The Rise of Synthetic Passwords in Botnet & Attack Operations
Show original YouTube description
Show transcript [en]
Welcome to Passwords Con. Our next talk is entitled The Rise of Synthetic Passwords in Botnet and Attack Operations by Travis Moore. A quick thank to our sponsors, our diamond sponsors, Adobe and Aikido, the gold sponsors, Drop Zone AI and Profit. Reminder about cell phones. Please keep them on silent so that it doesn't disrupt anyone anyone around. There's no need to record or stream. Uh the talks are recorded and they are being streamed. Also, a reminder that uh the Bides Las Vegas photo policy prohibits taking photos of anybody without their prior consent, including speakers and their content. So, just please keep that in mind. Um obtain con consent before taking a picture of anybody, not just
here or in the audience, but the whole conference as well. Right. So, we're going to get started with the rise of synthetic passwords and botnet attack operations by welcoming Travis Moore to the platform. [applause] >> Can we take the picture? >> Yeah. >> Yeah. >> Yeah. I'm I'm I'm okay. >> All right. Uh good morning everybody. Um very very cool to be here. First time in uh Las Vegas. Can everybody hear me? >> Yeah. All good. Okay, cool. Um so yeah uh riser synthetic passwords in botnet and attack operations. Um so just a quick little who am I? uh I'm a security rearch researcher at Bitrack Cyber Security based in South Africa with all the lions and tigers
running on the loose and then uh yeah I'm focusing on uh credential abuse and detection evasion um also interested in password systems and attacker behavior. So um it was mentioned earlier that it's also passwords con isn't just about passwords. It's about you know kind of human behavior and I think I think that's a very important note to to remember. I also really enjoy hardware hacking and low-level exploration. So yeah that's just a little bit about me. Um but without further ado let's get to the talk. Okay so uh I just want to fix this thing. There we go. Okay. So the credential landscape has shifted. Um so as defenders continue to strengthen protections around password reuse and breach correlation
and behavior behavioral analytics attackers are shifting tactics. So one such evolution I is the increasing use of synthetic passwords. So these are algorithmically generated, neverbefore used credentials designed to overwhelm and evade. So they're not sourced from leaks or created through guessing strategies. Instead, they are crafted at scale using scripts or AI to mimic humanlike formats or generate high entropy randomness. So their purpose, sorry, I was meant to go to the next one. So their purpose is actually to flood login systems. So I mean the reality of you getting a uh getting into an account with a synthetic password is very low. But that's not their point. Their point is not to log in to the system. It's not
a brute force in a traditional sense. Instead, it's meant to flood the sock and obiscate credential stuffing attempts and poison the uh the visibility of security tools that rely on known patterns or breach history. So, let's just uh let's just take a step back. So, synthetic passwords are they've never they've never been used before. um and they evade detection. So the detection that I'm talking about in this sense is uh many bigger platforms they use breach correlation. I mentioned that earlier. So breach correlation is basically um if your password or the password you're trying to create or login with was previously found in a breach, they're not going to let you use that password again. they're using um you
know API calls and stuff like that from other kind of password um what's the word? Yeah, that that's it. Thank you. So password repositories, they're trying to look through that and trying to see okay like obviously if the password's in a leaked database they're not going to let you use it again. That's like the worst security practice. So that's just a little bit about what you know what what what we're trying to avoid here is we're trying we're trying to get rid of that uh alleviate that that kind of stress that we've got there as brute forcing and stuff like that goes. So terms of making a synthetic passwords it's actually really really easy. Uh
this is just a random Python script that I just uh whipped up with the good old uh chat GPT. And it's just obviously the the working part of it. But what you can do with this script is you can literally just put in um words and numbers. I believe it's numbers and digits. Yeah, digits. And it will just randomize it completely. So I think I did about 10 billion passwords with this. Uh I changed the how many it makes in total and not one single one was uh you know they were all unique basically not one was repeated. So it worked pretty well for that. Again it was just more of a proof of concept.
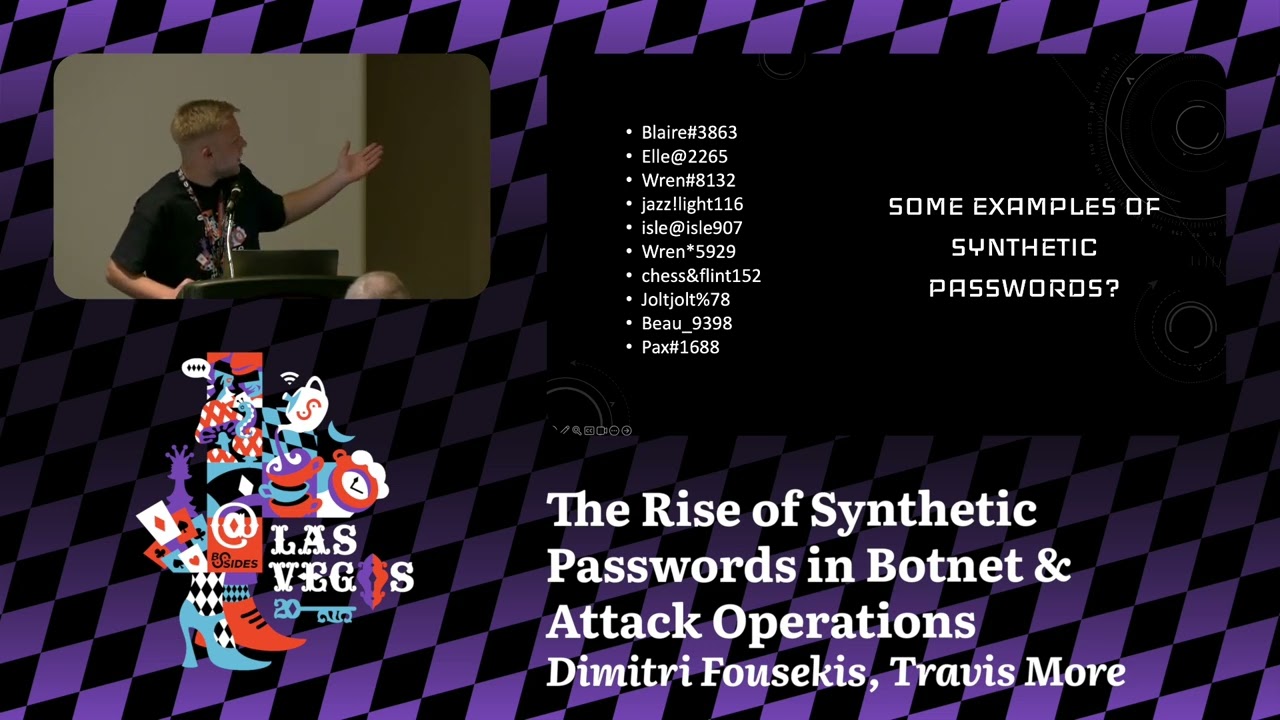
Um, I definitely think with with enough time and like actual effort put into to making this a real thing, I definitely could have made a better script than a whole lot of if state statements. But here's some examples of the synthetic passwords that that um that that script makes. So, I passed it in a whole lot of names and a whole lot of numbers and then it obviously does special characters. Uh but but it's so versatile. You can do whatever you want with the script really. Um you don't have to put names. You can put pets or uh literally drinks. Uh really it doesn't matter what you put in here, but they they look they look real enough,
which is which is kind of the problem here is they look real enough. The entropy level is pretty good. Um you know, nothing nothing out of the ordinary when we're looking at stuff like that. And again that no one's ever well [snorts] I say I think no one's ever typed these passwords into anything. At least they weren't in any of the breaches that we found. So they're pretty unique which is which is good. And they're not like you know password managers 25 character thinging that looks like I don't even know what it looks like. It looks like a bomb hit the alphabet. So that that's pretty interesting. They look real enough. Okay. So why why do we use them? So I just want
to change my notes here. So we use them because uh give me a second.
All right, I found where I was. Okay, so uh why should we use them or why why why are they being used? So defenders often assume that no match in have I been pawned should equals a low threat. So this assumption is now exploitable. We all know what assump what assume means. So if there's no match, there shouldn't be any attack. That's basically what they're saying. And I'm also on the wrong slide here. There we go. Okay. So just because it's not in the breached repositories doesn't mean that it's not um that it it's not a brute force trying to get in because what ends up happening is the socks drowned or your system operation s uh sensors drown in junk. I
mean it's like uh it's noise. So you're left analyzing high volumes of high entropy inputs that kind of go nowhere, you know, they're like uh rabbit holes. Then breach mashing, breach matching like have I been pawned and uh dehashed I believe it is and spy cloud. Um it just zero match means to them at least if if they're using those kind of repos means that it's clean and it means that it's perfectly okay to just you know let all the um the login attempts go through and then honeywords also break down. So, if all attempts are unique and high entropy, even Honey accounts become harder to trigger because it it looks like somebody maybe just typed the email
address in wrong and then they're using their real password because they look so they look so real. And then the behavioral signal kind of gets lost in translation as well. So, if every attempt comes from a different session or an RP, what do you focus on? Uh there's nothing concrete that you can focus on. You can't focus on the IP. You can't focus on the um the type of passwords they are because they synthetic but real looking. Um so it's it it's kind of like a a difficult one, you know. Um so I have this graph here. As you can see, I'm not very good at making graphs. Um because that's the strangest graph I've ever seen in my life.
So what I did was for this for this graph I have 10 million synthetic passwords and I have stolen passwords from stealer logs that were fairly recent and I compared them as my breach corpus. I compared them to the NAS API breach. Okay. And of this stolen passwords from the stealer logs 98.66% 66% were found in the NAS API stuff, which is kind of kind of a given. I thought it was a bit high though, but I suppose people aren't really changing their passwords. And then the synthetic generated passwords wasn't found in anything. So, I probably could have just put this into words, but I thought the graph looked kind of funny. So, I I hope you enjoy my
my lopsided graph. Um, so it's kind of the invisible attack surface, right? So synthetic passwords are no longer on the fringe. Botnets are using them. Attack scripts are generating them. They are cheap, scalable, and invisible to traditional controls. The attacker doesn't care if the password works. As I said before, in fact, many times they don't even want it to. The goal is to learn to mask and to distract and they're succeeding at these. So, detection must in evolve. Um, so to detect them, we stop relying solely on breach correlation, incorporate entropy scoring and login pattern anomalies. All pretty standard stuff. and session fingerprinting. And by standard stuff, I mean, we think it's standard, but some
people are just I don't know. I don't know. They're not they're not implementing them, which is strange. Um, credential attempts that fail too cleanly. So, we we could monitor things like credential attempts that follow fail too cleanly. And what I mean by that is, you know, if if as a as a human, if the password is wrong, we kind of try something maybe slightly different. We put put a little bit uh like I know for me when I before I used a password manager, if the password wasn't password, it was password one or password two. And that that's kind of how it went. But if they fail too cleanly and people are just like kind of
trying something completely different, you know, that that kind of could could mean that we're getting brute force basically. And then the seam logs with sudden surges in high format variance inputs. So what I mean is again that they they're varying all over the show whereas usually a normal person, a user, a human uh would would try something not not all over the show. It would be like closer to the actual word that you're trying to that you're trying to guess or whatever if you forgot your password. Um and then I have a final call to action here which is just shift the detection from uh ident from identity to int intentbased. So what what is the user's intent with
trying to log in? Um and I think that that could definitely be something that we can push forward with AI. Um, I know AI is not perfect, but we could definitely train train some sort of model just to figure out the intent rather than the identity. And then we could also flag sessions with non-human patterns, kind of like a recapture. But um yeah, you know, all of the stuff, all of the stuff that I've mentioned honestly seems pretty straightforward and pretty normal to everybody in this room, but a lot of the companies and uh login pages and stuff, they're kind of just using one method. It's like a one one method fits all type of thing. So, this is more
just to raise awareness um and just trying to trying to get the word out there. But I think I spoke too fast. So questions. >> Yeah, >> sorry. I want to back up a little bit. So we've observed this phenomenon where high volumes of synthetic passwords are being submitted as >> Yes. Yes. >> from botn nets or for the purposes of creating accounts for botnet activity. >> Yes. Yes. So this is this is brute forcing current accounts. So that that's kind of where we saw the you know the sock and the seams kind of get overloaded with these passwords that looked like the whole world was trying to log in. >> Okay. >> Human human activity and that's that's
kind of where we started. >> So they're generating passwords that they think a human might use. >> Yes. Okay. So the ultimate goal here is to brute force their way into So the ultimate goal here is to brute force their way into existing accounts by trying to generate passwords that would look like what a human would. Yes. But the sock might not notice because they look so much like generating. Okay, I'm following now. Okay. >> Exactly. If you weren't following, I'm sorry. [laughter] >> Yeah, I thought you were saying they were just trying to flood >> I thought what you were saying was that they were just trying to flood the zone with with basically useless data in
order to mask actual credential stuffing. >> Yeah. So, it's it's basically a a um a mix of those two. It's credential stuffing and kind of just you know basically dossing the login site with >> so in a way it is brute forcing. Okay. Yeah. I do have another question. You said you generated 10 million or 10 billion. Yes. >> Uh using your your uh your chat GPT python script and yet none of those showed up in any breach logs. >> Isn't that kind of statistically impossible? I mean there's only so many variations you can get upon like eight or 10 characters. So surprisingly um I can I'll I'll show you the after the talk I'll show you the the stuff but
surprisingly I got nothing >> really >> and I was also like that's a bit strange cuz now my graph's kind of going to look lobsided and I was like these people are going to think that I don't know how to use PowerPoint or >> whatever clearly not working right they're clearly not guessing things. >> Yes. Yes. Yes. So yeah, but I I'll I could definitely show you. >> I believe I trust you. >> No worries. No worries. >> Any more questions?
>> You're Travis. >> Yes. Yes. >> This will be our last one. Thanks. What's your opinion on really like have I been pawned in those larger pod stores? How much value do they have really? Because the control is rate limiting people from attacking with scripts like this, right? And having policies around that because now we're telling in the defense of the end user, hey, all these words in in the alpha in the dictionary are can no longer be used because they were once used in a compromise. But they're not there. Some most of the time those are tied to specific accounts. So you only have one half of the equation from your for your attacking. So literally we're just
basically creating large dictionary attacks that we're saying you can't use all the words in the alphabet words in the dictionary user. >> Yeah. Yeah. No 100%. So it's kind of like we're making a big rainbow table if you want to call it. And I think that is that is something um you know we we need to I think communication when it comes to trying to tell people oh this password this password sucks this password's good you know that that type of thing we need to try and convey the message a little bit clearer like you said it's only half one of the equation so um have I been ped and all of that stuff uh I think it's
good uh I don't think I think you should take it with a grain of salt personally Um I don't think it's like oh my password's here you know. Um but I think that's why they brought out that uh what do you call it the the email address part of things as well like you put your email address and then you put the password kind of like a login like they're just taking your login for your email address but you know it kind of gives you that that two-sided picture. So I don't know does that answer your question? Is that is that okay? Yeah, you're like it's helpful, but it's not. >> Yeah. Yeah. No, 100% 100%.
>> You can leave it there. >> Okay. Okay. Cool. >> Thanks everyone. That was uh that was also Travis's first talk at a conference this size. So, thanks very much for listening. If you had any questions for him, uh he's available afterwards as well. The next talk will be at uh 2 p.m. Extending password insecurity to the browser. How malicious extensions are used to steal user password. So we've been talking about steelers in the previous talk. So we're going to also break that open a bit more now as well. So that's 2 pm from here. We look forward to everyone attending that as well. Thank you. Have a good break.