Brad Duncan - Exploit Kits and Indicators of Compromise

Show transcript [en]
to kind of warm up the crowd uh one of them is a wave and the other is a chant so uh uh just kind of get us in the the the mood to talk about exploit kits uh i' would like to try a wave going to start over here I'm going to run over here one more time ready I had wash my hands in the rest from earlier and there are no paper
well that worked well uh the other is a chance and uh since I'm talking about exploit kits I would like to do a chance saying exploit kits exploit kits exploit
I can cross set off my bucket list now well uh for this presentation we're going to I'm going to do an introduction talk about exploit kit the concept talk about an exploit kit ecosystem discuss some uh common exploit kits talk about examining exploit kit traffic and finally we'll discuss uh what should be our best defense I currently work at UH H Alto networks unit 42 which is the public face of research for the company I also run the malware traffic analysis h.net website I speak or uh I write diaries for the uh uh internet Storm Center and I tweet fairly frequently at malware trffic so first things first in order to understand the exploit kit concept you
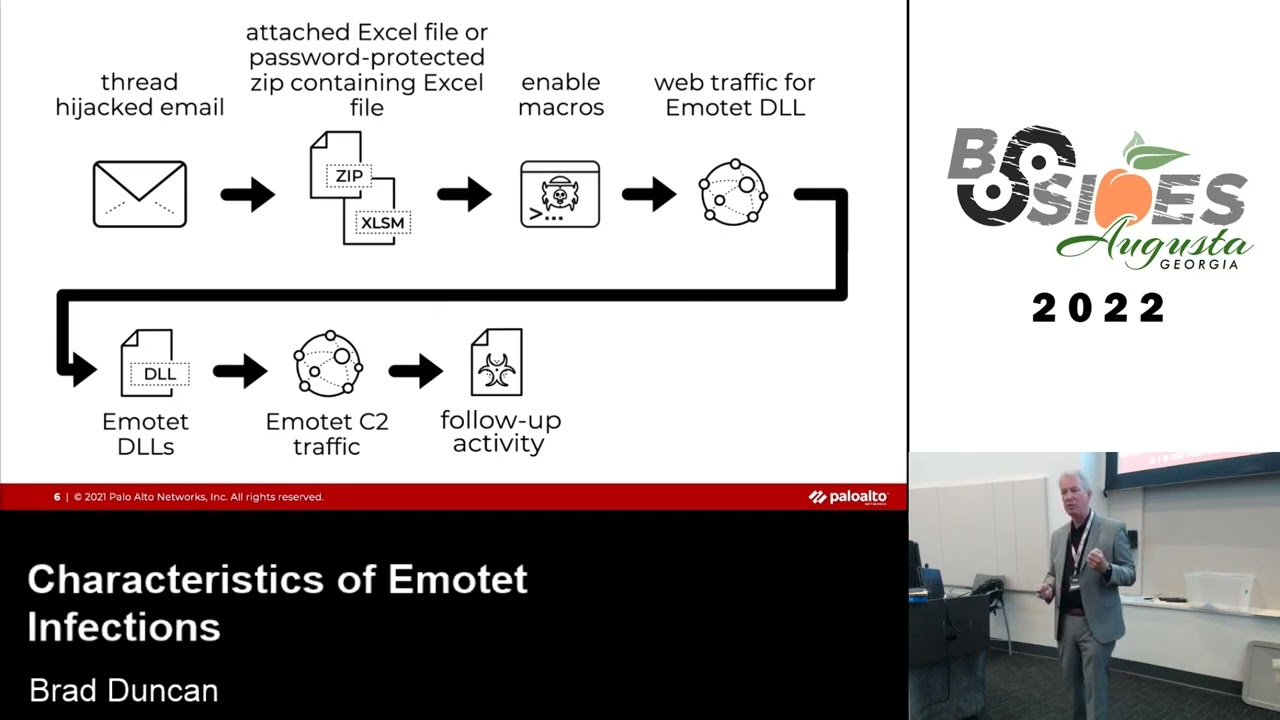
have to understand that there are two main methods that criminals use for Mass distribution of malware the first method requires user action which is a malicious spam or popup Windows during web browser here's an example of malicious span zip file attachment you open it up and that's not an exploit or Excel spreadsheet at all the other one is the popup windows that you'll see during web browsing in either case you have plenty of warning that you're going to do something wrong uh you're warned that this type of file could harm your computer do you really want to run that file and the average user well they're a clicker so we'll click right through that stuff but still I figure any one of us
here in this room uh is smart enough to know to understand what's going on there the second method happens behind the scenes without the user's knowledge and this is the method used by exploit kits where you take a criminal group's malware send it to the average user's computer behind the scenes little scary right how que coming up exploit kids distribute mware targeting systems running Microsoft Windows to understand the exploit kit concept we need to clearly Define what a vulnerability in an exploit is before we can Define what an exploit get is a vulnerability is an unintended flaw in software code that leaves it open to exploitation in the form of unauthorized access or malicious behavior
these are cataloged in the common vulnerabilities and exposures database uh cve numbers here's one for Adobe Flash Player if you look at the definition of it or the description I should say Adobe Flash Player 2.0.0 226 and earlier allows remote attackers to execute arbitrary code via unspecified vectors as exploited in the wild in May 2016 should be as of May 2016 and I I love this this is uh politicians speak right arbitrary code via unspecified vectors the the there's nothing arbitrary about this code it's malware right why would you why would you try to execute arbitrary code that's why do you say that and unspecified vectors this is export kits but you ever for these cves for these vulnerabilities
you will always see it described in that way arbitrary code via unspecified vectors just call it what it is malware in this case for this exploit or this vulnerability uh via exploit kits and exploit is a file or a piece of code that takes advantage of a vulnerability in an application a file or a piece of code so I can go into a packet capture of traffic uh that I've collected open it up in Wireshark scroll through trying to export some of the HTTP objects find a flash file export that because in this case I know it's a flash exploit and uh There It Is by itself and exploit although it's malicious it will not infect your
computer so for example if you have a Word document exploit that exploit by itself if it's sitting on your computer it or that that code or that file is not going to do anything unless it happens to be a Word document and then word will open it up and execute that exploit in a particular fashion so this flash exploit that I've uh exported from wire shark from this traffic if I double click it on my desktop it's not going to do anything it needs to work under a specific set of circumstances and exploit kits are way to do that an exploit kit this is probably the best definition that I've seen of exploit kits a server-based
framework that uses exploits to take advantage of vulnerabilities in browser-based applications to affect a client uh laptop or desktop without the user's knowledge without any additional action by the user except from casual web browsing so you might ask yourself what are vulnerabilities that exploit kids Target anybody have any guesses flash that is the big one right now flash is uh really really big another one is browsers Internet Explorer is probably the biggest one that's correct Java silver light is probably the third most popular one common I should say Java and PDF exploits those were very very common in exploit kits up until uh about a year year and a half ago any of the current leading
modern exploit kits that are out there I have not seen Java or PDF being exploited I have seen flash almost across the board Now browser based exploits pretty much Internet Explorer and to a much much lesser extent Microsoft silver light exploit kits have turned to a software as a service model SAS platform as a service model pass however you want to say it I call it exploit kits as a service which uh uh that term is caught on but the acronym uh how I pronounce it eks I've gotten slapped for that before and I'm told I shouldn't say that in front of a large crowd while I'm being recorded but uh uh hopefully you'll see
that acronym uh out a little bit more we should be talking about exploit kits a bit more in my personal opinion so we're renting an exploit kit we're not buying it much like we're uh software Ula for Microsoft Windows we're uh we're we're buying the rights to run it in this case you're just renting the service you don't really get any code like you would uh uh if you're uh buying Microsoft Windows so how much does it cost well in April 2016 the checkpoint blog published a study on nuclear exploit kit and in it they said that leading exploit kits are sold in cyber criminal circles for a few thousand a month that is just
Benjamin's a day in June 2016 now where don'tneed coffee.com the security researcher caffeine that runs that site he reported that your trino exploit kit cost $7,000 a month that was shortly after angler exploit kit disappeared from the exploit kit scene uh which was about that price prior to that nutrino was costing around $3,500 a month so the XO kits themselves once you are actually able to cough up the dough and pay for it you have yourself a server and that server in order to understand how it works basically when your computer connects while web browsing to that server it will first hit a landing page the landing page generally for exploit kits tends to profile the machine to see
what's vulnerable once it determines what is vulnerable on your machine it will send an appropriate exploit and if that exploit kit or I'm sorry if that exploit is successful as leveraged by the exploit kit it will send a payload which is your malware that will infect your computer once again all this is behind the scenes but this is your block diagram of the chain of events within the exploit kit but exploit kits cannot exist by the elves I cannot pay $7,000 a month for a nutrino exploit kit server have it out there and expect people to come flocking to it to come get infected it just doesn't work that way uh there's an ecosystem that exploit
kits work through or exist in and this e this ecosystem consists of actors and campaigns an actor is an individual or a criminal group behind a particular piece of malware is the best way of looking at it now actor is a theater term like uh many theaters there are good actors uh you know the good guys which would I presume be all of us here in this room and then there are the bad guys which I've heard called bad actor I don't don't like the term bad actor because that reminds me of people like Paulie Shore or George Clooney both who are Bad actors I mean that guy plays the same dumb character in every movie and uh I
don't particularly care for poly Shore either threat actor that's uh what I like to call them uh if I have to call them anything other than actor that's a common term so if you hear the term threat actor that's where it's coming from so a campaign is a system that consists of an exploit kit plus an infrastructure that directs potential victims to that particular exploit kit so you got to have a campaign set up if you have an exploit kit and that's what some people don't understand you see an exploit kit an alert for an exploit you're thinking well I got hit by nutrino or I got hit by rig exploit kit and sent that malware well just because
it's for example rig exploit kit doesn't mean that you will always get this one particular piece of malware it could be there are different campaigns that use the various exploit kits out there and they are sending different pieces of malware for the different actors that are using so an actor can use more than one campaign to distribute their malware that they're trying to push out there on a massive scale and I've seen instances where a campaign can distribute malware for more than one actor where I've identified a particular campaign in one hour it's sending one piece of malware and then the next hour it's sending something completely different so that indicates that there are there is another criminal
organization that set up a campaign that's renting itself out to actors who are trying to distribute Mal so it's a it can be a very complex sort of uh criminal Market there if you're in the market to uh try and infect other people's computers so in its simplest form the chain of events for a campaign looks like this where you have a compromised website and that website will redirect traffic behind the scenes to an exploit kit server which is also working behind the scenes now compromised websites are a dime a dozen uh if you look at anybody's malicious URL feed you will see occasionally a good percentage of them are they they look like just regular
websites and you'll check them and they're legitimate websites they're not set up specifically to attack anybody or to have anything there they're just people that uh set up a WordPress site on their own and forgot to update it it got it got uh owned it got compromised and sometimes you'll see different actors compromise the same website you'll find injected script from different campaigns in the same compromised website but in its uh uh most basic form any exploit kit infection always starts with a compromised website here's an example that I did uh uh last week the website was penopoly capital.com which is common it may be fixed by now I don't know but if you look injected
script which I have highlighted here in this slide uh from what I call the pseudo dark Leach campaign the patterns of injected script are common among the campaigns in this case if you look uh uh in the span it will put that I frame in a negative position relative to the viewable screen so that stuff is all happening out ofsight of the user and the highlighted portion in yellow is a URL for a landing page for the nutrino exploit kit sometimes campaigns will use another server that will act as a gate between the compromised website and the exploit kit server I like to look at the gate as uh that uh Bridge Troll there in the movie
Monty Python and The Holy gra so much like in that movie that Bridge Troll that gate is uh going to have ask you three questions before you can pass on to the exploit kit first question what is your operating system so now if you would say anything other than Windows here's what happens you're not going to that bridge if you do say windows and that information is readily available in the HTTP request headers you're one step closer to getting past the gate second question what is your IP address a lot of times uh campaigns will be specific to a particular geographical era area so for example if I've got a piece of malware that is German language for
some reason I'm choosing an exploit kit to somehow distribute this on a wide scale I only want it to affect Germany I'm only going to have it in some way shape or form that gate will will throw me over the bridge past the bridge outside of the bridge if I'm not a German IP but if I am the IP that's acceptable I am one last step close to getting past the gate so the last questions as you're staring the gate down the gate ask you is that you again a lot of uh researchers will try to use the same compromised website to generate a Chain of Infection traffic I've run through it before where I'll
infect a uh I will infect to host as I'm trying to generate exploit kit traffic get a full infection chain and something goes wrong I'll have to try it again if I try it again and I'm using the I'm coming from the same IP address it's not going to work that export kit that gate in this case the gate will not act here's an example from what I call the eii test campaign that was first identified by malware bites in 2014 and is still going strong today here's the pattern of injected script this particular website and and this one may already be uh done is uh it may already be fixed I'm trying to say is from the EI test
campaign highlighted in yellow are the URLs that go to the gate and then the gate will return if the conditions are right the gate will return script that will direct you to the landing page of the exploit kit it's kind of hard to see here so here's the script that is returned now that gate is opened up outside the viewable uh uh frame of the user in some campaigns you might see a second or a third gate before you get to the exploit kit and a lot of times here's an example where you can see past bin is being used as a gate before you get to the second gate so past bin URL shorteners like
goo.gl for Google URL shortener I've seen those plenty of times before although not recently but these are commonly abused by criminals the thing uh with something like ppin or something like Google is it's pretty easy to notify those companies and they'll quickly clear it up however it's easy enough for the criminals go back in uh uh you know pull some sort of Fraud and get more U uh uh set up another gate through a legitimate service like past bin or Google URL shortener or what have you common exploit kits the three common exploit kits that I currently see are neutrino rig and magnitude at this point these are just names if anybody is uh curious about
other exploit kits angler was a big big name probably the biggest in 2015 and throughout June 7th I believe of this year it was by far the most common one that I personally saw uh when I was generating expit kit traffic but uh angler exploit kit disappeared about the time the the criminal uh gang for the lurk uh Trojan banking Trojan was arrested by Russian authorities back in June nuclear exploit kit disappeared from the scene in April 2016 and rumor has it that when checkpoint released its big expose on nuclear exploit kit back in April the one that I referenced earlier that the criminal group or the author whoever it was behind the nuclear exploit K said that's it I'm out of here
and he packed up shop and he just quit after literally years and years of producing that particular exper kit which is interesting because now the exploit kit Market is really not as saturated as it was uh with different models of exploit kit as compared to 2 three years ago other exploit kits that are not quite as common Sundown is it kind of a Frankenstein's monster of exploit kits where it like robbed and stole from different exploit kits so you would see traffic from Sundown and you would think it was rig or you would think it was nuclear exploit kit or maybe angler it just looked uh uh rather rather weird Hunter exploit kit is another one
that's still out there I personally have not intercepted this but I've seen it on threat glass.com where uh there was an example there and then you have some really really uh limited distribution exploit kits like Kaizen which I've only seen associated with traffic from South Korean websites and Palo outto networks has a blog entry about a particular campaign Distributing malware uh that's targeted towards South Green Banks using this exploit kit so if I'm going to examine exploit kit traffic I need a few things before I can gener at or see the to actually examine the export kit traffic the first pre wacr that if you're going to generate export kit traffic is you need to stay off your
corporate Network or your home network if you're doing this at home because if you infect your computer there is a chance that you may get malware that happens to check shared drives or it may happen to you know just start scanning through the network that you're currently a part of and uh trying to affect other hosts so if you're doing this and the way I do it while I'm at home is I use a VPN service and I went into detail on that when I was talking about my uh uh setup at home in the security onion conference yesterday that should be available at some point uh publicly and you can check that out for
details second thing I would need to generate exploit kit traffic is a vulnerable Windows host that is running an out ofate version of of flash Internet Explorer silver light Java PDF Adobe PDF reader the next thing I'll need is a compromised website to kick off the explicit infection chain and although I don't need full packet capture to generate the traffic I do need it to capture the traffic so I can actually look at it and see what happens some of the tools I use for examining exploit H traffic first there's wire shark security onion which I talked about yesterday and snort or cotta which are intrusion detection systems IDs uh uh programs that can U that I can use to generate alerts
on the traffic and see what I've got there's a screenshot of wire shark for what that's worth there's a screenshot of security onion and I will be forever indented to both of those uh uh the Doug burs and the crew at security onion and the people behind wire shark because without those I wouldn't be where I am today snort snort is pretty interesting because the the uh um the rules that they the rule set that they have for snort to detect stuff is a tiered model so you've got a community rule set that you don't need an oint code or anything special if you're setting up security onion for example Le uh uh you might be
able to use the uh or should be able to use the open rule set the community rule set you can go to the snort. org website you could register and all you need for that I believe is just a valid email address and you can get an oint code and you can have a much more robust and comprehensive rule set than the community rule set for snort and I've uh I've corresponded with some people through email who had been using the open Community rule set for snort and I'm telling them hey just register uh the register rule set is only 30 days out of date from the subscriber rule set where you would have to pay money and
you can subscribe on sn.org and uh somebody was saying I think it was somewhere around $50 a year if I remember correctly serotta is another IDs and uh uh it definitely is it's an IDs and it works in general the same way as snort in that I see alerts from the traffic I'll generally use the emerging thread side uh for surot really emerging threats in surot the the rule set for emerging threats in goes with surot much like the snort Talos uh registered rule set or those rule sets go with snort it's really they're designed to work together and I you can mix and match those but I don't recommend it so we looking at individual exploit kits
first we'll look at magnitude magnitude is generally what I've seen it from is malvertising campaigns it uses profiling Gates and the payload when it's sent over to the network is sent in the clear and this is one of the few leading exploit kits that sends its payload in the clear so you can actually detect this if you're running something like security onion and you have bro and you can extract that exe from the traffic another thing about magnitude from Pro proof Point blog in April 2016 they're talking about the zero day back then uh it was an adobe flash player zero Day 2016 1019 and for a period of about 24 hours that flash exploit was Zero days so it
didn't matter if your computer was fully patching up to date if you ran across an expit kit and you were running Flash Player regardless of the version it would get infected in recent months Magneton seems to be used by only one actor who since the end of March has switched to Distributing serber or cerber ransomware am I pronouncing that right
ransomware anyway here's an example of magnitude exploit kit in wire shark traffic in that I can see Gates that are pointing to magnitude exploit kit and then I can see the actual magnitude exploit at traffic if I run it through security onion running the emerging threats cot in the emerging threats Pro rule set I will find various alerts that tell me this is magnitude exploit kit after a while if you see this traffic often enough you can ID it visually without the need for alerts you can also submit pcaps of exploit kit traffic whether you find them from my blog or some other blog you can submit him to virus total and it will run through both snort using the
snort subscriber rule set and serotta using the emerging threats Pro rule set so if I were to check magnitude I would see both sets of alerts snort and surot and you'll see magnitude I want to say on both of them now magnitude exploit kit has a profiling gate and there are a couple of blogs that already go through the details I'm not going to get too deep into here but the first thing this is a the second gate and that track that pcap of track with that we had so after it goes to the third uh the first gate it goes to the second gate the HTTP request actually contains the screen resolution of the computer the victim host so in
this case it was 1024 by 768 for the screen size and then it has some uh code checking for Chris berski aners I believe and there is another gate that's not present in this traffic where it will literally check for everything from wire shark to uh Fiddler to uh VMware any sort of virtual environments and not send you to the exploit kit it's an extra layer of protection from the people running this particular campaign to make sure that security researchers aren't trying to get through and pull samples get examples of the traffic flash exploits are often used among many of the major exploit kits if you look at uh uh traffic using wire shark pulling up a TCP
stream you'll find where it says X Flash version in the HTTP headers that's the version of flash at the victim host is running and the first three characters uh the first three bites of uh this is a flash archive zws or CWS are are the asy representations of the first three characters of any flash exploit that I've seen in the past couple of
years that's what was running on that my vulnerable host
it's just a browser header this is ActiveX an ActiveX plugin so uh anytime flash is being used by this machine whether it's the exploit kit or anything else if it's using that ActiveX plugin that xlash version will pop up in the HTTP hitter no problem and the executable the malware is sent in the clear so rig exploit kit is a mid-tier exploit kit has picked up some steam in recent weeks when angler exploit kit disappeared in June 2016 nutrino I saw nutrino everywhere where previously I had seen angler exploit kit and the past couple weeks the one of the major campaigns I've been tracking the EI test campaign switched from nutrino to rig and now it's just
running rig so I'm seeing a lot more rig exploit kit in the past coup
weeks all right EI test is one of the campaigns that uses rig exploit kit so earlier when I said uh uh exploit kit cannot exist by itself eii test is just what malware bites first called it when they discovered it back in 2014 at the time it always had e test as one of the strings in the injected code now it doesn't but it's still the same recogniz recognizable pattern of injected code in that compromised website so you can still identify it as what we're still calling the EI test campaign it's the same
guys right right that's EI tested what we're using to identify the campaign the payload for rig exploit kit is obfuscated how is it obus skated it is exord with an asky string and I'll get to that later so if I were to open up a pcap of traffic exploited in this case through the EI test campaign you've got your compromised website you've got what we're calling the EI test gate and then you've got rig expit kit if I'm running it through security onion like I did before see bunch of events for rig exploit kit once again I can submit the peap to virus total and see the same information so I don't need to set up a
security onion if I don't want to for whatever reason and interesting thing when rig exploit kit sends the payload now malware binary an executable file for Windows it will have a lot of bytes that are z0 so if you look in that area of the uh uh of the TCP stram where all the 00 bytes are represented you're going to see that texturing over and over and over again the problem is where does it start and where does it end so the way I figured it out is I go through the fourth bite from the very beginning is the first 00 0 bite in the malware biner so if I count back that shows k a
capital K if I count back four from the capital K that is your asky string that they're using to exor the binary and here's a python script I'm not going to leave it up uh long enough for you guys probably to write it all down uh this stuff will be a available afterwards or you can uh uh tweet me on Twitter or email me at the blog address and I would be more than happy to uh send you the text for that nutrino exploit kit it's currently a top tier exploit kit even though it was not as good as angler exploit kit was now with nutrino currently it's the only leading exploit kit that I know of
right now that is OB skating the payload using an actual encryption algorithm I want to say it's rc4 and they're using some sort of key and I don't know what it is so uh personally I don't worry about trying to decate the the payload I just pick it up from the infected host so opening a peap of traffic with neutrino exploit kit see the compromised website neutrino exploit kit the uh in this case you're calling it I I've been calling it The pseudo dark Leach campaign if I had to run it in security onion using the emerging threats Pro rule set we'll see plenty of alerts that show that this is nutrino exploit kit and once again I can submit it to
virus total and see the alerts there if I don't have access to security onion or some other IDs and Sim combination so nutrino exploit kit really the only indications that you're that you have that it's a payload on a visual level is seeing in the HTTP response headers that the content type is an application SL octet stream and the content length is similar to the artifact that you would find that's the actual malware on the infected host so what does an infection look like when you're browsing let's take a
look this one is not online anymore this compromised website it's called the wine group so if I'm uh sipping a glass of wine smoking my cigar part of the 1% uh browsing through trying to find what type of wine I want this is all happening Real Time by the way so you get a idea of the time it takes from the time that you first hit the compromised website to the time that the infection happens and there it
is that popup window doesn't happen anymore this is a cryp mic ransomware which is a uh I believe it's a a new version or another uh family uh prior to that was grip the XXX all of my letters to the editor of Modern Bride magazine now
going so I would go through and I would check with this particular ransomware it'll pop up a browser window I'll go through find my files are encrypted find I have have to pay Bitcoin and then I would use security onion and wire shark to find the indicators to compromise document that stuff provide samples of the traffic and ioc's on my website some observations based on my research ransomware is currently the most common payload for exploit kit traffic so if your grandmother is at home and saying I didn't do anything my computer's now infected uh it's possible that it may have been an exploit kit that happen if uh especially if she doesn't check her email legitimate sites and domains are
frequently associated with exploit kit traffing one of the things that I've seen is people will block legitimate websites the compromised website that kicks off the infection there's a technique that export kits use calls domain shadowing where you've got a legitimate website and they compromise their domain uh uh registration credentials and then they will set up servers so uh New York times.com for example not that they've actually been compromised but let's just say that their domain credentials were compromised the criminals will use those domain credentials to set up other servers like random string of characters New York times.com and then that's your malicious server that's your exploit kit New York times.com is not compromised what those other domains
are the last thing is exploit kit indicators are constantly changing so even if you block something if you block a particular domain or if you block a particular IP address odds are within 24 hours probably soon sooner that's going to be an invalid U shouldn't say invalid that's going to be an ineffective way of blocking export kit traffic so what's your best defense if it's so hard to detect and prevent this stuff the first one is to keep your computers fully up to dat and fully patched easy to say and probably easy for every one of us in this room to do for our own stuff kind of hard for our family members to do it kind of hard for Grandma and
Grandpa to do it kind of hard for a large scale Enterprise with hundreds of thousands of computers to worry about to do you can Implement browsing restrictions uh there's also Group Policy restrictions that you can do that would lessen the chance of malware if it actually gets to your machine through an exploit kit of being uh executed and finally threat detection prevention and protection Solutions uh uh at least in the Enterprise environment are a way that many Enterprises try to combat this threat for example you can go to the poo.com website and find a bevy of Security Solutions I'd be remiss if I didn't mention this since uh halato networks is painful my trip here so to summarize we went over the
exploit kit concept cep exploit kit ecosystems common exploit kits examining exploit kit traffic and your best defense now we can do questions however what I would like to try is a little bit of exploit kit Jeopardy to kind of review some of the vill that we've had and there are
prizes so we got Concepts we got names we got traffic so let's uh somebody uh somebody raise a hand or somebody shout out category and price who's that answer traffic for 300 okay the traffic category going have a picture a wi shark capture of traffic that I just presented earlier and you'll have to tell me you sir will have have to tell me what exploit kit that was if you get it correct you get this land turtle device here we go what exploit K is this give him a chance to answer I see a hand in the backo yes that is correct
dang
it all right sir you had your hand up in the back earlier
uh yes please traffic for
200 look familiar what is a that is incorrect sorry anybody else uh you sir Brandon pardon that is correct
all right we got time for one more question so uh sir concept concepts for 300 this is how an exploit kit is supposed to work I I I'll be very liberal with this answer
something simpler in general Sirah in the back I'm pointing to you yes uh would be taking advantage of a vulnerability true true uh all right anyone just shout it out behind the scenes there you go behind the scenes and while web browsing without any user ACC yeah it's kind of hard that's why it was a $300 question and uh let's try one more here dang it names
300 commonly used in malvertising campaigns first exploit kids seen using exploits for C yes you are correct it is magnitude $300 uh imaginary to the gentleman in the front
row all right anyone Concepts 100 the answer is cve 2016 0034 this is a $100 question so it's not too complicated to say what this is not flash you're you're getting too specific vulnerability there you go thank you I I've heard people say oh cve 201634 they're describing an exploit it's like no that's a vulnerability say cve 2016 0034 exploit and then you're fine but don't just call an exploit a vulnerability and we'll do one more here before I sign off
anyone what is next one kit plus infrastructure that directs potential victims to it there you go $200 imaginary dollars the gentleman who answered that
question and that's it I don't want to waste any more of you guys' time thank you very much for uh coming out and bearing with me