Investigating IPv6 via UPnP
Show original YouTube description
Show transcript [en]
hey that works alright always nervous about it I'm Alex I come from Cisco Palestine this is my third time a possibility first time I think here four years ago I did a talk about some exploitation mitigations - initiative glad to be back and lets you talk about something that I've been doing so what I'm actually going to talk about today is a bit of internet scanning ipv6 can get specific in particular they're going to go over why it's interesting what whites from Austin little over how you can key can be used to couples in that and then just somehow and just show some results of analysis so a little bit about why just to go
through the previous work and the motivations were playing around with this dough with all the advantages internet speed all of us have a 35 speed internet to phone and especially in the offices if you work for a networking company or something so scanning the entire Internet ipv4 internet has kind of become simple you can do to the matter of hours not weeks or days and there are tools available for that like Las cañada's email which are specifically designed to to use the high benefit and the mobility and spend that first minute with you and that was elective subjects personal research because now you can quickly sped up the scanners technically internet got some interesting results
back about anything sure interested in and work from those results so some of the examples of in time scanning research results where the popular scams of for money and are those are posted all of the for adversity fun a bunch of medicine and you had high profile ability like Hartley where researchers were running repeated networking scams already things are not trying to gauge the exposure to this one ability as well as to gauge tax adoption rates and kind of measure what they're not on the Internet's regarding this particular vulnerabilities and then on the other side we had things like here on botnet which any infected emotion I hope TBI citizen and user as you were
devices just be testing the currently 12 potentials and spreading around for just getting Internet all of these things are being possible because it's relatively feasible to scan the whole life reporting for that Oscar cell can tell us have know some
[Music]
[Music]
[Music] how quickly they're being adopted get to get some results per day and that's all nice and dandy with ipv4 internet but what problem like before is we've been running out of ipv4 addresses in early odd-even yes running out of might be forever solving death like new sticks again the late nineties to melody that follow a switch go over 200 between the data that makes not only use a new number of addresses is huge they're the coldest possible populations who can this start from one and go forever so we need to be so we need to give it the clever when we want to scan the ipv6 intro the first thing that you need to
do when you want to scan something around three six internet is together a list at the coasts of addresses that are currently being used to convey these and target those and just scan the coal-dust base like you did with that beta for the in order to do that to be clever as some folks in the past we've done different interesting things to kind of mask the back to post a nice to expose that are present on entry for example sure none of projects a bunch of pens and PD stairs we've got out of two public pools or FTP which were used in live distribution so they ended up having a bunch of live server cracked into them twice per
Network time updates and the moles their musics gonna give it to you at the back there's another project called ipv6 tipless which publishes the updated list of aggregated list of active ipv6 addresses from different sources and the d2 is the Judas's so - so the public to public information like certificate transparency locks you crawls transparency laws removing a new certificate new IP 600 in there he used right hapless sensors to gather information from there and make many other tricks on them required engine up for position some don't but they just aggregate the less which is several millions of active I produced the exact person which you can use as a basis for for your scanner and getting a
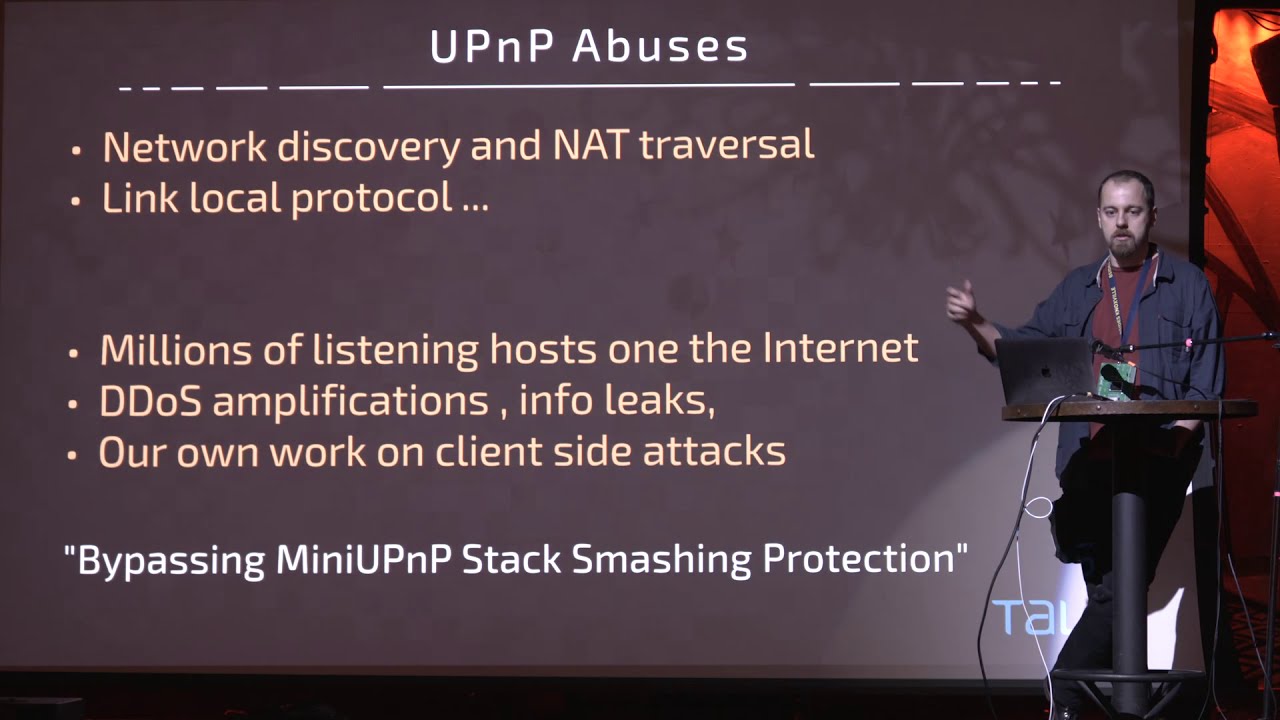
similar fashion project ipv6 far as published a couple papers this research from [Music] two main uses it's meant to be link-local so there's no point of there being any internet life you can't be traffic as I mention its network discovery protocol when you device connects to the network economics Bicol network aid [Music]
but this [Music]
[Music]
doing and for info leaks it doesn't have any authentication so you can just talk to the device and how many devices support existing queries okay give me your interest in information about the local network from big you can't be correcting the map to type sir and I actually did a bit somewhere with you maybe before a single packet to everybody on the network see just from this network and the packet was like this they weren't the park this packet is the location header which has a URL and then URL points to an XML document that particular XML document explains all the capabilities of that particular device so state TV on your network it will announce its precedents and say ok DB if
you want to take a look what I can do that's these XML parsnips and can tell you that I can use for streaming or something like that so this gives us
so we had a bit of we were thinking about something and we wanted to do these infrared lights gamma so 5 through 6 so it came up with a bit of clever bit so we asked ourselves what the top one is we replaced the URL into location Heather we replaced the destination post or target post URL using this particular [Music] one three six out of there would the receiving party actually trying to connect over x86 that's that's excellent and yes we just immediately and with just a little bit of flair to us like adding the target that we four ounces to the end of the location header we could actually as a result get a HTTP request
on our side effect at our site on our ipv6 HTTP server with enough information to the we can tell okay we set the items that this has been a poor actress West came back from the equity of six of us let me know those two have the signal to say no and what's this so remember what it says here none of the Newman's of post on the internet listening for you can't be traffic if something happened to have votes for activity in who sent of this packet they accepted to Parsons we make HTTP requests to our control that server which along the data and against menses Peninsula so what do we actually get from this once Department actually
parses the interview project they decided effects that that XML it will make an HTTP request and we lock that request and we can see in our web logs that we have a here in orange burst with envy I knew six animus from which they requesting floor and because we use for address in the request itself we can connect to and we know how eighty-six I agree for a pair so we can include it okay we have one post and it had these two addresses running a little sample what that enables us to do is that maybe can both sides to see very discrepancy to make me comparisons and so also everything that we get from this
each degree question that both you can be basins happily include some interesting information in the agent header information
understand oscillator all right so let's not go through how we extracts introduced a couple of engine converts the scan itself all this gathered we did in the first page we want to get those have this pair we want to make to make a pair of ipv4 and ipv6 now this period belongs to the same code and to do that we get the code live all of their equity safe senders to do that the money fight mask M which is a member of scanner optimized for speed
[Music] better for each one give that location Heather we are 36 average the power web server and the enemy including a group that I agree for others I do include collect before I just called the party wants to get it back following our data with just sending garbage we can actually authenticate the correct result so we can go back all the way to request and then [Music]
6:7 stop dude
now all we have is pairs we can continue to the next page next page black people have affairs big picnic lopsided the truth of every 496 sign of it was fireball in space frankerz foresight but some pieces there people might not actually know that they found these six connectivity and therefore not have a horrible place for so there will be less filter in parallel and maps games against all the all the posting our TVs we stand for open popular
on both sides and the reports the logs that's it this belongs for business you know reports or filtered words so the question immediately we find a course where we have we have that discrepancy where something is smarter walls on the r34 side and is still open on the x86 yes we did find that here's an example look like starting protective mask where divested because but in the first first first and macro we can get these four hours per port 25 which is the Windows Start seaport you probably love to expose windows with those summer shares and Windows networking on the oh crap there are community when you do with choosing an update so we love ya
before Sun properly filtered but three or can ii thought when the equity six where to see important we can see it in children and okay from this map atlas that you can't really tell that it's the same post but he is without a mask because humans using something [Music]
[Music] [Music] I
[Music]
network network diagnostic circuits and what you've done here is its first I'm sending out a UDP packet report one two three score and the pact of time 300 bytes just filled with with nothing device and a little porridge packet of the tree so what in fact the what I expect to happen is the packet will go treat hops away from me and I'll get the notification to the back attack and that's exactly what we get from summary of the ticket summary level speed memory we've got a detail serum through defendant from this is there and the packet back to this is what you all right so that works that's what we expect but we set the scene the exact
same packet report 1900 we don't get nothing back so something is dropping these package dead and the only difference is the port Pete so that's included the level threes actually doing doings UK peaceful tree probably came up Aditya visited the bunch of these devices we saw
[Music] so I replied we have 12,000 unique ipv4 and ipv6 at espares so that's not huge number
we have some really tight constraints just being actually working it's the first we need a toast out there in the equity court with the public before you have to request a URL so once he temp would you concede that would actually get up and request our URL or visit there you are L so no alphabet dos and don'ts needed to have to be doable so to have public entities what we got a response or mostly consumer devices and cameras and work that's 40 devices they insisted for boxes
so since there are ways to generate identities like there are different ways your system computer or shooting I'm pretty safe tempest wasn't trying to connect to the internet and to recognize doesn't do some see what's what the usual thing that they see so when we saw our [Music]
and which probably about this problem one was eui-64 which is basically which every six coming up with diabetes six is based on your Mac habit which is not good for privacy you're leaking your mattress all over the integers using eui-64 to generate the public Oh
[Music]
[Music]
[Music]
[Music] their user agent string so whether they protect or vserver we actually see what they're running which also lets us what type of device they're talking we're just limits or device and again from the Virgin name we can judge they're mostly cameras security cameras that storage and a large about the Smart TVs TV it's just simply all the windows host we're actually clients with these computers that's the way it will actually talk to stay with this box that we saw we're actually running by the corner flies like murderers for a big part for something which include their own versions of the library have no surprises there
[Music] rather small arteries embedded so that lets you follow what was a surprising was that the most popular version of beauty was 1813
[Music]
[Music]
or right build what we see here is Google for these you can actually pick up the there's these particular versions are parked up major releases of a product for example so thunders tender dozens of one ground and doesn't change anything
Midori
one of those 3.0 which is an older home mostly by 3.10 which is with chemicals which is also and I was surprised to find it so few close that's where other newer person newer the board of X but on the other hand there was a hex blow post still running Colonel Reardon's six which sound do embedded distributions like open
and we have to enter it side most with devices if you can connect a device Android wear fire the one is one which is also and so nothing too surprising here
meet questions did become as we do this was could we find those toast with full transparency
there wasn't from a bunch of well some extremists have died he did of metaphor and those words included majority those sports where HTTP FTP for our summer stairs or SMB shares which is
I expect peace numbers will be the larger numbers found this two out
[Music]
divided and ipv6 connectivity is where you divide 100 you might actually have like v6 connectivity at home but you don't actually know did you your ice cube I'm experimenting with it for your browser just as evidenced by the main results will be found this is likely a bigger problem to the power research shows because remember all the good news here is and public ipv4 internet 7 this community packages public ipv4 internet and get requests back amended their memory board devices who have private
they're everywhere this these computer devices are a large today position and most importantly this shows us that we need novel techniques for finding those active every six coasts on the other if we are to continue music research and that's previously the ipv6 hitless product which aggregates the results of some different ipv6 after the gathering product and they published a to be updated list of activities east coast so we compared our results to journalists and probably out of all the public oh we got only like 50 of them we read a list a list so we even though our dataset resulting media said run run through this wall they found a completely distinct set the very basic scientists do what's already
publicly available and you can imagine there are many many other distinct substitutes are so different
we definitely continue this work in some similar directions and the deaths of every
and
[Applause]





