Keynote: Fragilience - The quantum state of survivable resilience in a world of fragile indifference
Show transcript [en]
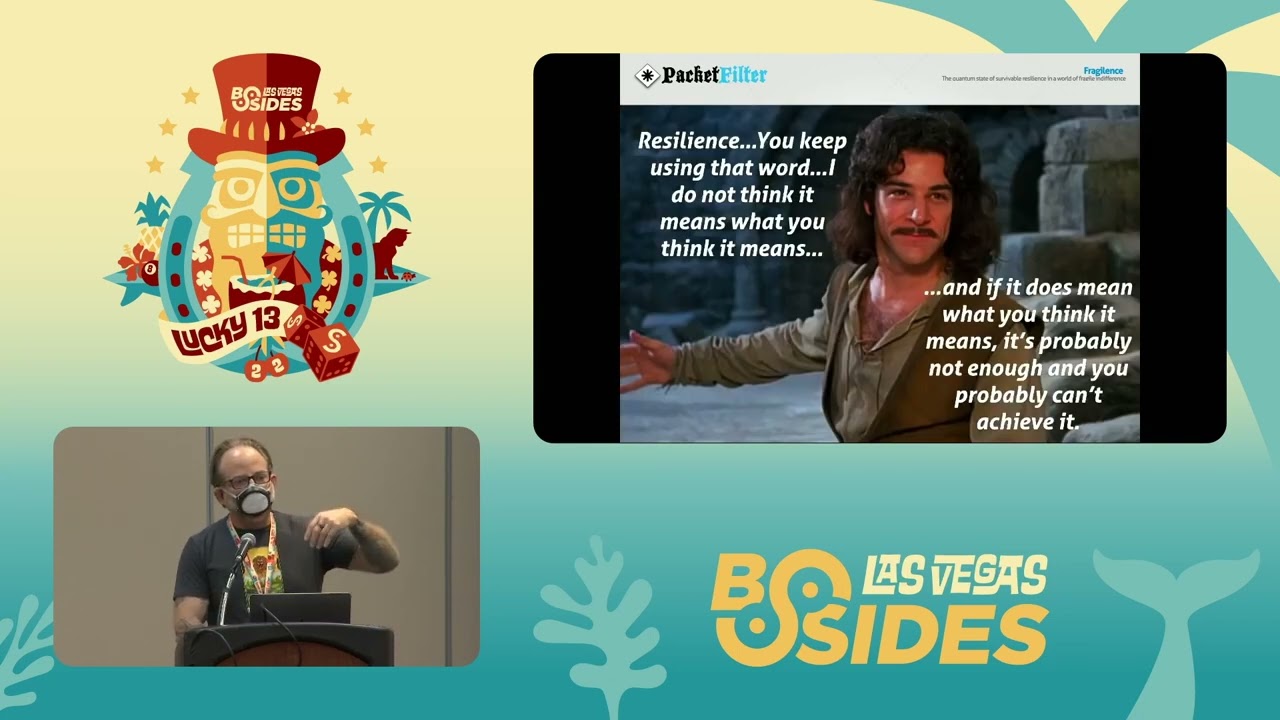
our first speaker to kick us off in this first return to in person besides las vegas is someone you probably know way better than me uh he's someone many of you have probably had announced the changes of your careers in your lives ladies and gentlemen please welcome chris hoff or beaker to the stage good morning i thought i got out of this with the speaker not working but unfortunately it is can you guys hear me okay with this bane mask on yeah all right fabulous let's see let's see if this can get this to work all right cool so uh they asked me for an abstract for this talk which is what the line underneath the fraudulence is i took a word cloud of words out of words out of my presentation and threw it at them so it actually means nothing the title fraudulence is a mashup of two words fragile and resistant and resilience and there are a couple of takeaways that i'd like to establish out front about what this talk is about and why i'm here and what i want you to take away from it the first is i have not been able to publicly speak in seven years that's what happens when you get subsumed by a risk-averse financial institution so uh not only is it b-sides back but uh i'm very thankful and grateful that i get to uh come up and and talk to folks and have ultimately a set of discussions after this um the second thing is i um there's a bunch of points in this talk that i think will come hopefully into into uh cognition as we as we run through it but it's about five different talks crammed into one so i'm making up for for for uh for miss time when i think about infosec there's a lot more art and compliance than there is science today uh when we do make use of science and when i and i use that term broadly it's often very siloed we aren't very organized in terms of how we take advantage of science we don't define model or manage risk well at all uh we are not agile and our definition of resilience varies and it is insufficient this word resilience is sort of critical to this conversation uh instead of resilient and you some of you may moan or groan when you hear this term but we ought to be anti-fragile and anti-fragile is an interesting topic that i'm going to get into in this talk because it talks about both the past the present and the future of where information security is headed and hopefully the thought process is here they don't pretend i don't pretend to be right what i do hope is that we start a set of conversations to get people to recognize that things aren't quite as bad as people make them out to be number one and we have an awful lot more at our disposal than most people actually recognize so with that this is not one of those grumpy oh my god infosec has broken talks um although i it sounded like it from the introduction but what it is is a discussion about words so there's a bunch of words that get used interchangeably these days secure or security resilience uh robust survivable recoverable defensible certain sustainable resilient has become or resilience has become the new buzzword of our industry a lot of it is because of the types of attacks and the outcomes that have happened so when you look at things like supply chain attacks nation states when you look at what we're seeing with with ransomware no longer is it about being secure it's about being resilient and the definition of resilient is is interesting um if you look at what nist defines the um the government agency ultimately that that defines a lot of things for us and standards that we use these words are important the ability to anticipate withstand recover from and adapt to bad things from happening the stuff on the left which will be hard to read but i'll give you all these slides later it just talks about the context so you talk about network security nation st are you talking about um critical infrastructure applications people etc the table on the right which ultimately came from accenture was about goals and outcomes from from the perspective of performance characteristics of what happens if you do resilience well so if you look at that chart you'll see oh if you are more resilient you will stop more attacks you will find breaches faster you will fix breaches faster and you will reduce breach impact but the the challenge with what is meant by resilience came to a head for me about well not me in this fictional guy we'll call chris uh in in let's say a financial institution about five years ago showed up uh chris did uh to this uh regulator meeting where they were talking about a horizontal across these gcps which is globally significant financial institutions systemic financial institutions there are eight of them in the united states by the way they're not publicly named but you can probably guess who they are and the question that they ran through this in terms of scenario modeling was uh listen we understand what you do from a security program perspective we understand all the controls you have etc we want you to assume that all of your controls have failed and you are a smoldering pile of rubble and you have to rebuild and recover and restore and they looked at me and they said what do you do and i said besides the normal sort of cliche you know update my resume and crack open that bottle of bourbon was i don't do a lot i'm an infosec besides securing the environment in which the owners of applications and services would restore like i don't do much and they said well who does and i said the application service owners in i.t and they turned and i watched this imaginary turret turn towards them and they said okay so out of all the app and critical service owners purportedly in this bank which you know who's the most important and they all raise their hands and they said okay we're gonna pick one payments okay payments who's the owner me this guy says he goes which one of the sub-component services do you get back up and running and of course there's like 200 of them and he couldn't really answer the question that kicked off a set of the portaly uh these things called mras matters requiring attention across all these banks that talked about you're doing resilience wrong which means you need to be able to recover rebuild within these service level agreements to make sure there aren't impacts to the public at the same time in the frb that was the us base the bank of england was talking about no no resilience means you should never go down in the first place so if you if you look at what we talked about right anticipate with staying recover from and adapt to adverse conditions the definition by itself even with regulators today that drives a lot of what people do in terms of their security programs is out of date and the challenge is that if we don't understand that word and it's supposed to be the next evolution of security how do we even know what we're aiming for so a couple years ago uh whether you're a fan of him or not um nicholas taleb came out with a book uh titled the black swan and black swan events are events that in the middle of things in the fog of war that you could not anticipate ever happening but in hindsight you're like oh yeah of course we could have seen that we could have prevented that great examples the reason we're wearing masks pandemic 911 uh for example the interesting thing is in hindsight planes crashed into buildings like the empire state buildings like the empire state building we've seen methods but the motive and opportunity and outcomes are very different so in hindsight you look at a black swan event it's something you can't really predict and ultimately the outcome is much more is largely greater than instead of being proportional with with with the event itself and so hindsight is a very interesting uh uh part of that conversation because at he he uh talab went on to write a book called anti-fragile and what he stated in that book was the the primary uh uh thing uh a part of of what is the definition of anti-fragility which is that some things benefit from shocks they get better they don't just recover human bones are a great example you break a bone your bones actually calcify and become stronger than they were in the in the first place so anti-fragility which is a huge part of the conversation we're going to have is about getting better in the face of stressors not just remaining the same and that you can visualize that by looking at this graph uh ultimately if gain and benefit is the y-axis and and stress and change is the x-axis normally what you'll see when people use the word fragile is it's a concave response to stress you break and you don't get better if you look at ultimately resistance or robustness which is a natural response you resist you get you get a little bit better for time but then you go back to being how you were ultimately if you look at resilient you recover for and and you get better for a while or you improve for a while but then you ultimately go back doing what you want the key here is that anti-fragile fragility is convex in response you get better consistently right you actually not only just learn but you become stronger from the stressor so if you look at how anti-fragility uh is more interestingly defined on the right you have this notion of disorder volatility and randomness and your responses to them so on the side of being agile and anti-fragile you ultimately uh embrace change and you gain or benefit from it you you ultimately get better you absorb shock and get better in the face of stressors trigger word security is ultimately all the way to the left in the most part which is we try to get to at least a base level that we feel comfortable with we don't like change uh ultimately we don't adapt very well we resist change if you think about controls and you basically stay the same not that we don't learn and ultimately incrementally get better but we don't fundamentally change the system itself does not get stronger so with that the the notion here is if you start thinking about what that means to our practice and our industry um you could you could uh posit that that infosec is actually fragile but without sounding like that's a terrible negative thing there's a lot of opportunity there and in fact those opportunities have come from decades of work that have been done in the past so there was a paper written in 1999 that was titled information survivability and it basically talked about how the world was changing uh and on the left you can see for example systems are centrally networked and under organizational controls they will transition to systems that are globally networked with distributed control right the internet and without barfing things like web3 you can go down this list and really understand that at the bottom of it it talked about that today security is seen as an overhead or an expense versus survivability as an investment and essential to the organization and that technology it-based solutions have to become enterprise-wide and risk-based now we look at that today and we go well that makes a total bunch of sense in 1999 that was sort of heresy but the people that wrote this thought about what it meant in the evolution from both secure to survivable to anti-fragile and one of the challenges that when i looked at why we don't or can't or have a difficult time getting better it's we seem to conflate these tactical information frameworks sort of the what with this set of guidelines and playbooks that are linear in action chains the how with decision systems for complex system problems that actually tell us about the why when and who now that may not make a lot of sense in one slide but let me let me let me clarify that today if you look at this this sort of um spectrum of of sensors sense making decision systems and levers and actuators we have an enormous amount of sensors help take whatever you want in terms of instrumentation or observability and define it that way in a shotgun across the stack we have many different sense making capabilities lots of consoles lots of ways of single panes of glass that ultimately allow you to visualize what you're seeing we tend to skip decision systems that allow us to make decisions on risk and instead head straight towards with the application of some level of automation these levers and actuators right and you'll note the words on the top you'll see them again later probe and sense categorize and analyze weigh and decide and act and respond now i'll say having run large-scale security operations teams being able to have the time and luxury to make decisions in the fog of war is a very difficult thing but a lot of that has to do with the velocity the volume and the quality of the data we capture in the first place and we're going to get into that in a little bit because we're going to focus on the fact that the reason i posit that we are largely fragile and not anti-fragile is that we don't take time to invest in decision systems to actually make risk-based decisions in fact just the opposite this is just a small sampling from a company name a reseller called optiv and these are the products that they sell there are literally thousands upon thousands of sensors sense making and levers and actuators you can buy today and each of them claim to be open and integrated etc etc but the reality is none of them really feed into a methodology that lets you make a decision so with that being the case uh just an illustration i went through and i sort of did a quick inventory of a lot of different inventory of systems from it asset management to graph base uh functionality in clouds to vulnerability management platforms you name it there's tons and tons of different ways we can think about visualizing the data we get from sensors we have the uh a linear sort of view in lockheed martin's cyber kill chain that says that well this is the methodology by which every adversary uh basically enacts his his or her craft and it's always linear when we in fact we know it's not in many cases it's iterative we have great tools like mitre attack which allows us to talk about the and categorize the knowledge base of adversary tactics which lets us think about how adversaries may indeed be looking at exploiting us we have cool things like detect and attack flow and i think gabe bassett's giving a talk on attack flow later which allows you to visualize and map your defenses against attack to know how well sorted you are against a particular adversary and then actually even visualize it uh so go go look at gabe's uh go attend gabe's talk on on attack flow later interestingly we have the new cyber security framework which again says you should identify protect attack respond and recover and it's always linear but it's not in fact you go back and forth a lot of times we have sunil u's cyber defense matrix which takes the uh inventory of nist from the perspective of those categories and maps them across domains and lets you visualize where you have clusters of technology and or human-based responses to these particular sets of of threats and allows you to understand where you're weak you will notice that in most cases if you were to map this in your environment you would be you would have very few things in the respond and recover or at least in the recover category because it's mostly people focused um we have great things in in the in the vein of threat modeling we've got structured processes to do this we have pick your pick your favorite model stride dread pasta you name it so we have all the capability to essentially be able to document how systems ought to work we have debiakio's pyramid of pain and the effects and outcomes in terms of how we could degrade deny destroy or otherwise disrupt adversaries based on the availability or unavailability of certain iocs we even have amazing uh var model based frameworks for doing quantitative based risk management and risk assessment what that really means is you're able to get to and express dollars of risk based on the probability and frequency and magnitude of loss and actually attribute dollar amounts to what a particular event could bring you so i just shotgunned you and fire hosed you with an enormous amount of stuff we have and you would say well if that's the case then why can't we make good decisions quickly and a lot of that would be answered by these four guys so dave snowden not related to edward snowden james rasmussen nicholas talab and simon wardley incredibly smart people i only share two um two things with them which is a receding highlight uh hairline and graying of the beard but i am fans of the work and we're going to cover some of these in a second in a very rapid-fire way because i want you to think about tools and whether you're even thinking about using these tools so simon wardley built this process and he open sourced it called worldly maps and it's a way of mapping strategy a lot of people use it for business but you can literally use it to map anything and it basically uses a bunch of doctrines and rules to allow you to understand based on a user's a customer or user's needs chain a set of needs and dependencies and components what that allows you to do is make really interesting decisions um in a relatively short period of time now there's a statement that says all maps are wrong and some are useful and this is a true statement because it is a very uh we'll call it personal um uh uh thing a map now maps are good if you know where you are if you don't know where you are it's very hard to know even if you know where you're going how you're going to get there right so that's where mapping comes into play this particular map was open sourced and published on the web it was a team that was looking at the executive management as a decision maker or customer with drivers like regulatory compliance they need to prevent breaches detect reaches and manage breaches and they took those components over a level over an x-axis of maturity of the component and and that chain if you follow like regulatory compliance depends on having automated control monitoring but that particular component from genesis to custom to product to commodity means that some of that stuff as they grouped it here would have to be delivered in-house because it is not available to be able to you know just buy you have to build other stuff in their view was more commoditized it became more product oriented so you see things like vulnerability scanning or attack monitoring so mapping like this gives you a view if you take like sunil's cyber security defense matrix and you say i have all these capabilities and tools not all of them i'm able to harness not all of them able to harness myself how can i map those and make use of them in my environment to make better decisions mr snowden is famous for something called the conoven framework and it's a welsh word which is why it sounds nothing like what it's spelled like just like comrie and basically what he says is it's a decision fabric that is based on four different domains simple complicated complex and chaotic and in simple what you ultimately have is a bunch of known knowns and so you apply best practices you sense you categorize you respond complicated you sense analyze and respond because there's a bunch of known unknowns things that you know that you don't know complex is a bunch of unknown unknowns like you just absolutely don't understand the space but you're able to sort of probe sense and then respond and then chaotic is where you ultimately are unknowable unknowns really think about that black swan events i was talking about and you act sense and respond the interesting thing about that is it's a maturity of where you are in the space that you're analyzing if you apply this to infosec we tend to have a binary view here of looking at things as either being simple or complex where i would argue that the majority of things are more complicated i'm sorry sim





