so you could try uh an AMEX card with a a monthly service
all right uh you're gonna need a VP uh VPN uh either as a threat hunter or an act hacker you just need a VPN uh two providers that I know work and allow for anonymous purchases uh private internet access takes gift cards or prepaid debit cards uh they require an email address but just use a burner email address uh you buy a full term one year three years it doesn't really matter the one I really like is mobit it's you can uh you sign up you get an account number that VPN service is excellent uh you can mail cash to Sweden or use a prepaid debit card you can actually buy a service card for them on Amazon
I looked into this because it got me concerned uh but there's really no uh association between the account number and the service card so that's also a very convenient Factor all right uh personally my house all my internet traffic goes out one VPN service using PF sense then I use a local VPN agent on my dirty equipment uh dirty equipment is just equipment I use to do my threat actor uh stuff it's just a different provider vendor there is tor but this is useless for the purpose of this talk activities that were where we're looking to remove at a station between ourselves and the Target and not raise red flags social media companies are entrusting when your IP address
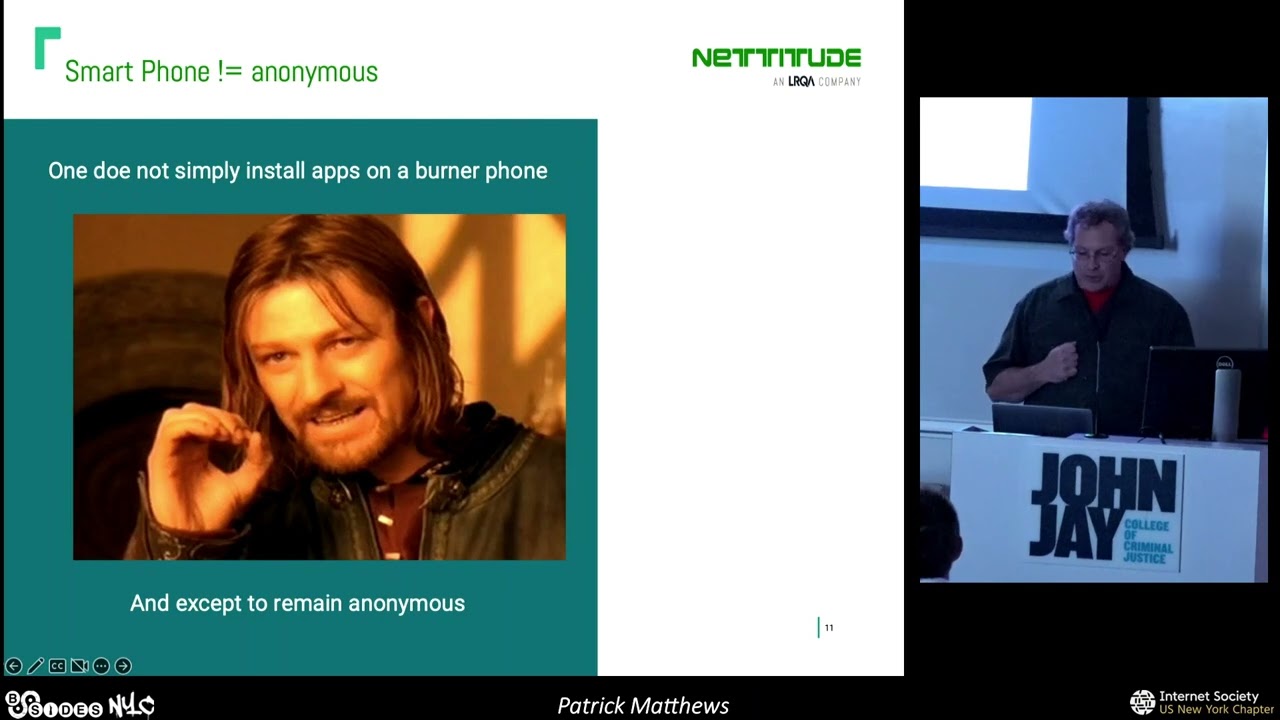
comes from the tour and points and VPN Services firewall vendors now have rules that block torque inbounds they're using the same tour endpoint list that are published however there are ways to bypass uh the last building block obviously is a burner phone prepaid monthly cash recharge cards major retail outlets Target Walmart whatever the burner phone gives you a number in the geographical location of your choice nothing will burn a vision attempt quicker than calling a company outside the geographical location or the area code number uh having a burner phone is the most uh uh is it a must when you're looking to create these proxy social media accounts or getting other internet services smart burner phones are still the
easiest way to get the proxy service accounts
start my camera all right uh smartphone apps simplify keeping social media proxy accounts without having to send your ID or tilt your face when you're all your traffic goes out a VPN endpoint and if you've ever used Facebook for a long time you know that all right uh remember LTE is not Anonymous or are smartphones smartphone apps will never equal Anonymous you can remember to disable the tracking services and other trackers but you're still trusting the OS and the apps not to take that extra data that will disclose your geographical location or any other data on the phone remember to use your separate burner phones uh and your social media accounts for engagements because frankly metadata
kills in all things remember your metadata between your phone numbers your accounts your infrastructure that you use threat Hunters have adps profiles on penetration companies besides threat actors thread Hunters have several different models to correlate and share the metadata it's beyond the scope of this talk to uh it's beyond the scope of the talk to talk about this but as attackers we need to be familiar with the models beyond the Martell attack framework as attackers we can use the threat Hunters intelligence Feats not only to see if our metadata May tip off a Target before the engagement starts but what threat Hunters are currently seeing and focusing on all right that is my 10-minute summary
of the other talk let's look at some active uh attacks that can be anonymized all right drop boxes I'm so glad that we are able to do physicals again all right to get into environments all right we have some real choices to give IR some nightmares with dropboxes or fountains we all have our favorites the device I prefer is the Nano R1 Pi why it has dual Nicks for duck walls 2004 Mac Bypass or just appearing as a man in the middle of the MAC address of the device that is a must if you're going to be placing a device on the network it has an internal 8 gig memory storage an SD slot Wi-Fi Sports and boom core
and a dual USB ports if it came with Bluetooth it would be perfect for deployment but it is what it is a small factor form makes it a pretty conceal I did say self-destroying and I'm not talking about lithium because that's just not safe for life and limb all right uh when you have a pi unit with an SD card the typical IR response is to plug in a console cable or take the SD card both of these events can be monitored for when you have a device such as this uh where the real OS is actually running from internal memory so what needs to happen is to monitor if the SD card is mounted at boot time
and with a Cron job that runs say every 60 seconds or so that looks and checks to see if the SD card has been removed if that event is triggered you just start wiping your configuration files that disclose where your data is going at the point it's done just reboot to kill any artifacts in memory the same thing if you see a Serial cable getting attached you could destroy the debug ports before deployment but that wastes a hundred dollars and while I'm cheap all right uh don't forget to place a fake OS and config on that SD card uh the Nano R1 will boot uh first from the internal storage so there's no issues about
worrying about the wrong image being booted from all right uh for more details I actually have an article at natitude's Labs uh with the details of how to set up this device the proof of concept scripts for a external egress the Wi-Fi side Channel duck walls uh Nat bypass and the self-destroying script um and depending on the client and engagement I use several different methods for egress Communications but first i'm going to talk about the issues with LTE and then we'll discuss some side channels three of them that are currently unmonitorable and one that is detectable all right even if you're using cash to buy LTE Services it's going to be tracked at least to an area in a
geographical a general movement by cell tower triangulation the eef and others have some really interesting reading uh on how the government violates the spirit of U.S constitutional law by buying from third-party data sources like cell phone tower metadata and other metadata you add in safe graph and a number of other data Brokers and LTE tracking is a trivial matter you may not know who but you can associate where that device has been I should say that the FBI called an oops my bad after they got caught and claims to have stopped buying uh this type of data without a warrant but what about all the other three-letter agencies that we have in the government including the U.S Postal
Service I guess based off of reports a few years ago as a side note uh there are other ways to track a target with the same concept as an air tag you've probably read about that look at pet tracking devices they're waterproof and they work just as well um but it's obviously not always legal unless it's your kid then how about it it was your kids make the perfect test subjects when you're looking for tracking devices and methods you know all right this is from uh the FBI presentation in 2019 on cellular information it's a little small but uh this uh slide shows the retention period of text messages internet surfing and other uh things on cell phones uh by the
different providers um again this is talking about the right target you know this isn't the mom and pop shop that you're running but this is uh you know you need to be smart about where you make your purchase of Lte modems and where to your model once you have one that's working buy it when you're in the geographical location if you target turn it up they won't ever see the transportation from your home or whatever all right let's go all right talk about slide channels now the following two site channels are not really useful uh as a side Channel Beyond on-site configuration and operational confirmation of the Dropbox um both are currently unmarchured so it's a
good choice for this purpose because frankly there's nothing worse when you get a Dropbox that's not going to call home and you have to troubleshoot it Bluetooth SSH over Bluetooth is supported by a number of pi devices now its ranges about 30 feet to 300 feet depending on what you read and Equipment you have but you can figure it's about 30 feet it's not really practical Beyond accessing during deployment but there's lots of documentation on the internet on how to actually get SSH over Bluetooth or a Bluetooth personal area network zigbee uh same Wi-Fi also in the 2.4 gigahertz range to be honest I haven't really had a chance to play with it because I haven't
seen the Practical use for it uh I'm self-funding a lot of my research and well the wife and kids they like nice things too uh everyone can say well it's me and that's my impression of Prince Harry that's right I work with UK people they didn't like that joke either all right Wi-Fi uh it's a fair range use of a jagger antenna does improve it into being an operational range to make it practical as a side Channel when you're in the geographical location however many vendor products uh have some form of Rogue access point detection and some can actually Jam if you're required to use it I would suggest that you monitor the e-sids in the area before your
deployment and figure out how to blend in um and I should say while it's not a side Channel I did mention about S Tunnel um if you're going to send a reverse SSH shell out your client it's a requirement Network look at using an S Tunnel wrapper and a Cron job to turn up and down that tunnel during business hours the S Tunnel will hide the SSH traffic from devices on the network detecting it all right now actually let's talk about the one unmonitorable device that is actually untraceable and it's actually practical to use once you overcome some limitations all right low Roth low range radio it's approximately six miles with the right position equipment it operates in the
unregulated frequency band of 954 megahertz in North America uh Laura is a physical proprietary radio communication technique that uses low power but long range it's mainly used for iot devices and sensors where the distances of operation in these environments are great and harsh it's ideal for sending receiving messages uh they're receiving the small messages that sensors iot devices or PLC type of devices use all right it has end-to-end encryption asterisk that with uh depends on the initial build design and the protocol version you're using the newer versions actually have addressed those flaws when using low raw for nefarious site channel it's important to remember that it's a Serial protocol and the packet messages are small and it's half duplex
to effectively use you're going to be writing your own custom programming but since the adapters serial devices is Trivial um so two ways to operate is a gateway adapter in my testing the range is a half a mile to about two miles uh where I live and testing in Albany the mode of operation allows for multiple devices to connect but that's really not important unless you're going to deploy multiple dropboxes in a site uh you can use a public low raft Wan service but there's obstacle issues with that which can be overcome for example the low raw server provider the thing Network offers a free 10 device account it requires a credit card and an email
but again prepaid debit card and a burner account and you're good to go uh this service has some interesting features and add-ons that actually make it very functional for a team to work off of a Dropbox this way it has authenticated mqtt it has multiple endpoint services for mapping so the functional range and the number of people that can use a Dropbox uh let's see you can self-host a low raw lion server there's a number of Open Source choices um or you can get a device that has it pre-installed using this setup would all but be untraceable but you will need to answer the questions for field deployment such as the power of the Gateway and the internet connection
personally I don't have it on me but it's a hollowed-out rock with the solar panel to power everything and the battery pack all right oh yeah well you're thinking um well the Gateway with an LTE uh will uh in the power source it's very practical uh if you're thinking well I just say LTE is bad it is but again the Gateway device is going to be deployed up to about two miles away from the Dropbox all right the other operation mode is point to point again several vendors have point-to-point firmwares and there's a standard for point to point low raw same operational issues with the Gateway setup as far as power et cetera there are several tools that have been
written for providing TCP Services over Laura but essentially what you do need is just to install the ax25 protocol and you will get TCP Services running so you can do your SSH into the box all right one of the features of low rope hero that helps it to be used as a command and control method is the F Port byte the purpose of this byte is actually to send and receive different types of messages to a sensor uh plcs and whatnot are very simple devices but we can use it to overcome the message size restrictions by sending by sending a large Uplink message by breaking the message up and increasing the F port number with each Uplink
message until the message is completely sent you have a 224 before you have to reset the uh f-port byte 225 and higher is restricted for future development all right same way as we can use the download message for the F port to distinguish what kind of commands we want to run on the Dropbox um again there's an article out in meditude Labs uh the address later on they think that will show you how to set up the low raw the proof of concept script for your own testing um and I am in the process of actually writing out one on my deployment of the Shell Rock and stuff all right um I guess I should have told you how I
like to run Dropbox uh I of them automated where once they're deployed they run certain Recons get me the data before I go interactive with the devices so all right so this works for map my testing all right let's go all right but we like interactive speeds in our shells and our c2s while LTE devices have the ime number and the Sims information for tracing you can look for a prepaid dust service provider the data service it works just fine use cash again we are looking to meet certain clients cyber security postures and not beat criminals all right I talked about Dropbox so let's uh just talk about cost building custom concealments real quick old
bricks are good this is all repetitive stickers units that have screws are easier but you can crack over power units Goodwill shops you waste turn up also great places to find oversized bricks the negative is it is a fixed space but you'll be surprised once you learn how to cut cables and USB uh connectors how easy it is when you're making your own custom concealments uh Parts you're going to need are as a micro AC to DC 5 volt DC two amp converters is uh good the that's the device by the quarter as you can see so it will convert down 120 down to the 5 volt DC uh c14 recessed male adapters those are the ones that look like at the
back of a computer I know how to cut your own RC RJ45 and USB cables since uh duck walls uh work requires knowing the computer and the switch connections I use two different color uh connectors for this purpose at the end of the day that's what it looks like and it's just yo big and when it's under the desk nobody's ever going to see it and if they are looking at that point it's uh you know pretty over okay so you got a 3D printer now what we'll do what everyone else in the industry does just copy and modify your figure needs the sliding box one actually modifies out really well um look for a case that makes it look
sort of like a Poe injector that would work well too labels uh laser printer with a clear sticker on top of it you're good to go you can buy Amazon uh or several other locations yellow electrical warning stickers that uh you know slap on it you're good to go once it's under the desk as I said or deploy people are not going to notice it sometimes even when they're actually looking for it I've actually had to tell clients no it isn't by the printer no no no no no no look at it no no it's the Lenovo brick come on so so but okay let's change up a little bit uh let's look at Daily acquisition for uh
social engineering one of my favorite fishes are tax time and open enrollment emails nothing original there but how do you get that data for emails to get that click so we can do our Nifty HTML smuggling or credentials uh capture session capture with evil Gen X I use the breach data I look for breaches where a Target will mix business uh details with personal data such as travel sites or hotels I mean how many times have you all used your personal cell phone number when you're booking a business trip all right one way to get this uh uh one way to get a targets or excuse me one way to get a Target company's employees
personal information is combining the data breaches services with personal search services such as the public website the hash and the free search true person search this will allow for getting a target's current address and birth date for using a social engineering attacks since this talk is about Anonymous services I have used prepaid debit cards to gain these services like the hash um it requires just a boner account and burning number so it's nothing uh two-person search is free but it may not be after this talk you know so all right uh but there are others I mean there are just others these are just happen to be two that are very convenient and easy to
use for the people um I would recommend if you have the means to look for the raw data breaches to get a copy of that because the legitimate services like the hash allow for Target to request that their data be removed all right to look at one sample of a breach that contains data that you can use in social engineer taxes the Acura breach from 2020 yeah uh it provides names home addresses telephone numbers uh this breach also contains work email addresses which is going to be the quickest way obviously to associate an employee with a Target the addresses uh within this data can be old but it the true person search has the old addresses
with the present dresses so it's really trivial to associate the data through the targets this is just a sample email that I normally use when I'm using breached data uh to get the address in the uh as soon as you put in certain personal information and exit out a little bit it just automatically causes the level of trust depending on the client's email banner I either use uh something similar or I have a number of pre-text domains that we'll talk about in later um this email never sends in any kind of tracking but I sometimes use a readjust read or delivery receipt just to add weight all right so how do you find out about
the current payroll system just call the HR department looking like to sell them a new system I mean questions such as oh uh how you know how do you like your current payroll system oh I'm sorry who what what vendor was that again um same as getting the information for the target's open enrollment period or benefits provider you know just ask them what the open enrollment period is and uh you know who handles their benefits both will give you the information you need to make a personalized email that sends it right to the people um as you can see from these slides I am limited excuse me uh in my creativity so how do I get fishing uh samples I want
to get a good one in the email I'll just stick it in a folder that says sample emails I just clean up any links with the company systems and then create a reasonable landing page it's not original but you know it does work for me I love Microsoft all right let's see which leads us into the uh burnt sites um nothing worse than creating a nice landing page get it ready to go and have it picked off before even first email sent in this first bit is kind of like regular type of pinteresting let's say that you cannot use one of the nice tricks by Mr docs such as browser and browser or even Gen X you know the client doesn't use
0365. other client just really insists on wanting something of their services you know so how are these Services burnt well in my experience the items that get you burnt when you need to clone a site and use a domain that's similar it's failure to remove the Google tracker which is a good way for a threat actor to find sites associated with a Target but if you clone a site and forget to take it out Google has a tool and it will alert and it will burn you uh the others is monitoring Services looking for new domains and cert sites hosting a different company site before changing to the spoof site will help but brand monitors and threat Hunter vendors
check out new domains or domain names similar to the high profile companies some under contract and some of them are just looking for a perfect sales introduction how to avoid this I find is again when you have to clone a site is to kill the Google tracker don't host the targets files self-host them change the cloners user agent nothing stands out more in a log file than that you can use a proxy to clone the sites to mimic browsing instead of cloning okay but it's like how easy it for threat Hunters to detect new sites I mean do they need a lot of resources to monitor this type of stuff no really it's fairly easy sites like a search
stream from fish finder and other TLS transparency sites and the common crawl project make it very easy to monitor uh new sites when they're registered and turned up the service sites such as uh search stream shows all note TLS certificate is being issued in real time it's rather trivial for a threat Hunter firm to create a script that Flags potentially dirty sites for investigation or classify new sites domain names that have been registered at dodgy names and just other metadata common crawl does take a period to go ahead and cash new sites that have been created it runs about once a month but this is the snapshot of what you get with the search stream feed there are
other services so this isn't the only one that offers it again for free on both the Common Core crawl and the search stream are free so you don't need to worry about that as attackers we can actually use these types of services for an offensive purpose using the transparency records looking for type squatters and high volume sites when we get a hit you know go clone the site normally it's a nice malware redirector you gotta clean it up but you'll get the javascripts and also potentially new methods of infection you will need to use a proxy to capture the data because these are smart they uh they look for the agents um and also if you hit the site more
than once they will actually redirect you to a clean site um here is the site foxbnews.com you'll notice on the keyboard what the B and the N are next to each other it's a rather nice fat finger uh domain squat um while the domain has privacy I don't think Fox broadcasting group registered it at a Czechoslovakia um and this is also a way to monitor uh for malware sites and to go ahead and get some free samples all right all right now how to avoid because we're talking about actually going up against Real Advanced targets my practice for fishing and Recon is actually to set up a company with a proper internet presence okay nothing
brilliant there um I have a cyber security company such as this one a Tax Service Company a couple secured messaging sites a job recruitment site and maintenance company and I may or may not have a law firm these sites are pre-taxes or will proxy malicious traffic through this company was from around 2017 it was fun because actually I've created a fishing training course to go along with that pretext uh the course is clean and it actually will teach you how to spot a fish based off of other courses um however the video training was based on COBRA strike's Java payload this was when this was like before cobaltrek became the Metasploit of red teamers um and a certificate of completion which
was a malicious Word document again this was 2017 now I use isos download isos Etc uh this kind of pretext allows for going in multiple directions um I should point out that uh you cannot get a personal code signing certificate that's required for Java for either business or personal with by Anonymous ways unless you're really going to break the law so Java is really out all right secure document send was another legitimate site service that I used my recommendations when creating a company pre-tax besides having a nice landing page is actually to create a LinkedIn page I have a few LinkedIn profiles all I do with these LinkedIn profiles is modify the job and the
descriptions of them to match the next pretext I don't create new ones and try to get a thousand friends um let's see I normally Target all right so I've like I said I haven't had any issues so far with LinkedIn where I just changing the company names uh and experiences I normally Target people that state that they attend conferences and speakers at conferences you know it's a nice hey it's nice to meet you at besides or I saw your talk be my friend um oh another side note uh if you actually want to get a target's employees to connect with you on LinkedIn just create a profile that says you work for the Target LinkedIn will be really nice and
helpful and give you everybody else a friend all right let's see um again the domain register account is uh using a burner phone number and an email the domains are all purchased with prepaid debit cards and the infrastructure is hosted either on a one-year prepaid service or one of the other vpcs all right doing good all right now moving back into say an act of reconnaissance let's talk about Network infrastructure for bypassing the tour and points and VPN signature detections we're from America and frankly we love Overkill the more overly complicated and future Rich well it's just got to be better but if you're going to go duck hunting do you shoot two pounds of lead at a duck no
general rule over complicated will with the wrong tool is going to get you uh detected using the tour will likely red flag a Target again we're talk thinking about targets with more mature Security Programs so how can you anonymize your traffic to appear from a clean IP address in the past I used to use an openvpn hidden service on the tour to proxy my traffic through but in analyzing it really all you need is a Windows RDP session in the data center you don't need Tails so you don't need some other read-only OS at the end of the day you know we're under contract and we're not actually looking to be criminals we're just looking to meet our clients
teams abilities so the workflow to bypass the tour or a VPN endpoint is just to buy with prepaid debit cards either VPN service or VPC and VPC you just set up a Windows host in the VP Center tunnel VPN tunnel RDP to the host to Surf from I do it this way to avoid any kind of Ip leakages that you sometimes get with some HTML magic or webrtcs uh if you want to use socats to proxy the Windows host for go ahead it's really won't make a difference but I find Windows hosts are just easier with social media accounts and doing active reconnaissance against the target uh just remember always to clean up your logs on the vpcs and the hosting because
good opsec hygiene always all right but you want overly complicated same thing prepaid VPN vpcs set up an open uh openvpn hidden service on your VPC provider on the dirty laptop connect to the VPN uh to the tour Network connect to your openvpn hidden service openvpn self-signed certificates do not have the same issues on the tour endpoints as you do with https hidden services so using a self-signed certificate is fine and then proxy and surf your web but again overly complicated all right well I did go through very quickly cool all right uh let's wrap up we're highlighting uh why we would want to anonymize uh our traffic with a little story all right our client company is an
energy service is the target PS I have never worked for this company and I have no association with this company I want to do that to any of my clients or anybody I'm under NDA with uh basic reconnaissance determined that they use proof point in o365 likely MFA is enabled but we have our fake companies our fake fishing sites maybe an eagle Gen X ready to bypass proof point and o365 to get you know an email into the target's inbox we use Zuma uh Zuma is like Showdown uh it's just better it's not blocked as much it's again Chinese and it's dodgy but whatever uh zumai we see a couple of Fortinet vpns several sip servers likely
video conference solutions which is a plus several sign-in portals that are within the target range IP space a couple will actually look good to be single factor and usable for further attacks like it looks like they have a file service and this is all true I've again passively looked at this company all right so we feel we can social engineer uh this client and get initial foothold from an employee to download our payable the Sip servers beautifully they give you the internal domain name so now you have your domain pinning for your C2 payload all right all right we look at the physical location there's the one on the left hand side there there's a one food
location uh open lines of sights for either Wi-Fi low raw side Channel a couple places to actually set up and actually monitor for a physical break-in the flow of the employees in the morning physically the building is isolated but uh you know it looks like right there on the bottom is an open seating area so that looks uh well for a physical break-in for placement uh you see that the the e-sids have quite a few uh guests so they're likely to have employees or guests coming in to visit it also could be used by the employees as a bring your own device Network and if that's the case you're likely to find a corporate asset on the guest Network
all right so things are looking good for us so we used to the height the hash site we see that this got 656 records related to public breaches and looking over the data we find the one user the seismic vicker looks good multiple passwords that appear to be the kids and The spouse's names this person has a large social media account context again with kids family trips and whatnot good stuff to use against social engineering here so we do a quick uh Google door to confirm that she looks good as a Target the job title looks good like something that would receive outside documents or files a side note Google Dorking with the social media Service Company
um as the site and then the target domain name is a very effective way of getting the data very quickly all right so we go over to True person search to get the data to send a personalized email we get our current address birth date month the phone numbers whole nine yards again free we look the kids and the husbands kids may be dependents since they show up uh they still live at home you know it's not a good play for the email but maybe if you have to make the phone call you know knowing the kids information is good interestingly the husband has a different address but the phone numbers match up so let's go ahead and see and
just like that our engagement Target could have resources that we did not plan on going up against so all right uh and now we're glad that we took the time to anonymize our accounts and infrastructure before going into an active testing again all of that was done passively and in about five minutes uh while this story was in my attempt to recap the different activities uh discussed today to give reasons why you would want to go to the trouble uh the point to remember in any engagement you never know who knows who or what relationships the targets have this is especially true in certain geographical locations in America like Scottsdale Arizona that you have so many different
vendors internet companies and data centers but really what happened I was looking at the FBI's email accounts for public breaches to use that as an example and I came across John's number the husband and it just wasn't matching the other numbers that were in the dump the other numbers I could see were associated with the FBI or business so really quickly looked at uh the number well it seems that John decided to mix his personal cell phone with his work email address and really it was just bad op sex for an FBI agent so I created the backstory uh with the wife's employer as the fictional client just to recap FYI all right John is retired from the
FBI so don't harass them you know everything I've shown again was a passive Recon I did say this right all right uh just to restate once more uh once you get into the habit of using prepaid debit cards and burner accounts it's really a trivial matter to be able to run engagements against targets with more advanced capacities to put a layer of uh Anonymous attestation between you and the targets to make yourself appear as a threat actor that has compromised the third party site or utilize a side Channel method that cannot be monitored or tracked to be able to use threat Hunter tools and services to better hone our own tradecraft I hope you have gained a little
knowledge to using your engagements thank you for listening and Pat Matthews and you can reach me at P Matthews and ed2.com and as I said the articles on the Dropbox creation and low raw can be currently found in attitude's labs and again I want to thank the b-sides team for a very good conference and I'm going to be available for questions either here now or outside
hmm questions yes sir how sophisticated as a company's I.T security need to be to make an engagement like this worthwhile um it depends on who their monitoring solution is to be honest unless you're going up against say the dod or a government agency state agency it depends on who their monitoring company is so if they have a a sock that is uh um you know one of the better ones then yes you would want to go to the struggle because they have the capacities to actually figure out stuff but you're not a criminal so it all depends on where you want to be and stuff of that nature I will admit some of it is
academic um with the day-to-day usage and stuff like that but you translate that into your own personal life as far as using burner accounts uh other things for example drives my wife crazy that I have three cell phones you know so you know I have my burner one that give out to everybody I have my work phone and then I have my family only phone so but yeah all right does that answer your question yeah do they bring you in after to sort of scare everybody no no no no no it's it's not a scare it's actually meeting your clients sophistication because at the end of the day as a penetration tester or a red
teamer you need to make your clients better you have to introduce methodologies that make them think that you know improve their skill set so it's not about scaring anyone it's actually about meeting the capacities that they have yep yes sir for your burner phones do you use like a graphing or just like Android or iOS uh both I have IOS and Apple and Android uh because of the fact that each of them give you uh uh benefits that the other ones don't have especially in the realm of when you're using proxy accounts for um uh social media and stuff like that so uh you have an Apple account you get uh you know an Apple email address you
get an Android you get a Gmail having a Gmail email address is more beneficial in certain areas because again the trust model is such once you have that Gmail you can get other Gmail accounts off of it yes there's you know metadata associations and stuff like that um that's actually what I talk about in 2019 so a lot of that stuff is there so any other questions no excellent well I want to thank you and like I said hopefully you did get something out of it and uh if not thank you for not all walking out thank you [Applause]