BG - Abusing Webhooks for Command and Control - Dimitry Snezhkov
Show transcript [en]
and with that let's get started please welcome to meetry everybody hopefully you can feel me well so I've been introduced my name is Dimitri and I just want to say that my opinions are my own and do not reflect do not reflect the views or opinions of my employer or its products anyway so this talk is about web hooks but before we get to that that talk is really about a way to escape or provide bi-directional delivery of content thank you better yes better thank you hostile networks monitor network censor networks and the escape is to your external host under your control your can command and control servers or wherever the case may be the focus is on proxy more
specifically content proxy and that's what we're gonna talk about today so the audience is for the talk is going to be from the red team perspective but obviously ranting red teamers pentesters defense folks and privacy advocates are definitely welcome here so before we go into thank you Oh much better so the before we we go into the details would like to set some stage before the strategic goals the technical goals and the tactical goals of this talk and so we're gonna seek alternative means of effective outbound communication through contact proxies we're going to maximize adaptive retool and capability for exfiltration and we're gonna try to minimize our discoverability by elevating our OPSEC and last but not
least we're going to use the opportunities that we have inside the organization to do so the tactical goals we are going to try to do reverse connectivity to the environment we're gonna do a synchronous communication to your CNC and we're going to try to add voice avoid censorship with this technique the technical mechanism will employ webhooks concept and we're going to go over that we are going to do this in a synchronous manner and we're gonna showcase a tool that will automate that so to set the stage where we're going to talk roughly about the offense/defense red and blue the content proxy is the central piece of that talk command and control is your c2 we're going to
introduce the concept of c2 broker and we're going to have two players two agents one the client and the other is the server so the problem of communication from restricted networks it's it's really not a cat-and-mouse game it's more like a game of a red elephant and six blind blue men just like an old tale when six blind man would touch an elephant they would not know who that animal is but they would touch the trunk and it would say okay well that looks like a hose you know they would touch the body that would look like a wall and so on and so forth so essentially the red elephant is you the pen tester the red teamer somebody
who is on the inside and the blue man are the sensors are the mechanisms for defense and that's what we like to think of this specific situation so from the blue perspective you know the blue man need to identify what this unknown entity is really how blind is it what capabilities it has how can we better restrict the movement of this elephant right how to detect capabilities without revealing our own and basically is just a matter until the the unknown moves then we're going to have sensors it's going to be passive and is going to be good rate but from the red perspective the game changed too to the opposite what is this in one known
environment that I'm in how quickly can I quickly and safely can I learn what it is and how really blind are the sensors I'm not exactly sure this is my first time in the environment and my wish is that if I sit tight if I don't move then the sensors will go away and I'm gonna go on doing what I was doing but in reality the rat has to figure it out on on his own the elephant has to figure it out on his own and so the the challenge here is that the elephant has to move but unfortunately the first move may kill right you are if we're focusing on the proxy you need to bring your tools
in into the environment or do whatever you need to do here so touching proxy in unsafe manner in quiet environments or restricted environments is a challenge so the three outputs from your move as an elephant are the unsafe negative outcome we're going to talk about that the safe negative outcome and a safe positive outcome how does this play out so unsafe negative outcome right you're done your your your pretty much you know you can you're in the environment you're discovered you're burnt and you're done now the safe negative outcome from the red team perspective you can probe the environment and you can tell when it's hostile right you've got the idea sensors you've got some of the tunneling
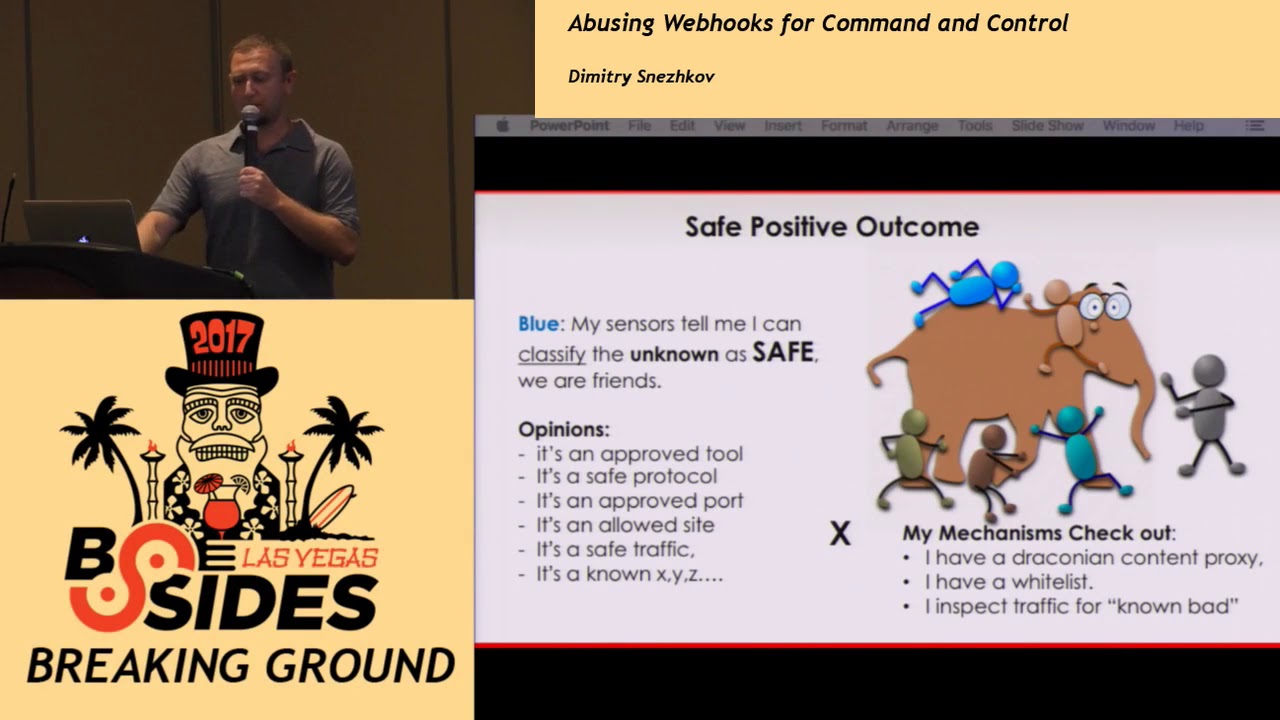
that is prohibited you've got tight content proxy and you've got no domain fronting or any kind of online drives that you can reach you're pretty much constrained but you're still alive you're still on the inside and you're trying to figure something out you just bind yourself some time so this safe positive outcome from this is going to be when we've convinced the blue that we are good right so the blue operates on some opinions I would say rate depending on what sensors they have but processes and procedures they put in place is that you know they may discover that you're just an approved tool or your safe protocol that that is allowed through the internet through the internet out oh
you're going to an allowed side you know your traffic is deemed safe on the other side the mechanisms are being trusted right the blue mechanisms have been entrusted there's a whitelist that the company may have and so you're golden that way or you've got in the environment where only known bad is true is is is is being watched for so that is a safe positive outcome when you have when you are able to blend in so but the last really if you think about that the last two outcomes the safe positive outcome and the safe negative suffer from from a few issues rate they are both built and assumptions of trust for sensors or trust for your own tools that
are available to you and the environment that you're in and so both the red and the blue can be paranoid about each other's capability that would sit tight not move they can be dismissive each other's capability I bought this really cool product it works it's going to be silver bullet for me so from the read as much as well as from the blue perspective you need to understand that the map that you've built with your probes is not the territory it's just the map so what you need to do is as a red elephant in this case is that in even in very restrictive situations you need to break static map of the world that the blue built for you or you have
built in this environment you need to meet blue at their map of the world you have to blend in into the traffic you have to blend in into business process and so on and so forth and you need to do pay a pace and you have to pace and lead them that's what we're going to talk about so how do you achieve this sort of pace and lead and and and and you know being safe really in the environment that you don't know it's it's a key into mimicry right where you resemble a specific animal or a plant or in this case protocol or some feature mechanism and you just blend in so for the red you
need to be an approved business need you you can be an approved traffic or protocol and you need to use good tools and valid rules depending on what their what the company is considering to be now the static map of the world that the blue has built is based on that white listing is based on this content proxy rules it's based on a known bet that they see so in any given company you would want to take this business processing you need to follow that now in this case we're going to look at the developer we're going to follow the developer through the organization we're going to code rat tools in the developer process and we're gonna hide in plain
sight of the developer process routine right so we're pacing to lead and the way we lead is that we say we're the developer huge us the developer so you should trust us but more importantly we're going to reach the strategic goal of meeting the defense at their map of the world it's all good and well right but we are in very hostile environment and we have the content tight content proxy there is nothing you can do about that in certain environments some things are being taken care of really well how do you work with this will diverge a little bit and talk about web hooks so web hooks is a new technology for asynchronous web
responses it is being used on the internet a lot it's been it's it's making its way to the enterprise just because developers are social animals they code open-source tools and they use it and they like it and so they obviously bring it back to the enterprise it has really good interesting capacity of for a collaborative and social coding updates it runs over HTTP which is great for us and it uses the HTTP protection mechanism or transmission mechanisms so to talk about web books let's let's step back a little bit and talk about how the server request works in HTTP world right we all know that we submit a request for processing to the web server then the
server starts executing it and we are asking the server every second less than that more than that but more or less we're gonna look for a response from the server by propping um you know asking the server for response and so the server has some issues with switches contacts right resources the server gets overloaded maybe maybe not but on a scale it might and so when the server is the result the client grabs it that's the old way of doing that the web hooks is is a little bit different concept it's really of the response subscription so the web server says okay well um stop asking I'm not gonna be able to respond to you why don't you give me a
URL the end point where I'm going to post my response once I'm done right it's a synchronous subscription the server executes request as as I did before but the client is is doing something else it's not it's not pulling the server and then when the server is ready the response is being posted that's a synchronous way of communicating back to the client through the web hooks how does implement it is very easy right it's a link that you provide to your client resource on the internet and it's a rest right it's a rest resource and the server says hey you know I'm gonna register you and when I'm done I'm going to post to your IP
address and a port and a resource the request that you have or response response to the request that you have so web hooks are being used everywhere now continuous integration code repository slack anything that has to do with monitoring of your network for events for for any kind of notifications and alerts so it's it's cool but we're still here right how does how is webhooks technology helping us in in the context that we've outlined before so let's talk about the c2 broker what if we can find a allowed site through the draconian policy and the content proxy that we can actually communicate with I mean any business has to do business online so there are some
sites there completely white listed and you can you can just go and browse them right we can turn that site into a broker using the web hooks so essentially we can drive the data and communication over that c2 broker to our external site through the web hooks so we're still keeping the big goal in mind of classifying ourselves as something known good to the business process that the defense has the we're going to go into details in this but this is the general architecture for our you know technique here we're doing a request to some c2 broker which is which is going to store our request and for the two to the c2 on the other side the C to
execute sit posted back into the website that you know the c2 c2 website and then we're gonna go and pull the result how that works we're gonna see in a minute but before that what constitutes a good c2 broker like you can pick any site on the internet because they have to support web hooks and they have to be allowed right they also have to be public they need to have decent setup or web hooks API they need to be allowed and look normal to what the company is doing and they obviously need to be allowed through the products again coming back to the webhooks we're following the developer thinking back to the environment in in and saying that
well I mean the developer uses exactly the same thing right the decides that we're talking about our Hiroko github slack any kind of notification sites they may be really good candidates for C to broker let's pick on github so github is is very popular it's pervasive in enterprises we use developers use it infrastructure folks use it anybody who is pulling any kind of code would probably be pulling it from github at the moment from our read perspective there are tons of advantages is developer friendly we can code against it it is extensively used allowed in enterprise and through the proxies and it has OPSEC features right github makes our life easier by encrypting our communication making it more secure but
the last point is very important because developers adopted so you you have great chance of github being used inside of the organization and not go anywhere so octa hook as a github c to broker toolkit that is going to use github to do all these transmissions right it's gonna try to broker github is we're turning github into a broker for our communication to our external entity we're gonna register activex hooks server through the web host as we talked before and we're gonna use octopus client to send request to the server through the github so first things first when you get to get help you have a very nice set of API right as we talked about
you need that for your communication the payload URL is what your client is going to be receiving this is the URL the format that is is gonna receive it in as a JSON and then you activate the hook right so once that's done you can subscribe to I want to say a dozen events or types of events off of github but you really care about you know issues and comments that's how octa hook is gonna drive the transmission of requests and receive the responses now the opposite part you know minimizing the exposure and blending into the environment is we're gonna write on github great way of securing our communication with you know H max and you know you've got certificate that
is being validated so your content proxy is not going to intercept that unless and and if and if it does and we'll know about that so great features for us now this is the sort of the guts of how these things work every agent on the inside your client is an agent and your server and the situ is an agent but the agent on the inside and the agent on the outside they both have identifiers it could be anything in this case it's probably like 8 to 10 character configuration string and then so those agents are posting issues on the github just like a developer right we're trying to blend in we're opening up an issue on
the repository that we're gonna we're gonna store our requests in and we're communicating the responses breath back from the C to over the state of the issue which is closed-open and also the comments for the data so you can see a developer going in from the defense perspective you see the developer going into github opening up a an issue type in something in and then they might have comments right very normal uses the git git application tokens so you can actually toggle through a through your configuration here now this is the example of what that what that really is is the github submission of of issues and comments now so we have a one-way directional
communication right can we make it better because we can still we need to still go and pull the github for our execution for our details what can we do well it turns out that github and github you can configure multiple web hooks up to 20 so guess what you can do by directional communications broadcast of your responses and requests to all the parties talking so that's a real-time shell through get through the github to both the client on the inside the agent right and the c2 so essentially you're doing real-time communication over github and that that's your shell through the proxy this is the example of how you would configure that all you have to do is just create a different
URL for your for your client and then you can start playing with roles you can have a server you can have a command client you can actually create a pretty elaborate you know configuration where you would say the client on the inside is going to post commands and the server is going to respond to that or you can flip it around right you can actually say if you have to do directional communication that the external host is going to be the requester and the internal host is going to be the executor of the request so thereby is your shell back so clients and and servers are configured and configuration file we're gonna see this now on to the demo so when we go through
this we're gonna see a synchronous unidirectional command execution the first example where the request goes through C to github and then gets executed on the c2 server we're gonna try to turn on the real-time communication mode to do the both both ways bi-directional we're going to look at execution of commands and put in the content because sometimes you need to bring the content content back into the environment
so servers and clients on both sides load from the from two configuration files right the server and the client they can have similar features but essentially this is declined you're sitting on the inside and what you're gonna do you're gonna execute a command and when you do that this command goes to this c2 over github you're executing LS command nothing happens right because now is the first case where you need to pull github for the answer so you check issues and when you check that you see that the c2 actually says I'm done here's the response I closed the issue right and then what I'm gonna do I'm gonna look at the issue and get the
response back right that's the first one that's all executed through the github the next part is we're gonna turn on bi-directional we're gonna start the thread that is gonna go both ways we're gonna do exactly the same thing with LS and we're gonna receive the command right away so we're achieving the bi-directional communication here there are some commands in this octave hook that is released today's just just for convenience but mostly is for putting content through c2 through the broker into github and so you can actually grab it an execution of the commands that's the file put right so when that happens you can be sure that well we're just simulating that we're touching the file
on the c2 right now we're gonna write something into the file on the c2 side and then we're gonna bring it back through the github to us so that that's the that's the execution of the the content on the other side and then we're putting it back right the get transfer we touched a little bit about on that but essentially this is the demo of how things are put together through github you've got the command and you've also got the the response if there is any and then while we're looking at this we can start thinking that well that's normal right developers no defense is going to look at this right now and say that it is it is something that is not
used so everything is locked so you can actually see centralized logs on your clients and your agent and the c2 if you want to but and you can actually expand this to create different commands it's a plug-in based architecture the configuration is you know time permitting we can go into this but essentially what that is is just a llamó file with a bunch of configuration stanzas to connect to the github and how to drive the execution also to assume the roles
alright so the client and the server configuration is very very similar because you can actually tackle the the rules here so right now it's cross platform for the most part except for the command execution because it uses POSIX so your c2 might need to be a POSIX machine it is extensible to come with command plugins it's one process with embedded web server and the command server so when the defense goes and sees that they just see a process a user process without anything else no Forks or anything like that but what we what we really want to think about what's gonna come next with the 20 Hook's for example this is github right you can
implement that across slack or anything not anything like this the concept still works the web hooks work exactly the same way as you go you just need to write different plugin but so we want to do swarming capability we want to probably do the follow the Sun for example if your C 2 gets burned you can actually send your request to different C 2 somewhere right or maybe even 2 or 3 internal agents somewhere we can Reese reassign the direction and we can reassign the rules who is the requester who is the responder and we can also send it to specific agent in the future right if you have multiple C twos we won't send it to this one or that one
so defense and mitigation web hooks are here to stay there is no way I mean it's it's too good for developers it's it's just very useful so if you're on defensive side make sure you restrict your laptops to go to specific size that the users need to not everybody in your organization needs to go to github or to slack that is a less sexy approach of course with group policies or whatnot but this is the way that is gonna serve saved from that perspective say save so the content proxy is not going to be in the way if this scenario is used because your github is allowed so make sure you're taking care of this on the
endpoint and then from our reading perspective we're gonna keep continue writing social coding and the more the more times developers give us the you know the way for you know to execute we're gonna take advantage of that this is the github repo if you want to fork work on it or just check it out please do if you have any questions let me know please thank you





