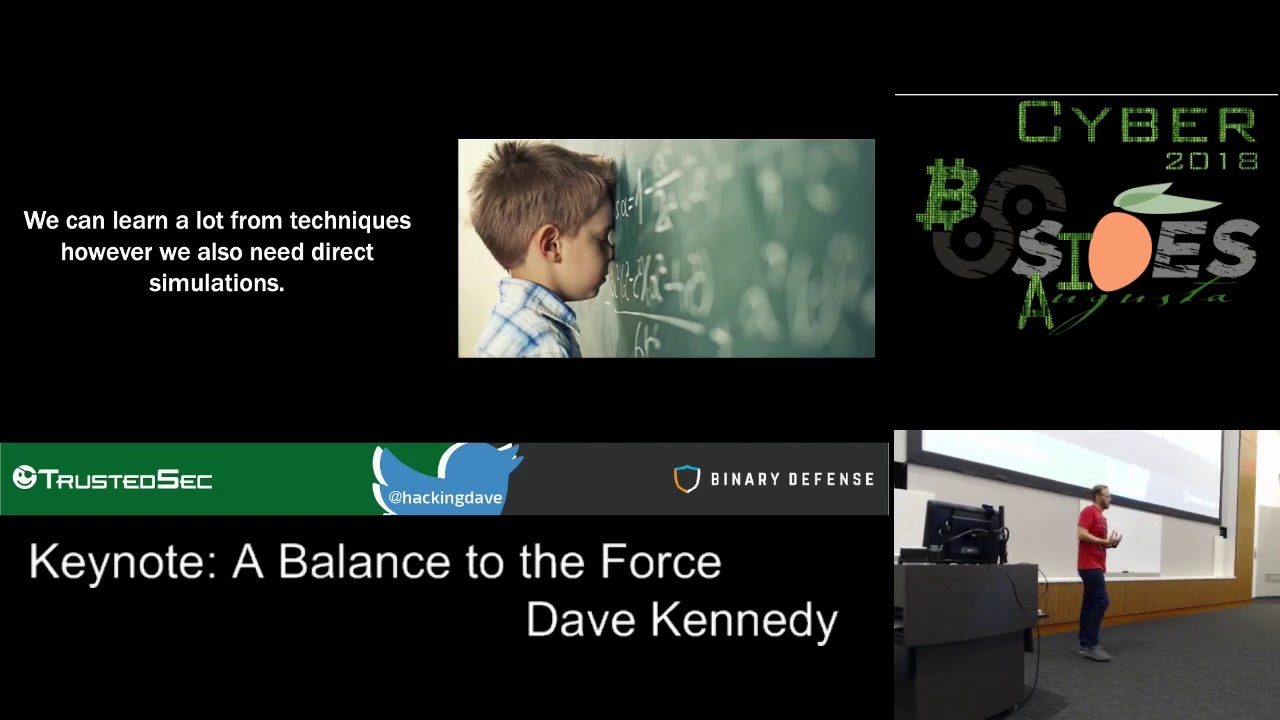
Keynote: David Kennedy
Show transcript [en]
ladies and gentlemen please join me and welcoming the co-founder of trusted security the co-founder of binary defense and the co-founder of Derby con mr. Dave Kennedy
nobody hear me okay good great well thank you everybody for for besets Augusta coming up super early in the morning I got an email last night saying hey can you be here by 8:00 a.m. I'm like oh man like I like to sleep in and all that good stuff so I see people drinking coffee and everything else I'm two coffee cups in so I should be okay for the rest of the presentation after that I plan on sleeping but I really appreciate everybody coming out today to hear me talk and I really like this talk because it's it's talking about a lot of things that we struggle with today and I'm gonna dive down into a lot of the
different types of technologies that are out there that stop attackers and really how effective they are and what they do but really today's talk is is looking at how do we get better with with identifying attacks and in the earlier stages and there's a lot of Technology out there like artificial intelligence and machine learning that we hear out there today that tell us a lot of success rates when it comes to what's actually happening out there so I wanted to dive down into some of those technologies and take a look at how affect that they are what they really do and really we can do to get a little bit better with with what we're doing but
first I'm gonna says give a round applause again for everybody that makes besides Augusta possible it's amazing what they're able to do after using the funds to fund stem and be able to help kids learn and get more folks into technology in general and that's so so so important with what we're dealing with in the shortage that we have in information security just a brief background of myself as I got introduced earlier a co-founder of Derby con started trusted second binary offense I'm the author of the social engineer toolkit unicorn artillery number of other open source frameworks the pentesters framework like writing code when I when I have spare time so it's been been a lot of fun on the
information security space funny enough I was doing a presentation in Chile for four is C squared and and I started playing a lot of my videos like it was more of a higher-level talk and I started playing all my videos and I realized that every video that I'm in I had the same suit on because I only own one suit and and so like everyone that I was in I was like oh no I need to change that how cuz like I don't like suicide just like you know when I fly and I'm like a sweats type of person and you know I'm that type of person and suddenly really own one soon I really
like that tie but even big day when I was heavyset had the same tie that was interesting also I've been in a rap video I thought that was pretty cool as well in a Chris Brown rap video which never thought I'd be in a rap video before more of like a 90s grunge alternative but it's all cool like it was kind of neat I flew out to LA and they wanted to do like a real live skit on a hacking video and so I'm like okay so I created a head an Android device and the whole purpose of the the video was basically Chris Brown and another rapper Zoe dollars wanted to hack into their their ex-girlfriends
phone and delete all the pictures of them it's called post and delete it's not safe for work by the way so don't watch it when you're at work and so the whole premise was is that you know they wanted to lead all the Facebook posts and things of them together so they hired their best friend hacker Dave to come in and so I actually created all the the code in the background and you stage-fright to trigger an exploit on the Android device and then delete all the phone delete all the stuff of its they really wanted like an acro portrayal that's been really cool steam thing for like for mr. Roboto I've gotten helped out a little bit with that
TV Joe and a few other things so it's been really neat to do a lot of the cool stuff out there and and being a rap video which is like I said the only prerequisite of me helping out the rap video is is I have to be in the rap video and I like will figure that out so that's me for like a half a second in a background like bobbing my head as I'm hacking into computer systems as people are dancing behind me but it was really weird it's awkward like it's like picture of me on a computer and there's like 15 dancers behind me like doing flips and stuff and I'm like literally
just typing on a keyboard it was the weirdest thing ever but it's fun that's fun so a balance to the force the reason why I started this that this talk is we have a lot of problems when it comes to being able to respond effectively to specific threats against our organization and the reason I bring this up is that protection versus detection protection and most organizations takes a long time doesn't it to implement application whitelisting is anybody successfully implemented an application whitelisting and high integrity mode with very little exceptions right right has anybody gotten rid of macros so there might be a couple in here anybody got rid of macros in their environment nope not one right
so we have a lot of things that it takes us time to get towards to really build out our infrastructure network segmentation do we do network segmentation extremely well do we do DLP very well all of these programs that take a lot of effort in time for us to implement and we're always striving to get better at it right it's so protection is something that takes a long time right a good example let's just say a new attack vector comes out today and you can fix it with a registry key change can you make a registry key change across your entire enterprise within the first day comes out maybe maybe not depending on its impact
testing everything else that's happening out there without a patch you get that patch out the same day across your entire enterprise probably not right so we have a little bit of work to do when it comes to the time it takes for an attack to come out to when we can actually protect against that and the same thing goes for our strategic type of protections right network access control or network segmentation or DLP or application whitelisting or rolling out an old antivirus with the new antivirus right that takes a lot of time for us to go and effectively do so what we try to do in the security industry now is augment that protection piece with the ability to to have
detection in place so that we can minimize the damage to our organization and hopefully respond we don't care robbing sales gets compromised I mean we do but we don't really care right it's better than our entire IT infrastructure being owned and then having access to all the data so can we minimize the time it takes to detect those attacks and then respond effectively and so for us the major concern right now is protection equals timing and in most enterprises it takes a substantial amount of time we're not Andamanese this word sorry but we're not agile the same way we do in development to be able to implement sweeping changes across your enterprise to be able to do things and
so then we focused on the tactics techniques and procedures of attackers and that's the big buzzword right now right TTP's TTP HTTP so here at about 400 times in this talk and I'm doing it intentionally the tactics techniques and procedures of attackers are what attackers leverage in order to compromise an organization or and the methods that they used to do it and the ways that they operate so everything from standing up or operational infrastructure or using a high reputation sites using domain fronting doing a specific type of code injection attack to get code execution on the system these are the methods that attackers operate by in order to compromise their infrastructure and the big big thing that's focus focusing on
right now are what are the techniques that attackers use that we can build detection criteria off of it ie the mitre attack framework and a lot of other things that we see out there today right so trying to get an understanding around what attackers are doing so we can build defenses against it now I thought a really good comment from Jeff Moss at the opening comments around blackhat with hit home with me which was we as an industry don't focus on the tactics or the procedures of attackers were only seldomly focusing or only focusing on the techniques and that's really where the industry is at today we're focusing very very myopically on the techniques in an attacker uses
what's the command that they use for wmic what does MSHDA look like when it's beaconing out to the Internet let's focus on the technique and let's build detection criteria off of it and we don't necessarily focus on what the patterns of behavior look like or the procedures that attackers use in order to compromise an infrastructure so today what we're really looking at is that we're using signature based detection on techniques so we're basically the antivirus of the 90s and that's where our security programs are today so we're essentially writing signatures for commands that look malicious but if we modify them in some way shape or form or we use a method that hasn't been discovered we're fine
no problems as an attack goes so we're still really back in the 90s which is a good year at good years I love the 90s is my favorite time got arcade games Super Nintendo and he had 90s grunge you know I was friends came out the 90s right friends was a good show Seinfeld nineties are the best so we can learn a lot from from the techniques of attacks we can say okay well if we trigger a specific type of attack vector can we detect it great that's fantastic now you have maybe 50% of the coverage out there but do you really know how effective those detection criterias are unless you're doing something like simulations
like red teaming or very specific attacks that are very applicable and practical to your environment as you're actively going in and testing them and so the current state of detection and I love this an example I wrote I wrote this tool in 2012 so six years ago right six years ago I wrote a binary dropper so it's a binary non code signed executable and it was just a basic native HTTP shell and it incorporated AES for the command control so basically you know you you you trigger an executable on a machine it beacons out via HTTP or HTTPS to the epoch attacker sites and then it communicates with command controls like a basically command Sheldrake do IP config you do
things like that but it leveraged it over AES so I released a source code and I published the binaries okay and since I since 2012 I've had 3.4 million downloads of this specific binary okay so really good download rate I would say all right 3.4 million seems pretty pretty sweet and so I decided to upload it to virustotal to see how well it was detected on code signed binary out in the wild public code six out of six out of sixty found it and guess how many of those were by the way were the next generation product lines zero zero zero zero point zero like McAfee found it I think claim maybe did which I was really
surprised that I didn't know that was still around I was like shoot claim he found it whoa semantic a couple other ones great but six out of sixty found enough funny enough I tweeted this out and guess somebody found it after that 37 out of 60 magic right it's amazing what you can do by a tweets that's exactly what attackers are doing by the way when they when they write some custom code that isn't getting getting detected they tweet it out to all the antivirus vendors as a challenge that's exactly what they do shrubs see - I wrote Trevor see - which was a command control structure for basically it's it you can use it you can
bet it in documents from macro injection you could use it as a PowerShell stager I also has a c-sharp stager and what Trevor c2 is and you can go and download today is it's a command and control infrastructure and exploitation framework for command and control and basically with Trevor c2 what it does is it beacons out via HTTP and you can use the PowerShell stager there's a Python stager and there's a c-sharp stager and what happens is is that it the the back end you can clone any website you want to so let's just say you clone Google it'll have Google there and I'll show Google being there and when you go to the site or OB Google but embedded and
spread throughout the whole HTML source code is its command and control infrastructure and it's all randomized author out there and so what will happen is the beacon will go out it'll look like it's browsing as a regular user and loading the site but it's reassembling the command control instructions that it needs to do and then it sends it off and then executes so good luck detecting that right and this was two years ago I released a gherkin last year and still have 0 out of 60 detection ratio out there good stuff Nick Carr did a blog post there was that every remember remember the setting contest - MS extension type this is a extension type that a guy named in nigma
0x3 or Matt Nelson came out with from Specter ops and he found that this this specific file type setting content - s the extension type itself gave code execution function yet specifically in what we call deep links parameter and instead the deep links you could have it call an executable or execute code you could have a new powershell whatever you wanted to after this was released it was weaponized within about three hours there's a lot of different attackers that were leveraging this in a while to use it for commanding command and control or for code execution because it was something that hadn't been discovered yet two weeks later zero out of 60 detection criteria so again when we look at
detection today we're focusing very much on that pattern piece and what's awesome and cool but yet we still don't get a lot of value from our tools that we're leveraging and especially the next-generation stuff that's out there and really the focus on today not be on the pattern the pattern can be good for low-hanging fruits but we need to be looking at the behavior of specific attacks on what they exhibit a good example would be like application control bypass techniques which we'll talk a little about so instead of looking for G's Power Cells the simple example before explaining this so powershell for power show do you look for in Bocca expression do you look for
encoded command she noticed twelve different variations of encoder command think it's more than I think sixteen so you can do - you can do - you see you can do - en and Co different variations of the coca manage you know if you throw double quotes in there it's still a valuable string are still a little bit string or you throw carrots in there same thing so are you looking for all the variations of all these different techniques from a full-fledged programming language or can you look at the behavior of PowerShell and say well hey maybe we'll get some false positive out of this but if we can bubbled up to human to look at maybe we have a better
stance at detecting this like a good example be why is PowerShell beaconing onto the internet we're gonna get some false positives exchanged it's gonna be came out to the internet we do certain updates it's gonna be came out to the internet but can we baseline that environment and say okay well now PowerShell speaking out to the internet let's look at that command that was executed and take a look length of command is also a good indication right so there's a lot of things that we can say okay instead of looking at a very specific string that we're looking for why not move to something that's more behavior centric and say okay bikini that's the Internet in PowerShell I want
to look at that from an analyst perspective I want to see what that looks like to see whether or not it's malicious and there's a lot of good examples of this so let's do a demonstration I want to show a demo of Windows Defender and I've had a love-hate relationship with Windows Defender for the past like months I think I started to war with them so I called them on on on on on Twitter because I wrote this tool called magic unicorn about I don't like four or five years ago okay and when I wrote the unicorn what it is is it's a PowerShell office keishon tool and you know for things like encoded command like if you
have - en - nee & Co etc etc what I did is I'm able to use - value into string convert an encoded command back so that it doesn't get detected by most EDRs and things like that that's out there and what it does it takes shellcode whatever you want it can be Metasploit also I could be your own custom shellcode and it uses PowerShell to inject it directly into memory without touching disk you know why that's important is that PowerShell today is starting to become more of a dying breed when it comes to us as attackers because with PowerShell version 5 and version 6 integration into the anti-malware scan interface script lock logging things that nobody is using
right now anyway those are all great things that eventually companies will use now it's funny about script lock logging is it's like one of the best things out there not from the script lock logging it's basically getting like the raw syntax as it's about to be executed by the PowerShell interpreter it's a good visibility piece but no one enables it cuz the amount of volume of logs that you get it increases your Splunk license by like five hundred thousand right and we don't wanna pay that so so screw detection on that we that's too much right and so a script lock logging won't be there we don't use constrained language Bo no one uses that
because it's gonna break all of our developer standing over doing out there but we are seeing more prominence of PowerShell version 5 and version 6 which ultimately increases to two additional logging now I did I did the very first ever PowerShell security talk it was when PowerShell beta first came out and it was at Def Con I think Def Con 14 maybe what's that I do it there die deliver beforehand I think I did I think it's a Def Con first and I did besides after but as one of the first-ever PowerShell tops ever and I basically talked about how power show was gonna be the new new way of attacking this is back in 2008-2009
and what was funny about as I called a PowerShell oMFG and we leased a bunch of cool that we can use in PowerShell wasn't embedded into Microsoft at that point and and I said hey Mike this is gonna be the number one way of going it but PowerShell with what Jeff Snover with the creator of PowerShell me homes from a security perspective have done have really made PowerShell probably one the most secure programming languages at least from an identification perspective logging and monitoring on PowerShell you don't get that with dotnet you don't get that with Python you don't get that with bash the amount of logging that goes into Power Stone what you can do to
lock it down with constrained language mode and everything else makes it a substantially better programming language out there than anything else so we as attackers know that our window for PowerShell is extremely lower but with Windows Defender specifically and I'll talk about the antivirus and a skin interface the detection that we're using right now are still signature based there's no machine learning or behavior going on and these things even though that they tout it it's it's absolutely ridiculous what is happening is you have a PowerShell command that gets executed in prior to execution it goes into the anti-malware scan interface a MSI okay again it gets inspected by a mess sign that says hey it's basically in its Ross its clearest
form so after after encoded command after it's decoded and basically right before it's about to hit the PowerShell interpreter it'll scan it with a net with the antivirus engine and say hey do any of these meet our signature criteria in a MSI and so so what happens is that they'll take unicorn which is a public tool and I called them out on it because I wrote unicorn like five years ago and it still wasn't being detected by antivirus and I'm like listen can we just start to get better on the technique that that unicorn is using a wrap injecting shell code directly into memory through PowerShell is probably not a great idea like why do you need
create thread why do you need a virtual a like what do you need all these things in PowerShell kill the technique not the specific signature because an attacker isn't going to upload unicorn to github and talk talk crap to to a bunch of antivirus vendors right that's not what they do so when I wrote unicorn five years ago I wrote two versions one was kind of like a buggy version but it worked fine but then I'd like gala but better on the coding stuff and I released the what became unicorn today interesting enough does anybody know what my detection criteria is on that one that I wrote five years ago that I haven't published zero the one today it released new
signatures every week because they think it's fun because they just basically write static signatures on different things my codes actually got so much better like it's it's great works a heck of a lot better so I'll show you a demo of that right now I'm gonna show you an example of what what defender will typically look for now in in show code specifically with Metasploit they really really like writing signatures for Metasploit that's their their big number one thing and it's awesome right we're gonna write signatures for Metasploit we're gonna tech Metasploit well with Metasploit version 5 that's coming out you can get get it from the github repos right now they've incorporated rc4 encryption to d6 AES and a couple other
ciphers or a couple of encryption standards for for the shell code itself so you can actually encrypt all of your shell code completely which completely circumvents its inspection criteria now interesting enough if you just generate a medicine meterpreter shell with no encoding like like no shikata guy Nate or nothing like that there will be static portions of op codes that'll be inside of your show code that Windows Defender will look for they'll take they'll generate Metasploit they'll take a secondary snapshot of it and they'll see what our static patterns and then start to write signatures for those and so all you have to do as an attacker is when they decide to write specific instruction sets that are
common across the board is just chunk them up into different variables so if you notice here where it's highlighted it says you know is your X 3 3 and then it has a new variable and then it just chunks it up that was a specific signature that windows defender was looking for and if you chunk it up it's no problem you don't have any issue getting detected by antivirus and this is what it looks like when you get snagged by a mess I specifically it'll say the content of this has been blocked by your antivirus software etc etc and a lot of times about logs will be generated now what I love about this is
that it says category suspicious behavior there is zero behavior going on here it is not behavior at all it's literally compare this string to this string here and if it matches then trigger a virus alarm ok there's zero behaviors when you see behavior alarms I used to get scared by I'm like oh man people are really going into like this behavior stuff but think about it and from an enterprise perspective at Microsoft can you really build in the mass fleet of billions and billions and billions of computers build good behavior based stuffin out there that 100% block absolutely not there's no way you can't scale that you can't say hey if a parent-child process of Outlook that Exe spawns community AC
and Power Cell that exe we're gonna block that because it is militia 99% of time it probably is but in an environment as fast as there's there's no way you're blocking that based off of Markov chain so let's take a look let's actually do a demo here of what Windows is looking for
and we see that and then we got our Windows machine here and so this is Windows 10 fully patched with the latest signatures up there and what we're gonna do is take a look at what what specifically to be be flagged on so let me generate a quick shell a second me my IP address I could type today I cannot type
now this is unicorn what's gonna do is it can generate a partial encoded command that we can just copy and paste somewhere for code execution okay now I'm gonna copy this over real quick anybody can read this right good so what we have here if you look at the very top let me just blow this up a little bit and notice here some of the funny ones with EDR is like carbon black for example looks for Parrish W dash T but doesn't look for /w /c okay but notice here that we're using a two string to basically convert an encoded command back now you may be like what this well down here is is our base64 encoded
strings that have all of our code in it now what else to do inside of unicorn as I chunk up the code because a lot of places will look for base64 encoded strings and while this is a valid powershell syntax and most interpreters that are going like EDRs and stuff they don't recognize concatenated strings when it comes to encoded command now what I'm gonna do here is I'm just going to decode this really fast and I want to show you what's actually hat well first let me let me actually execute this I'm gonna take away the /w so you can see the command actually being executed let me run this from the command line I
notice here we get malicious content right it has been blocked by your and about suffered hey they released another signature it's another signature week with Windows Defender folks oh it takes me a lot less time to rewrite certain portions on my code then it takes those folks to build these signatures so it's been a fun game with them it takes me about 20 minutes probably takes them a lot more resources so it's a resource game at this point so let me decode this real quick and I want to show you what's actually happening here and what's actually getting flagged so let me just make some quick changes here
alright here's the code that's happening here just move over here so you can see it here's our code okay now you can notice here some of these things have changed over time like hey they're flagging on on very specific strings like kernel32.dll well if you put double quotes in there and no longer it gets detected it's this simple this simple that we're dealing with at this point in this case here I wrote a tool now this is why it takes me about 20 minutes to do it is I wrote a tool that natively understands the PowerShell language I wrote it wrote in Python and it looks at my code and it basically submits it to
Microsoft's defender and then it finds the chunk part that of the actual code that is being flagged by NRS or if there's multiple flags that are being flagged by universe I'm going to run this really quick let me just regenerate my code real fast so we can see it and then I'm gonna run my tool that will go through and find out what part and and you can just by trial-and-error if you want it to you and what it's gonna do is it's gonna chunk up on my code submit it to defender to see what's actually happening and what gets detected it takes a sec
it takes like 30 seconds if that depending on how long it takes so I found one string so it's flat Windows Defender is flagging off a very specific unicorn command called four which is basically a four loop and it's going through all the opcodes and it found that that specific string right there triggers on a B detection okay so if we change you look at the four instead of doing four why not just do while true all right and it also said and let's let's let's submit this I want to show you real quick submitting this into the interpreters well so you can see it's still the same thing so if I hit if I
hit play notice it's saying getting blocked by the the at the bottom so we're looking at the same same code here so we also found that this string here 0 0 X 8 D start these op codes here we're gonna what we're gonna do let's take a look at this and I'll just break this up real quick I also call Camus like house and I'll do mu two real complex real hard let me see where and then so I need to add this here and what I'm gonna do just to make sure I'm just gonna create my listener see if it works better handler I'm gonna copy and paste this into here and we got our show real
difficult right machine-learning ha behavior yes right so if you look at some resources you look at all blocks at Microsoft comm this came out recently and they've been touting a Massiah sharpshooter now one thing that Microsoft did that was awesome with sharpshooter and sharpshooter is a very specific technique for DC ization acts is that they actually blocked a specific type of attack on called dynamic invoke and that wasn't commonly used across the board and dynamic Evoque once that's blocked it's very difficult to do DC realization attacks and if you obviously did enough that's great but here's some of the benefits of a msi notice on top that's the obvious gated code on top on the below we can actually
see the div skated code directly through a messiah there are benefits from an analyst perspective in integrating the MSI but it's still static signature based detection isn't it it's not behavior it's not machine learning but you have the data at least available to you to be able to look for I just wanted to throw a quick dig on the machine learning thing I'm on their comments they're not happening most EDRs pretty trivial to bypass as well this is a good example for for carbon black command a DX e / c / q equals will get caught command ID XE / parent c /kr q does not get caught so we're still a signature driven industry
watch list in carbon black are significant a lot of the tools out there that tout ninety-nine percent protection 100% detection I love that comment you know what the hundred percent detection is 100 percent detection on what they're looking for if you change it in any way shape or form you're fine you're 100 percent fine absolutely fine no issues whatsoever and so how detect today is this machine learning stuff is really based on telemetry and telemetry if you're not familiar that term is data that they're harvesting off of your endpoints and using that it's a massive big Splunk instance to be able to query and write signatures off of and the same thing goes for virustotal when that debt
control settings - MS came out our settings content SMS came out what I did is as I took that and I named it apt 28 dot settings control - MS and in the deep links I had like a pretty op skated PowerShell command and in there I put a shout-out to one of my friends and I uploaded the virustotal within about 14 minutes I had somebody reaching out to me saying hey it was a funny joke they literally have massive armies of people farming through virustotal data to write signatures they literally have telemetry coming out of Windows Defender and they have a team of people writing signatures that is our artificial intelligence and machine learning of
today human beings going through massive amounts of data writing signatures and again if you change that in some way shape or form you're usually fine when it comes to it code execution this is from what we see a binary defense but today about 84% of what we see are still binary Dropper dropping an executable usually unco non-code signed on to an environment to get code execution still about 84% that's the massive amount of that's the most prevalent amount of attacks that are out there 13% is PowerShell injection okay definitely an increase from last year it was like 8 percent last year so Power Cells definitely prevalence in environments now what we're starting to see is the change to
to application control bypass these what we call wall bez binaries and scripts and I'll talk a little about this but most companies today are still focused on executables in PowerShell which is where you should be that's your highest percentage of attack surface when it comes to be prominent predominant amount of out there but we still need to be looking out for these Lal Baz if there's a good good source from odof our mo o d'Ivoire has a great site that lists all of the different application control bypass techniques and scripts that you can use and what these are if you're not familiar is that Windows come shipped with all these different binaries rights you have to run an operating system
right you have to have PE files you have to have executables and so when that when the operating system starts you have what explored ID XE you have all these different executables in your operating system right well a lot of these have code execution functionality with zero logging whatsoever so a good example of like MSHDA wmic register here are 32 CBD DHCC stic even BG info and other things that the background info has remote code execution functionality with VB script so these are code signed binaries from Microsoft that have additional functionality to go and download code from the internet and execute it either in memory directly or download a file and execute it and so
these these things are great for us from an application whitelisting perspective why because you whitelist Microsoft signing certificates don't you and so this is where a lot of the research is going into today is finding these in either publishing them Casey Smith from sub T is one of the best resources when it comes to finding these you have a lot of other folks too that are that are doing research into this in this area here but what's interesting as less time I checked there are 68 total binaries just binaries alone that have additional code execution functionality in them that allow you to execute code on the system without detection and that's where a lot of the research at axe are
going into right now so my personal favorites this is my favorite meme I've literally put this in every one of my presentations for like the past five years and it just gets better as you watch it so like you know and I usually use this for ones I'm gonna talk for a little bit because it entertains the audience and it just gets better like people are looking like it's gonna get better it is getting better right sorry awesome whoever created that is like the most genius person I've ever seen in my life it's like the perfect skinny one second one second all right all right good so some of my favorite ones like WIC for example you can use the slash
formats which will look for HTTP bad sitcom and you can download XSL an execute code cert utils you know certain you still has the ability to download code directly from the internet one of the cool ones we saw in the wild that Daniel Bohannon did a tweet on recently no sorry about prior a few months ago but as using cert util to download power show code and then execute the PowerShell code and it went with in PowerShell what is that that that specific chain do they may know so if we're looking for PowerShell baking out the internet but instead they use cert util to go and download the PowerShell code and then execute the PowerShell
code that doesn't use the internet what happens boom there goes our detection criteria right what happens if you write certain things in EDRs what happens when you rename PowerShell yeah right it's usually that easy by the way and so a lot of these have the ability for code execution em sh t is another good example um you can actually you don't have to the extension types at the end of them you can have it be a dot txt what happens if you see em SH if you see Internet Explorer user agent or user agent from from MSHDA go out to github and download something like only github.com slash awesome tool slash license that's suspicious to you
probably not depends on if it's em sh t going out but a lot of have the ability to download code and execute and that's what's important now let's talk about behavior for a second so I saw when when the wmic portion came out most almost all the EDRs all the signatures they come out looks 4/4 Matt what happens if you change slash format is something a little bit different well they're 100% detecting on slash format but they're not 100% detecting on anything that you modify or change in any way shape or form again very easy for circumvention a good way to detect something like this would be why would wmic tidy XC and ever in the
first place beacon out to the Internet why would it ever got to the intern in the first place WIC doesn't go out to the internet MSHDA typically does not go out to dinner the only time I've ever seen MSHDA go out to the internet is that when they're to use like an ancillary method for AWS management services which uses HTA's but it's like a fallback method that they couldn't use the first one to go into so you typically don't see em sh t in environments register you're at 32 sometimes can go out to local IP addresses but never beacons out to the Internet in most cases so again a lot of things that we can look for and so the balance that we
have to figure out is that most companies don't have the people inside to research all of these techniques and to understand what they are and we'll talk about automation testing here in a few but you might have the data but you don't know what to do with it hey we're getting em point locs awesome but you have to have em point locs today there's no if ands or buts I know increases your Splunk licensing I am NOT a spokesperson for Splunk but it increases just your licensing is substantially you have to have endpoint logs and point logs are like number one when it comes to attack surface does it mean you shouldn't do server decimation
do dns does it mean you should do firewall logs but it means that the importance of endpoint logs at this point time is substantially higher and so doing that and implementing a protection again takes that long time and investment and so what do you do when you don't have the people because we would we would solve security right like I'm here to solve security today in today's presentation right so we can solve security today period 100% like I would say that we could solve secured 99% if we had one dedicated security person to every single person employee that you had in your organization because then you can sit behind the person like hey don't click that stuff
that's ridiculous right your response time would be awesome all you anyway well me me take the laptop they passed over to Bob Bob pass that Mary and Mary pass to Jojo reimage it you send it back it's a little loop be awesome it'd be so efficient unfortunately we don't have that ability do we and so we have to say okay well we don't have the people to do this stuff how do we get to a model where we can see these types of attacks in our environments and keep up the date and that really comes to leveraging read and you'll hear this concept a lot around purple to me I'm sure it's it's me a lot
everybody knows the concept of probability I mean blue team's and red team's working together to figure out things but in most cases the blue team even if it's a hunting that's supposed to understand a lot of the TTP's that are out there or gets threat intelligence that shows them specific indicators doesn't understand in most cases how those techniques work you don't understand when you execute the specific command this is what's happening behind the scene or this is a new attack vector that came out that applies to you know in our environment because of this and if you don't leverage red then you don't understand the attacks that are happening out there today it's really important that's the
solution today it's often referred to as purple teaming and it's collaboration between red and blue working together to simulate an actual attack and what I mean by that it's a lot different than a penetration test right a penetration test we try to find as many exposures as possible during a given time purple team engagements aren't supposed to be something where you are trying to fish individual users and you're trying to find different ways or avenues in you're simulating very specific attack patterns and you're working with the blue team to build detection cards here that works let me ask a question if a threat hunter and this is not no offense of threat hunters are absolutely brilliant
fantastic and needed and also our stuff but if a threat hunter is building a detection hole off of a specific attack what happens you get wmic slash format in those directions if you get a red teamer that's helping build those out what do they do oh hell I can bypass that with this right and now your detection criteria becomes much better doesn't it so simulating actual attacks in your environment and working with the blue to collaborate work together mix makes a huge difference when it comes to those those simulations and it's got to be continual ongoing exercise it's not something that's like hey I'm gonna do once a quarter or once a year and then
from there we're gonna walk away this is something that needs to be built into our programs that we do today we don't do that right now use these as exercises as in conjunction with our penetration test you should have an internal dedicated red team you should have an internal dedicated blue team and they should be working together to do this corrective them yeah and the reason I say this is that what's your biggest return when it comes to being able to stop attacks protection is one right detection is there if your detection sucks you have a big problem on your hands when it comes to responding to those incidents these simulations really help with that it
also goes into building threat models everybody hates it hates talking about threat modeling because no one understands threat modeling but really understanding what you're trying to protect the adversaries groups that are in play and then building out your capabilities to simulate those attacks in your environment and and what should really be happening is the red team should be up here a little bit right and your blue team should want to get to here and then your red team goes here and you go like this right and it's about going through and it doesn't mean you have to detect everything that's out there but a good example like lateral movements people focus on decom lateral movements pass the hash other methods
for 4wi exact to get to understand letter movement you know many different types of lateral movement there is in your environment lots however if you look for something something something simple like here we're gonna get all local logs and we're gonna do forty seventh log ID 46 24 we're gonna look for login type 3 and we're gonna see what workstation or workstation lateral movement that we have in our environment that is a very specific behavior in our environment instead of looking for a very specific pattern in our environments and based on your environment saying hey well maybe we have a few service accounts coming from this source IP address let's say put exceptions into those but let's look at
lateral movement as a whole and what we're seeing do you want to see Bob and sales moving laterally to Mary Ann I t's computer that's probably not a good indication that something's right there again behavior versus pattern the red seem responsibilities in a big portion of this comes down to research research has to be the foundation of what makes up that red team building out you might start up here we're gonna do Metasploit meterpreter with no encoding and we're gonna do encoding here we're gonna do cobalt strike okay now we need to use our own custom c2 infrastructure to build out and use a undocumented method for code execution because our team is so good at this point
um we uh stood in a sales pitch there's a lot of great companies out there a trusted SEC we found a couple customers only a couple like to that the sophistication level was so high that it made us look like a bunch of children and so we ended up dedicating our entire team a year and a half ago to building an entire research team for doing methods and techniques that haven't been discovered before so that we can get access to those environments and do it and we do very well at that now but during those periods of time like there are only a few companies that have hit a level based on what they're doing to get
to that specific type of level out there and that big that's because the continuous needs being a lot of a lot of testing and really your red team output directly equates into what you're doing for your defensive capabilities now really quick talking on on automation testing I'm a huge fan of automation testing if you're familiar with the miter attack framework you know you have Caldera you have the atomic red team you have a lot of commercial platforms that out there there's a lot of great things that those tools can do if you're not remote them you can run a tool on and endpoints and it generates a bunch of alarms for you now that's great
but do you know what to do with those so if you see MSHDA what do you do you write a signature for MSHDA going to this and we see if we see in our logs let me write a detection it can't help with a lot of the commoditized stuff that's out there but to be honest with you and most companies that are running these tools still have password one as their administrator password for their domain admin you don't have to worry about this type of stuff yet unless your programs actually functioning appropriately I can't emphasize the the amount of time it takes for research in our industry both offense and defense requires a substantial amount of research and if
you aren't dedicating your team's to having that research time you're losing out and what you what the possibilities are for understanding what's occurring and research should literally be at least 25% of the time that a red teamer has in their environment to be able to develop code or develop capabilities to be able to do certain pieces there it's it's really important to understand that what it takes out there I mean just looking at delegation tokens in Kerberos and to figure out what's happening for for Active Directory it's you understand the ins and outs of that to build tools around that to understand what how it applies to our environment that takes a lot of time if you're not developing
research as part of your overall security program you're behind the times research is an absolute necessity when it comes to what we're dealing with today you had Edie ours out there right and endpoint detection response tools I approached this too the acronym first and point detect and response tools are supposed to be that augmentation wing for you to be able to have a lot of the advanced attacks into your tools so that you don't have to have a research team dedicated to it in most cases they can find a lot of the low-hanging fruit that's out there and a lot of other good things out there so as an attacker we need to understand how to get around
those specific tools and how to use our techniques to get around them to see what an actual attacker can do and if you're not dedicating research to those again you have a lot of a lot of major problems so closing up when it comes if you take one thing away from this it's that a Windows Defender is awesome right machine learning is awesome artificial intelligence is awesome the EDRs are doing a great job because they detect 100% of everything that's out there derbycon is far less appear than BC at Augusta there's a lot of things that you can take away in it anybody's watching just this talk there was a whole joke we have before this I don't want to you
know throw anything out there but the biggest piece around any of this is that as an industry we are still very much signature driven no matter what anybody is telling you out there whether it's in IPs and it's using behavior that it's a baseline there are things that can be behavior based but it still requires a human being to interpret whether or not the DES malicious and that's the part that we miss in this industry we're trying to still rely off of the tools and while the tools may provide us better visibility or may meant us in a way if we don't have the people to support that then your program is non-existent you cannot sidestep people period people
have to be invested upon people have to have that time to look people have photo training you have to have a team dedicated to this type of stuff and if you want to do detection today you have to have people there isn't a tool out there that I know of today that doesn't require people to actively through them a good example would be some of the best prevention that I see out there today some of the best prevention is application away this thing can you run an application where this ting program people right we laugh right is everybody here have a standardized laptop where everything is exactly the same on every machine no you have to have people for
that good example process chains if you look at a parent-child process that's one of the most valuable things that you can use in an environment for detection so you have a parent process of windward dot exe spawning a child process of PowerShell or command at exe or W script or C script what does that mean something bad happen right but if you don't have that visibility to look at that and say well maybe there are certain business processes that leverage that maybe we have a couple macros in our environment that uses a business process as powershell or committed exe but if you did investigate that with the person would you know that can you just
straight-up block that across your entire environment probably not you probably have deviations to those a good example I was doing a breach assessment for a company and I thought I found something amazing I'm like oh I just just paid for my whole consulting you know experience here because I found this one thing and it was an exchange server and it was a domain admin account running as a PowerShell command that was going out to a Chinese IP address and downloading and non signed codes not an on coats and executable and it was like a randomized name is that bad yeah right I'm like I just I just made my money domain admin go don't going and downloading an unsigned a
binary from the internet from China I made my money so now I can just like chill and write some code for the rest that we know just getting on in there they did what we do right so as funny as is is I went to the customer Mike found some stuff like this is critical urgent we got it got to shut down the exchange server we got to change the password like oh no that's we have a third party development company in China and it's a reporting tool for our exchange service it's it's legit I'm like oh I got a couple suggestions this is here for improvement there however is that malicious is it it's a business process
that they're using in their environment but if I didn't look at that and investigate that I wouldn't know when I look at em sh TI b XE beaking it's an internet maybe we have a business process that does it but if you don't give that to a human are they gonna are they are you gonna know so detection really focuses on the people and one thing I want to close with is that there has to be a innocent I notice a big term but there has to be a whole process for how you continuously mature a good example would be hey is every the D de Otto stuff that happened about a year and a half ago right so if you're not
familiar like DD Otto most most code execution through office documents comes through macros right that's the the primary method well a security researcher have found a way to do code execution without macros so it's called DD ATO as a method that you can use to then get code execution on a system does anybody know how long it took to be weaponized by locky 24 hours does it mean know how long it was how long it took to get weaponized and used an exploit in the wild for hours so our time window for that is is very small right how do something like that in your environment where DD odd is being released get to your Security Operations Center
from an analyst to be able to detect it and that's the gap alright how do you continuously make MSHDA when it beacons out the internet a known issue for your analyst and how do you train them on that and that process that it takes in order to do that if the red team discovers new methods for bypassing your detection there should be direct ways of building detection into there and training your sake analysts or individuals that are going on the hunt looking for those as a way to proactively identify those in the future one of the biggest things and I run a 24/7 security operations center one of the biggest things I have with humans as
humans looking for something that is legit like not legit like me asana as it is a attacker we had recently that that our team missed and the really we caught him on the Power Cell execution so we got on that but we didn't get him on the MS HTTPS so there was a thing that was like user awareness training HTA is there ever going to be a user awareness training that HTA if you're an attacker you know that that's not legit right you know that there's never a user we're gonna stray today HTA out there there's not a company uses each tas so our stock analyst looked at it and said oh it must be user awareness training and you
closed the ticket didn't know that that was a method that's our bad for not being able to train them in a way to get better than now luckily our other detection is like power shell injection everything else you know quickly hit that which is fantastic we caught it but in those specific cases do you have a mechanism to train your stock analyst of what looks malicious and what is unusual behavior those are all big pieces that we don't focus on today and that process where you're looking at from the beginning of when we discover or when we actually do a simulation or test in our environment what does that mean to get that into a format to where we can use
it intelligible in our environment and those are the things that we have to answer in security today I want to thank besides Augusta for for having me out here really appreciate everybody's time is they made many questions open up for like like two questions or no questions you don't feel shy I don't bite yeah
good question and just for clarification - I wasn't ripping on any of those tools the tools are great for visibility carbon black is great for visibility we can get from process chains what you can get for what's being executed on the system itself they're great for visibility but if you don't have the people to build them up and to manage and maintain them then they start to become a problem and so the question was is there any tools out there that have given us a headache and honestly the answer to that is is there's not a product there that it's giving us that it's getting us a headache it's been the teams that have given us a headache
there was a company that was leveraging a specific tool and I won't name the the vendor and this one the the product itself out of the box is is not gonna be good for detecting us right but they've had a team there built in and doing the testing back and forth purple team exercises having a hunt team and they built the tool over time to where once we got code execution we did something that we thought was super stealthy like we're like oh yeah we got a show or I'll high-five all of a sudden two seconds later the machine goes in can team and we no longer have communication with our command control infrastructure like how
the heck did they attack that so we used somewhere else so that the people have really been that been the big aspects there really hasn't been a tool that has has been a major problem for us that to get around as an attacker I would say that things are definitely up ticking getting better it can get harder for us depending on how much they lock the machines down like a good example would be silence silences AI components aren't hard for us to get around right but their application control functionality Devon there's actually a really solid so if they implement application control very effectively then we have to figure out ways to circumvent and get around
those to be able to do it so I would say that again it's not necessarily the tool it's how its implemented and how the people are using it in order to make it better and understand those attack vectors so it's not every doesn't matter fusing carbon black using science using CrowdStrike using whatever you whatever you want is fine as long as you can build those tools to be better than what they are out of the box is out of the box they think about it from an organization perspective if a company releases protection that actually works is that going to work across every single enterprise most likely not the variations and differentials that you have to
do in most environments is substantially large so they have to deal with a lot of these things and while they can mock things down to stop things it requires the people to customize and to use those tools in a way that makes it makes it different so they answer your question no not not really any tools that have caused us a lot of headache hurt issues good question any other questions one less one or well thank you all very much for having me on I appreciate it [Applause]