PG - Making Your Website Vulnerable for Fun and Security Awareness - Kenny Jansson
Show transcript [en]
all right good morning everybody welcome to besides Las Vegas the proving ground this talk is making your website vulnerable for fun and security awareness given by Kenny Janssen a few announcements before we get begin we'd like to thank our sponsors especially our inner circle sponsors critical stack and volley mail and our stellar sponsors Amazon blackberry and silence it's their support along with other sponsors donors and volunteer that make this event great impossible just another friendly reminder these talks are being streamed live except in the underground and as a courtesy to our speakers in our audience we ask that you check and make sure your cell phones are set to silent if you have a question at the end of the talk
flagged me down I'll be roving with this microphone we just wanna make sure that we get your questions on the audio for the live stream as well and with no further ado turn it over to Kenny okay good morning so in October 2018 a number of foreign developers in Stuart brown in Norway will challenge to hack a clone of our own websites so we did this to increase the offensive security awareness of our developers and have them better understand our digital services from our threats point of view because we are to stop a security background it could be challenging for developers to understand the real impact of an ability let's take exercise vulnerabilities as an example many pen testers and
automated tools argue that accessible abilities are really dangerous in the report but they rather have the time or ability or budgets we create a proof of concept of anything but an alert box but when the developers read this report they may not be as convinced that exercise is something to worry about since the web application have security hazards and security flags on the cookies many developers often believe that the user session is indeed well protected and the negative business impact during an attack is low especially on reflected access when there is a prerequisite that I user must click on a link but most cyber security aware people know that users do click links and most web app hackers know that
securing the cookie does not fully protect the user session however many developers I worked with assume that securing the cookies will fully protect to user session only when giving those developers insight of the same origin policy etc from an offensive perspective the real consequence of XSS becomes clearer to give developers vulnerability insight from an offensive perspective we could use vulnerable applications such as be web web goat and vulnerable cetera in Cirebon we are conducted regular CTF events to increase our developers offensive security awareness we have used online CTF services for this purpose although these are great in showing how to technically exploit a vulnerability they are less great in showing what a certain vulnerability means to the company's business and the
digital service of supporting this business so we thought that security guys that if we identify where a future vulnerability could typically reside on our own web page introduce that vulnerability in a clone of our website and then challenge our developers to attack the clone website this might give some insight what the vulnerability could mean to our business and reduce the risk that it is unintentionally introduced on a real website so we went ahead doing this as part of our security awareness month we started by identifying new and business critical mechanisms on our website and one such mechanism was our chat BOTS in Cirebon the shelter provides our means for communication for customers they can ask
questions and quickly get answers or direction the security team was aware of future planning of improving the shopbot with authenticated access to customer data we immediately thought of the risk if this is done in an insecure way and what role an XSS vulnerability could play in such a scenario exercise attacks have become among the most common attack methods on web applications these days and with an increase in automation and robotics it is extra important as such human simulated mechanisms are protected so sure to show our developers how dangerous these XSS vulnerability this can actually be in context of store brands business we went ahead and created such a challenge in our new CTF which was a front-end clone
of our website linked to a burnable back-end so this is our website and this is the clone our website clone see the difference the there is no difference and that's the point here so do the cloning we use TTT track to close to clone the front-end into our docker container we created server responses in available PHP we back-end and then link those responses to the front-end then for showcasing the challenges we we used C T FD in city of D we had challenges ranging from excessive Mobilicity's to brute force etc but the main challenge involved exploiting our support which we made vulnerable to exercise this was actually a browser that frequently looked at anything that was typed in the
chat window so if one submitted our JavaScript into the chat window then that script would run in the context of the chat bot which had access to sensitive information through an API the cookies used by the chat pod was protected by HTTP only and secure Flags thus to successfully complete this challenge one would have to trick the chat bot and submit our XML HTTP request to make the shotput stored in sensitive information into a variable and then send this to a listener controlled by the attacker five participants managed to complete the Shepard challenge and afterwards we got some feedback that the sharper challenge was a great way of showing session hijacking however we also received feedback that the clone
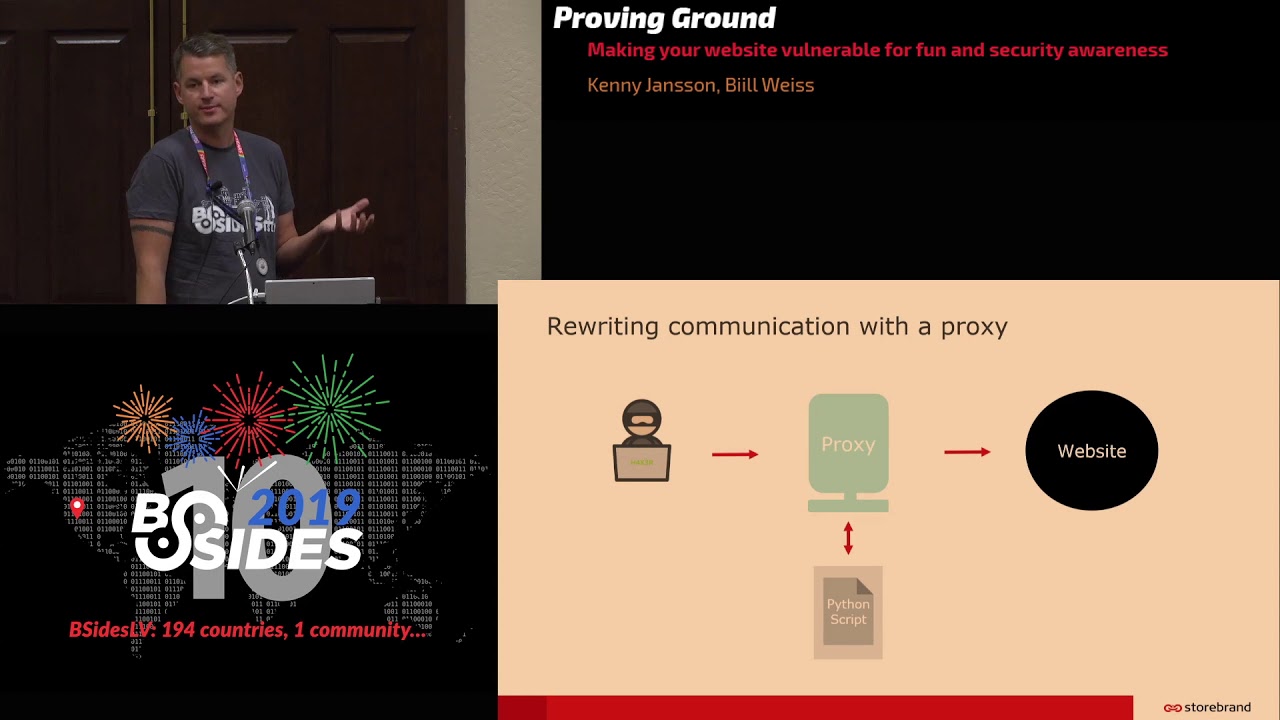
contain many false positives and that links another thought was that our CTF on a real web application instead of a clone could prove more valuable so the question is could a CTF on a real web application be possible without altering the web application and production test environment what if I told you yes you can achieve a simulation of vulnerabilities on your website without going through the hassle of cloning our website or altering the real web we can achieve the concept of a burnable website by using a proxy that loads a pre-written script or filter that contains rules for altering the responses to requests so to use this in a CDF the competitors would simply surf
the web site through your proxy on my github repo you might find our script called one filter the script contains example of vulnerability security introduced and how to do this I know of two ways to connect through the filter either through our normal proxy or with our reverse proxy so here is a brief overview of the script is using a text editor but let's dive into some more specific details and demos that uses this script and setup so this example here shows how to rewrite our shop or JavaScript with MIT and proxy what we do is using midden proxy script function with a Python script to rewrite the request since the JavaScript dictates how the browser will behave everything
typed to the shopbot would now go to a vulnerable back-end in a city of this server would of course not be on localhost but on a remote IP reachable by the participants alternative ways to reroute traffic is to simply create a redirect response including all the parameters or you can do it this way here we take the parameter SQL and we route it internally to our vulnerable SQL /p PHP back-end on port 800 and Rubright the response with the response from our SQL back-end this example show how to insert a path traverse your vulnerability in the file parameter of the URL if you copy some files and folders into a web server directory for example here port 900 then
those files would reflect when someone requests them in the file parameter including at least four dots lashes the example here shows the et Cie password being reflected if it's not clear it's using minion proxy this way can be done on a any website this example here shows how to insert our afflicted XSS in the Q parameter on bing if we search for my search string on bing not calm and look in the source we would find this highlight this string here this is what we could match and replace in order to insert the XSS note this particular reflection is within a city data tag so to get XSS to work we need to close the sea data tag so let me
demonstrate here and just be clear we are not finding real vulnerabilities on being here we are only rewriting the response locally however to be on the safe side only our templates type of research on websites that do have a bug bounty program so what what are we seeing here is that browser that this not set up to go through a proxy and there will be no vulnerability here now when we instead load this in the browser that is set up to go through our proxy and we run the same XSS we pop an alert box we used gave a whole talk about how popping in alert box doesn't get a point across so let me demonstrate something
that could give some more insights about exercise something so Bing has a history page that stores information about the use of search history so what if this could be stolen might by an attacker through the implemented XSS that was shown on the search page on bing.com so here we have an attackers email client the attack list prepares to send an email to the Cookie Monster claiming that he has been fished energy seems to click the link on the Alpha ping the attacker has a logger that locks requests the attacker sends the email and now the Cookie Monster uses his browser to check his email he has received the email here emergency clicks on the link which takes him to
the Bing web page with some strange data of course here we have it of course it could have been any Content displayed here and when they do attack your now get into his logger you will see that he has gotten some data here and if he searches for flag he finds the flag so this is basically the Cookie Monster's search history in rendered in in Brennan form here and this is what was sent to the attackers logger so how did we do this we want to steal the search history of the user second we want to send this to a listener so our XSS payload becomes this yellow script code shown shown up here which achieves use that it
basically stores the content of the search history into a variable called data and then post this to our logger posting content to our two other sites usually works it is usually only the content to show on the website that is restricted by security headers same origin policy etc so this was a full link which would put inside a link that says click here of course we could upload this from an external source making the URL smaller however we would have done been subjected to browser protection mechanisms such as same origin course etc a third alternative is to use a third website with a shorter URL that basically contains this link in our redirect so let's do one more demo
and this time what if besides Las Vegas of org had an XSS on their webpage how can an attacker Explorer have exploited this in the wild and how could this be demonstrated in terms of a CTF so let's imagine the following scenario the Cookie Monster wants to go to veces Las Vegas but he is too late kori see the Cookie Monster receives an email that lets him know that he is not too late after all and the tea can still donate and receive tickets if he does it through this special offer so he clicks the link and the following unfolds so the Cookie Monster is taking the visas Las Vegas lorg he shows two donor
and he fills out his credit card details and the name
on his payment is being processed
payments successful so now the attacker has gotten the credit credit card details of the Cookie Monster which we also could call a flag in the same logger that is in the previous proof of concept so the attacker exploited an XSS in the event ID parameter on besides Las Vegas of org this parameter does not exist but was created with our Platinum scripts injected into midden proxy the URL in the email basically contain a JavaScript that all rights the iframe elements and displayed another donor page that steals the users credentials so to use this scenario in a CDF the participant could be hinted to send an email containing a link that exploits an XSS and overrides visas Las Vegas dot
orgs iframe with the participants own page behind the scenes the inbox is monitored by the CDF host that clicks on any link and submits the critical number or flag into all form fields this could also be automated if many participants of course so I hope you get my point how such an scenario is different from popping an alert box the developer of this particular site should now have a better understanding of the real implication of exists on these specific websites through hacking his own website so consequently one advantage of making your own website vulnerable through your proxy or clone or filter I run it in a CTF event is that you can increase awareness amongst the developers of the
Willing business impact of a vulnerability and another advantage is that you could increase awareness of how your web applications defense mechanisms and the browser protects the users when surfing your website it is rather easy to modify their headers with a proxy and it is easy to set up our CTF tailor to your environment your business and your top of data instead of running the CTF in a generic web app where the goal is to exploit vulnerabilities with little business context finally while the participants are busy looking for the flags in a production or test environment they may actually come across weaknesses with no Flags a point associated like the student here we were tasked to color the dinies finish and
finish flag but through a goal flag instead of the flag for the country finland the student did not call it the right flag but don't you think he should get some point for the creativity likewise a participant in a CTF that runs in a real environment may not find a real vulnerability and if one does make sure to assign some extra point because actually you did get a few epen tests well that's it here are my contact details should you wish to reach out do you have any questions
[Applause]





