CG - Understanding, Abusing and Monitoring AWS AppStream 2.0
Show transcript [en]
good morning and welcome to b-sides las vegas common grounds this talk is understanding and using and monitoring aws app stream 2.0 given by rodrigo montoro from tempest security a few announcements before we begin we'd like to thank our sponsors especially our diamond sponsors lastpass and palo alto networks and our gold sponsors amazon flextrac and google it's their support along with other sponsors donors and volunteers that make this event possible these talks are being streamed streamed live and as a courtesy to our speakers and audience we ask that you check to make sure your cell phones are set silent if you have a question use the audience microphone that i'm holding to so that way youtube can hear you
now as a reminder the b-side las vegas photo policy prohibits taking pictures without the explicit permission of everyone in the frame these talks are being recorded and will be available on youtube in the future and we would like to you to please keep your masks on at all times all right all right so first thanks besides for having me here um i'm going to talk about understanding abusing and monitoring upstream if you look like the monitor is in bold and so like my main goal is the monitoring part but to do the monitor part i need to do the offensive part right but my main goal is to to to find the monitor parts uh
my name is rodrigo i'm spooker labs i do research interactive texture engineer at tempest security in brazil and i live in the south of brazil it's a beautiful place if you want to visit brazil florianopolis is an island so it's pretty good to be there a proud dad and her husband in my spare time i do a lot of sports i used to do iron man but if you could look for me like i'm not doing anymore like too big for that and my twitter handle is spooker and the motivation about that it started when we a company called tempest about an incident response that was happening and they they told us like we got owned by a apps string instance
that we used to have a administrator access role attach it and so when i was in the car my first stuff was like what is that stream like that time i have never heard before and my second thought was like if that company was our security operations center company would you would you detect that and the answer was no and so as i figure out oops i think you need to start to improve our detections and with that in mind uh i started to study a bit about app stream and talk with an uh with a shish from call secure podcast and we start thinking like maybe it's time to try to do some uncommon thread this detection response
for aws for uncommon service because like we have a lot of works like for ec2 instance s3 rds and lambda and more common service and when i talk about the aws service we have around 300 servers and so there is a lot of room and a lot of opportunities for the attackers and so as a defensive guy i started figuring out okay and so this talk this research is a kind of proof of concept like what we should do with uncommon service or service that you have in our environment but we're not monitored by some reason and and and and and show like what we have there a lot of opportunities that you have here
and how we could try to detect or maybe mitigate or or improve our security so i did a a very brief agenda so introduction app stream right um some recon attack flow like the way that i built this research and as i said like i'm a defensive guy and so like i'm not the maybe there is another way to do the attacks but i'm just based on my basic scenarios and so some scenarios are boosting some parts like this is not about finding vulnerabilities at the service it's about using the service and the features right and so the the important part for me like since i i do try the detection engineer like the monitoring detection
mitigate and some future work and conclusions so introduction through app stream so what is app stream i i i got a couple of words and and and message from the the documentation so it's a desktop application for anywhere so anywhere means like anyone could get inside that or use that like the applications run inside your vpc and subnets so that's cool like i could put some application maybe some legacy application into my my my cloud environment and i have access to the vipsy and the subnet so you're attached to that but look on the attacks attacker sider attack site what what what's the problem like lateral movement so i could get inside break the perimeter and get network
access and so x data and research that you have in your account and so that's pretty cool because i have a legacy application that needs to connect to my rds by some reason and so it's there i could connect to the rds so i attached a row that has permission through rds and like this is pretty cool but in this the view of the the attacker it's pretty good too because if i break that i could access that in resource right integrate with your active directors like pen testers loads active directors because you always have a problem right gpu processing so we have good processing there like maybe the crypto mining guys we would love to have some
access and so how does it works like you basically you have a builder part and install your windows or linux or what you need you build your operation all this stuff you need and you you create the users you create the instance and so the user will have access to that application or this os like a better image like it's from a presentation from amazon like so basically you have the image builder parts so you could they have some pre-built applications but you could just install windows and do what you need to create application and so after you you work here everything red you go to the snapshot and it will go to the image
headers and so you could add to the fleet and so fleet is where you you do some out scaling like you could do like the things so the user will always have that application uh red and so the user will connect the fleet and you have the stack part that you could do some prestan's data cloud star use s3 and because when you access you do your things and so the the instance is terminated so you don't have first test data and so you have this opportunity here most of my research of this proof of content i'm not i didn't get all the the steps here already mostly i'm i'm i'm talking about the image builder only and the image i have
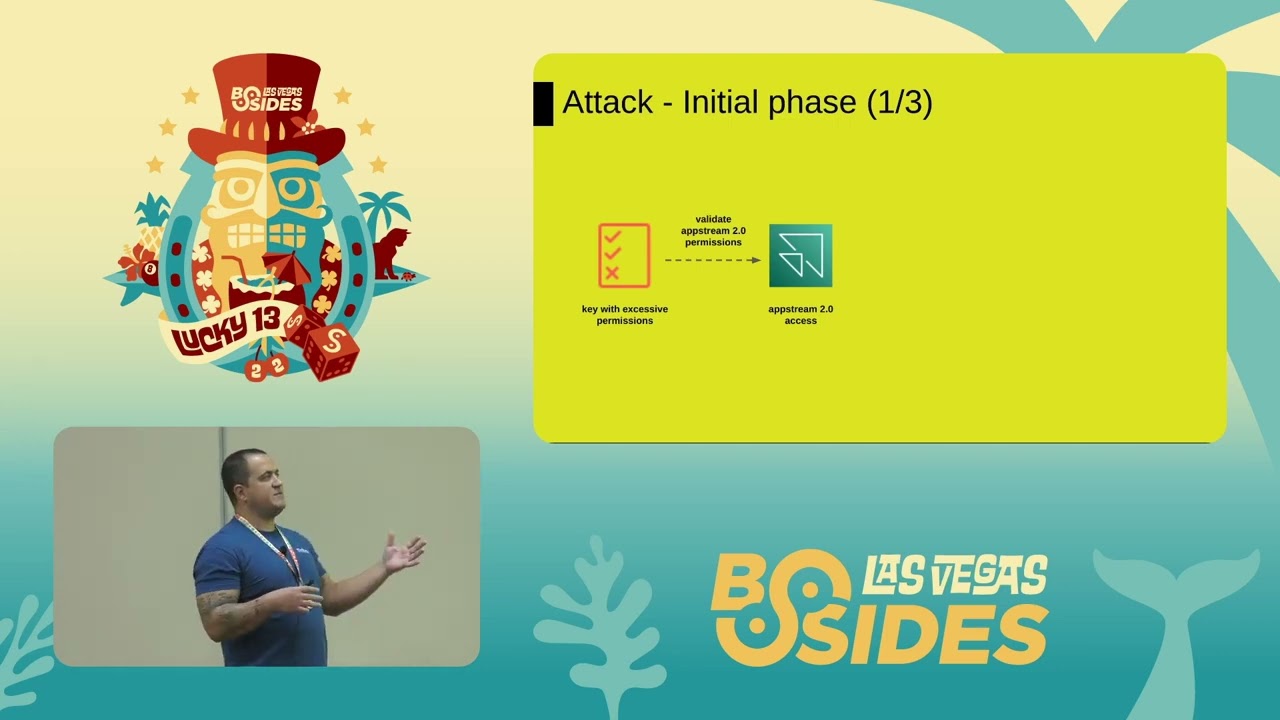
a bunch of stuff to do here and even if i i had the time to do all the stuffs i probably could not have time to speak about all the stuff because it would be so long and so how it works how my idea worked how in my mind like how i would build this recon and how it's going to work and so we'll have the initial phase so first what do you need we need to see if you have access should the actions relate to that to that service like uh over permissive policy is not a problem at aws like most of the time they have that they they do administrator stuff and so probably you you find some some
some permissions here after that as i validate those permissions i show each permission you're going to need i have access type string right and when i have access wrap string to do some steps that i'm going to show later i need to do some enumeration about the app stream itself because you have some information there and about the general aws because you need to to know the the vpcs the subnets if you have some role that could be used with the app stream service and this this kind of thing and so i'll do the app stream enumeration and the general aws enumeration and on the side of general aws enumeration i i i would try to say like since i'm
going to get inside the vpc i i would figure out like which vpc i want do they have like transgator direct connect and so i could figure out like how far it could go like maybe you could go for an app stream throw on premise and and do what what do you need so supernat security groups and this very important part like rules that have thrusted paulus for app stream so the app string when you you created the image you could build the image with that row and the app stream part i will see like the the image that they have are right there the image no aws image like when you have no aws image probably something
you created and there you have some information from the company maybe something you want the fleet and stacks and and the builder image and the fleet part i'm not going to talk about the fleet part but the builder image they have the the the possibility about attacher row right and so when you can attach a roll or pass the roll that means that something could be much dangerous right when you have right uh permissions to this and personal storage and so it's it's a bit part of the the actions that we need like i i split here like image builder the part the image the fleet and the stack as i mentioned i'm mostly talk
about image builder and i will mention image part because there is some easy stuff to do with that that is interesting and so the the verb first the privileged collision there is three three ways to have privileged collision uh the very first one like if you have a exist existing builder image with a role already running like someone is working right with a role and testing and doing stuff you just need app stream create image builder stream url i will show what this means and with this this section you guys are url and you type their url in your browser you get inside the machine as root and you could assume the role that is running with
that and so depends on the combination of the facts with just this you could do the privilege collision if maybe you have some builder image there with a rule associated but that role that that instance is not running you stop it and so you you need the start image builder too and so you start the image and so after that you create the builder screen url and with that you access the machine and the the the most like common part like the most privileged collection for sure right you have the pedro and you have the app string create image builder and so you create the image builder you attach the the row and you have the
access to the machine and you could use that row i i have a lot of scenarios i have some live not live gmail or record demo showing like part of this and so we have the first tense part right and so with create image builder and are using uh a a builder image that's there like you could create an image builder but you don't need the press roll so it just creates and you have a machine inside the vip c and the subnet and what what and when i'm talking about prestons that come to my mind like what's the problem with upstream on the detection side we don't have detection mostly and so if they don't have
detection this kind of for instance we probably will be there forever because if i'm not looking for this kind of actions they will create that like if they don't create some large machine like to be like just a few bucks that you'll never notice and the person's parts is really interesting and you could have a presence with a privilege collision with your role attaches and so and so some that's filtration and resource exposure like when you have the create image builder streaming like if they have something there you just create the the string url and you have access to the machine and that's it and and and if they have applications secrets something encoded or hired coded on the
code do you have access and the same lateral movement you could create an image builder as i mentioned and that's the part that i mentioned here sharon on arsenal too and what is this there is this permission app string update image permission and as i mentioned you go to the the builder part and you create your your own image you could create a good image for a good purpose or you could create a malicious image like oh this image i have all my tool set and now this this stuff and this stuff is on my account i create the image on my account and what i could do i could share that image with your
account right and when i share this image with your account i will do all my account update image permissions and this this image will appear as in your account and you you don't need to allow that it will appear right and so if i have a create image builder and i i have i i create something malicious i cr i can create an image builder with my own image and the fun part is it's when you're sharing your image you that decides that they they could use on the fleet and on the the the builder part and not the the target account and so this kind of thing it is something that for attacker for a crypto mining that
could be a problem because i could just create an image like with all the the mine stuff and so i just start that image and okay it's probably triggered like something quickly but in another point with this update image permissions you have in your account the your your application running that you're providing and so i could share that image with my account and so in my account i create the image builder and i have access to the content inside there and this kind of impacts that you're going to have like data leak network access that could like just the cloud part or maybe as i mentioned you could have the direct connection and people to
the to the to the on-premise you could do crypto mine data destruction research for a deck mass user infection i'm not talking here exactly about the mass user infection but the the person's data for the users could be s3 and so i could have access to the s3 and modify something and like when the user access they will have some surprise right and so some scenarios that just drink some water quickly
and so first enumeration as i mentioned that it's pretty hard to have some enumeration because you probably need some some some some part of this that's information and and so the the first part i i make sure that i have access right to those actions and so in this case i just have the create image builder i list their roles with apps to interest policy until i have these threes operate units right and so i don't know which one has more capabilities but i could check and the existing builder image so you have like those four here i'll stop it oh and the good points here when you have a roll attached it will show the role so
if i have like to choose something here i'll probably try to use something that has a whole roll attached so i could do a lot of more things and so i'm mapping the security groups because another way to just to to have access you could do ssh to that image or you could do something uh i reverse uh reverse shell and so i will map the security group that probably has more parts allowed and so like i i'll do my life easier because maybe i can create an image and so instead of i keep access the control the control plane and and have access i could just make sure that i have a security group
that allow me to to get inside that machine and so i add my my key there and i do just network traffic and so probably you're not going to notice and so listing souvenirs and so the souvenirs and the eyepiece and so like when i'm doing the paint testing the guys are doing what they need they this kind of information is pretty important so those informations together will allow me to do a lot of things and so first the image builder part a resource exposure and so uh all those demos are based that i have read only plus the specific action right so i could i could do something and so i have app stream create image
builder here i i i know that this result research v2 is running so i basically do app stream create the image builder stream url the name of the of the the builder image and so it will generate this url and anyone that typed this url in the browser it will open the shop there is no no there is there isn't an extra authentication on our extra need and a curious part like if like five guys use the same url like you see each other typing is a kind of google drive like for for a desktop and so when you put this in the the browser rail you are getting inside a machine like if they if you
have like in this case i don't have a roll attached and so i could not try to devote to the to the contour plane but but i i have access to i'm inside the vipsy and the subnet so i could try to do some lateral movement use the network part and so i could create an image to do that the same right and so i'm just using here to to show like you create image builder you put some name is you choose the instance type like there is some large instance if they going to have uh default internet access the iron of the image you want to use like there is like i think by default
third image there are different options and so those information that i i i mapped before like the vpc config the subnet ids and security group ids and so i probably use like the subnet the subnet if i know the ip that i i want to to to achieve it's easier to choose the subnets and the security group as i told before like as more parts open they have better it is right and so with this i could get inside and try to do my things and that's image iron it's that part like if i share my image with the the the target account i could use my image iron here and it will be my own my
pre-built tool and so a privileged collision sample i i need the create image builder and press roll and the biggest difference between the other command and this is that i have the i am roll iron that will be the password and i i will need i will need to try to specify a a rule here and and i roll that i i have the trusted policy and so that's why the enumeration is very important if if you drop my mayo could send you the codes like the code is nothing than a cli with jq like you're doing some pricing there is nothing nothing different from that and so when you run and if you show that you have the i am
really iron with the ar the the rule that you specified right and so that's the very first step the second step i will create image builder url right and with the same name research v3 research v3 and i will access and the biggest difference like now they it's generated aws.config the config has this command inside and if you run that command you have the the keys the keys that you could configure in your machine right and i didn't test somebody asking and but i didn't have time to test like if guard dirty is going to trigger that because i know that where that has now some some new detections that if you have a rule
attached with an instance if you pick that role by some reason and use outside or use it in another account it's going to trigger and so i didn't test that but you can use right and so this permission uh because it is a profile app stream machine role right the app stream machine role the profile if you want to use the aws cli from this this shell and you you could use and like it depends like probably what's happened with that customer because i was just on the call but it didn't finish like but just opened my mind and and probably like someone get this and grab the keys and do especially like if it is
administrator access like game over right and so it starts uh existing image as i mentioned like you have running and running and so i probably i would prefer something that i have a road right and so i just start image builder and the name of the of the the machine the image builder and so here a quick demo and so i i just run that bunch of bunch of app streaming and so i i will show like oh i have created builder allow it here is the app stream trust police that i have so i could choose any of that and here i have uh machines and just one running with a app so with only this permission i could try
to to use this and so what i did is i just tried to create the app stream image builder url to that instance running it will create the url and you go to your web browser and you paste and boom that's it you're inside the machine that's pretty simple and that's pretty scary and sometimes at the same time and you have the the full user that runs and you have the the app stream machine role that you just type that command and you have the the access to the key and so you could try to figure out what's going on and besides that you have access to the network the subnet and so with that
you could it could do whatever you want internally and so when i i did all these research like those opportunities and those things i i started figure out okay i have those opportunities maybe there is another way to do the same thing but by the end of the day the cloud trail logs will be the same right and so i start okay now the parts that i really want and so it's not our offensive the idea here is to make blue team great again right so try to to do something more proactive because most of the textions that we created is based on someone else's research like that the attackers go there they do that and do
that and we are incidentally responder or the text engineers okay now we have to create a detection for them my goal here is like okay let's create a detection before someone i read try to do that are they abusing that maybe i don't know i don't think so but maybe they are because since we don't have detection right we don't know so basically what i'm trying to look in here like from the create image builder stream url the app stream start the image builder they create image builder and they update image permissions and the key point like talking about monitoring detection like you need to have the detections like you need to have the visibility like since you have
cloud trail logs and going to somewhere else you have the visibility but you need to have the triggers the detection and so the detections we are creating here and maybe you have another information to do the incident response and so part of the problem try to find like okay i triggered that the because of some event some action here but we only have all that the information that i need and so i i tried to to do something and so basically create image builders through url uh we have the request parameters and the url is high due to security reasons makes sense right if you're not attacker just look up the cloud trails and you should have access
to the url and use their url right and so if you don't use it any create image builder streamer are always dangerous so if you have like this you're using app stream your company sony take care maybe you could monitor the search ip but the create stream url there is not much room for specific detections but when i talked about the crate image builder so you have more more information there so you have the iam roll yarn and and this cool like because when you have the the event name that has the request parameter i am really earned is where they pass the rule is happening and because the pass rule is not logged that's that's set but it's not logged
and so this kind of event that we detect past the rule happens happening somewhere uh the vps and so you could like make sure that the the rule that's going to be used like for this kind of create image builder maybe something different maybe it's not supposed to use the role uh the vpc part like maybe they are putting their own subnets it's not supposed to go to this subnet how the the image builder should go through a specific subnet a specific security group and so and by the end like the image iron and if the the full internet access and so here you have a bunch of opportunities to create detections and they start image builder like mostly you
have the search ip address and the name of the the image but as i said like if you don't user is not supposed to user the app stream your company like any action is supposed to be malicious because it's not supposed to be happening and the update image permission the update image permission you have some room here because as i mentioned like a low fleet and a low image builder like you that ex specify what the target account could do right and the shared account like here i have a shared account here and you could maybe have a white list of shared accounts that you're allowed to share by some reason and so you could create a kind of allow
list and some incident problems that i detect like when i create a user besides search ip and user agent use aws internal and all the parameters i he didn't do security reasons so like it's it's it's terrible that like especially like when you need to do incidental response like how i know the user that what or what's created here because like for me it was pretty easy like i have the create user parts here and the email address because how it works like i'm not going to get in deep in that but like you create a user pool you add the user and the user receive email with their url and the user and pass
so he probably needs to use some email address that's not part of the company right and so if i i at least have the mma or address i could just just create a detection like if create user has event name and some email address different for my domain that's a good a good detection but like if you have this kind of problem you probably need to go to the api list of the users you have there and compare like with which ones the new one is the different so it's important like just to be ready right that's that that's the point because when these things happen you need to you start to scratch the information try to
to to to find what's going on and if you don't have that information like at least you know that you need to go somewhere else to have that information and another fun part that's happened here we have the this this the web console and the web console and here you have the the cli right but the web console the visibility is shared with others because we have the accounts here being shared right and so i figure out okay i will create a cs pen detection use the because i was supposed to go to create for a prowler and the product that time is using the cli but when i go to cli the visibility show lies private
so like there is some mismatch here and so i talked to aws guys and they open internal tickets to fix that like because the information is not i don't know how to say but the information is not equal because it's very important to show like it's shared because maybe you're not supposed to be shared and so like if it's shared that's a problem already so there's a kind of problem that we detect and that's being said some grad derails and if you don't need to use app stream then i have stream right but it's going to save my my account or environment where as i mentioned we're talk like for something around 300 servers you're being protect for one but
probably there is a lot of more room for attackers and so what in my opinion what you should do like allow only service you use like the most important service create a scp like if the services are not those 10 12 30 something else deny and if you need to use app stream like depth screen right actions and make sure that they have condition i i i like to say that ip search conditionals ip source address pretty cool because like okay the the the key liquid but i need to to have access to something else and maybe you have a bastion hold or something like that and monitor configuration with cs pen too because sometimes
it could help and future work and conclusions uh maybe explore more fleet and stack as i mentioned i'm on the image the image builder part and a bit on the the image part they were used uh it should have to boost the person's data so maybe there is more opportunities there and stood more about the user pulling in the integrations create some sigma rules so i think it would be pretty interesting like create sigma rules and anyone could use the those detections oh add to paco framework right they they have like 22 privilege collation stuff maybe we could add more and so when we're doing some some testing we probably could attack and maybe create a closed scenario so we could
simulate and see how it works and my as i mentioned my main idea is to create an accidental response you cheat for oncomo aws service and when i am talking about like creating this is it's something like that the main idea is like to try to create an incident response plan that you are ready ready right and so know the service you you have no the service you you have no idea like what how they worked and like create detections understand what could go wrong and this kind of thing but you have 300 service right and so like the idea is to create something crowd sources because i would probably look at this because some companies
customers have that and so someone some someone i also will look for something different and some conclusions deny what you don't need remove builder image you don't need right because like some problems that i i i mentioned there i i need to have an image builder a red built like and running and so if you have no image builder there like i need more more privilege and so if you need to keep doing something by some reason stop at least so i need two actions instead of one like use condition as i mentioned already understand and study service you use and most important part if you have some service running in your environment make sure you have some detection like like
some understand like at least go for example for the emrk like permissions.cloud for aws pick the rights and maybe the the management actions about that service and try to see what you how they works on if something logged already or as i used to do like start to clicking everything and see what's going on what's being generated and this kind of thing i think i speak like okay third five thirty six minutes and that's it thank you very much [Applause]





