PW - Passwords 101
Show transcript [en]
can everybody hear me y all right so if anybody has any questions ask ask me now don't save them to the end of the talk I I I it just drives me crazy because people forget questions and stuff so somebody said to have an about me page I have an about me page I'm not going to read it you guys can read it um I've done a lot of stuff mostly software some cyber security everybody got that so tools there's two big tools there's Dr the Ripper and there's hashcat they both have really good features they both are super awesome I use them both a lot in my experience I did much better with hashcat and GPU
accelerated Pastor cracking with John Ripper I having a little bit more trouble making that work um me switch glasses so with with John the Ripper there's there seems to be a lot more updates there generally of a less formal nature um but they're constantly under development I got very good support from the community that when I ever asked a question um the custom rules is going to be important I'm going to get to that later and so it does it doesn't really paralyze so well unless you do the magical things the command line to make it work when you have only a few passwords left with hashcat it it's really an awesome tool it is highly optimized to work with
gpus it tends to work very well um the the rule syntax is not as sophisticated as the John the Ripper rule syntax and I'll get to that in a minute and and there are reasons there philosophical design decisions and neither one is good or bad but I like tur rules so if you go somewhere and you see like here's a bunch of rules you have to find out if the rules are for John the riper or for hashcat because one won't work for the other one so word lists everybody's got them everybody says that they're the best most of them are junk most of them are really really bad the one that I really like the most is
Rocky but I've got probably 50 different rule lists I'm sorry word lists um I needed to make tools to parse these things some of them had non characters some of them had incredibly long lines some of them had completely random junk and so you've got a file that's a couple gigabytes in size and you've got to somehow make sense of it which is not very easy to do so I had to write some tools of my own to do that um but if you want if you want a really good one the rocky 2021 is a super awesome list extremely high quality there might be better ones out there but that that's the one that I that was my go-to list so
custom word lists so again since some of these are really long and a p so a password in GES is limitate characters so if you got a line that's thousand characters long it's not a password and it's probably junk um I wrote most of the stuff in Python short we'll take a big file and just get truncate the first few characters um there's sort which before G you could do offline sorting you were limited in how big things you can sort and when you when you want to combine different word lists you really have to sort them to merge them together and make sense of things sometimes they don't sort them sometimes they have the most common
words at the beginning which makes really good sense if you're in a rush but not when you want to manipulate multiple word lists um so I have multi merge which will merge any number of files um simple sample just grabs line every so often just to make give you an idea of what's in a file so when you've got a billion lines you're not going to read them all because you just can't um I I wrote other programs I have line length and I have count I also have a thing which does substring so if you have a thousand character line you can grab like the first eight characters then you can shift over and grab the
next eight characters and you can take you know Sub sub samples of everything and that didn't work out to0 for me but it's a tool that I wrote and I use that well so some of the standard tools GN sort super awesome now that it can work with more than physical memory it will just make temporary files and it just keep on chugging along unique will take repeated things and squish them down so you only have one of them Comm will give you things in one file that aren't in another file which is very handy and the one true editor emac so with emac you can edit multi- gigabyte files you can make sense of them you can
display things I know some people don't like emac you're all wrong for the in the context of password in the context of editing word lists and password files I I have yet to find a text editor that does a better job so hashing speed so NT landman is the current Windows hashing algorithm it is very quick and and quick is good because it doesn't use a lot of CPU resources and so you can do lots of passwords attempts very quickly on the other hand from a security standpoint fast is super terrible so md5 is actually slower than NTI landman there's landman which is the predecessor of N landman I think that was used with Windows xpn earlier I could be wrong DS
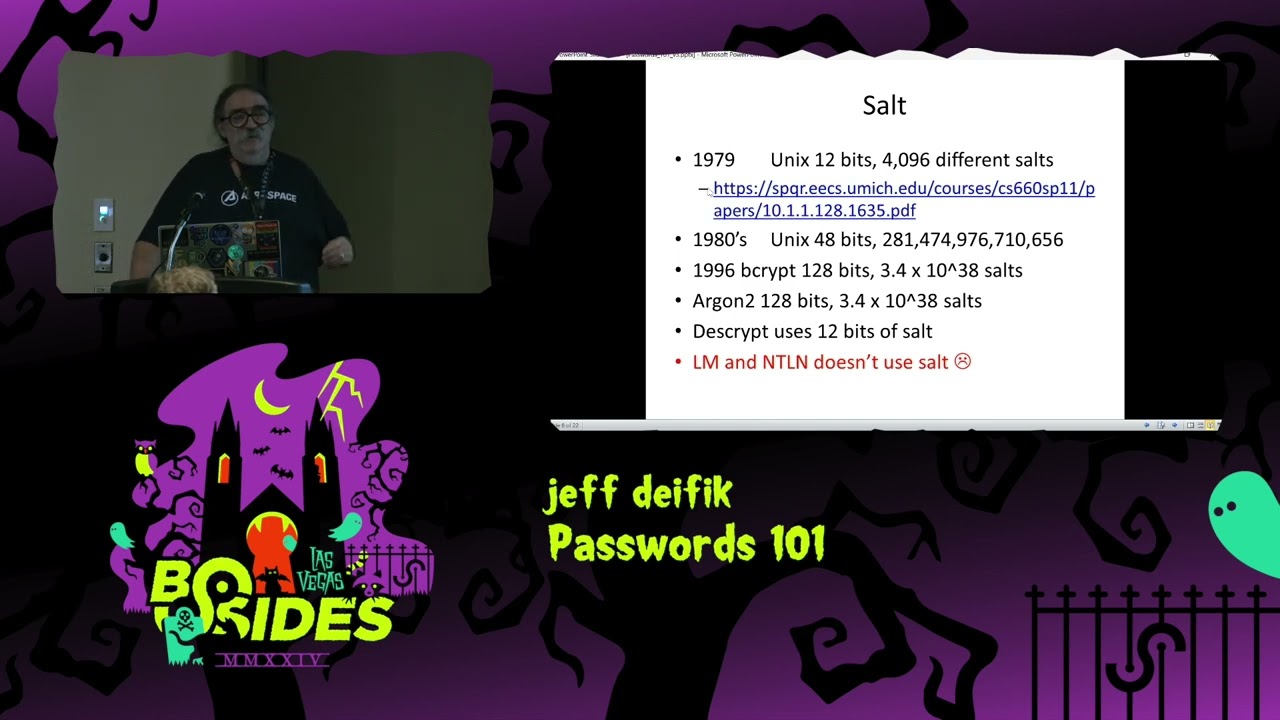
Crypt is the one that I use so these are these are all relative speed so you can see it's like a lot slower so for modern algorithms you've got sha one uh you've got script uh the wap2 and you have bcrypt bcrypt is probably what's used by most Linux implementations now it is very very secure it is very very slow and it has I think 128 bits of Salt by default which makes it very very secure so salt in 19 79 the Unix guys put 12 bits of salt in their password does everybody know what salt is anybody not know what salt is all right very good so let's say you have your password and your password is
password 1 two3 and let's say he's got the same password his password is password 123 so if you just what's that I'm I'm sorry I'm sorry so if you're just using some encryption function his password and my password encrypted would be the same so that's bad because if you break my password you have his One automatically so what salt does they they sprinkle this into the password it it's a little bit more complicated that they they sprinkle it in that's why they call it salt and in the case of Linux in 1979 they had 12 bits of random entropy so the chance of his password and my password having the same encrypted form is one and2 to the
12th but you know that's 4,000 so that makes things a lot better so you can have 4,000 people with the same password and you might get a few collisions in there but it makes things much more secure so again this happened 1979 in 1980 Unix added a lot more salt to 48 bits BCPS got 128 bits argon's another cool thing so Dees script uses that so the bottom line n landman today for Microsoft does not use salt so this is not a new idea don't ask me why they don't use salt so the thing is if if my password's password 123 and his password 123 on on a NT landman thing we're going to have the same encrypted thing so you
say who cares well people pre-compute lots and lots of passwords and you can either have pre-computed things you can have something more complicated called rainbow tables and when you don't have salt it's economically viable to pre-compute all this stuff so let's say you have a dictionary of a billion passwords and each password is eight characters long so that's 8 Gab so that's not a lot so if you want to have the encrypted form let's say it's 8 gabt of data but see now if you have linux's I'm sorry unix's 12 bits of salt that's 4,000 times bigger so instead of 8 gigabytes you have a lot more somebody help me out many terabytes of data so 8 8 gigabits
you're going to byes you're going to put on a flash drive it's real easy but when the modern algorithms with 128 bits of entropy that's a ton and you there's no way you're going to be able to pre-compute that and store it's just completely non-feasible but with Windows N Land man you can do that and so people do do that and so that makes so if you look at the encryption speed N Land man is really fast and there's no salting so maybe this made sense in 1960 but it's not 1960 anymore somebody should probably tell Microsoft that I I don't I don't know why they're not doing it again this this is 1979 that's what 44 years ago 45 years
ago so this this is not a best practice this is not a standard practice this has been a standard practice for several decades don't don't ask me why they don't do it so my DS dump I had 1576 passwords so the interesting thing about DS Crypt is you're limited to eight character passwords that's a stupid thing but in the context of the 7 and ' 80s it made a fair amount of sense um so I decided I wanted to break every passwor it took me 5 years which is a lot longer than it take me to do it again today um so using John the Ripper and using my and using no options at all this is
this is how fast you can get passwords so realistically I got a th000 passwords in 2200 22,000 seconds so that's like 2third of them so so if you want to break into a computer and you've got two-thirds of the password you're probably going to get some administrative privilege access by that probably long before then so only somebody with no life is going to break all the passwords because it's a stupid thing to do but I decided it was time to do that it's a hobby it's a hobby it's a hobby it's it's a hobby but but the fact is is that John the Ripper is is very very good and very very fast and it has very very good
default dictionaries and this is fast I mean look at this 537 passwords in 126 seconds that's 2 minutes so that that's the third the passwords so it's incredibly good at finding passwords so I was using this version and these are several different dictionaries that I use there's the small rocku dictionary it's 139 megabytes there's the weak pass dictionary the 2021 which is pretty big 98 GB and you can get quite a lot of password so with with rock Q I got almost 1,000 passwords that that's without any rules or anything I just let it go um so there's this option called prints I'm not going to go into what it is it's probability infinite chain elements it's
a very good tool to use to break passwords it's beyond the scope of a password 101 talk but if you're actually breaking passwords look into it it's supported by both hashcat and John the Ripper very very good thing there there's other options but this is probably your first go-to option when you're breaking passwords so my Hardware I have a 64 core AMD epic processor which I bought to used I started this with a Nvidia 1060 I went to a 1070 then I went to a 360 TI and what I wanted was something that would break a lot of P hashes per dollar and all those made cents per dollar at the time nobody's going to go
buy a 3060 today you're going to buy a 40 70 or whatever you're going to be buying um but these These are the tools that I used and I I also wanted to maximize the performance per price I also wanted to maximize the performance per watt so the the really fancy graphics cards the 4090 I don't know how many watts he uses 500 watts or something you know I can cool that but it's going to heat up the room and it's going to make a lot of noise and I didn't want to do that so I pick something that would be a little bit slower but not not melt things so I went over the word list that the
quality was all over the place um so there's basically two ways of breaking password either you have wordless or use boot Force attacks wordless are thousands of times more efficient if if your password is in a word list or you can come up with some permutation using some magical rule it's like add a number or dollar sign or you know change a three to an E or something like that you use use word lists so here's how long it took takes to do Brute Force stuff all eight character lowercase takes about 3 minutes on a GPU um 8 character upper and lower case 13 hours so that's a good amount of time now we add the lowers numbers and
special characters 5 and 1 half days now we have all the printable stuff 80 days so that that's for one password so you don't want to be doing this when you have you know 100 passwords that you haven't found but when things really get bad you've gone through all your dictionaries and all your rules and all your permutations it's time for The Brute Force passor attch no questions everybody still asleep all right so rainbow tables rainbow tables are a time space tradeoff and it doesn't really work with salts but it works really really well for landman N Land man and md5 so with with the rainbow tables you can usually get 99 to 99.99% chance of
getting a password if it's in the so so a rainbow table it's going to say like all lowercase and number things up to 9 characters long and and it's going to be a big file but when you have the rainbow table and you run the software it's going to be a matter of seconds to find your password so this is not going to work with any modern Unix which is going to have you know 128 bits of salt but this is going to work great for all your windows systems it so so the guys at Defcon have the data duplication Village you give them a hard drive that's either 6 or8 terabytes and they load you up with
rainbow tables so go go buy yourself some hard drives load them up with rainbow tables and and start your hashing or your password hash cracking um it's an extraordinarily effective thing to do but again with salting you know with with the old DS script you'd have to have 4,000 times as big a file so instead of a terabyte hard drive you would need you know a 4,000 tab hard drive which probably doesn't exist anywhere yes why are they called rainbow team I don't know I does anybody know no but I believe that there was the early papers that talked about this technique they kind of explain I remember just like glancing through it and they explain why
they called it a ring yeah there's an economic paper from Philip bin who created sort of inventing the stuff uh so I can't remember the paper now but there is an academic paper explaining the concept so maybe you will find the answer in there but but it is it is a well accepted name and and I'm just I I don't know why it's called that I'm I'm sure some smart person had a good reason for it sure but but it it's just it's ridiculously fast um I had an old landman machine I think it was a Windows XP machine and it was like 30 seconds and it found all the passwords it was just ridiculously fast I mean it just
you know years versus seconds it it's not even funny um so here's some password statistics this is with my data dump of the 1500 passwords so we have the lengths most of them you know 49% R characters long there were a bunch of shorter ones then we have the character strings we have all lower case 60% it's a good amount and and we have a whole bunch a mix of stuff um we have different string classes I just thought this was a useful thing I don't see a lot of this being published with with this the password statistics so I I thought this was this was cool stuff um so so obviously if you're going to
start breaking password you're going to boot Force you're going to start with a lowercase because you got 60% of people doing that and it's all a game of statistics so now we get to the weird passwords so when people were using this stuff they were using they had big computers they had like VX 8 650s and stuff and people would tell net into this is days before SSH so if you type the password it would have to go through tnet unmolested so I had a tab character so there's there's standard character classes of uppercase and lower case and numbers and specials and all that stuff none of them have Taps so you have to make a custom word custom character set
and have a tab in it so I had a control character here oh so there's my custom character said so control characters I had a control R and there's another password thing I'm going to talk about later on that had a control W so the control characters were really quite vexing because I did a Brute Force attack and I didn't find the password I said well I've exhausted I've gone through everything how not be there the answer is some clever fellow put in a control R so if you want to make a password that's super hard to break put it into control character obviously you have to make sure it's going to be accepted by
whatever password tool you're using but I have never seen any standard rule list or any standard character list that has control characters in them has anybody ever seen that you have a question yeah so how prevalent is something like this it's not very prevalent so again I had one controlr one Tab and another very small password thing I had a control W but I decided I'm going to get all the passwords and you know you you do an exhaustive search say I've done everything you say what's wrong has has my computer broken and and the answer is no you're you're not looking the right place and the right place is some clever fellow put a
control AR there so I'm going to I'm going to get to the the rules about this I think to on the next slide all right so I asked the John the Ripper mailing list I said how can I do a substitution I'm sorry question yes no just to add something there in Unicode 15 say that again in Unicode 15 there are 150,000 characters that you can use as passwords including anything anything so DS Crypt Works basically with seven bit asky so this is very old school but in today world you have to worry about people doing all kinds of things with all kinds of different dictionaries which makes the words World much more complicated and difficult to deal with
including Emoji cons including what including emojis Emoji cons emojis oh yeah and and people keep making new emojies so that that's the difference between DS Crypt and and modern stuff I actually saw a paper of somebody that was looking into an iot camera currently like last week and the camera was using GS Crypt for its encryption and this is something you buy today so this is not completely dead some embedded people are still using this so this is this is not only of historical interest anyway so with John the Ripper I asked how can I insert a control character in in the first position the second position all the way up to the eighth position and
this is the m rule I can't explain what it does but it actually works and the second thing is how can I do a substitution of this so so the problem is if you do this with John the Ripper these are the two lines and and the first thing in the square bracket is the comment if you do this with hashcat you need 32 * 8 lines to get the same Rule now you can obviously generate those lines but it's going to be a lot more verbose than with John the Ripper but but hashcat can absolutely do this so this is what I use to find those control characters I use the insertion the substitution along with the rocky 2021
dictionary and you know in like 10 or 15 minutes it went through the whole dictionary all these permutations because there's 32 time8 permutations in there and that's how I found my password because these people that use these weird words one of the passwords was song birds the S was capitalized and the r was a control R the other password I'll get you later was chess whz with the w was a control R so they just substituted a principal ASI character for its equivalent lint control character so if I would have had to a Brute Force attack of all this stuff I'd probably still be doing this but these These are the rules I asked the John the
Ripper guys they gave me an answer it worked I found passwords so I was very very happy with that so now we get to the 1980 BSD Unix passord dump somewhere I think is on archive.org somebody found a bunch of BSD files including the password and these were these are live passwords so DS scrypt was deemed to be so secure that they made the password file World readable they didn't have Shadow password so anybody could read the password file so the way I found this password file I just read it I didn't do anything illegal immoral it was World readable I had World access I read it so the bstd password dump I don't know how it got out there
on the internet but it got on the internet and people cracked most of the password so was Bill Joy's password was chess whtz so the control W that that's the I'm sorry yeah control W that was his password and I'm sure he has better passwords by now Ken Thompson's password was this weird thing it's a chest Smo with the P's and the exclamation marks so yeah and and Steven Bourne's password was his last name I find that a lot I find I find that a lot I find that a lot so hashcat strips away all the information with the pastor fall and just has the hashes John the Ripper has some context like the person's name and the first thing it
tries is the guy stupid enough to use their you know first name or last name or something this happens it's a real thing I'm I'm just telling you what I found so here's a list I'm sorry well so here's the statistics on the BSD passwords and I think there was something like I don't know what like 20 passs and something in that rough neighborhood but it's interesting it say SS here's the actual passwords these are all of them um they were all found except the chess whz I actually broke that myself using the John the Ripper rule with the I I tried some Brute Force attacks which didn't work other people had done that too and then I tried the
one throwing in the control characters and because chess whiz was in some dictionary it did a substitution of a control W boom popped out so I found all the BSD passwords from this particular pass to dump um so how do you defend against this I mean if you can't defend against it you're screwed so two Factor authentications probably the best strongest way um so I have a Ubbi key I have a smart card you know if you have a cell phone there's fingerprints there's face ID there's a bunch of the cell phone guys want their phones to be secure whether it's Android or Apple stuff I know there's ways of getting around all that stuff but they're they're reasonably
secured it does act as second factor of authentication um you can use cryptographically strong password that's what I do so I generate passwords this this is the output of my password generator by default they're 20 characters long they have 129 bits of entropy obviously I don't memorize them I have a password manager but if if you have some tool that can break my 129 bits of cryptographically random passwords go for it um but but in in modern terms you need to have something that's cryptographically strong and random it's got to be long and you're probably not going to be able to memorize it may maybe you guys can memorize you know 10 or 20 of these things or a hundred of
these I I sure can't that's why I have a good password manager there's a bunch of ones out there I personally use key pass I don't trust anything that's stored in the cloud if it's stored in the cloud it's not your computer don't do that so with gpus you can actually undervolt them and underclock them and you can save roughly a third of the power to very good thing to do there's a tool called MSI afterburner it works very well uh it was developed by some guy in Russia so it hasn't been updated in a while because we got some political termo Russian folks but but it's a good tool they're probably tools on Linux
that do the same thing but you know if you're if you're saving a 30 ofe power bill that that's a that's a significant amount the other thing is your GPU will run cool which means it's going to last longer so it's a bit fussy because you have to iterate eventually things going to crash and you have to crank the voltage up a a little bit more but with within half an hour or less time than that you can get it running at a stable point or work and use a lot less power and this is a reference from the John the Ripper guys on some recent stuff that they did it's just one reference there's a billion references
out there for for password cracking and here's the dictionaries that I used and how big they are there's a lot of them um some of them are good so this this is not the size of the file that I downloaded off the internet this is the size of the file I downloaded then processed and I was using personally so the the file names I didn't change around except I had the dot dick at the end um there there are more password files out there they're probably better ones there are certainly a lot worse ones out there and that's it [Applause] questions hello that working yeah so I have a question sure um I've always thought that I could take my lousy
password and make an md5 hash and then use the hash as my password that way I can always recover it that's an idea okay um obviously if somebody knows what you're doing that that's not going to work too well so the thing is there with Comm and md5 hashes you can literally type cut and paste them into Google and it tell you the planex of your md5 hash but if somebody doesn't know what you're doing that sounds like a cool thing to do it it sounds kind of brittle I mean I wouldn't use it for you know nuclear missile Secrets or something but for your personal files sounds great all questions please yes so just to be clear uh you yourself use
this password generation uh tool and then you store your passwords in uh I forget the name of the Tool uh manager yeah you use a password manager and that's that's your strategy for that that is my personal strategy because look at these passwords maybe you can memorize one of them maybe you're a good guy if you want to have a different password for every place you log in which is a standard practice you know you're going to have 100 or 200 different passwords I can't memorize 100 or 200 of these and so that that's why I have cryptographically strong password and I just decided I'm going to go with 20 characters so the thing is when you
have something on on the internet let's say it's Facebook so you don't know what algorithm Facebook is using maybe they using something really strong maybe they're idiots and storing stuff in plain text so if you use the same password in Facebook as you're using for Gmail you know and one of them is using some bad algorithm or in plain text and people do store stuff in PL text you know if your Facebook account gets compromised I'm just using them as an example I don't think they're storing stuff in plain text then you're really screwed but if every account has a unique password only that one account gets screwed if they have a data breach or bad things happen or they have an
Insider that's you know doing bad stuff so you're you're limiting your exposure by having a unique password for every different thing you're logging into yeah we had Jeremy Gosney uh here two years ago doing a a lightning talk uh about password stuff he's the guy who have been helping me out organize uh pastor G have for many years uh and in his lightning talk two years ago he talks about you know well reasons for why you know password strength and your password doesn't really matter that much because there are a million One problems in the world regarding passwords and where you use them how you use them and so on and he said that well you don't know how
different services are storing your password they might just as well be storing them in plain text and you don't know if their administrators will get uh uh compromised and through that they will be able to extract password hashes and so on so Jeremy gsy made actually a point out of the fact that maybe the most important thing you can do is to use absolutely unique passwords for every single service so that if one service gets compromised there's no way they can reuse that password to gain access to other accounts but if your password is really short if it's really long doesn't really matter because you do not know how they store your password as an example which is a pretty good
point and I made a small interview with him that you can also find on the YouTube channel for pastor Scot so it's worth listening to that one as an example because he has many good points in that one there have been real breaches where people store passwords in plane text y I mean and and some ones they use md5 summer they use something really weak so you you want to think everybody is doing something super awesome and probably 2third of them are but probably a third of them aren't and you don't want to get SW swept up you know by some bad person or bad actor compromised system and use the same password in different places
plus one of them might actually be used in something important and that would really suck but you also said Jeff uh you know you found that there was one password in in in that dump that you cracked yourself with the control R character the the chess whz yeah and then you mentioned something about you know cracking passwords for as a hobby and you spent five years on this stuff and and you said also something about not having a life uh um so I I'm really curious about you know how did you come up of with the idea of testing control characters and so on how did come I had done a Brute Force attack yeah you tried everything
upper case lower numbers special and and the tab and I didn't find the password Y and I said okay I've done my job my my my computer works pretty well well I didn't find the password therefore the password must contain something I haven't tested for and I said maybe it's when OT used a tab maybe somebody's using some control characters yeah and and the and these were desk scripts so they were probably no there most probably there were no emojis in there so yeah you can leave that one still seven bit aski so I had another program I wrote which basically transformed 8bit aski down to 7 bit aski or it would like you know prun Out Lines it had 8 bit
asky in them because I didn't even care about if if a file had something or a line had something with the first bit set I said this is not something I care about obviously you care about that today but for my purposes in D script I didn't care about it yeah any more questions got a
question uh I I guess this is two questions one why do you trust keypass more than the others besides just cloud computing and two uh Windows doesn't you said Windows doesn't use salt does it does it use something else to store the passwords uh more encrypted I believe I believe it it just uses NT landman that I I haven't been breaking Windows passwords lately but my understanding it's using n lman today do anybody yeah okay so an expert says that's how it's done so so why do I trust keypass well firstly I don't trust anything in the cloud because if it's in the cloud who who knows who's doing what to it last pass last pass that that's obviously a
good counter example but you know something that's relatively straightforward something that's open source I probably could write my own if I really wanted to so so these password managers they've got a master password so you memorize your master password it's you know password not1 123 or whatever it is something hopefully stronger than that and once you have that then it basically you can see all of your real passwords and hopefully you can cut and paste them into whatever applications you need and when you're done you close the program and hopefully whatever it store gets randomized in memory so it's stuff's no longer there there probably other programs I use ke house other good programs there's lots
of other programs first of all um why do you have to bring up BSD logs again I thought that was behind us but anyways um but what me what made me think about the BSD thing is so I was guessing last names back then so obviously there's tools and I I didn't want to bring up AI at this conference but like I'm sure there's things scraping the internet scraping social media so they can actually start using our dogs names our children's names so without naming a tool those toar okay right yeah so it just feeds a dictionary so so every dog's name every spouse's name every birthday every you know common word found in Wikipedia is
probably in some dictionary but look look at Denny's Denny Richie's password the one with the chess move in it the the P SL whatever it it's some cool chess move that's not going to be any dictionary I mean it will now but at the time it's it's not in any dictionary so so he he picked something cool that he could memorize that was hard to guess and and realistically you're probably going to have to Bri Force attack to get that password and that's how people got these things way back in 2018 I did Pastor Con in Stockholm in Sweden and I had one speaker from South Africa uh speaking there and he had done a pretty cool
experiment uh he looked at sort of like the top 100 most popular common passwords found on the internet which is you know that easy passwords you shouldn't use them but he had a fascinating idea he looked at those and most of them are like English names or words and he was looking into local languages that you have inide Africa or Southern parts of Africa and he looked for translations of these English words into like Swahili or other languages that they have in South Africa and for those words or names where he actually found a a translation he wrote it out in Swahili and then he hashed that Swahili word with md5 no salt and he gave those
hashes out to a bunch of passord crackers and he said here's a bunch of md5 hashes unsalted you will have extreme cracking speeds with these and these passwords are incredibly easy they are very very simple passwords and nobody were able to crack any of them because who's got a Swahili word list right or who know Swahili so he said that as you know a sort of like a recommendation whatever you do at least do not not use English names or words as your password because the majority of sort of our experience in cracking passwords is really centered on Western alphabet English or other languages that are using uh Western alphabet a to c as an example I'm
Norwegian we have 29 characters in our alphabet we have three more letters than us English as an example but if you can do this in kilic or in Greek or Arabic for that matter you can make very easy passwords that will be incredibly hard to crack because again the majority of academic research and hacker research is really focusing on a Toc English words so if you want to do a good password do it in Russian but there are dictionaries for different languages they they are far less mature than English yeah but there's shic dictionaries in Chinese dictionaries and probably so you will only be a little bit ahead of yeah the current status Crow yeah any more
questions for Jeff no more questions then thank you oh okay one more last one so so this kind of a little silly question but I was just curious if we have MFA enabled uh on anything can we really just go with the most stupid password you know abc123 because all the strength really rest Ona they did that with secure ID in in two three or four they really regretted that so the RSA algorithm got compromis I don't know how it got compromised maybe it was an Insider maybe it was a nation state but these these little six character token things they got compromised so I I wouldn't say that you need to have 20 character
cryptographically strong passwords but but you should have something that's appropriate for what you're protecting if it's your cat videos use a four character password if if it's your financial stuff you probably want to have something stronger if it's nation state secrets you probably want to have something that's really really strong you have you have to use passwords that are commensurate with the level of thing you want to protect yeah I I was telling him that I I have a uh smart ups and to log in the UPS you need a username and password so it's only on my land you know you don't need anything smart for it I used to use a four character username and a four
character password but now now require something strong hunger it's a waste of time it's my UPS if you're not on my land you can't see it so it it it's pointless to have that security in my opinion but not all UPS's are on my land some UPS's are World readable so maybe you know it's a good idea to have stronger passwords for those UPS you can turn computers off that way but my use case it's silly okay thank you Jeff [Music]





