Hackers Kinda Like to Eat
Show transcript [en]
Good afternoon and welcome to Besides Las Vegas's I am the Calvary Track. Few announcements before we begin. First, we would like to thank our sponsors, especially our diamond sponsors, Adobe and Akido, and our gold sponsors, Formal and Profit. It is their support along with our other sponsors, donors, and volunteers that make this event possible. As a reminder, these talks are being streamed live and as a courtesy to our speakers and audience, we ask that you check to make sure that your cell phones are set to silent. If you have a question, there will be an audience microphone placed down this aisle so that the YouTube live stream and recording can hear you. As a reminder, the Bides Las Vegas photo
policy prohibits taking pictures without the explicit permission of everyone in frame. However, we have explicit permission for pictures of the presenters. So, pictures of them, okay, pictures of everyone else, not okay.
All right. Um, show we're going to do just a little audience participation here. Kind of get get everybody in the right spirit. Um, who likes to eat food? Raise your hand. Okay, I'm seeing a lot of hands out there. We all love food. Well, we kind of need to eat food. I am delighted to welcome Mr. Curtis Hansen, joined also remotely through the internets by Mr. Andrew Rose. Wave. Wave to the crowd, Andrew. There we can hear me. That is awesome. We We did very many fancy technology today to accomplish this. Big thanks to the to the AV team. It's a team of people. Like we had eight, not eight, we definitely had three people running
around doing stuff. So that was super cool. Um, help us understand all of the areas that we should be worried about our food supply and what we can do about it because no one's coming to save us. So what should we do to save our own selves? Over to you, Curtis. Thank you. Well, um I think do a little bit of intro of who I am, who Andrew is, the organizations we're representing because I think it sets the scene quite nicely. Um and then we'll we'll dive into it. So, with that being said, um Andrew, you want to represent Bio Isac for us? >> Absolutely. Um you guys can read the words on the screen. Um, when we talk
about the bioeconomy, we're talking about the entire life sciences continuum. And within the life sciences is agriculture, and that's what I take care of. But life science is going to encompass your pharmaceutical companies, biio manufacturing, pretty much genetics, pretty much anything that touches somebody on the on the planet some way, form or shape, or other. And um, we're small, but we do punch above our weight class. And I'm happy to have Curtis there as our proxy uh as one of our members representing us there and a total lifesaver in this instance here. But and thank you uh for allowing me to stream this in here too. I know this was a a big uh change of uh
plans, but thank you >> making it happen. And I'm here representing a company called Invictus Incident Response. And well, it's in the name. We do incident response. And um myself, I became a member of the BIOSAC this year. Um, so just happened to be here in Las Vegas for Black Hat Defcon and Andrew couldn't make it. Whitney also, who is one of the co-founders and directors of the BISAC, also had basically got dragged into other meetings elsewhere um couldn't make it. So you're stuck with me unfortunately in person, but hopefully I'll I'll make it worth your while. Um, and Andrew, we've had many conversations together is is really I learn something new every time speaking with him. It's an awesome guy.
So hopefully you guys will walk away learning a lot of stuff. Um and with that being said, take it away, Andrew. >> Sure. Let me give you, if you want to go back to that slide a little bit, let me give you a little color on who I am and why I didn't qualify to stand here in front of you. Um about 10 years ago, I accidentally found some um significant uh vulnerabilities at a $300 billion bank that finances agriculture. And it terrified me to the point where I wonder if the entire a supply chain was as vulnerable as this institution was. And the answer then is almost the same as it was today. Yes. And not only is it
vulnerable, there's a lack of awareness in both communities. Both the cyber community and the agricultural community. Um the a community views cyber attacks as a weather event. Something that just as an act of gent happened, we'll move forward and we'll get on. Um once I realized you know standing between the two fields just the lack of communication between the two I began a series of national um conferences and conventions around awareness building within the a supply chain. Now um with the bioacc I work on future threat modeling. So understanding where all the dots are then what the lines are between them then validating our our assumptions and probabilities in those lines and then bringing together
several states and we'll tabletop these different vulnerabilities. Um, another piece too here, and this is, um, shout out to Josh. He goes, Andrew, he goes, it'd be perfect if we can talk about water, agriculture, and hospitals. I'm like, uh, this is great. We just did a TTX out North Dakota, and that was one of the we had multiple complex layers in here, but that was one of the layers that we we extrapolated. And I'm going to all I'm going to do since we're live and streaming, I'm not going to give you a lot of the the stuff the the information behind the lines. I'm just going to give you dots. and you guys are pretty bright and maybe put some
together and and hopefully we can protect this piece of our egg supply chain. But Curtis, thanks for giving me that that little bit there. >> Absolutely. >> You want to dive into it now? >> All right. I do. I do. So, I'm an agricultural futurist. Um, and everyone's like, "Well, would you go to school for that?" No, I didn't. I worked in capital markets and I was trying to finance novel plant and protein production. So how do you finance a seaweed operation or insect operation to make that normal? In order to do so, you need to protect that loan out 7 to 20 years. So really understanding what are all the variables out there. It's not
hard to be a futurist when you're when you're playing with bank money. So that that was part of it, but you can't really be an agriculture futurist without being a climate futurist. And meteorology, like any other field, is massive. So, I just picked a little tiny niche within the whole meteorology field and focus on flash droughts and fire weather. And as all of you are aware, it's getting hotter outside and when air gets warmer, the capacity, the whole moisture increases. In the upper right hand corner, that's a shot from a um satellite called Eddie, EDDDI. And um Dr. Mike Hobbins is the the fellow who compiles all the data and gets it to where it needs to be. But basically,
this shows you how thirsty the air is. It's a sponge. So, kind of where you're sitting right now, it must be pretty dry out there. And when when I say dry, that means the plants will give off their trans evaporation. Everything evaporates up from the the ground up, including including us when we're walking around. Um, the other piece of this is a good precursor to fire weather. Um, as many of you know, there's more wildfires occurring around the place, but this is a good way to sort of understand when are the conditions, when's the probability the highest for an event happening like that. Um Curtis, you can bump the next slide up there, buddy. So, um as you know, um in the water
field, the majority of water that's used on this planet is used for agriculture. And [clears throat] one of the ways we get that water onto crops is by using these things called center pivots. And there's a pump that pulls it up out of the ground and it goes out through the pivot and it um will move around and do do the things it needs to do. In addition to water, um these center pivots can then also apply fertilizer and other inputs, the chemicals, herbicides, pesticides, things like that needed for conventional crop um production. Um the um these systems um are operated um I don't I'm not going to say click the video there. You guys can
click that later. Um but these systems can be operated from your phone, from an iPad, from a great distance away. And I think many folks understand that when you're able to manipulate something that from afar, that that's always a a window that needs to be checked to make sure it's locked appropriately. Um, and there have been some incidences of um attacks on these um these systems, but it's one of those things on to to see as a probability that this could be an increasing point. And if you go to the next one, and this is where you get the the neat hospital or the the handy hospital tiein. Um, right now if any of you guys are from Iowa, especially in
the De Mo area, you know what nitrates in the water are all about. You know, it's it's dangerous to drink your water there. And nitrates um will accumulate on the soil surface from the application of synthetic fertilizers, conventional fertilizers, but also if um a center pivot were to malfunction and overfertilize and under hydrate, that's going to lead to a concentration as well. And um right now in Iowa it's fairly dire. And what happens on the downstream effect of the nitrate in the water system is children especially children it I it might manifest itself in other places too but children it inhibits the uptake of oxygen in their cells. They get what's called blue baby syndrome. So their skin turns blue from
lack of oxygen. So anytime there's a nitrate spike the hospitals need prepared for a possible incoming of the blue baby syndrome. Curtis, you want to bump ahead there, buddy? Hope I'm doing okay here. Yeah. So, I'm I'm gonna be quiet now and hopefully I came through clearly there, but Curtis is really the genius here. And I've got some pieces towards the end I'll pop back in for. >> Definitely not the genius here. Um, no, I I think hopefully Andrew kind of highlighted that when we talk about food, it begins with kind of the source of life, which is water, right? And we're all heavily dependent on well, water getting to us when we need it
most. And also that can be impacted as we've saw in the previous talk with healthcare with cases like ransomware. Um and coming from an instant response perspective, we kind of live, eat and breathe this stuff on a daily basis unfortunately. And I kind of wanted to wrap the reality of this into what we see in the real world and kind of underpin it with this is kind of our canary in the coal mine moment. It's not something we're we're not trying to be alarmist, but we're also trying to show you that things have happened in the past that could have resulted in something much more catastrophic and worse than what they were. And we can
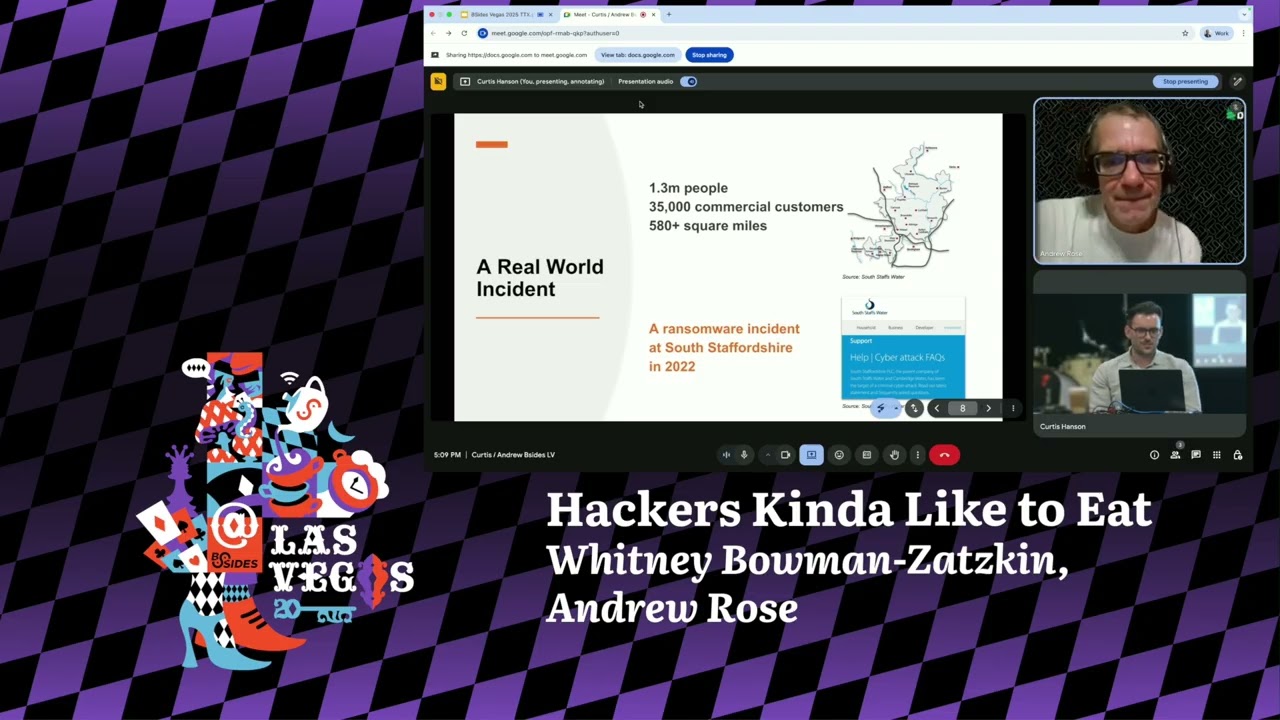
take some lessons learned from that today and hopefully make a better future, more secure future so we can actually have our food, right? We all raised our hand. We wanted our food in the end. So, I think that still stands today. Um, and one of those cases that I think really puts us in a perspective of this could have been a lot worse than what it was, but this actually happened almost three years ago uh to date actually. And this was actually in the UK, so over in in England. Um, a company basically called South Staff Stafford Shire was hit with ransomware. Um, they service 1.3 million people, 35,000 um, commercial customers. This is basically the equivalent size of Dallas
Fort Worth. Um, equivalent size of San Diego. Those are quite large cities when we put it in that perspective, right? They're not little towns. So, you can imagine kind of the rippling effect if water was cut off to all of them. What would happen to those crops? What would happen to those hospitals? Um, short answer, not good things, right? Um, in this case, you might ask yourself, how did this happen? Who was behind it? What actually was the gist of this? And you know, I said do incident response before this though. Um, I did thread intel. I used to track state sponsor groups for for many, many years, uh, PWC at UNI42. And KLOP was one of
those that we always kind of put up there as a top tier ransomware groups. They're not just kind of the script kitties, if you will. They actually are, dare I say, sophisticated, um, financially motivated. They used to run a lot of ransomware via encryption. So, one of those that would lock your computer up and you couldn't get anything. And they've kind of shifted away from that to more just pure data extortion, just taking data and extorting you for it. And that sort of shift has also is better for us when we talk about critical infrastructure because well, we can still access systems, but our data has just been leaked. So, that's kind of a good thing
that this group has kind of shifted away from that encryption uh mechanism, but they're very much known for high-profile cases. Um, Acceleron, Move It, um, Cleo most recently, what they decided to do is go after uh, file transfer applications, seeing that they can just, you know, pop one organization that uses a technology to get to like a hundred other customers downstream. Very clever, very thoughtful. But this kind of happened around well 2023 this shift I think move it was a big one but prior to that it was very much more targeted attacks on those heavily industrialized organizations national critical infrastructure if you will um and actually was doing some research and water ISAC actually looked at
victimology from klo around this time of this incident and saw that almost 45% of those victims were industrial or infrastructure related right so there is that clear sort of hey, the metrics match this sort of motivation of going after these organizations that are probably going to have to pay because they're so critical to society, right? If you cut off water, well, you don't get food, you don't get healthcare, everything kind of goes well south. So, this is um it's a good case study of they're still around. I was just looking at ransomware figures um for H1 of this this year and they were the second most active looking at their leak site and victims. Um so very much still around
still much causing harm. Um and in this case what actually was the impact or outcome of this incident. Um so first off it happened in July the actual incident itself. Um you started to see the extortion methods in August and then a second wave in September. And I think that's something important to recognize and realize. And I think the previous talk if you were in the room um talking about how you know ransomware cases the hospital been down for one or five weeks um in this case it demonstrates that you know for 3 months ultimately this incident or the tail end of the incident was still occurring and so that's something to remember like these
incidents just don't happen in a vacuum. Um recovery takes a long time, negotiations take a long time etc. Um, in this case, according to the victim who worked a lot with the National Crime Agency in the UK, basically came out and said it was an IT breach. Um, customer data was taken. Maybe some of our internal data was leaked as well, but nothing that affects the delivery of water or the levels of water, whether it's um chemicals inside was altered or potentially changed. And I think that's key and important, right? don't want them to have access to important OT assets to actually turn water off or maybe alter it in a way that could actually harm us if we drink it or if
it's going into our food and we consume it that way. So that's really good. At the same time, the thread actor themselves um basically came out with some of these images if you can see here uh basically saying hey we had access to scattera systems basically OT devices when I say OT operational technology um and we could have altered those things. Now this was never cooperated. It was never proven this was true. The threat actor also said oh yeah we also had access to water utilities in London. We could have done something similar. Um, at the end of the day, they're trying to get you to pay a ransom, right? So, it's kind of one of those things that we take
this with a grain of salt. Um, did they or did they not? We will never know probably. But, this is also a case of the threat actor wasn't so malicious that they decided to actually turn this water off or tamper with it in some way, shape, or form that it affects our crops, it affects our hospitals, it affects everything in our daily lives. And again, that's kind of that wakeup call like, hey, this happened three years ago and it could have been way worse than what it was. And so, this is something that we can kind of learn from of, hey, how do we maybe prevent the next one for the threat actor who isn't
so mindful of not turning things off, not tampering with things? And as the famous Intel analyst DJ Khalid says, and another one, um, yeah, there's plenty of case studies here, but this one like just rung into my head because I used to track a lot of Iran activity. Um and so 2023 of last year or 2023 not last year uh October 2023 we saw basically it's hasn't been confirmed how many but at least 10 if not less uh water facilities in the US um were hacked in some way shape or form. Um on record it's confirmed that a municipality in Pennsylvania servicing 15,000 residents for sure was hacked. Um, but this was done by an Iranian
group. Um, state affiliated. I'll I'll talk about them in a second. But this wasn't ransomware. This was something else. Um, it was actually kind of spoiler alert, defacement of actual OT assets. Um, it was a specific uh PLC, Ultronics PLC, meaning a program logic controller. Those are the devices that actually control the flow of things, whether it's water, in this case, water and waste management facilities. We're using these. So again, sort of a way to allow water to flow or way allow to um restrict certain things within water so it's clean. All stuff that is quite necessary if we want to grow crops, if we want to have clean water in our houses, our hospitals, etc. Um so this
was one that was kind of also a wakeup call within the US of these thread actors are able to come in and actually get access to these PLC's, right? We're moved beyond from an IT breach into something that could be super harmful. So, who was doing this and kind of what was that outcome? Well, I gave it away. This was uh an Iran uh based threat actor called themselves the Cyber Avengers. Um, this was a group that was very much sabotage focused and their sort of focus was on primarily information operations, amplifying something that could be bad and kind of just trying to drive home that we we got you. Um, and it resulted in a defacement
and I'll show you on the next slide what that looked like. Um, but there's also been um some indicators that some of the malware they develop has some say wiper capabilities disguised as ransomware. Um, I used to track this group as as a different name. Um, and clearly see that they were connected to one of Iran's major intelligence organizations, the IRGC. Um, they've been active since 2023, and they weren't all that great. I'm not saying they were the the best, the brightest of the bunch, but at the same time, they got access to about 10 different water facilities in the US that is providing us all clean water, is watering our crops. that's pretty serious and if they're not that
sophisticated, like how did they do this? Um, and as I said before, they went after actual OT assets. They weren't going after the IT network. They were going after something that could actually cause quite a lot of harm and impact if well done right, let's say. And thankfully what happened here was they didn't go to that extreme of like bricking those PLC's and just causing them to go offline and shutting the water off and we wouldn't have food on our tables. We wouldn't have clean water in our houses. Hospitals wouldn't have running water. Um instead what they did was they defaced it. They put this politically charged message around um Ultronics being sort of not sort of
but being Israeli owned and affiliated that hey because you buy this you're supporting Israel and this this time this was around the uh attacks in Gaza the terrorist attacks. So this was all very politically motivated and drawn from Iranian groups and kind of similar to what we see with Klopp in that sort of hey we have access to scattera it's in London. Um, we also saw the cyber Avengers posting a lot of BS really. Um, so they were saying, "Oh, we hacked a bunch of other things. It turned out to be false. There was actually sort of cooporated that those were false claims." They're trying to amplify again, conduct sort of this disinformation operation, but in the
other sense, they had actually hacked other things that were real. So, it's one of those things like, hey, if one thing is real and you make up 90% of the rest, how do you discern actually if all 100% is true or not? So, that's something to keep in mind here. But at the end of the day, you you you know, I said they're not sophisticated, but yet they had access to these PLC's and could have caused real harm and damage and chose basically just to face them with a political message. How did they do it, right? Well, basically these organizations had these devices internet facing, which most likely they did not need to be. Um, and they either had no
passwords or they were using default basically admin password 123, right? not the best cyber hygiene when we talk about well anything really I ito IoT etc. Um, so this was again kind of lowhanging fruit for the the adversary. But on the flip side of that, it's lowhanging fruit for us to actually do something about, right? Segmentation, not making sure OT stuff is internetf facing because why does this need to talk to the internet? Probably doesn't. And also maybe let's throw on a password there rather than just using the stock or or nothing. Um, so kind of lessons learned of those cases. I think this one goes for every industry, every sector, but the attack surface is constantly expanding. Um,
it's just kind of the nature of things these days. I think postco we've really seen it. Um, but when we talk about agriculture, when we talk about water, we talk about hospitals, we're just getting more and more technology within those industries, more and more things are touching the internet. And that means a lot more opportunities for bad guys to exploit them. And it means a lot more work for us to go in and harden and secure that stuff. And that's just the reality we face. And you know, a lot of that is a burden on us. It's kind of our own. But there are some basic things we should always be doing, right? And we
saw I think on the last talk how actually some of those cyber hygiene basics are actually an impediment to actual business operations, right? Putting on MFA to a station that a nurse needs to log into. Well, that stops them from doing their job because ultimately patient care is going to decrease. Um, so that's something we also need to balance within these critical infrastructures of, hey, we should be doing cyber hygiene, the basics, but also what's the business cost to that. Um, in this case, I think a lot of what we can argue is like, well, maybe exposing stuff to the internet probably isn't a business downturn. um you know putting a good password on there
probably in the PLC case you know not causing much harm to that business and that that's something we can do but I just want to raise the factor that we as security professionals and especially in IR when we come in post incident we can suggest a lot of considerations you might think oh that's easy um but actually it has an actual consequence for the business in terms of actually being able to do your job the other thing is the complexity of this um I don't think this gets acknowledged or is understood quite enough. Um, and I I would actually like to see this more sort of understood but also talked about and again in these
cases we talked about it OT but it's easy to say those words and not recognize the complexities that come with it. Um, it's often times these networks are very extensive. Um, within those IT systems, you have cloud stuff, you have onrem, um, you have different people that own the cloud stuff that are in charge of the on-rem. The OT network is managed by something else. Um, you have IoT devices now. Um, as Andrew talked about those center pivots that are out in the fields, right? Those are something that it's not a guy holding a gardening hose watering our food. That's stuff that's all now automated and it runs off the internet and it's something that requires actual connectivity from a
remote station. Um so that's something that you know when you think about how do we defend this? How do we respond to this? It's complex. It takes time. Um creating a response plan isn't easy. Um we saw in the last talk right too about crash cart a cool system to actually be able to respond effectively. um you can kind of adopt that sort of resiliency mindset to say agriculture or any sort of sector you might operate in but just realizing that it's not simple enough to say hey we got IT network let's secure it it's there's a lot more moving parts and doing that response effort is probably going to require a lot of different parties to play nice and
intersect internal teams external teams people with areas of specialty knowledge etc and I'm here representing not only incident response but bioacc as well and ISAs are all about intel sharing right and I'm a former TI guy um so it can go a long way sharing IoC's TTPs um you know in the case of that UK water incident you know that can be sort of the tipping point of hey we got all these IoC's let's share them with all the other water facilities so they can actually go do some threat hunting do some hardening etc um it also helps organizations contextualize the threat. So understand that if you need to relay this to management, to the board, whatever it
may be, having that value of this is KOP, this is how sophisticated they are, this is what they've done in the past, this is why we need to care and respond today can go a long way. Um, a lot of times that's missing. Um, but being a part of an ISAC really sort of helps that community effort um, get that established. So I'll speak to some actions we can take today on the cyber side and then I'll pass over to Andrew who's can talk a little bit more about what we can do on a personal level when it talks about well when kind of critical infrastructure fails and we need to well keep living keep eating keep surviving.
Um so from a cyber side this is less about us individually more about our organization level. First off join bioacc right if you're part of life sciences if you are part of agriculture come join us. We do cool stuff. We are a great community. We're always helping each other. Um we are highly confidential in and also what we share and everything. So yeah join us. Um we'd love to have you as well as that cyber hygiene. Um the basics are always important right. Um, we can always talk about MFA everywhere, but ones that I really find valuable is just like inventory of everything. Again, coming from an IR mindset when we come in and we're like, hey, do you have the logs
for this? Do you have an understanding of what your network looks like? And they're like, no, not really. It's like, well, this this is going to be fun. Um, and they're like, yeah, we have network diagrams, but they're from 20 years ago. Okay, cool. That's useless, but we'll we'll take them. Maybe we can find some value there. Um, so just certain things like that which again I don't want to oversimplify because there is a lot of time and effort that goes into doing that creating that inventory but along the way you'll oftent times find shadow IT stuff stood up 10 years ago by the CIS admin that eventually left and that's usually what gets popped by the
thread actor and that's how they get in. So, it's one of those, yeah, it's going to be a lot of effort, but we might find some valuable stuff along the way that actually harden our our security posture. And of course, be be ready for an incident. IR plans. Um, this includes, you know, who's in charge of what, contact details, outofband communications. Um, there's a lot you can do in a very pragmatic uh perspective that doesn't require a whole lot of effort. Um, but again, just knowing contact details. You'd be surprised that you talk to someone and be like, "Do you have an IR plan?" Like, "Yes." Be like, "Okay, what happens when it's Fourth of July weekend? Who do you
call?" I don't know because that guy's on holiday. Well, who's the backup? What happens if you're using Microsoft Teams, it's part of the ransomware incident, and then it doesn't work. What's your what's your comm's method look like? I don't know. So, there's little things like this that people just forget to ask themselves because they haven't been in that moment of crisis. And you don't want to be asking yourself those questions in that crisis, right? You want to get ahead of that. Um, so little things like that, of course, backups, regularly tests. Um, one that I really enjoy and Andrew already mentioned, TTX, tabletop exercises. I think these are really important. You can have the best
plan that you want, um, but actually testing it, rolling out, um, that's really where you learn a lot of valuable lessons. And again before the crisis has happened we saw again not to keep referencing the last talk but you know they kind of rolled out that crash cart system actually at a hospital to see like what are the weaknesses where if we set this up does it fail where can we improve and that's ultimately what you need to be doing as organization operating in these sectors that are are dependent on our life right understand that hey if we run this TTX what can we learn from it what can we improve what can we make better um and just one last
notion here is Andrew will talk about this but we're you know kind of moving we we're heavily dependent on technology I told you before like lots of our stuff is becoming more and more internet facing connected but we also need to have that realization of dependency on the past that analog methodology and I think again the last talk talking about when you have to go from electronic health database records on on the cloud to actually handwriting prescriptions. That's kind of a lost art. And I think when you talk about agriculture, water, also having kind of those manual overrides, having those manual sort of ways to test, ways to actually act um is really key. Um a a great example of this
again from a TI perspective, stuckset, something that happened over a decade ago. you know, if for those who aren't familiar, it's basically malware that caused disruption in Iran's nuclear um facilities to basically break their their reactor. You know, if they had a manual actual gauge that was measuring how those centrifuges were spinning, so it wasn't electronic completely, but just a manual sort of sense check, they actually would have caught that that there was something off. But since there was no manual actual visibility there, it was all trusted on technology, they didn't catch it. So it's again good examples out there of like, hey, let's trust technology. Let's use it, but let's also have a redundancy when again
stuff hits the fan and we need to act. And with that, Andrew, you walk some walk us through some real world resilience rather than just the cyber stuff. >> Outstanding. You've earned yourself a glass of water. That's for sure. Good job. Um, going back to the instant response plan too, one of the things that it really helps with is muscle memory. When you run through something like that in one of those sessions, it really builds, okay, who are you going to call? Yeah, you're going to find gaps and blind spots, too, but you're going to build that camaraderie amongst the team. So, when something like this does occur, we're not relying, you know, hopefully someone's written something
down or someone has that phone number or who is this agent who's coming in to run our um our our cyber command center. And another piece too about instant response plans. In the old days we used to say um it's you know it's not if it's when but nowadays it's when and again. Um we're seeing just cycles of attacks happening constantly. And the more prepared you are for that if you haven't been hit already, God love you because that means that you haven't realized it yet or something like that. So um and and Curtis, you you stole a little bit of my thunder there as well. I love to tell people as a futurist, the further I
look, the more analog it gets. I don't I don't really see any other way around um where we are, we're pretty close to the apex of technological advancement and what can be supported on this planet as it is. So um when I speak to other uh futurists like myself and others that are in the risk management uh point of view, we sometimes joke and say, "Well, how much dry food do you have in your basement?" And it's kind of one of those little litmus tests that we pass back and forth. And six months is kind of the the bare minimum that people like to have that are aware of what what could happen. And when we talk about six
months of food, it's typically one dried cup of food per person per day. That could be beans, could be rice. Um we'll certainly need water for that, but in terms of that dry food, and and I found this out the hard way. If a mouse gets into your food store and it has a choice of eating the rice or the beans, it will eat 18 pounds of rice before it even looks at those beans and they make quite a mess. And if you've ever seen those videos on YouTube of those mice infestations in Australia, if they get in there, trust me, they're going to replicate. So, I spent 10 hours cleaning my basement understanding exactly the
science behind rice versus beans and a mouse's diet. Um, in terms of capturing the water, um, a lot of people will overco complicate this with life straws and things like that. Very basically, you can capture water through evaporation. DARPA had a challenge back in 2020 called AWE, atmospheric water extraction. And what they wanted to do was find a way to pull water out of the ambient air to service troops in the desert and places like that. And I contacted them to see if they'd be interested in running a pilot in the Mid-Atlantic. and they said, "No, it's too easy there. We want a place that has less than 15% ambient moisture." So, they solve for that. There's multiple
different iterations on the market today. I haven't investigated them, but I think for drip agriculture purposes, it could be an interesting thing to look at. So, don't over complicate that. Um, and one of the the easiest hacks you can do is get a whole bunch of five gallon buckets from Home Depot or something like that, clean ones, and if you do have an air conditioner that has condensation, just keep them topped off from time to time because you just never know when that flash is going to hit and how long that power could be out for. Um, now we talk a little about being self-sufficient. I'm in the Mid-Atlantic, so I've been had some time
to experiment with different crops. I love collards because in the middle of winter, you get these giant elephant ears of green and they're so rich. And if you're from the south like I am, you just cook them for a long time on the stove and they kind of lose their bitterness and become like vinegar and they uh it's a good green to ingest during the winter time. Lamb's quarters is a common weed that grows pretty much all over the country. Tastes like spinach. Great vitamin A in it. Um turnipss, for whatever reason, do real well here in the Mid-Atlantic. Um you take the greens off, you sauté them, but you also got that that kind of bitter
potato thing at the bottom. I still haven't figured out a good way to repair it, but it'll keep you alive. And then in terms of the chickens, um, Rhode Island Reds, I've raised all different breeds. They tend to be the hardiest. You know, they they're they're pretty mellow. Um, they're decent layers. Um, you know, kind of low maintenance. A lot of people start when they start getting um livestock curious. Then they get some goats. And I can tell you right now, don't get a goat. Goats, if you've ever had a goat, you know that if there's a way for the wind to get through that fence, the goat can find a way through that fence. You're much better off
getting sheep. Um, and and for those of you who um are are vegetarians or vegans, you might want to cover your ears for this one. But sheep are nice because you get a boy and a girl and they replicate. And the little boys, those are those are the lamb chops, you know, little girls and you can raise for the wool and stuff like that. But it's a gift that keeps on giving. They'll consume the same things that goats do. Um, sleeping outside. I don't know if you guys make a practice of sleeping outside or not. I would encourage you though a couple times just see how little it takes to sleep outside. Um, obviously I've gotten away many times
with a tarp and a yoga mat. Garbage bag is kind of a luxury if you got that with you, but a tarp and a yoga mat, it's all you got. And we we talk a lot about global warming and daytime temperatures and 120 degrees on the surface. That's yes that is dangerous but the real danger is at night time because if the temp temperature doesn't fall below 80° we as a human being our bodies begin to degrade it can't reset again for the next day. So when you start watching the weather forecast yeah look at the daytime highs but make sure that nighttime temperature falls below 80° especially if you're going to be outdoors. Um I'm planning to do a
webinar on grreyzone warfare and right now um domestically we view warfare as kinetics as uh boots on the ground bullets and bombs and things that we can respond to at the military might enforce. Our adversaries on their hand have a full stack of different types of warfare. Espionage, sabotage, information warfare, cyber attacks. All these things for them are in the same warfare playbook. If we migrate from gray zone warfare where we currently are and move into that kinetic warfare, one of the first things our adversaries will target is our GPS's, our ability to to navigate, our ability to have a um a credit card transaction, to have the internet. Um so um I've sort of made it
a side quest to to collect as many um paper maps as I can and keep them in my car just in case. And they're not as readily available right now um as they have been in the past. And I can't see the audience, but if there's any of you that are under 30 years old, you may have never even used a paper map because GPS has been around for 25 years. Um, I would encourage you to practice now. You know, as they say in a make hay while the the weather's good. Don't wait till it starts raining to try to figure out how to find your way back home with a a paper map. And then last but not least,
um Josh was asking me, what kind of firearm should you have in your house? Um I'm a big believer you can't eat bullets. And I've seen, you know, I know I know preppers. I know preppers that got a whole whole like bunkers full of guns, hundreds of guns and stuff like that, which is great, but you know, there's only so many deer you're going to be able to hit with that gun. And you're not going to be holding an army off by yourself. You're a lot better to understand who are your neighbors, what is that community around you, who are these people, what do they do, what do they specialize, and even if you're an
introvert, it makes a lot of sense to go out of your way and just understand who these people are because if the hits the fan, it's going to be that community. That's that sort of that tribe that moves things forward. It's not going to be a whole bunch of rugged individualists fighting it out on the street like like gladiators. Um and then two two fun facts here. Um when I speak I tell people in the audience, listen, if your kid goes five days without food, you're likely to break a law and three weeks without food and our government falls. That tends to hammer home how hammer home how important food is for our society and and how we operate. Um
the longest I went without food was five days. That's why I say five days and you're you're going to break your law because that was one of the most miserable things a human being can experience. And if you've never gone a day without food, I certainly encourage you to do at least one or two days and just see what that feels like because it's good to prepare for the the eventualities of what could come. And with that, I believe Curtis, we are taking questions. >> Yeah. >> Good. I hope I didn't speak too fast. I get real excited about that. All >> righty. Um Thank you very much. So, this is this is your opportunity. I'm staring at the
crowd uh for questions. And if you've got a question, come on up to this fancy microphone and ask your question. We'll get fancy answers. >> Really interesting talk. Thank you very much. Um what about the sort of um kind of communications part of this? Uh, I know like yeah, ham radio is one of the things that you hear a lot of people talking about, but I'm hearing more and more about other alternatives to ham radio that might be effective in a situation where, you know, stuff is infrastructurees broken down. >> Well, I I'll take a quick stab at that one. Um, I asked uh Peter Zion, if any of you guys know who he is, he's he's
YouTuber futurist. Anyway, we we hired him at the bank several times to come and give private presentations. And I asked him one time, said, "So, what happens if an EMP goes off over the US?" He goes, "Uh, you know, it'd be bad, but what we have here, if you go outside, we got copper wires hanging from poles on the streets." He goes, "If you go to other parts of the world where they skipped over that part, went four or 5G, they don't have that backup system." So I mean we might be talking a bald rate of of 1,200 or something like that but there'll still be at least that sort of backbone of communication available and
I do encourage other people too to really think about analog communication. What does that look like? What does that mean? um you know that that we certainly live in a world of on demand luxuries and it you know yeah I'm thinking we're pretty close to apex of what can be accomplished but just you know if if you if you were born in a if you're born pre-digital and in the analog days just think back to how we got around that. >> Thank you. >> Well Curtis don't jump in there but he can too. Uh >> hey uh so you guys talked a lot about sort of the inputs to the agricultural uh enterprise. Uh not so much about the
uh the processing that goes uh goes on with lots of technology like tractors and combines and other things like that. Do the bioacc how how do the biosac engage that element and uh and you know what what are your thoughts there? I love this. That was almost like a planted question there. So, we had our um annual event earlier this year in in February and we did bring um a brand new combine in um that had not been experiencing the headline hacks the way most of the the main brands did and we were able to um to manipulate it from the stage and um do things to it. Um, that is a major area of concern. And if
you think back to when we had the solar flares earlier this year, there was a lot of people that had issues in North Dakota and southern Canada because their their lighter or the GPS was not tracking in the fields the way it should have been and it just it caused a lot of havoc there. the the the vulnerabilities are vast in the a supply chain and and we can use all the help from the community there to to help us identify these and and disclose them ethically to the manufacturers. >> Okay, thanks. >> Uh I might have missed this. I had something distract me for a couple minutes. Um, a lot of this track and a
lot of the undisruptible 27 is predicated on the idea that we may have hybrid conflict during the Taiwan Straits and uh, activities as early as 2027. Part of that um, that we focus on is the no water, no no hospitals in 2 to four hours. It's the interdependence of water and power generation. No power, no pumps, no pumps, no water, no water, no hospitals. No water, no power generation. We talked this morning about data centers. One thing we didn't talk about in this room is it's widely believed and there's uh confirmation of some of the ports and the smart connected equipment and the cranes in the ports where we get most of our food imports are also compromised and part of
the risk posture and maybe part of a campaign. So therefore it would put an even greater dependence on domestic production movement cold chain cold storage spoilage prevention food uh shelf safe safety etc. And then there was an exercise done by MITER Corporation they shared part of the unclassified where they simulated something resembling salt typhoon and it was additionally complicated by being in December uh further constraining some of the responses and repair times in the extreme cold. So, you know, can you like pontificate for a little bit uh on how all those things would come together from domestic production and distribution of food supply? Like how long would that last? I've heard some people say, "Oh, we can make plenty."
And I've heard other people say, "No, it's about 11 days." So, I don't know. And I thought I'd ask people that spend more time on it than I do. >> Yeah, I think 11 days is is highly optimistic. You know, I would think three to seven um typically is what we're looking at with the on demand. Um I've been preaching let's shorten the supply chains as much as possible in the communities where you are. Focus on local production, local procurement. Um typically an urban area is not going to be able to produce enough to support itself. But there is the exurban in the suburban and the rural. So you can form whatever you need to have around you for
that that purpose. Um I gave a a presentation to the global protein supply um uh society or organization back in October and one of the things I told him said the future is one of of survival and scarcity. We can no longer count on the abundance that we have on the grocery store shelves and your marketing people do a really good job right now if they went and talked to the aronomists and the farmers and asked them in 10 or 12 years what can you grow what can be supported here and then sell that to consumers. So, um, you know, again, we're kind of at this weird place. We've always we've known this our entire lives, this this abundance, this
this choice and and I think we're starting to see that sort of tighten a little bit and who knows how quickly it will tighten, but um, you know, that's a great question as well. Paris, I'll let you define. >> Yeah, no, it is a great question and I think two two things. One is we also need to realize or take into account as I said before complexities on the technical level but also the complexities of geopolitics and economics right because stopping say the ports of the US or something else within here has rippling effects throughout the rest of the world right and so in this scenario of China taking Taiwan is China ready to actually cause that rippling
effect which will impact them economically, politically, etc. Um, that's something I think is well above my educational level of I know nothing about Chinese politics to actually make that determination, but it is a factor, right? And that's something we also need to take into consideration. Which lends me into my second point of again lessons learned. What's happened in the world recently that we can maybe draw on to actually kind of assess how cyber would be used in that scenario and how it actually might impact say us on a on a practical level. And we have to look no further than Russia Ukraine, right? Um, Russia has deployed numerous wipers across Ukraine over the last what's it
now three years um since February 2022. Um, the cause and effect hasn't been as much as a lot of people originally predicted before 2022. Um, which is honestly is a good thing, right? We we don't want that. Um, but nonetheless, it is a factor that we need to take into calculations. Um and just because that was a failure or we can consider it a failure doesn't mean in this new scenario it will be the same right there's always a factor that it could be more successful. Um we also can look at what maybe was targeted in those cases and does that mimic or mirror what this scenario would look at. um thinking you know historically energy sector for
Ukraine thinking uh logistics viaat was a a big example of that taking communications offline um but not really so it's one thing again to say that's feasible if you know China's attacking Taiwan and they come after us the US um and you know they use cyber what does that actually really mean right what is the actual practical implications what are the actual economic fallout. What's the calculus there? Um, it's complex is the best consultants answer to give. It's complicated. >> Yeah. So, you've kind of touched on it a little bit, but I was curious to get both of your takes about um the way in which culture has to change the approach to if you think about agriculture,
farmers, dairymen, they don't know anything about cyber security. They could care less. And uh I worked in the electrical industry when we were trying to put forth NERK SIP compliance and all those things. And the culture was the hardest thing to deal with. I would walk into a room and try and talk through procedures for incident response with INC technicians and they'd write FU all over the procedures. They were just done with it already. So, how have you kind of gone in to these cultures that have had nothing to do with cyber security and convince them that all the automation, all the things that they've paid for over the years is actually uh a risk.
>> Yeah, I can take a stab and if you want to add Andrew. Um, so not even say agriculture or this, but just in general all sectors of industry security is one of those things that it's it's not the balance sheet. it's it's always in the red, right? It's not producing money. So, it's never one that's sexy. It's it's just one of those that's it's a hard pill to swallow. Um, so the best way I've seen to approach it is either put it in terms of risk, which is probably less of the crowd for say guys in the dairy business or whatnot, but put it in in dollar value. If you do X, it will save you Y amount. And again,
it's it's not easy to maybe calculate or quantify that, but there are ways and methods to to kind of put it into perspective, especially if you can say, hey, that farm AC across the state line had a ransomware attack, and this is actually how much money they lost because they didn't spend, I don't know, let's say 100K arbitrarily, but it cost them 10 million. The ROI right there is very easy then to articulate to them, right? And that's something that they can kind of grasp. So I think it's all about bringing it back to reality, giving real world case studies and putting it in something that means something to them, right? And usually it's dollar value, but it could be
something else, right? It could be loss of of life, it could be loss of land, something that represents utility to them. Um, so yeah, Andrew, I don't know if you have something you you talk more with those guys than than I do. >> Yeah. Well, you know, let's talk about culture. you know, um, as as a society, our culture doesn't move or respond to things until after they've had until after the bomb has gone off. So, a lot of that culture is not going to be real or not a lot of that response not be realized until they've had something occur. And then the pieces didn't come back together in an appropriate way. Now, how do you get around that? And
that's something I wrestle with constantly. And I look back to 2007 during the first cyber war when Russia attacked Estonia with their best weapons and their best cyber warriors. And Estonia, a tiny little country, and they used knocking over statues as a pretext for this. Russia was hoping Estonia would have a kinetic response, but they didn't. Instead, starting in kindergarten, they began cyber training their citizens, so their citizens become their strongest defense. in high school, they still refought those same cyber wars they fought during the the the first cyber war there to learn from that. Um, and then Russia realized that they were much harder target to penetrate and went to uh England and and
facilitated Brexit happening and took them off the world stage. But that just shows how a society then can harden themselves. The state of North Dakota was very appreciient and inviting some consultants over from Estonia to teach them as a state how can they become more resilient. And Governor Bergam who is now the Secretary of the Interior at the time had a mandate that K through PhD everyone had comp science and they've got every high school in the state. It doesn't matter if you're on a tribal lands or in a regular uh Bismar or Fargo, you've got highspeed internet access in the high schools. This is to the core of what that state is. I think,
you know, not everyone's going to follow that lead, but if we look to where there's a domestic example of a citizen a citizenry becoming more resilient, North Dakota is a good place to look. >> All right, we uh we are at time and so can you please put your hands together for Mr. Curtis and Mr. Andrew? [applause]





