Analyzing Emotet infections

Show original YouTube description
Show transcript [en]
good evening everyone how you doing brad uh doing okay how are you doing good good let's get this show on the road so today presentation is analyzing emote infections the presenter for this is brad duncan bran duncan is currently a threat intelligence analyst from the unit 42 team at palo alto networks he shares threat indicators about emote trick bot and other and other high profile mass distribution malware campaigns through his twitter handle at malware under slash traffic brad has shared malware and packet captures of infection traffic through his blog at www dot malware hyphen traffic hyphen analysis dot net with more than 1600 pages since the summer of 2013 he also writes technical diaries also
known as blog post for the internet storm center at isc.sands.edu last year he ran a full day traffic analysis workshop at b-sides tampa this year he's working on a series of video-based wireshark tutorials that will eventually be released through palo alto networks with that being said i present to you brad duncan all right uh hello everybody uh thank you for coming to uh to this presentation um the pcaps the packet captures of uh traffic used for this presentation are in the url listed on the slide malware traffic analysis dot net slash 2021 slash b-sides tampa
and uh uh ernest uh went through this all in the intro in the introduction so i'm not going to hash over the stuff again once again uh packycatchers of the traffic that we'll be looking at in this presentation and malware recovered from the infected windows hosts and a pdf with the slides from this powerpoint presentation are all available at malware traffic analysis dot net slash 2021 slash besides tampa so while we're going over some of the introductory stuff you can if you want to follow along with the pcap analysis feel free to those peak apps and the password for the password protected zip archives on that site is infected the word infected all of our
case letters now if you're going to follow along it is much easier if you've customized your wireshark column display according to the first section of a video that was posted to youtube from my workshop that i did for shark fest 2019 shark fest being the annual wire shark festival i'm sorry conference uh in the united states and there are other annual marshal conferences uh that actually happened in europe and asia i believe but i also have a list of all the wireshark tutorials that i've written published through palo alto networks at my blog malware traffic analysis.net tutorials now if possible you uh should use should use uh um wireshark version three
i've been told to turn up my microphone or speak a little louder all right is this working better if it is i will uh i will continue excellent excellent all right so um what uh what i generally do is i'll use wireshark uh version three and a lot of the linux distros that i'll be reviewing pcaps in uh generally for example debian and some of the centos distros will use an older version of wireshark 2 which has some different commands than wireshark 3 and wireshark 3 is better what you see here is a screenshot of wireshark uh that i'm using in xubuntu um with a plain white background so for this presentation we will review
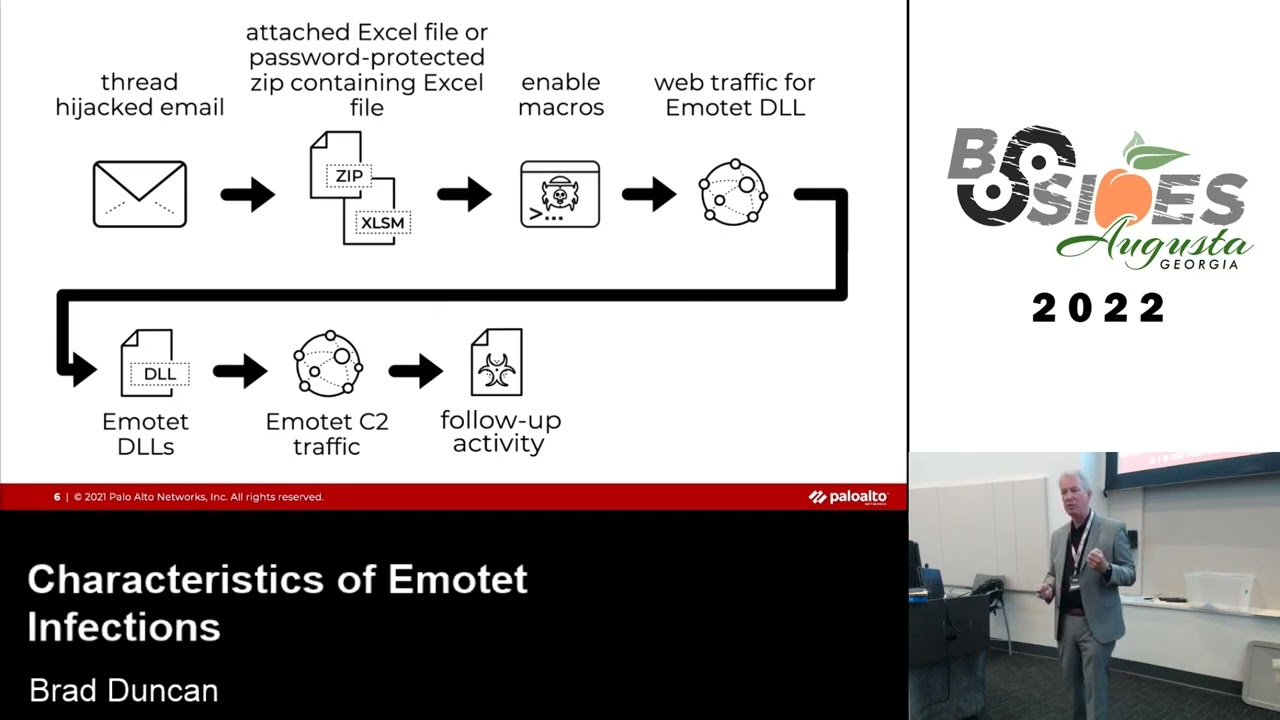
the chain of events for an emote infection we'll talk about emoted's final days because the botnet was actually taking down uh well after i had submitted my proposal for this particular presentation to besides tampa but it was at the end of january the last part of january 2021 approximately two months ago that the emote botnet was taken down by law enforcement authorities we'll discuss that and then we'll get to the meat of this particular presentation which is examples of emote infection traffic and post-infection activity now for emote the key thing the the key piece of emote of the chain of events that starts the infection is the microsoft word document with malicious macros so the word document itself is uh just
fine until you enable macros and the macro code is the malicious is the malicious part that kicks off the infection now you have different methods of getting this word documents all through malicious spam right so an email may just have the word document attached to it which is pretty easy for spam filters to detect the email may have a zip archive that contains the word document which is a little harder to detect much harder if the zip archive is password protected which will have the password in the text of the email message in other cases malicious spam will have a link and you click on the link and it delivers you the word document so you avoid having the any sort of
malware directly attached to the malicious spam another method of doing this is to have a pdf file attached to the malicious spam and that pdf file will have a link to download the word document which seems a little more convoluted i haven't really seen that personally i haven't seen it since a little over a year ago but i think other people have reported these pdf attachments used for malicious spam distributing emote they've reported it uh well into 2020 well after i stopped seeing them personally this is the latest template that i consistently saw in the final few weeks of emote before the botnet was taken down now once you have that word document and you enable macros
it generates web traffic to retrieve the initial malware binary for emote uh this initial binary ever since uh october and november of last year has been a dll file prior to that it was a windows executable file an exe file once that dll is run you start seeing command control traffic generated over http this is encrypted data over http channels it's not https because you're able to see the http headers in response uh headers the request headers and response headers from to and from the command control server servers used by emote of this encoded c2 traffic will update the initial binary uh will perform data exfiltration will deliver follow-up malware and we'll also deliver a module that's run
in system memory from what i can tell that will uh kick off spambot activity that literally turns an infected windows client into a spambot sending out emoted male spam so before we get into the actual traffic let's look at emotetet's final days so in january 2021 a coordinated law enforcement effort headed by europol took down the immotec.net and you've got some of the countries law enforcement agencies from different countries that participated there there's a group uh called cryptolimus which uh has been keeping track of emote activity for a long while up until january 25th which was the last day that they saw any new uh activity from the emote infrastructure and botnet before it was
taken offline now it was incredibly easy for me to generate i've got honey pot email accounts through popular online services like yahoo outlook gmail aol even and this is uh from a yahoo honeypot account uh that i use basically i set these up on infected windows hosts and emote will steal these uh email chains uh that i have on these legitimate hosts and we'll send it back to uh the various other hosts uh various other email addresses that it finds in those email chains so uh this particular yahoo account you can see that i have believe all these are emote messages and you can see that some of them are password protected zip archives but the last one the most recent one
that i have was dated 28 january however if you were to look at the email headers you will see even though that yahoo email server received the email the last email that i got on the 28th of january if you look back through the email headers it looks like it was sent on january 20th over a week prior just for some reason didn't get to that yahoo email account now the infected windows host uh that i'd originally infected with trickbot i'm sorry with emoji whenever this happened uh was a uh used a outlook account from a username with the initials kr and it uh sent this email chain that had also gone out to a yahoo account
with the initials uh username with the initials a s it has an attached zip archive and you can see that it says archive password to zero to two and you can use that password to extract the word document from the zip archive and once you open that word document in a windows environment you'll see without microsoft office anyway you will see that it uses the same template that i had been seeing in the last couple of weeks before emote was taken offline now emote as much as it's an information stealer it is also a distribution system for other malware so if a uh if a host is infected with emote you need to check and see if it was
infected with other malware and by far the most common uh malware that i saw especially in january 2021 i only saw trickbot but i think other people may have seen a different malware like cacbot but law enforcement officials in the netherlands are in the process of delivering an emote update that will remove malware from infected computers on april 25th uh approximately a month from now uh basically netherlands law enforcement officials had taken over two of the three main command control servers within the emote botnet infrastructure and so if there are any computers out there which i'm sure there are they're still infected with emoteet they're not getting anything stolen but they're the law enforcement officials
will use the server the emote c2 servers to send an update that will remove the emote infection from those hosts now let's look at examples of e10 infection traffic and the post infection activity once again malware traffic analysis dot net slash 2021 slash b-sides tampa uh we'll have password protected zip archives that uh contain the p caps that we'll use here today in this presentation there are four p caps i'm sorry there are five p caps covering four infections that one that happened on the 20th of january had to split into two parts or it would be too cumbersome and way too big again another um another warning if you're following along that uh hopefully
what you're going to see for images in this presentation that i'm going through is a wireshark that column display is is customized according to what we have in that youtube video from my sharkfest workshop in 2019 our first example is from the 13th of january it's an emote infection with trick bot this happened within an active directory environment where the victim the actual infected host is at 10.1.13.101 the host name is desktop bwuxt58 the windows user account is jimmy simmons and the domain of this active directory environment is amazingboxes.net so if you open this p cap in wireshark with a customized column display and you use a basic web filter which is uh something that i cover in one of my
other tutorials i've got it highlighted there basically with this setup you can see get a very good idea of what's going on web traffic wise on an infected windows host or a regular windows i was just looking at the traffic that's generated and this is a windows 10 client so you'll see a lot of https traffic where we won't see the urls but we will see the associated domain names a lot of that stuff is going to domains for microsoft.combing.com msedge.net azure edge.net so live.com there's a lot of stuff that is generated by microsoft windows 10 and some of the applications that are included in a windows 10 installation what you'll see is the very first
http get request is for kato recipes fit dot com and it's a get request so katorecipesfit.com is i believe a legitimate website that has been compromised that is hosting uh in imotete malware binary which in this case is a dll and then you'll see http post request to an ip address directly to an i p address with no known associated domain name now we can more closely filter when we're searching for the emo tech malware dll if it's sent over http if it's sent over http we can find it using this particular wireshark filter ip contains this program cannot because that string has spaces you have to put it in quotation marks and yet it is case sensitive so
it usually means this program cannot be run in dos mode or this program must be run or cannot be run under windows 32 mode or whatever but usually if you look for this program cannot that will find uh approximately 90 to 95 percent of the windows executable files or dll files that i see uh on a routine basis when i'm investigating malware traffic from a windows 10 host and uh um now if it's over https you're not gonna see this because the traffic will be encrypted and at most you might find a domain name that is um that is sent over uh you know some uh weird domain that might be associated with emote it'll be hard to find but not
necessarily impossible but if we were to use this particular filter in our pcap in wireshark looking at our first pcap we'll see two frames in the results in the column display the first one is to i p address 207 180 199 176 these are this is traffic coming back so this is the source ip and you'll see another one coming from 205 185 216 42 which actually is a windows update sending a windows executable file to that windows 10 host this is a very common thing that we'll see that windows 10 tends to do every day or two or so there's something that windows 10 is updating without your approval but we can follow the tcp
stream for the very first http request i'm sorry the very first frame in the column display so basically you want to highlight that very first one uh right click on it left click to bring up the menu uh follow tcp stream and you'll see that this shows uh up the very top there there are the there are the information for the url in the http uh request headers for k2recipesfit.com you'll also see indicators that this is a windows executable file or a dll because the first two ascii characters of the file itself the first two bytes spell out the ascii characters mz and you'll see this program cannot be run in dos bone also which i don't have highlighted here
i don't have an arrow pointing to it but you'll see in the http response headers under content disposition it says attachment file name uh string of characters.dll and that's common that we'll see uh for an emoteet infection we can export this dll file from wireshark using the export objects function so you go to your file menu export objects http that will bring up your http export http objects list it's the very first one with the hostname of keto recipesfit.com so you can export it and um i'm not going to go into what you would need to do you can submit it to virustotal you can and hopefully you're not doing this within a windows environment
because uh windows defender would probably uh would probably detect that right away as i'd said the other frame result when we did that ip address contains this program cannot is uh from windows update so we can follow the tcp stream for that uh particular result if we went back and filtered on that again and this is what we should see but there are several requests uh in that pcapp to [Music] au.download.windowsbay.com if we want to check for emote command control traffic in this pcap we can use the following wireshark filter http request method equals post and i do not want to see any http request uris that contain the string mor13 and i don't want to see
any http requests where the http host contains the string ocsp dot mor13 is traffic in this case related to trickbot it's an identifier for that particular trickbot sample and ocsp is prefix for non-malicious traffic that we will occasionally see in uh normal web traffic for windows hosts so if we use that particular filter this is what we should see we should see a bunch of http post requests to an ip address not a domain name some of these http post requests are going over tcp port 443 that is not https traffic that is http traffic because you still see you still see the http request and response headers to and from the server that it's calling out to if
you were to follow let's say the very first frame that's showing in the column display here you should see this you'll see an http post request where it posts it you know using form data that you would normally see with a legitimate post request from legitimate traffic if it was even over http because most of this type of stuff for legitimate traffic happens over https in this case you'll see a bunch of encoded or encrypted data and that is uh emote exfiltrating stolen data from uh the infected windows host whether this is system information or a string of uh email email chains that it that it acquired from the infected host's mail client in this case it's about 6.3
kilobytes of data so it's probably related to system data and maybe some usernames and passwords if i had to guess but let's go back to our basic web filter and we'll look for trickbot traffic since we can't really determine uh much of anything else from uh the emo traffic other than this is what emote post infection traffic looks like for command control traffic going to and from the command control servers so if you filter on that basic web filter and you scroll down you should find uh what you should see is some what looks like https traffic in this case over tcp port 443 and it does not have a domain name associated with it that host name
when it's set up like that it is blank and that's because it's going directly to an ip address unlike http traffic if it goes to an ip address it will actually show up in the host field for https traffic we will not see any hostname or any ip address other than what's showing up as the destination ip address in a different column now trickbot uses ip address it has the infected windows check its ip addresses public ip address so what you see there with icannhasip.com is a legitimate ip address checking service it's just being used by this particular trickbot malware infection if we scroll down we can see more uh https traffic to ip addresses over tcp port 443
and tcp port 447 and we will also see i have some arrows pointing there to http post request with that string mor 13. now if i want to filter on just those particular post requests i can add either the ip address to that or http request uri contains mr13 but in this case i just opted to use the ip address and basically tack that on to the end of my basic web filter so for trick bot uh the http post requests that are sent these are sent by data exfiltration uh modules password stealers and whatnot that trekbot uses so in this case you're going to see post slash mor13 once again that's an identifier for this particular trickbot sample
basically the method of distribution the specific distribution channel is what that identifies you'll see the hostname of this uh infected windows host you'll see where it says w1001 which is the version of windows and then you'll see a uh a exit a small ascii string that represents that particular infected windows host this identifying number so those urls that in in slash 81 have password data username and password data those urls that in in 83 have form data for example if i went to sign up for facebook on this uh infected windows host prior to that that form data would probably still be you know that i used to fill out username passwords phone number whatever you know
when you sign up for an account and then urls that in slash 90 have system data we're not going to go through every one of these here you can follow those tcp streams at your leisure and look and see what types of username password and form data is being stolen by trickbot but in this case i wanted to focus on the url that ends in slash 90. this http post request which is system data so you can follow that tcp stream and that post url it's posting data that contains a list of all the system processes currently running on that infected windows 10 host it contains the system information host name mac address whatever the ip
network configuration local machine data it contains active directory information in this case right because this host is in an active directory environment so there you may also see usernames and hostnames from other windows hosts in this environment you won't see it in this particular one because it was just a domain controller and uh one specific client but you can follow the tcp stream you can start scrolling down and looking at all of that particular information now with trick bot i like to try the following wireshark filter which is http request uri contains dot png now there are no examples from this first example but there will be in our second example so if you'd be so kind as to open up the
uh pcap for 2021 or 120 part 1 from the 20th of january this is an emote infection with the trickbot and spambot activity it's a standalone environment so there's no active directory domain the hostname is desktop user 1pc and the windows user account name is user one if we do our basic web filter like we did for our first example you're gonna see the same type of things and if we use that filter that i talked about in our for our previous example http request ui contains.png you're going to see a url and you can follow the tcp stream for this you'll see it's a windows executable or dll file you can export it from the pcat just
like we discussed earlier export it from the pcap and find out if it's a dll or if it's a windows executable file in this case it should be a windows executable file
that should be example two i messed up the slideshow here uh but uh we're going to uh look at those trick but post request if you want to do that again basically add http request uri contains the morrow one more one is the identifier this time but you can follow the streams you can look at the same thing that we saw earlier in our first example in this one if we go back to our web filter for the first pcap part one of our second example what we will see is we scroll down towards the end we're going to see what looks like https traffic to ip addresses using tcp ports associated with smtp this is tcp port
25 465 or 587 so that's an indicator that you have spambot activity on your infected windows host if you see this if we filter on smtp we can see some of the smtp commands before all of this traffic uh you establish a smtp connection and then you immediately go to encrypted traffic you can see at least one line two lines in there that say start tls so we're not going to see anything in this if there was unencrypted smtp what i could do with this particular pcap is i could export imf objects as you can see here imf stands for internet mail format but there is none in this particular pcapp because all of the spambot traffic from this
infected windows client is encrypted which is uh and that generates a lot of a lot of traffic for a pcap you could easily uh you know it wouldn't be more than a an hour or two before you start getting a gigabyte or two gigabytes of data that's uh um you know that's literally being spammed out by an infected windows client uh you know within your land so i took uh i took approximately this is approximately one or two or three or four minutes uh of uh traffic later on that actually has some unencrypted smtp traffic what you're seeing here is your you continue to see http post request uh uh generated by trickbot that has
that string mor1 basically what's happening here is it's a trickbot is calling out and it's not receiving an appropriate response from the trickbot command control server but uh what we could do with this one is we can check you can easily check through your wireshark display filter if there is any emails that were sent over on encrypted smtp and you can do this by filtering on smtp.data.fragment in this case we see five results in our column display so if we see these results we can actually export these five emails from the pcapp using the export objects function and selecting imf for internet mail format and if you look at one of these emails that you've exported from the pcap in
a mail client like thunderbird which is what i would recommend uh you will find that it is spanish language and it's a password predicted zip archive and it is going to a mexico based ip address once again you can use that you can use that password to extract a word document and it will have the exact same word document template that we saw in our earlier in this presentation now our third example is an emote infection with trickbot in unusual https traffic so we have another standalone environment that's using the same hostname and same windows user account name that we saw before now if we filter using our basic web filter on this particular pcat
what we'll see is we'll see an http request the very first one and this one actually returns a word document so if you filter on your basic web filter see that http requests that get request to in-hip i can't even pronounce what that is to that particular domain on 171 244 132.130. follow that tcp stream you will see indicators that this is a microsoft office word document and literally when you see these uh this was downloaded uh by clicking a link in an email which brought up the web browser and literally the file name that it shows in the http response headers is the file name that the victim would have seen when they downloaded this word document
that's what the web browser offers to save it as if we go back to our basic web filter we scroll down a little farther the second http get request to trendmoversdubai.com returns the emated dll now once again we can use the export http objects function to get that word document in the cmotet dll from the pcap and we'll also see below that we start seeing http post requests to ip addresses with random uh alphanumeric characters with backslashes which is typical for emote we scroll down even further we will see indicators of trickbot activity which uh includes https traffic to over tcp port 443 maybe tcp port 447 and maybe tcp port 449. um and we also see one of those http
requests that ends in png which is also another indicator of trick bot activity if we scroll down even further what we start seeing is a little bit of unusual traffic because we're seeing lots of https traffic to several different ips over tcp port 443 every minute so if you know you're seeing uh you're seeing 10 20 uh addresses and that's not how trickbot generates its https traffic so this is something unusual this is something odd now you can actually look at the certificate issuer data for the certificates used when that https traffic is generated and i have a wireshark tutorial on examining trickbot infections that kind of goes through this the https traffic in this pcapp
the stuff that's not trickbot has different certificate issuer characteristics than what i normally see with trick bot https traffic so we can filter for the certificate data by filtering on tls handshake type equals 11. scroll down to the end of that list this is one where the source ip is 216 128 1316. select that particular frame go to your frame details window and start expanding where it says transport layer security certificate and you work your way down to the certificate issuer data and you see where it says already in sequence you'll see uh uh country name as cn organization name is nl and uh organizational unit name is sd and a common name which it will we'll see with the
various legitimate stuff where you'll see a common name which is the domain name of a particular website in this case that syxe is not a legitimate domain name even if that string of characters might be a legitimate domain it's not in this case because we can look at the certificate issuer data for the previous result at a different ip address and it has a different string of characters for that common name if we do the one before that the frame before that look at the certificate issuer data we're seeing the same country name organization name organizational unit name and another random string of characters alphabetic characters and uh so you're seeing random letters.com and a lot of the stuff
although it's not consistent it is that mostly and this is not what i see with trickbot with trickbot itself now it could be caused by a trickbot module and this may be there is a trickbot module that does use tor traffic this could conceivably be tour traffic but it could also be something else i was not able to find whatever may have caused this on the infected windows host finally emoted infection with spambot activity this one is another active directory environment bearfighters.com this is on the 22nd of january this is the last uh one i believe this is the last one that i got because i didn't check it in the last couple of days or maybe i did and there
just wasn't much in there in this particular pcapp you'll see four get requests before the server returns an email dll this one was taken from a document that was part of the email itself and not a link so the word document when i enabled macros it went through uh four mac uh four domains four urls before it returned to dll you can follow the tcp stream on those and see uh either four or four not found or 200 okays with the message that the file requested file was not found again you'll see tcp ports used for smtp traffic that looks like https traffic with this basic web filter we can filter on smtp data fragment and
find one email example and if you were to export that you would see that this would be another example of spanish language malicious spam and geez i went backwards so that's really it i've kind of rushed i've really rushed through this uh stuff normally i would tend to spend a bit more time uh on this stuff but uh we're stuck with uh virtual events like this uh so it's kind of hard to do the training or to properly do this in a way where we can uh where we can give enough time uh i'm limited within the space of this presentation uh and i tried to give you as much uh new examples of anyone that activity
that that i i could uh again if you want to better understand how i use wireshark to analyze uh malicious network traffic i've got a list of tutorials most of them that i've published through the my employer palo alto networks and that's on my blog now we're traffic analysis.net slash tutorials and once again you can find the powerpoint presentation pdf document containing the slides in this powerpoint presentation you can find examples of you know the pcaps that we reviewed today and examples of malware retrieved from the infected windows hosts for all four infections this is at malwaretrafficanalysis.net 2021 slash besides tampa and i want to thank you all for uh those who stuck around oops
those who stuck around
and if anyone has any questions uh feel free to send them uh through the general chat i'll be more than happy to uh to answer uh otherwise i'm just gonna wait here until uh until ernest or someone else comes back to uh um to uh uh to move the uh move the uh conference along but seriously if anybody has any questions you could also email me at brad malware traffic analysis dot net feel free to email me ah don't forget to ask a question for a chance for a bag of coffee so if you like coffee ask me a question if you don't like coffee ask me a question and then donate the coffee to someone
you don't like thank you justin i'm always happy to share this information uh the slides for these uh talks uh they should be uploaded what will happen is i will be contacted by the event organizers and i will i will provide them the the slides but a pdf copy of the slides is already available on the link uh on my blog uh where i have them set up and that's probably what i'm going to send to the b-side stamp a crew anyway excellent yeah and uh yeah i fully recommend if if you are a uh if you are a technical nerd or a pcap nerd and like looking at uh suspicious network traffic especially the web-based uh traffic
uh do i see issues detonating the malware in my lab to collect these b caps for me no i'll use either isolated physical environments or virtual environments in in the virtual virus or windows vms on non-windows hosts so i don't have to worry about uh necessarily about the the stuff infecting outside of that virtual environment now people will tell me that there are ways that malware can escape a virtual sandbox and that very well may be true but the vast majority of stuff i deal with is commodity malware that is literally sent out to everybody and it's not trying to be too stealthy it's just trying to infect a windows host and it's pretty easy to detect once
you've seen enough of these so uh i don't in my lab i don't really have any also i i isolate i'm not going through my you know through my work i p or my residential ip when i'm infecting a vulnerable windows host i'm either going through a vpn or i'm proxying through some other residential ip address or phone line ip address or whatever so i'm generally i'm generally not not too terribly worried about that any other questions what in what got me into investigating this type of activity or what interested me in this um that's it's kind of a i don't want to say a detailed story but uh um my my background is in the u.s air force uh so i did
intelligence work so i did a lot of analysis for classified intelligence work while i was in my 20 years in the u.s air force when i got out in texas there wasn't a much of a call in this area for my particular specialty in the classified intelligence work i was doing so i had to find something else to kind of translate this uh of my skills towards and i was fortunate enough to get my foot in the door of uh a contract work at the uf the us air force cert uh monitoring air force networks and uh i gravitated i don't know why i gravitated towards the traffic and the more i investigated it the more
fascinating i found it and quite literally the more i realized that there wasn't much out there that uh that people were sharing as far as the actual traffic at the time this was uh 20 2010 or so when i got out of the when i got out of the air force and started embarking on this new career path i also didn't have too much time to waste because it wasn't like i was a college graduate uh getting out i literally uh you know 20 to 25 years past that date and uh so i didn't really have time to waste so i dove into it head first and uh uh i guess it's just a uh it just was a way
of um of uh you know my personality really fitting uh the subject matter and the fact that that niche this kind of specialization wasn't really uh wasn't really being promoted or filled or advertised out there so that's when i started the blog to share this information and that's why i do what i do now and my the the my focus being on the infection traffic is because uh a lot of people will focus more on the malware itself and uh what happens on the infected host as opposed to identifying characteristics of windows based malware infections if that makes any sense i don't know ernesto that answers your question as to you know what got me
interested in malicious network traffic in general but that that's really how i got into it what i would uh what i would recommend for people is to uh if you're just starting out in information security in cyber security whatever you want to call this to kind of find that niche find uh what you find interesting that may not be covered by anyone else or has very little coverage you'll find those uh find those paths a lot of in don't be afraid to make mistakes the hardest part of tracking viruses and p caps uh i would have to say that uh with the web going more and more to encrypted traffic uh https only and all that it is getting
harder and harder to i'm seeing a lot more malware use https channels for its command control traffic and i'm seeing more and more compromised websites that are hosting malware they're doing this over https so unlike when i first started doing this uh say in 2010 and before where you would see a lot of http uh web traffic that was related to command control and uh uh malicious uh malware binaries passing over the network unencrypted uh a lot of that now more and more we're seeing more encrypted stuff it is uh it is unusual it basically encryption means a bit more work for uh the malware authors and the bad guys to set up their infrastructure so it's not impossible
and we're seeing it more and more so at some point i would say in the next five to ten years we're going to be seeing a lot a lot more encrypted traffic associated with malware infections that'll make it hard harder to identify the type of malware involved in in that case then you would have to start focusing on okay what does the malware look like if you're reverse engineering it or what does the malware traffic look like if you've got uh if you're able to decrypt the https traffic or what does the malware do on an infected windows house what artifacts does it leave behind so i i do a bit of that as well
but that's in conjunction with the uh malicious traffic and uh so it's a uh it's an evolving landscape that is moving more and more towards uh encryption on a day-to-day basis which makes it harder to find the stuff and you're welcome digital overdrive thanks thanks for the question
what's very interesting is uh over the past few years i don't talk that much so uh my voice gets very um uh uh very easily winded now so i'm going to start talking and let ernest uh get back on here it looks like he's tried to pop in a couple of times already to move on the presentation uh move on the uh conference what's going on brad no i have but overall it's okay you were insane questions and i had to jump back you know one minute we had none the next minute there was a bunch so i was glad that we were able to uh get those q and a's answered um with that being said does
anybody have any last minute questions that they would like to ask we have five more minutes if necessary all righty so it seems like uh that's all the q and a's we have here brad um so that concludes this presentation do you have any last minute words uh if anybody has any other questions uh feel free to email me at brad malware traffic analysis dot net i may not answer right away but alrighty um with that being said thank you brad um everyone else i will see you at three o'clock for our next or our next and last presentation for track two thank you so much have a wonderful day