G1234! - Measuring the Use and Abuse of Brain Wallets - Ryan Castellucci & Marie Vasek
Show transcript [en]
we're here talking about some work that we did along with some other people on measuring brain wallets so who in ah we can go to the next slide I'm a newly minted professor of computer science university of new mexico just finish up my PhD and a lot of this work was part of my dissertation I discovered Bitcoin back in 2011 and it's interested me ever since I wrote my first Bitcoin papers in 2013 published in 2014 I'm also a con noob this is my first hacker con I'm Ryan Cataloochee I don't do Bitcoin stuff professionally this is just one of my weird hobbies I think somebody described this is Orion tries to prevent people from losing lots of Bitcoin and
generally this pisses them off so a from a sexual job I do bought detection research for Y tops and then Bitcoin I have been messing around with since early 2011 and I'm not sure how many hacker cons I've been to at this point but it's not your first so if we think about how to securely do key generation we could look at a scheme like RSA now a bunch of really smart people have taken a lot of years to write libraries in order to generate really really big random numbers with very special properties these numbers have to go through some approach X and then make some calculations based on derived values now Bitcoin uses another tick
curve key generation if you went to Ryan's talk you know that what you have to do is generate a random number basically what it has to be is it has to be 256 bits and it can't be 0 and it can't be another number so this this key generation process can be fairly trivial now there are ways of securely doing it however if maybe you don't trust your computer you don't trust the hardware you don't trust the random number algorithm that some person you've never met wrote you could say hey why don't I why on create my own system and why don't we base it around something really really secure I know how about passwords
and so what these people did is they use this MIT really easy-to-use tool um you just insert a password and the Bitcoin private key is the hash of the password now people have actually stored quite a bit of money with these schemes and so on the flipside so on one hand there's these users that have lots of and secure money stored and so naturally there's this attacker ecosystem that evolved out of that it's like a money pinata you just have to guess the right password all right I'm sure everybody who's seen this comic before but this is this is xkcd on passwords and the the passphrase is that this this suggests using are more secure than typical passwords but
um they are not secured against offline attacks so one of the offline attacks that I ran when trying to look at what passwords people had used for brain wallets was based on xkcd password generation I found a couple xkc password generator tools used their word lists and generate a lot of passwords I think it was a couple trillion so correct horse battery staple was actually a default password on brainwallet on org which resulted in it getting you mistakenly a lot and it was also involved in some of the bitcoins spam attacks that happened one of the ones that I found that was more obscure was expect-- pants size clue which actually looks like it was a randomly generated
one that somebody genuinely thought might be secure that one held 2.18 Bitcoin in it then there was earth air fire water which is not random of course and then deal iron science food that one actually does seem random - although it's and we had a few cents in it and due to the transaction that created it it looked like it had been made by somebody who is just trying to put out bait to see who would take them we also identified a large group of brain wallets that were created in August of 2014 all of them were extremely simple single word passwords there were about 15,000 and something of them all created within the span of a few hours and all
of them had only tiny fractions of a penny worth of Bitcoin in them so we're we've excluded those from analysis because they're not interesting and as far as other things try it as I mentioned xkcd style up to four words for four words I had to trim down the word list size just a little bit so I picked words that were common between the three tools that I found but for three words I combined all of the lists and use all of the words and got some hits there as well cryptocurrency IRC chat logs were sourced from my computer I've been sitting on a bunch of cryptocurrency channels on freenode for a good six years and I just
the mall in his past phrases that got some weird hits like somebody had used was it there's a Bitcoin over-the-counter trading channel and there's a bot you can authenticate against and somebody used an authentication string that was posted in the channel to authenticate to the bot as a brainwallet password again this is that was probably somebody just doing that to see how long it would take then there's a data set of reddit comments that is available online it's got comments for basically every every subreddit since the beginning of redmond except for a few some comments have been deleted in there but mostly it's complete that was that was processed mostly to strip the markdown punctuation that
reddit allows and do some other minor cleanup wikiquote I scraped and turns that into a phrase list Wikipedia the Wikipedia list I used as far as I can tell was included with ocl hash cat at some point that was the list that I found the how much wood could a woodchuck chuck if a woodchuck could chuck wood brain Walla that had 250 bitcoins in it and I tracked the guy down and he moved he moved the Bitcoin out of that wallet was very appreciative brainy quote is another site I scraped basic normalization Facebook names came from Skull securities lifts ribbon dictionary I scraped and then I purchased a song lyrics database that was fairly recent and that was where I
got that data I would cited phrases I I think these lists should be familiar to a lot of people the rock you list is of course obligatory crack station has a good list there's one put up egg a guy who goes by éxito I don't know if I'm pronouncing his handle correctly but it is very large I think it's about 40 gigabytes uncompressed and full of kind of garbage so I clean that up yeah and got it down to about 4 gigs but originally it had for example every 5 letter asked there 5 character ASCII string in there using printable characters and then having them and no list is not super helpful uniq passes a commercial list that you
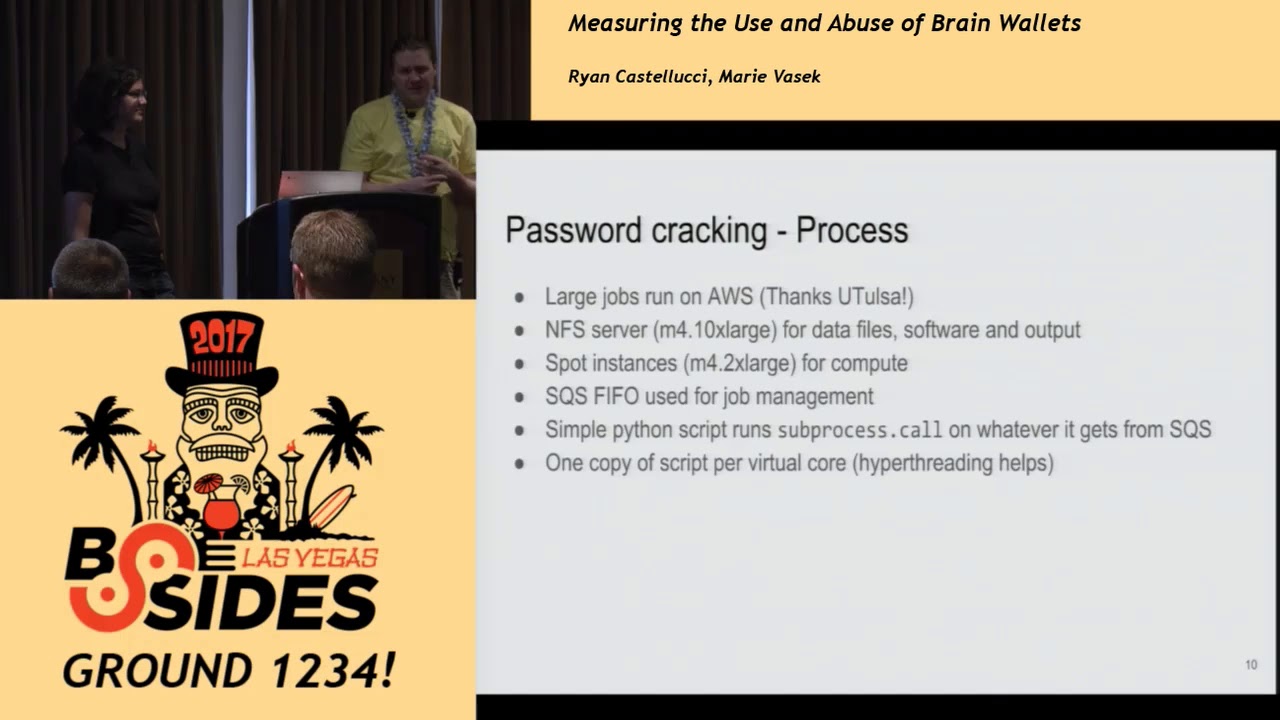
can get fairly cheaply I have a couple different versions of it because they update it I think quarterly and school security as I mentioned I used that all of their lists and I did a bunch of brute-forcing every ASCII printable ASCII up to 6 characters lowercase letters up to I believe 8 numbers up to 10 or 11 I think it was 11 and this was all done on AWS so so the AWS setup there's an NFS server that hosted all of the data files needed to feed the cracker all the software was on there and output was written there two directories named by job ID so they wouldn't overwrite each other and so that was non the man
instance and then they used a bunch of spot instances for the actual compute if you're not familiar with AWS spot instances are a way for Amazon to sell capacity that they otherwise would not sell by letting people bid on it so if you want to do a bunch of compute and nobody's willing to pay full price for certain type of instance at that particular time Amazon will let you do it let you use it for a steep discount the instance types I use typically you get an 80 90% discount by tina this way the caveat is if anybody else wants to spend more money than you your instances go down with two minutes of warning so it's good
for certain kinds of workloads where you can split the work up and keep track of what you've processed and restart redo redo interrupted work it would not be a great way to run a web server for example so this with a bunch of spot instances I had to have some way to distribute jobs so Amazon has something called simple queue service and what simple queue service does is you set this up you set parameters like whether you want exactly once to delivery first-in first-out how long whether you want the messages to be resent to a worker if a worker doesn't confirm that it has finished processing by deleting their mess their job and they have nice
Python libraries for interacting with that so that's what I did I wrote a Python script that added jobs to a queue and then a script that ran jobs from the queue by executing them directly which is completely insecure but yeah it's it's my job queue and then one copy of the script run for virtual core so here's here's what accessing the sqs api looks like credentials removed for obvious reasons just a couple lines of code to set it up then to read the job queue I have it get one message function calls receive messages maximum one really straightforward and then to actually run the jobs there's just a pretty simple loop and all of this is
started up using the cloud init functionality that most AWS instances have and the this is when you start it up you can say okay I want 30 machines and they should all run this shell script when they start up so the shell script will have them mount the NFS files or Melfi em in NFS file system execute the job runner script and anything else you want to do like like even you can install updates or whatever and let's look at some example cracking jobs so the applicant utilities are fantastic for all of the pieces that I don't want to implement myself as far as password Canada generation goes so this first one is using a tool from hepcat called NASA
processor and what that does is it just generates passwords based on a mask this is some specific ASCII characters followed by its like yeah for lowercase letters so yeah so it will go right through all of the possible ones and the reason it's picking out specific characters is because there will be I had a couple thousand of these running with different first characters and they all wrote two outputs which were then merged at the end then Combinator 3 is another tool that I was using to do the sum of the XK CDs passwords had to split this up into a bunch of sub lists as a way to divide up the work but what this
tool does is it you give it three input files it takes the data from each file and outputs every combination one standard out so anything that can read from standard in on standard i/o can use this as input for cracking so this is I don't know how many of those jobs total there where this looks like it was job 925 um other shell shenanigans this is going through the skull security word lists that I had picking out the dot txt files removing the redundant versions removing RockYou because they did other things with rocky and then passing it through through can to combine them all together and stripping out da style new liens because da style new lines are no fun
this used a feature in brain flare where it will start in this example start at the fifth password given and then only process every sixteenth final example is just the hash tag by taking in a combination of rock you myspace and Linkedin and running in this example the leet-speak role set on it and passing it in for drain blair and the shell script is is a really simple thing it just has common parameters pre-loaded so that i didn't have to put any of your job one of the interesting things I learned the my first attempts of distribute data files was to put them in an EDF snapshot which is I think stands for elastic block
store lots of three-letter acronyms on AWS so that was incredibly slow it turns out that the first time you access a block in one of those it has to fetch it from s3 and it goes somewhere so this was just unbearably slow so I went with NFS instead which still takes a long time because it has to copy bring player usually was loading up about 20 gigs of files to do its run and there's a copy there's all over the network which takes some time the other thing is this spot instance price can vary a lot between regions and if you want to do large jobs you have to call Amazon and say hey I
know what I'm doing I will not get myself into millions of dollars in debt by running away too many instances please let me run more so you have to get you have to get a limit increase approved and like if you don't have a limit increase in the right region that can be problematic this is if you if you've got an AWS account and you're planning to do something like that you got to do it a couple weeks ahead of time just to make sure there won't be problems okay so Ryan dealt with getting all of the passwords processing them seeing which ones were actually in the Bitcoin blockchain then the next thing is to find all the
transactions the passwords that are actually in there as a first pass we had an entrepreneurial undergraduate who wrote a program to download the block pane gather transaction data for each of these brain wallets however we don't get that granular of data when we're doing it on on transactions that happen years and years ago the attacker is also drain way too quickly for us to pick up information because you get about a 10 minute granularity when attackers are working within seconds so what we did is we use the blockchain dot info API they can give us when the transaction that put money into wallet occurred and then the next transaction a couple seconds later when the attacker drained the
money out of the wallet this isn't as defensible is downloading the blockchain so we also sanity checked it using the first method and it's same information different granularity of time so Ryan took three point nine trillion candidate passwords and from a bunch of different lists now this is a edited version because there's all of those lists that he talked about but these are the most interesting ones we can see one that really sticks out is the reddit one that was reddit comments reddit user names we see that on this forehand column it's the money in US dollars so it's it's the most it also has a lot of the really unique ones and the data set there's some other
interesting ones so Lamas off to gave us some data that's used just for you guys today it was two hundred and seventy five wallets they're all unique in the data set and it's actually quite a bit of money it's about fifty thousand dollars we were surprised that brute-forcing didn't get more there's only 84 unique and only about twenty four thousand dollars and then from miscellaneous that was some old data that was some combinations of data those were all unique because we tossed out anything that wasn't unique so there is about 2000 total distinct brain wallets just over that there's just under that distinct number of passwords that's because some passwords were turned into two brain wallets one compressed one
uncompressed we also found about 3,000 Bitcoin now that sounds like a lot of money but a lot of this was lost back in the day when Bitcoin wasn't worth that much so what we did is we converted it to the amount of US dollars that it was worth when it was put in and that's about three hundred thousand dollars so it's it's a good chunk of change we know that we're necessarily missing things right so we only have information on brain wallets where we actually knew the plaintext but it's still a good amount of money we have some notable past phrases so the first brain wallet that we found was this string contains 0.25 Bitcoin hiding in plain sight some guide
posted this in the Bitcoin forums back in 2011 it was the first real time that people started using these brain wallets and around the time of his post people in the forums also created other similar wallets it was the first kind of community around brain wallets however unfortunately now the the second one is the empty string this is the most common brain wallet and I don't think anybody actually ever intended to put money there but a lot of people did and a lot of people lost a lot of money this is because of softwares it was also one of the default passwords on brain wallet org which people used so if you didn't understand what a brain wallet was and
he went to the website it would automatically prompt you with you know a private key and a public key that associated with it and the private key was just the hash of the MD string we found the most amount of Bitcoin tied to this phrase Bitcoin is awesome now this person put the money in and then he drained it himself we found 500 Bitcoin now the drain that walk Ryan did the woodchuck drain while that one had fewer bitcoins so bitcoin is awesome is 500 Ryan's wood chuck was 250 Ryan's with worth a whole lot more because the price of Bitcoin at the time of the drain was not insignificant if anybody hasn't seen my previous talks I
like I put the money back because I emptied it on accident and then I found the guy and got him to call me and I explained why this was bad and he was happy so we noticed that we normalized the price of Bitcoin to US Dollars and that's just because the price has fluctuated a lot over the course of the time and Bitcoin brain wallets were actually somewhat popular in 2011 so the first post in the forum that started off Bitcoin was in July of 2011 and we cut off our data collection in January of 2017 the bars is the number of new brain wallets used every month and then that is this axis so in 2017 there's a couple
created we can see that there is a bunch more creative in 2013 the gray is the uncompressed brain wallets and the black is the compressed now what's really weird about this is the most popular type of Bitcoin wallets more recently are compressed wallets you save money because you pay a transaction fee based on the size of your transaction and compressed keys are smaller than uncompressed so you actually save a little money by using pressed we know that the default standard for most of the brainwallet websites is uncompressed which is why we see this trend though we do note that during this time period here compressed keys weren't available to get into bitcoin it is certainly days
now in the blue line what we see is the new wallet value in u.s. dollars and then that axis is over here and we see at the beginning while there's a bunch of there's some brain wallets that were created they weren't actually worth very much because the price of Bitcoin wasn't actually very high and we can see it it approximately tracks the popularity though there's a couple big fish that put in quite a bit of money so on one hand here we're looking at the user behavior we can also take a look at the attacker behavior so we can look at the time that it takes for an attacker to drain a brain wallet so in black that
shows the overall amount of time to drain so our time to drain metric is the time from when the user put some money in the wallet to the time that the attacker drains the wallet out of drains the money out of the wall and he puts it in a zone we used a cumulative distribution function so we can read this chart as on the bottom is time and hours and on here is our cumulative distributions so in like you know it's about half of all of the ever drained brain wallets were drained and then we can see about 80% took about half a day and almost all of them 99 percent of them were drained within 24
hours now there's some speculation that attackers were colluding together and they were trying to not drain wallets that only had a small amount because some users were using this to test the security of a brain wallet so they so some people thought that maybe if you get them to wait a little time it's not drain then they'll put a bunch more money in we can't really see that effect so in the rabbit and the blue is so the red is wallets I had less than a penny in them blue is less than a tenth of a penny well it's actually significantly different than in our overall trend a lot of that is because transaction fees
right so you're not gonna if you're trying to drain a penny during some amounts of time you would actually have to spend a penny to get that transaction on the network so it's not actually worth it and so what these attackers would do is some of them would wait for more things and then some of them would wait for a mining pool that would just take a transaction with a lower fee now we can look at how the attackers changed their behaviour over time so in the early days of Bitcoin in 2011-2012 attackers took a longer time to drain those brain wallets there's fewer attackers so we looked at the number of unique addresses that these brain
wallets were drain to so a lot of times the attacker wanted everyone to know that they had the money so they would have one unique address it might be a vanity address and we can see that it goes down to zero so here in 2014 the median time to drain is seconds it picks up again so in 2015 there was a lot more time with just all transactions that spent and so it took longer for any transaction to get on the network and brainwallet transactions were no different now we also want to know two questions about the under all underlying passwords that were used so when one hand we want to know if user behavior change so did users put more
money into rain vaults that were better that were more complex harder to guess on the other hand we wanted to know if attackers because there's just so many of these brain wallets that we're with really insecure passwords we're attackers actually going after more complex passwords or are they just sticking to the easy to get ones and so what we did is we measured the complexity of each of the passwords that we found we used zxc vbn which is a which is a password metric it's developed by wheeler at Dropbox it's one of the canonical measures we actually tried out a couple other ones but they gave us about the same results and we tried to see if more complex passwords
affected anything so we looked at every single thing we could possibly try to throw at this we used a Spearman rank correlation coefficient and we couldn't find that it was significantly correlated with anything so we don't actually see any effective password strength on anything this is actually in line with literature so if you do a bunch of user studies and people have looked at passwords that users use for Bank websites compare to throw away websites users don't pick stronger passwords when securing more money or when securing money at all compared to anything else that's that's the same that we found we also noticed that attackers don't prefer more complex passwords they just like more money two
quick notes about zxc BBN one if you don't understand the name look at the bottom row of a keyboard - it is very much designed for passwords not pass phrases so here's why we have the next slide so the next slide we tried to look at the length of the password and we could see that the 0 to 5 character passwords or drain much quicker those are in green than overall which is in black however we tried to look at longer passwords which are in blue aqua and red and they're not actually significantly different than the overall trend so we can see that small number of character words which are likely to be passwords and not pass phrases are drained quicker
we don't actually notice any difference between pass phrases in the overall effect right so people taking money from weak Bitcoin addresses is not limited to brain wallets there's a lot of other bad key generation stuff that has happened one of the most notable was some Android Wallet software was not using proper random nonces and if you create two transactions with the same signature nonce in Bitcoin that is sufficient to derive the private key which is a problem the popular brain wallet org tool had a random button on it which would just generate a random key for you but it works by calling the thought random function from JavaScript and that was not very random in Firefox
in particular this the random number generator is seated essentially just by the time of day that the page was loaded so that's rather easy for an attacker to replicate and that was the random function on brainwallet org so a lot of users were actually using these things and thinking it was secure yeah I actually talked to somebody who lost money because of that other other tools allow users to they have they generally are used with random seeds but the user can select their own if they try there's a bunch of example published example addresses that have published keys with them and I've seen seen those cleaned out whenever somebody sends to them for whatever reason also random arbitrary
constants are sometimes used as private keys for reasons that I cannot begin to speculate about I've also seen random data from the blockchain used as private keys hashes of files then if theorem there was this site called ether camp and it did it did a cachet cache of the password and it didn't tell you that's what it was doing you'd go to the sites and hit generate new address and say oh here's a password and it it didn't say how it worked and I suspect some people got burned by that and then after I [Music] called the guy out on this he was like it's not a problem it's not a problem and then a bunch of other people yes it
is he replaced it with something that still was not secure I think it does 213 rounds of of KISS check because nobody has rainbow tables of that or something then there's the etherion parity which is has been in the news lately because they had a bug in one of their multi-sig contracts that caused that resulted in a 31 million dollars worth of aetherium not a private key problem just the etherium has smart contracts if they have bugs they can be real big bugs and then weird payday script - stuff so here's some private keys they're all empty but feel free to check and there's a bunch of weird stuff so the first one is the sha-256 of one of the default
pictures that comes with Windows 7 chrysanthemum dot jpg how I found that I fed the contents of my hard drive as raw private keys in what that house was doing on my hard drive I cannot tell you the next one was a Bitcoin transaction ID the next one was another it was on my hard drive I don't know why it was just a bunch of it which is part of Pi represented in hex as the fractional part of Pi represented in in hex although it was it was robbed i'ts on the disk another was a padded zero padded hash 160 of that address found one that was one two three four in ASCII prepended with the bunch of nulls which
is of course the frame wallet an idiot uses on his luggage the next one was n which is the order of the curve - 105 and about week or two ago somebody sent ten Bitcoin to that and it disappeared right away and this person was kind of sad but he said it was his fault I messaged the guy on the coin talk trying to find out what happened there another chunks of raw data from Bitcoin transactions block hashes other random strings of bytes that were on my hard drive for who knows what reason the sha-256 of the Bitcoin paper was used as a private key and then the last one was just one and I I don't know what
to say about that we also found some other interesting things so there's a couple ways of making Bitcoin transactions we looked at hated script hash also and we found 139 Bitcoin brain wallets I'm their first seen in March 2012 and actually quite a number of them are still under aimed there's most of that money is actually all in one of the wallets there's ethical reasons for us draining it there's Exel reasons for you not to drain it to the ones that were draining though again we're drained in 24 hours the median drain time is 9 hours so they're about like the other ones they actually have a similar group of attackers so about out of the hundred
ones that were drained there's about 25 different people who drained it and 13 of those also drained brain wallets and at least eight of them were spam attackers originating from the same group and one of them was a mining pool and we'll talk about both of those later yeah about those ones the pea script cache ones that aren't drained I believe all of those were two addresses for for which there is no way to satisfy the scripts to make it spendable so yeah so the large Bitcoin Collider is is a interesting project that somebody started up on on the Bitcoin forums and this is if you remember steady at home if this is that for Bitcoin just
sequentially searching all of the key until the end of time or whenever somebody decides that they're done burning electricity on this so they're doing an incremental key search and they're only searching for keys with a balance which really disappoints me because it is interesting to see keys even if they don't have a balance the admin claims the sweeping funds as Austin found is legal in his country which is somewhere in Europe and I I have no comments on that claim they have a gpu-accelerated client that is able to do sequential search only it is launched by a scary piece of Perl code that will execute arbitrary code from the server that was that was also there was a
debacle about that some people tried messing with the script and it started deleting itself after the server set back a kill command people weren't happy they actually did hit some keys with small balances these were likely original keys not not collisions none of them had very much in them and I assume they were tests there's also this puzzle transaction I I wrote a blog post about it but basically somebody made a Bitcoin transaction with 256 outputs each of which had one more random bit in it than the last so it would be a bunch of zero bits followed by a one bit followed by random bits and so they're chewing through that and they've gotten up to 2
to the 52 and think they're not going to they're not going to find anything from anyone who used a proper random number generator so most of the transactions that we've looked at have been Abba sort users money gets drained to an attacker in the early days that's what they look like they might leave a small transaction thief the mining pools later when the when the time to drain went down two seconds one way to have your transaction be the one on the blockchain is to get a larger transaction fees the miners so that I get to put on the canonical chain so we're used to seeing that sort of thing however we notice that there was a number of brain wallets
that were just drained completely - transaction fees and that's what I have this slide in the next one talk about so we saw there was only eight different mining pools that did it they drained quite quite a lot of brain wallets though the amount of money was quite low so they only in all of these drains it was like less than five hundred bucks so clearly they're not doing it for the money well not I mean not clearly but they're not doing it for the money but why so in Bitcoin what was happening is people we're putting like the lowest number of Bitcoin that you can into brain wallets and they were just flooding what are known as the
unconfirmed transaction at puts so people who want to run Bitcoin owns each mining pool has to run at least one Bitcoin node it eats the disk space so it's all of the transaction outputs from previous transactions that still have not been spent now one group of people that decided to abuse this was in the the Bitcoin block the the network stress test were a bunch of people advocating for bigger block size cause mass disruption because that's that's what people do in Bitcoin and they were set out to create a 30-day backlog of transactions they achieved it they put bunch of money into fifteen brain wallets and some other types of easy to guess keys and they put a bunch of Bitcoin in it
and the mining pools then drained it so that it really reduced amount of consumption on the network though if we do look at the dates mining pools did that before the stress tests and after so before we end our talk and ask for questions we'd like to thank people that also worked with us on brain wallets so this is largely based off their a topper for my dissertation which was largely based off of a paper that Ryan and I wrote along with Joe Pino who's at the uff and Stanford he's a password X expert Cameron Keith who's our entrepreneurial undergrad and Tyler Moore who is my PhD advisor we'd also like to thank Filippo at CloudFlare
who did an earlier talk with Ryan at hope I believe yeah on brain wallets we'd also like to thank llama soft who gave us data that we used on this version of the talk and as a conclusion this is a this is a screenshot of a website run by ether camp about why brain wallets are the best and we're just like no this new one thing I would like to say about that in this blog post a challenge aetherium wallet was posted which i believe that current value is worth $70,000 and my estimate on the compute cost using AWS fought instances to crack it is about fifty thousand dollars so if anybody really thinks this
guy wasn't lying you could do that because he said it was available for anybody who could find the password to take and questions yes
okay okay so the question is okay so the question was how do we distinguish whether is a brain wallet a normal wallet what we did is we did that by guessing the password there's no way of just looking at a wallet and saying what it was but we only looked at things where we knew the password I am not familiar oh that oh so the question was about the random sanity org project by Gavin Ryan do you want to comment I have no comment on that service yeah I don't either sure sure okay next question okay so the question was have we spoken with the drainers Ryan yeah one of them reached out to me after the paper that
Murray and I wrote for FC last year was published and was was kind of bragging about his exploits a bit and mostly just wanted to get paid for data and we did not pay him for data yeah he wanted a lot of money for like the place yeah he wanted to empty strange like like if he wanted a tiny bit of money maybe I would have paid it out of pocket I've actually serious I planned to set up a website eventually to offer bounties for brainwallet planes but I have far too little free time yeah we also had some money that was just being able to that we were only able to spend on Bitcoin related research projects so
if it was actually good data and a small amount of money we could have paid it yeah but he wanted way too much money yeah so that's also like there are a lot of people who think that it is totally ethically and legally fine to drain brain it's um I think those people are but uh like on public forums people have bragged about this trivially attached to their real name like if anybody's familiar with hacker news somebody was recently bragging about feigning brain wallets out on Hacker News oh and there's also I've met people in person who have talked about it and talked about their crack legal theories of why it's okay yeah yeah there was
also a guy who was on reddit for a while who would take them and then if somebody posted on reddit hey where did my brain while ago he would give it back went by PTC Robin Hood I talked to him a bit yet another instance of people doing ethically questionable things out of the goodness of their hearts yeah next question yes so yes if we track the funds after they left the brain wallet the next steps we tried because we thought that maybe there is going to be a bunch of people that you know owned a bunch of identities that were draining brain wallets what we actually saw is that mostly they had they drain to one
single wallet and we could see some amount of people mixing their Bitcoin after it left either using a mixing service or by gambling using Satoshi dice at all but we didn't act so we we tried to do it but there wasn't actually that much there there are there additional questions I guess not okay great thanks for coming [Applause]





