PG - A Quick Story Of Security Pitfalls With Exec Commands In Software Integrations
Show transcript [en]
thank you thank you all right how are people feeling great great yeah so before we start let me ask you two things who here has a 10 talks on API security raise your hand yeah quite a few of you who here has a 10 talks on uh supply chain attacks vulnerable dependencies on yeah a little bit more of you right that's bomb yeah uh there is a a theot type of vulnerability that I'm going to talk today which is exact command or command injections that I think is very important so with that said welcome to a quick story of security pitfalls with EXA commands in software Integrations um a little bit about myself my name is Le alpi I'm from
Mexico I'm currently uh working as a security engineer for Google I'm also an open source contributor I have worked in small companies big companies everything in between and I really love cyber security so quick agenda for today uh we're going to talk about software Integrations some of the common Associated vulnerabilities on each one of those categories we're going to discuss a couple of case studies then we're are going to talk about one of my CB that I reported last year and finally we're going to discuss a couple of lwh hanging fruits on how to exploit this and also how to mitigate and reduce risk but before we start let me tell you the usual uh disclaimer
so the opinion expressed uh in this presentation are my own they don't not necessarily reflect the opinions of the organizer or my employees or future employees and all this is um uh with uh learning and educational purposes and to enhance cyber security awareness with that said uh probably we are here agree whether if you are just starting to write your first lineer code on your experience developer that code that doesn't tou anything else like any external platform system is not very useful right in order for code to be useful it needs to have some type of integration uh to any other platforms these Integrations are usually in the form of libraries and codependencies mean you are importing others people
code into your programs but you can also do through calling external Services meaning you are executing other people's apis through a channel it can be the network uh and also you can do what is called like exec system calls with meaning you are executing uh programs in your same uh process name space so each one of these uh categories of Integrations has some Associated pitfalls and vulnerabilities for example when we talk about libraries and dependencies uh we may think about vulnerable dependencies right we may think about uh dependency confusion attacks uh Famous Supply chain attacks type of squatting uh misconfigurations here is your solar Wing attacks right like very famous supply chain attack lock for J here you have your national
state actors trying to take over GitHub repositories hoping to inject malware in those dependencies and so on right on the other hand when you integrate software by calling apis or calling external Services more probably your thread model change towards data validation and Sanity ation you take care about the integrity and the authenticity of the package being sent uh you are uh you care about data security in transit and all the encryption and data privacy one of the most common issues for this type of integration is for example a misconfigured est3 bucket in which somebody push a lot of information and is publicly available and anybody can can exploit it right another thing is that if you expose systems to the
internet somebody can gr like web scrapers uh like in these scenarios and they can like extract all the data and most Pro most famous that is uh similar to the Capital One data bridge that happened right the thir type of vulnerability will be associated with common injection most probably we here we are talking about previlege escalation vulnerabilities in file systems and IPC vulnerabilities here you have uh Equifax that I'm pretty sure everybody knows because it was a massive data Bridge impacting over 800 million uh customers or users around the world and also more recently we have the Microsoft Exchange Server vulnerability that ultimately was a common injection and impact around uh 880,000 companies organizations around
the world so for the rest of the presentation this type of vulnerability that we are going to focus on we're going to do a deep dive into fundamentally how this uh may be exploit in some scenarios and looking for for for you I have a fresh CV that I submit last year in a popular uh open source software that ultimately allow you to take over um and infrastructure and and all the platforms be managed through that software and it was high criticality so we are going to do a deep dive into how how that analysis work how the exploitation work but before doing that let me tell you about the motivation be behind this research so as
probably of you are already um familiar to um who here is a fan of Home Labs or they do some kind of H laabs right I think H laabs are very cool they are a very they are a great way to experiment and learn hacking and learn new techniques and my current mass is most probably a bunch of uh has a bunch of virtual machines bunch of bare metal of physical machines it has a couple of Clow instances uh so I have a little bit of everything so as the home lab grows uh yes yeah approve yeah so I have a a bunch of uh little bit of everything right so I needed a way to manage all of
this mess so I try multiple tools eventually I I have to learn anible a very popular uh management automation management tool and anible is amazing right because it allow you to control multiple machines through a a thing called The Playbook and the playbooks allow you to set um a bunch of instructions that will allow you to update delete um install software in all your machines right so as the home lab grows um it's getting uh more and more difficult to to do this kind of management because sometimes I'm not in my common line right sometimes I I'm traveling or I just have access to my phone or so on so I start thinking that there should be a better way to do this
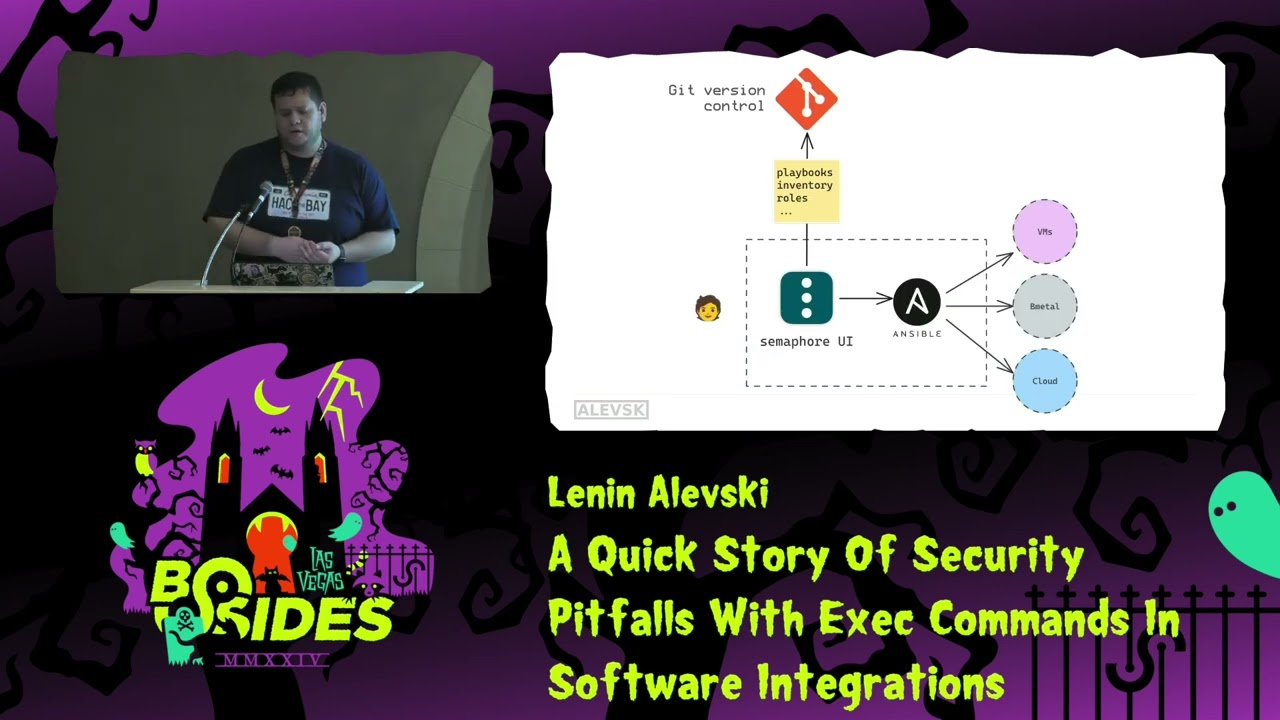
right I start doing some investigation thing about uh popular open source software and eventually I found a very cool product open source called anible uh called SEMA for UI right so SEMA for UI is amazing it allow you to uh integrate with all these automation tools including anible and on paper sem4 UI looks great right if we could have a diagram like this in our minds uh it allow you to do all the anible operations through an nice UI um you can have all your playbooks being pulled from a repository so everything can be version you have auditability governance multii authorization out of the box and the best part for me that it allow me to
reuse all my scripts that I already have right so as I was saying uh it was amazing it had an integration with anible so everything looks good however we are hackers here right we want to understand how this thing work how the Integrations work and this is the main focus on the talk like at some point I start thinking how this UI integrates with anible how the commands run so I start doing a like a code review manual code review the the project is is in Golan a programming language I'm familiar with and I start reading out the code until I found that the way they call the anible Playbook is by using a exact Command right which is a way a
system way in which you call other programs using the system call so I realized like this is dangerous right this is a problem so I continue reading the code the developers they they I'm assume they may or may not be aware about this was a bad idea they try to hardcode the binary to try to limit the arbitrary common execution but if I'm honest with you I didn't feel comfortable running this in my infrastructure right I don't want to expose it to the internet I don't want to other people to mess up with with my environment so I decide to continue investigating more right so I enter the realm of unble security so if you are
not familiar with anible security now it's a good chance so there is a cool website that I highly recommend you to bookmark that is called GTFO beans GTFO beans is amazing because it has a huge repository of binaries that exist on the Linux operating system that can be abused to elevate your privileges or exploit some aspect of security of systems including anible Playbook so right out of the box I have two examples of how to how can I pop up a Shell by running a malicious Playbook right and also how to how can I elevate my privileges so uh it's a very cool website book Market you can go you can look not only for anible you can look
for many other binaries and if you are a Windows person there is also a Windows version for this right called lbas which is exactly the same so armed with this knowledge I start creating my own malicious playbooks to do more experimentation right so as I was saying is possible by uh running a malicious playbooks to get an interactive shell so anybody that run the anible Playbook command and then pass this uh Playbook we'll get a shell similar to that uh you can do a Ser side request forgery um and basically you will turn that machine you need running anible into a proxy what about reading sensitive content and sensitive files you can do all of these through anible
as well right and this works uh this way like by Design because this may be a legitimate operation that you want to do with automation right and finally we have the most common example which is how how to get a reverse shell like if you have a netcut listener and then you execute this Playbook on a machine you're going to get a reversal so you get the idea so it seems that the most dangerous thing is arbitrary malicious playbooks right looky for us the whole semop for UI model take this into consideration and we can divide and we can have two types of users one an admin user high privilege user is the one that is going
to be pushing the playbooks into G Version Control like everything can be authorized auditing very secure and then we can have a regular user that is the one that is going to be just running authorized playbooks is not going to be messing up with anything just clicking a button to for example Lo that packages right um however if you go and remember the line of code with the vulnerability there is still two more arguments that are basically untrusted input coming from a potential malicious user so I start thinking can a malicious user can a low privileged user do something with that type of access so in the UI there is a part uh in the platform that directly relates to
these two arguments right this feature is called the extra variable feature and this is also part of how anible Playbook works right by passing extra variabl feature you are able to influence the way uh an existing Playbook behaves and this is very useful when you want to customize certain host name certain users certain values uh usually these extra variables are defined in a key value format but also support Json and jaml or or files and so on what they don't tell you in the documentation and correct me if I'm wrong is that you can pass what it calls plugins so these plugins are very similar to a serers side template injection attack that will allow you to basically P pass some
command that will get evaluated and then uh the result is going to be included in the Playbook right and this can be like some some malicious Playbook and just to be clear this is not um even if it's not documented in anible this is not like a vulnerability in anible right this is how it works by Design This is a vulnerability on SEMA for UI the the layer on top so armed with this knowledge I went and refactor all my malicious playbooks and now I come I came with malicious extra variables right so this is great because now a regular user a low privilege user can start doing all these um dangerous potential dangerous things such as uh
retri retrieving environment variables right environment variables usually contain uh sensitive data such as encryption tokens cookies uh API stuff right that then you can use to to um laterally move to move laterally right you can also do the service I request for G attack which is great for direct ex filtration and extract secrets from from a particular machine uh but then there was a caveat that I found right in order for an extra variable to be executed it fears need to exist on the Playbook that was a challenge that I found however anible anible documentation is great by the way there is any anible maintainer uh so there is a set of global variables that they they
will be always present regardless of the type of Playbook so if you define your malicious Playbook by using any of those that will guarantee you that you will uh execute your malicious code right so in order for you to trust me now I'm going to show you a quick reversal demo
so me one
second well no the demo Goods even if I have a backup this is the backup of the backup by the way let me
okay I can come back to this later by the idea is that um you have um you have anible you have semop for UI and then a regular user can uh use um Can execute let me U go back very quickly me see
there it is is this is the tier backup isn't YouTube but uh the idea is yeah you have your netcar listener listening you have a um low privilege user running a couple of authorized Playbook with a malicious um extra variable whenever they you update that this is a Playbook that will use update system packages right uh at run time the variables are going to be replaced with the Playbook with a issues uh payload and then you are going to pop up a reever shell right and from there you can do way more advanced things such as um you know like lateral movement and uh stealing secret back doors uh stuff like that so with that let's
continue so what happen by taking advantage of this vulnerability as I was mentioning a malicious user escalate privileges they can gain control of the host and potentially all the other machines uh being managed by sema4 UI right which is pretty pretty pretty dangerous so now let's put on the the red teamer hat right and let's think about how can we exploit similar examples right like whenever you try to do an assessment let's IM my we are trying to review this piece of code let's think everything that can go grong about this so the first thing is if you are able to inject an arbitrary command that's common injection out of the box right you can run anything that you want it
will will be executed with the same level of privilege as the program running this function uh if you are able to control the arguments or the environment variables that will help you to influence how this program uh behaves right how this execute then if you are able to control the execution folder that also may give you some intended access to somewhere in the system next uh if you are able to control what the input that the software is passing to that binary that may also be interesting to see if you can exploit that that binary that integration and finally most of the time these these commands being executed through XX system calls will produce some type of output that may contain
some sensitive dat right some tokens cookies things that should be remain private right and you don't want users messing around with that um the good thing is that most popular programming languages have native apis to do this exact system calls doesn't matter the programming language you can there is a way for you to call other programs and as long as this is like this like Dev developers will uh will do it right so besides the traditional Dynamic testing and fing testing what I recommend uh for you to kind of do this type of analysis is to do thread modeling right understand at a fundamental level uh what are the different components that are integrated um and
how that uh impact the security right the security aspect uh I I I always recommend to read the documents maybe there is a flag there is an argument that you can use to abuse the platform abuse the system and uh there is a lot of interesting files right files and flags so now let's remove that c and then put the Hat of the blue team right how do how do we defend for this how do we uh mitigate the risk so the first thing that I'm going to tell you is if you have to if you are starting from scratch and you have to do an integration you prefer any other method right this is probably the worst
method to integrate programs um if you don't have a uh if you cannot do that because of Legacy reasons because maybe you are dealing with a binary or a program that doesn't have an API or doesn't have an SDK then the next thing you have to do is same team as the red teamer you have to really understand fundamentally what is the thread model for this how do we impact the security of of the overall platform of the overall uh um program while you are doing that I follow the the list privilege principle meaning sbox execution of the of the of the binary like Drop privileges try to uh drop out capabilities you can also complement
this with a bunch of a couple of static analysis code tools and while you uh found all the places in your program that is doing these system called the exact commands make sure to always uh sanitize the input right and if possible use uh a low list so people doesn't pass like arbitrary arguments arbitrary commands as I was also mentioning read the documentation be aware of those dangerous Flags uh security training for your developers is very important but the most important part that I want to takeaway is that this is a continuous process right you have to do this uh these analysis for every integration that you bring into into your system right into your
platform so today we talk about the different ways software Integrations the common pitfalls and vulnerabilities associated with them uh we discussed a couple of uh famous case studies like more like data breaches uh we we did a deep diet analysis into the CB on SEMA for UI and what was the impact we did some uh lwh hanging fruits um exploitation analysis and mitigation risk and with that uh thank you so much uh we are open for questions in casee we have time I think yeah we have two minutes minutes [Applause]
so I think if anybody has a question there is a mic over there oh perfect uh fantastic talk I really appreciate it uh what was the painful part of your research from the time of discovering that uh they're using uh anible in the background and what prompted you to start digging deeper into uh the project and what was very painful in that process yeah so I will say the most challenging part was um like to run SEMA for UI it was very easy right it was just a container I can deploy it on kubernetes or any other container run time being able to set up the development environment was kind of challenging I spent a couple of times uh
a couple of um days trying to get the tools and the right versions of libraries until uh I saw that they use what is called depth containers that basically simplify the development uh process a lot so that's was one of the things that I learned and then um to kind of exploiting the vulnerability and find it it was a couple of um because I didn't do that like full-time it was like across like a couple of weekends until I have like a pro of concept and then I I responsible disclos it with the team and they patch it and and they assign the CV yeah thank you thank you for for the question thank you
[Applause]





