The Way From App To Brain: Attack Surfaces Of Smart Medical Infrastructure - Denis Makrushin
Show transcript [en]
okay before I start the presentation and I just want to ask you to do something without no exclusions all guys in the room please stand up like Eminem Sade please stand up I just have three questions for you pre-sentence and if you agree with me take your seat first sentence if you think that cancer or catastrophe skews more people than doctors mistake take your seat two persons three four five holiday you're busy okay second sentence if you think that cyberattack can kill a man with the implant take your seat okay if you think this is the third sentence it's okay if you're stayin it's okay it's okay feel free it's still your opinion if you think
then your electronic medical record is in safe place right now take your seat only one skeptic to skeptics me too thank you for your answers my name is Dennis my crucial and I try to break your skepticism and I try to show you how our smart medicine smart implants become stupid and thank you for this opportunity to besides organizers besides Munich and I want to start from this sad statistic almost 300,000 people die annually in the United States only there's a terrible numbers in main reason of that is the doctors mistakes the third reason of this and United States only in this numbers always increasing I think this will be not an exception and the let low qualification of doctor
is not the main reason the main reason is around diagnostic procedures the second reason is the run to repeat occur and tactical procedures and only the third reason is low qualification objectives and what happens because our releasing becomes connected and a few years ago we have already predicted that hospitals clinics medical organizations from acidic organizations will be a tidbit for attacker and you see that statistics already proven in this year and last year is not an exception we have seen a lot of newspapers when that when they try to penetrate into the medical networks when they tried to exfiltrate a musical data when they try to and creep medical data and waiting for the ransom etc etc a lot of
newspapers are related to the medical topic and it happens because the medicine comes connected what I mean the connected medicine huge machines like MRI CT scans your curves they are connected to the classic to say P IP networks or easier so old-school machines they are connected to the computers using the proprietary protocols and the computers this computer is connected to the dissipation editor and sometimes in medical clinics they have the PAC's servers picture achieving or picture championing communication making protocols or servers it's something like an ass in your flat but nass for the medical purposes is just for decom storage the combination and using the tech comm practicals this machines digits use machines connects the back servers and if you try to look
for this machines in the shoulder you will see there they're sometimes connected to the internet you just need to open the census shot and zoom by wherever else google and you will see that some decom servers connected to the internet exposed to the internet it means sometimes if it's not hani puts it me that this machine's available for everyone and everyone could try to connect without any identification or authorization procedures and try to steal the dye combination with the image of the patients the personal data of the patients and it's that statistics that almost 1000 DICOM servers connected and exposed to the Internet and it's not it's a bit for attacker I think if your
attacker you can just open the SMB port just open the show down try to search something like SMB ports plasmatic plus clinic or something like that the key words and you will see that a lot of them for interesting information for targeted attack is exposed to the instrument for example this is a topology of medical nervous very difficult or ghen ization that was expel traded from the Chardon you can bring your laptop to this medical facility you can connect to this facility using the Wi-Fi and you see that what is the most interesting computers interesting pcs and endpoints for you and this is an example screenshot from the penetration tester penetration so here the assessment of medical organization well
you can easily identify what is a computer is this interesting for you if you are an attacker then you can easily identify what kind of servers there and there are a lot of servers not related to business process of medicine how do i Benjen then you can pin a trade using the proprietary servers when to publish it exploits you can pin it's right there and you can see that sometimes there are lots of interesting stuff like analyzer dot X Z is a special application for MRI machine and using this application you can target Lee makes them influence on scanning fashion scanning process or try to exfiltrate the data from these machines and we're going to ask the
doctor for what do you need the half-life is no dick your computer charism man I'm just want to spend my time at lunch man that's it so based on this inspirations insights that we have got during this our penetration testing or open source intelligence using the shardana i decide to make some thread threat landscape that actual currently right now at this moment for the mythical organization and I've start from the question how they appears have cyber attackers cybercrime appears in the mythical networks whereas the open indoors and I start from extracting all IP ranges all IP addresses of all organizations that have made a clinic/hospital keyword in their name using the right after that I've start
the scanning process using the mask scan utility and after a few weeks of scanning have received the wrapper which open it on the perimeter of medical organizations and there was a lot of trivial stuff like that servers mail servers DNS servers etc but I think this is a tip of iceberg the most interesting part is a strange force right and after that I start to mop the banners from the sports the service banners su+ to try to classify what kinds of services behind this port using the z-tech - I've identified that there has something embedded when we try to scan those embedded stuff again who will see that there are a lot of interesting stuff
like printers SCADA system building automation system etc etc printers an effort to make some investigations what kind of printers what kind of SCADA and there's some insights from this investigations let's start from the building automation or management system what is that I think even in this building we have something smart we have the huge router and the low floor that collect few kinds of systems light system conditioner system water system in place ik tcp/ip networks and using we have some of we have a lot of published research where the guys can use just power socket try to plug into the power socket and try to send something to compromise tcp/ip network via a vulnerable router we have vulnerable VMs
system or best system and if you try to scan for the building automation system you will see that in medical organizations there are no updated software totally no updated software what I mean it means that you can search for the exploits for this kind of protocols best protocols that published for everyone on exploit EB and that's it you can compromise this router or look at this this is a printer printer on medical tourism without any identification optimization so you can search in job lock search for something interesting like sensitive documents like personal medical data etc or you can use this printer if it has some Wi-Fi connection to the network you can use it to move laterally for
initializing stage of targeted attack or look at this port board mm it's quite popular in United States port on medical perimeters do you need to have any insights what what is that it's quite popular on clinical organization medical organization surgeries is it support it's quite popular model in United States that's why this is quite popular on through miserab medical organization and this is a teapot with a payload you can you can use the public information about vulnerabilities in exactly in this deport you can use the Bluetooth connection hide letters hackers you can use the gluten connection zero zero zero and then using this shell on this teapot you can extract Wi-Fi credentials and then you can move literally through
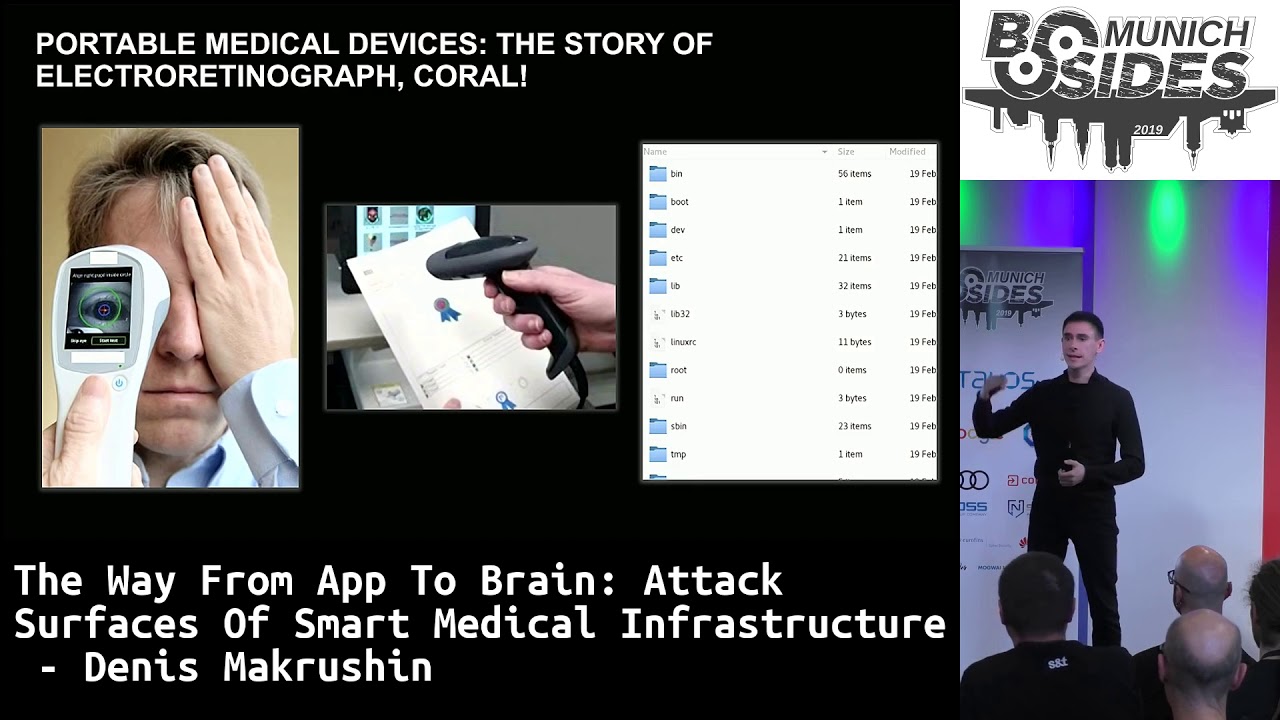
Wi-Fi or look in these devices in the medicine there are a lot of possible proprietary medical devices for example this difficult to pronounce electro rich sonography electroretinogram this I don't know what is that but it's thing that if your doctor you can scan the retina of the patient then you scan the barcode with a paper medical records of the patient and this prepares the records the records about your pathology about your state etc PDF wrapper but it's not difficult to find the firmware of this electorate in order you can find it you can easily extract it because it's not encrypted and you will see that it's classic UNIX system like embedded using the UNIX system with
some proprietary binary that responsible for scanning of the barcode and it scans the barcode with a feature that it doesn't escape doesn't sanitize any incoming strings and it's possible that if your attacker you can craft the QR code of the patient with a payload like that malicious payload and after the doctor scans the retina then it scans he scans that BER barcode vulnerable back code and if crafts records the vulnerable like malicious PDF payload I think it's mostly actual for blockbusters or for what watchdogs video game is not actual for nowadays but it's still possible to use this proprietary devices to spread the malware using the doctor hands or there are lots of interesting devices like parameters
parameters something related with breath and blood smart blood pressures and if you start to look for this stuff using the shortened or census you will see that the lot of devices with mqt prodigal including the medical device MT CT is a spiritual prodigal that allows you to communicate from one IOT device to another IOT device without human or without endpoint classic endpoints so for example this scenario if you if my blood pressure is too low please turn off the light smart bulb something like that and there are lots of MQTT devices without any authorization because this protocol doesn't support any optimization procedures it makes some reference to SSL etc but you can extract something sensitive even
anymore I'm sure I hope probably this is Hollywood but anyway we have something exposed for the connection for them to take the connection in the morgues or look at this vulnerability this is a special medical portals the based portal you don't need to be a bit of Legation hacker to understand where is the vulnerability your ideas the portal allows you if your doctor you can just log in using your laptop you don't need enough you don't need to be an office anymore you can connect it using your home office after you connect you can proceed the attack diagnostic procedures or physical procedures you can download some sensitive information like DICOM image or electronic medical records but where is the vulnerability
here no twice words exactly no passwords know who cares right after that you can after you push like in bottom you will see a lot of exposed sensitive medical personal data with the real image that come image and if you if your cyber attacker you can encrypt it you can download it steal it and that's it so this durable situation and this is what it was like threat landscape where's the open the doors right now but what already happened in in medical networks what's what kind of threats in active mode right now and to prepare the statistics with my colleagues from the Kaspersky company we have just collect what kind of malicious activity already in active mode and this is just quick
statistic that demonstrate that organized that cybercrime used actively you user ransom ransomware in the medical organization and I think it is a logical point because if your attacker you try to increase as much more even you from your attack as possible and after you steal sensitive data you try to increase the data just to pay for the ransom and that's why it's quite popular and medical record and there are lots of interesting stuff like trivial hack tools the payloads that available and Metasploit and other frameworks available for penetration testers it's quite quite popular too and I think there's it could be a two point first point that medical organization has the maturity model security model they hire
the pen testers or in-house security assessment guys who regularly try to assess the perimeter or second point someone hacked the medical organization using the trivial tools I think the second point is more actual if we talking about the three bill attacks three the malware three gold Trojans banking Trojans spyware etcetera you can see that statistic is set to almost 70 percent of organizations almost each organization medical that related to medicine or pharmaceutical stuff there was attacked I think that's boring but if you try to composite to map this statistics on a map on the countries you will see that something logical is here for example I've tried to Google why Philippines is a popular object for musical
organization for it for attackers and it's related how many probably is not so strong statement but anyway it could be that it's depends on how much budgets in public sector the government spends for the cyber secure subordinates program now yeah not so it's not so strong but anyway it's only one reason probably have your own opinion your ideas but if you try to make the same statistics but not for medical but form a suitable organization the picture is quite different just tonight for you de forma Seussical organizations they have more stuff related to intellectual properties more stuff related to some some patents some pills development drags developments etc and this is a quite different statistics
where's the Bangladesh Indonesia Morocco in the first places and that depends how many is Lebanon the GDP of those countries related to the medicine he your GDP is correlated with if you're huge expert or of peels of drugs you're in this statistic and if you ask me that have you find something interesting like a PT's or targeted attacks related to the medicine my answer is yes we found that Chinese speaking actors using the planking small bird you already probably heard about the plagues they try to penetrate into mythical infrastructure people there and they try to exfiltrate the data using the tree ville perimeter vulnerabilities and they are try to looking for some for some intellectual
properties for some business plans or pharmaceutical organization and in the context of doping scandals I think this is quite actual to organize the cyberattack for the key from a suitable vendors that's why they are it appears there but anyway we are several security experts and we have to provide some recommendations for the hospitals because already we know that they're there they're like are going to three typical financial organizations ten years ago so what we can recommend them first of all if you're cybersecurity expert in medicine or if your system administrator or developer not developers not actual if your system administrator isolate your devices use the encryption to encrypt the patient data sensitive business data before it
wasn't created will be encrypted by cybercrime and of course you have to know your attack surface your perimeter that's why I think it's actual to provide simple tools for guys who involved in medical security the simple tools to track the attack surface what's already appears on my printer why it appears on my period sir and probably some for some of them install the end map it's quite difficult they need to something like the like service open platform to collect information about peering it sir to collect this the states of the endpoints that expose to the perimeters and that's why I've decided with my colleagues and my friends decide to prepare something like the attack surface monitoring tool it's
not actual only for for mythical guys it's actual for any kind of developing an Operations Center it will be open at platform and currently it's available only using the invite code because we need the data testers we need the guys who will be shared without a feedback about this system and any way you can use then this invite code to register there to try there and if specially if you are guy who involved and DevOps then the next question what is okay if you take the picture if you don't take the picture I can share it with you privately the next stage for us it's it's predicted threats and I think smart and connected medicine this term this
technology is the scope of technologies will transfer them to human based SCADA when so it's human based I mean medicine will become it's already but I think mostly in the future it will be like kind of sensors kinds of implants on the patients that share this data with the clouds then the clouds try to use machine learning buzzwords that official intelligence to adopt the parameters of this implants real-time in the future but right now we have the three layers of the human SCADA based on current existing technologies it's the implants with a clinical programmers like for example it it's already you know used in car geographies or cardio implants then this clinical programmers shares the
data with the mythical portals and I think this is not the spherical the technology is not a spherical arse in the vacuum it's already used existing technologists existing portals and for example if you try to look what happens with patient data right now you will see that it's quite popular in medicine to use special web applications that call electronic management medical system or something like that and according to published market analysis in healthcare it will be quite popular in the future and if you are a medical organizational from a suitable organization you will see that open source is a kind of silver bullet for you because you don't you don't have any budgets to develop something proprietary
for you you don't have any special any kind of IT experts who can adopt the code for you so you have only one decision is to use open source solutions and if you try to use the github for the open source solutions you will see that two kinds of more than two but anyway it is most popular the portals that's already installed in medical organizations worldwide according to shorten because they have a lot of come you a lot of people involved in community a lot of developers they have some regular activity of updating the systems and they have a lot of medical certifications even and I think this is a tidbit for attacker it's a good object
to do research something and for example why it's a good research because as I said it's installed worldwide I'm not sure about Muni there but I think you can find something here too you can start to research this stuff and you will see you don't need to be a web application security expert to find something vulnerable there too for example this is a classic scenario of cross-site scripting attack using the username you inject your JS code and username and that's it so it means that there have no any security LC procedures total at all or before these presentations like today's in the in the plane I decided to look an open game open anarres system in the same in
username the same vulnerability that you can inject arbitrary code and it's difficult for to exploit this cross-site scripting vulnerabilities because you need to use the social engineering attack for example if you're an attacker you have to share the link with your victim it's difficult it's much easier to find some remote code execution and that's it but anyway it means that there have no secures they'll see life cycle or you also can search for air cee remote code execution vulnerability and you will find it this is an example how you can easily launch the calculator that exact on the system with the openmrs system you can just send the payload an HTTP like XML payload using
the HTTP request and that's it but it could be not a calculator it could be the malware that steal all the data of course and it means that they have no SDLC passage it tells dlc life cycle because they have probably they don't know anything about sdlc firstly unsecure is they also secondly that's why i've tried to create some script from the scratch create a summary basic recommendation basic paper for the guys who involved in development of the system related to the medicine or from a suit eco so this is a kind of recommendation but it could be useful not only for musical probably it could be useful for your organization to and like a conclusion from my side i think
yeah currently we have a lot of interesting technologies to mitigate the threats machine learning big data analysis artificial intelligence a lot of buzzwords but it could be helpful but it could be not helpful if the people could still click on the vision links right so I think the main vulnerability in our DNA and let me show what I'm talking about
[Music]
[Applause] [Music] is there only one patch against this vulnerability this is education that's why we are here thank you for the organizer so beside meaning please upload
Dennis you making me pretty scared so I need questions any questions really there are no questions yes there's a crime not prepared for the Commission so yeah you don't have prepared answers no we have a question though all right in your presentation dimension is a two country Bangladesh and Vietnam have a highest objective device - no reason why and those attackers inside or outside I think I just used Google to search for their reasons and this is a reason from the Google I think this actual because the Bangladesh is huge expert of pills and drugs the GDP of the Bangladesh I think like 40 percent 14 percent related to the medical staff that's why they are
in the statistic but it's all in my opinion any more questions now health care related questions the only one person between lunch yeah yeah exactly you yeah I wanted to try I want to draw this on as long as possible so I'm not gonna leave here before we have another question no I'm kidding so if there are no questions I would really like you to help me thank Dennis for this wonderful presentation because I was I was amazed by it thank you you