From SEH Overwrite with Egg Hunter to Get a Shell!

Show transcript [en]
hello everyone welcome with my talk i'm glad for be here for you all my talk is called through a c8 variety of egg hunter to get a shell
my name is but you can call by my nicki named hodox i'm i did about me i have penetration tester instructor oit constantine of information throughout 30 years mr financial hacker basically give me talks at conference as hacking the box occupy qubit conference arab security conference materials managing village besides calgary's etc magazine about stack of the flowing princess magazine about cover channel for further to get a shell through a c8 of a right to let the show i leave here my linkedin profile by my email for words take outs and doubts you can write me at my linkedin or my email [Music] our agenda you learn what is sc8 is 30 700 buff overflow we have a park impact we learn the sc8
override short jump aggie hunter many characters reverse shell and we have a questions exception 100 exception 100 is a chunk of recording from inside of an application which you have in the objective to handle an exception that can occur during the creation of the software reception look like with here we have try and catch and try execute some code you should call some exception should jump into catch it catch execute some specific code where inception core so a flow of execution of the software we will pass for the try execute some code if required some exception will jump to catch in the cache it will execute some specific code reception core
the sc8 works in chain and the hierarchies in end of stack in the classic buffer version of vanilla the exploit of writes the return address without worrying about writing more bytes in stack but with the sc8 of the right technique it is possible to obtain my space and final shell code in order to have exploit more stable so we have here in our stack remember that the se80 is localized in the end of stack and here we have necessitated recorded se hundred these sc8 work in as a chain
exception is an aspect event an error that occurs in your early ccr program where exceptional chorus the problems normal flow of execution is terribility it is important that the application can handle the services or errors to continue running normally the address of the exception hundreds are started on the stack the separation system has a default handler that gets any exception that is not handled by the program when windows handles an acceptor in application we usually see the message program has encoded a problem it needs to close so we learn here that each program has your own exception handler but the windows has two your own 700 when the 700 of the software don't work the except 100 of the windows work
in the world where we see the message problem has encountered a problem needs to close
buff overflow buff overflow is anomaly where a problem while writing data to our buffer overalls the buffers boundaries and the price said memory locations might be repeat based on stack based be based placing the memory which allocates a lot amount of data and dynamically stack based locate a limited or fixed size of data which is data from account variables or functions so we have two class of buffer flows repeat based and stack based here we have animation of the buffalo flow we have in left image variable 4 with level 8 right image variable 468 yes we can see this turkey is over a variety is taking the variety if you are what amount of character is
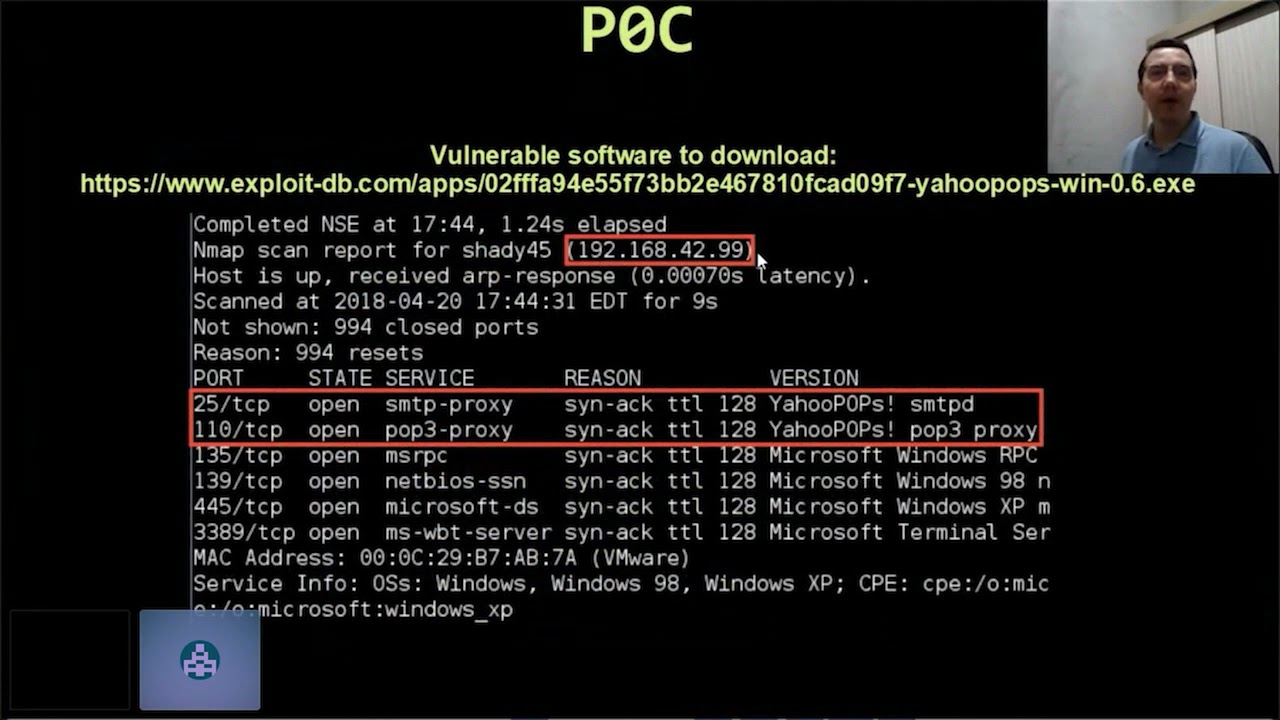
we saw variety the resistance abp earth sc8 as we can see here sc8 is localized in the end of stack so the s8 is a resource of windows to handle the 700 and the sc80 of windows is localized in any of the stack now we have a park the attacker machine will use the color linux 20 20.3 and the vulnerable source that we use is the easy fire shell web 7.2 it's running windows xp and service packet 3 here we have a link for the load of enable software i'll become available on my linkedin profile the link for this slides for after the stalking won't see this slides again [Music] and download the vulnerable software
you can we can find these this is rides on my linkedin profile so now now let's see the video park
let's see the video park let's open the vulnerable software easy file sharing web server is running on part 80 let's open the debugger remove file attach let's attach the vulnerable software choose enable software and clicking attach
clicking button run to running run the enable software in the debugger if enable software is running let's open the exploit code vi here we have a title exploit code is exploit code in python variable crash world for what amount of its characters this about amount of characters will say against the entirety with objective or because crash vulnerable software will send a method get get plus crash world below we have attacked ib tracked ip impart 80 this a lot amount of characters was generated by two pion create let's get in in folder usr sharemx sprite framework tools exploit and let's execute the two panel create with panel create dash and rank five thousand and we have here a lot amount of
characters we will copy the seventh amount of characters any place in our exploited code for after sending this out amount of characters against the entirety with a predictable cause crashing vulnerable software copy paste
let's save the exploit code
let's send with title x correct on two send execute the python sprite code and in vulnerable software we have the flow of execution powered acts violation click menu view sch8 chain and we have a very available now we learned we need we need to find it what's the offset of se e8 what's officer c8 for finding the offset of se8 we use a two pattern of set we should type which we must type pineapple set dash and link 5000 is a link basically and we must type the value of sc 100 46 35
66 46 this is a value obviously of s800 and we found the office 30 4065 4065 is offset for our sc 100 let's open the exploit code open the exploit code and then we have here variable crash world character a multiplied by 461 plus b multiplied by four plus c multiplied by four we will overwrite we will overwrite the
operations because these are functions that do nothing night is an open do nothing function let's do nothing
so let's restart the debugger
click button world to run the mundane debugger
let's execute the pytech sprite code
we have here axe violation again click menu view sc chain and here we have the sc handler a variety by 43 43 43 and the address override by 42 42 42 real variety real variety the 300 clicky write both to follow address in stack follow addressing stack and as we can see we override the 300 we have here pointed to next sce recording with bbb and the sc holder if you see ccc we overwrite it the sc 100 so now we get a control we get a quarter of a 300
we get a code of s800 because we overwrite as he heard with bbb ccc
let's open the exploit code now we need to find it an instruction pop-up return for this illusion we must type in command by exclamation mark sc8 exclamation mark sc8
clicking menu view log and as we can see here only the first 20 pointers i show here for my point is open se8 point text so let's open the sc8 file local disk c programs file immunity immunity debugger let's open the file sc8 s80 point text and then we have a lot amount of address we need to find some address that make pop-up return and we secure mechanisms as files we use iris 1003 fe we use address 1003 fe this errors is a pop eci poppy di return if secure mechanisms asadi is files rebates as false safe sc8 as files or spouse we could use the other address but i'll choose this address then there are the
automatically this important that is pci pdi returning with secure mechanisms pci pdi return if it's equipment can easily sndr is files with maintenance files save sc8 as fast for us as files this important that it has secure mechanisms false in the er expert equality we type here we create a variable se8 if you value feed your 3-0 world then this address is for pop-pop return then there are three fe and we type here when i can do architecture 8x86 is uh address fv0300 well there is a address for pop-up return now we need to find the eins up code for instruction jump shot shorty jump for this we use a two nas michelle we use a tunas michelle for finding ice
up code for instruction pop up for instruction charity
of destruction shorty jump now we create a variable in sc8
now let's type in asthma jump shark eight jump shot eight we found the apocalypse eb06 if b06 is code five jump shorty eight again b06 is our code for short jumpy 8 we must we must create a valuable any sc8 for short jump we type x 9 90 x 90 loop in oop and the view execute xb 0 6 is a short jumpy 8 so we put available questions character a multiplied by officer for the in for the se8 51 it's officiated for se80 plus any se80 plus se80 plus [Music] noobs that is 90. so we execute pop up returning and it will return for the short jump and we will security new penup eb06 eb06 is a shorty jumpy
aid so let's save this exploit code and execute the exploited code to see vulnerable software
we have valuable questions for character aim multiplied by officer of the c8 plus nsc80 plus s80 plus 90 that's a loop let's save the exploit code
let's restart the debugger
restart him with a burger run them under the burger run the vanilla soft moon of the debugger
software is running execute the exploited code
the flow of the question stopped click menu view sc80 chain now we have a very re sc 100 writing button follow address in stacking and as we can see we have it sc se80 recording of variety with charity jumping 0 6 eb 1990 and the s800 a variety of address of the pop-pop return understand the world through sc 10-0 you know three fe is a address for pop-up return and he pointed to next as he recording we have a short jump 0-6 it be 1990 so now we get a quarter of a ce recording again we get a culture of se recording and now we override the series required with shorty jump in the sc holder if we
pop up return
let's click if we write the bottom go to expression and let's find the address 10 year old rotary fee and then we found the interest 1003 fe it's a public property returning poppy ci popping the iron the returning crease right at the bottom breaking points toggle put your bracket pointy poppy ci we put your bracket pointy poppy ci
let's pass 4 of execution 2 with shift f7 click button 1 and here we stopped in pop ci we stopped the flow of execution embedded party pci for so let's click f7 for press pci f7 to best pop the eye here we is we are in return we are in return press f7 in return f7 in return and we follow out inuke here we have new penup jump shot ib06 as we can see a b06 means jump shot let's pair the loops with f7 f7 and the f7 you'll be short and we we are in oops we are in loops as we can see we have a lot amount of noobs but yet this isn't
enough space if i put our show code we should now put our shell code but i already know that this is isn't enough space to put our shell code so well we don't have enough space to put our shell code we use a technique called eddie hunter
in our case we don't have enough space to put our shell code here for this we use a technique called aggie hunter
let's find let's learn hunter
as we can see about the pop-up returning now we need to find the moodle instruction pop-up return this instruction will as shown image below make a return to departure to the next sc8 recording the pointer to necessary to record will variety with a jump to our shell code to get a reverse shell here in flow of execution we have asked variation activation credit sc handler so in korean the c100 will execute pogba return and you will make a return for pointer to next se8 recording imported to necessitate record we make a short jump to our show code point it to next city was a variety with jump to shell code so again the flow of the execution is running
vulnerable software so cause acts next variation in current sc 100 we execute the pop pop and return return for short jump so we'll execute short jump for our shell code here shall code real executor shall call to get every shell but as already say already said we don't have enough space to our shell code we don't have enough space for our shell code in this case we need to use a technique called the aggie hunter
so we know that we have a little space to our shell code for this we use a technique called egg hunter egg hunter is a small piece of shell cod which search for 12 bigger shell code which the attacker was not able to feeding the available buffer space for this make use of this little piece of shell called aggie hunter to have directed the crucial flow to show called it bigger so saying better the egg hunter is small piece of shell code that will make directors for a bigger space in this bigger space we are secure put our show called together racist show so remember again we override s800 we operate to see hundreds with
pop-pop return in the short jump will execute pop-pop return and return for short jump short jump execute short jump shark and the fellow out in our loops in place of it is loops we should put our shell cold together shell but in our case we don't have enough space we don't have enough space to put our shell code here for this we use a technique called ali hunter any hunter is a techniques where in place of this noobs we will put him a small piece of shell code we will put small piece of shell code called egg hunter that will have directors for a bigger space where in this bigger space we can put our shell code
to get a voice shell let's see it in the video part
in place of this loops we put our egg hunter we must type in commanded by exclamation mark
and do we have here command again the comments of eggy we have the full value is root we use it afterwards after we learn what means this root and you we must type extremely shamona egg for find the eggy hunter shellcode and we have here eddie hunter shellcode let's copy write a button copy to clipboard whole line copy this edith shell code and paste in our shell code and paste in our exploit code
copy this small piece of shell code of aggie hunter and the page in our express code let's open our exploit code
we have here already basically i heard the right bottom page selection we have here a shell called a small piece of the shell called the egg hunter we put in variable crusher crusher character a multiplied above set of a c80 [Music]
press in sc8 process e8 plus 90 moves multiplied by five
first egg hunter plus knight noobs
oh
and we have here payroll 2 equals bad shards we have here bad shards we will send against the target this better size this value is since zero world op f f c c zero up f let's learn more what the functions of this better size
now we need to search for bad characters depending on the application type of vulnerability any protocols you use may be set in characters which are considered embedded and should not be used in our your buffer or shell code one example of very characteristics is a zero zero this character is considered badly because a nubrite is also used to terminate a single copy operation which will introduce our buffer whenever we see a number japanese so has some values that for our vulnerable software are considered bad for this
for this we will send against the target this value is since zero up f to see if you cause some error in our target we want to change zero zero because i already know that zero zero is a very characteristic but already we we needed to know if he existed others bad characters for this we will send the scenes 0 up ff against the target for seeing focus others errors
if of course others errors mean that it exists others made characters we need to find the medicare test because after after we after we generate a shell code without belly characters we need to generate our show called together shell without the better characters here we have other agency which you would press payout to this means that afterwards rule to become our shell code after which would you come out pay all the two percent two equals many characters now we put bad characters but after we put our shell code save the expired code
let's restart the debugger
go to expression put a bracket point epoxy pointy puppy ci right button puppy ci break point toggle put your blackie puppy poppy
put a bucket party puppy ci
now let's execute our exploit code title x connect on 5 execute our exploit code
we have access relation press acceleration shift f7 shift f7 to pass acceleration
and the press f9 or
press f9 we follow out in pci press breaking point of f7 f7 f7 f7 press poppy syphopdi return f7 f7 execute the pop pop return it throw out in oops press loops and enjoy jump shot of f7 pass our loops loops and jump short of f7 here we have a small piece of shell code this small piece of shell called is our eggy hunter again this small piece of shell code is our egg hunter that we will have directors for a bigger space where in this bigger space we put our shell code together shell right button scans bracket point toggle let's put a back point in scans put your breakpoint in scans to see what
is in scans click button run clicking button run to running the vulnerable software the flow of execution with stopping is scans flow of execution will stop and scans write the button in edx write the button in the x4c what is in the x following them and as we can see we have here root we have a value here altitude this indicates that after this would will come our shell code after root would come our shell code will execute jump pdi will execute jump pdi and follow out in our banished characters we have here zero one zero two zero three zero five zero five zero zero seven eight nine
since 01 up f c 01 up f for c if requires some error informable software as we can see we have a all these values since 01 up f we have all this value since 01 up f this means that we don't have a more error so this means that the unique better characters is a zero zero as we can see we have here all these characters since zero f that means that we don't have others betty characters build the zero zero so let's we need to generate our shall cody we need to generate our shell code just without zero zero so let's restart the monarch debugger
let's restart the middle of the burger
run the vanilla soft mother debugger again
write the button go to expression let's find a poppy ci poppy guy return let's write both in puppy ci bracket point toggle put a bracket point to pop pci
let's open the sprite code
now let's edit the shell code let's select this old shell code to put in this place our new shell code for generator if i generate our neutral code we use a two msf vino you use a 2msf venom [Music] for generate
our new shell code
let's use a 2msf window to generate our new shell code you must type messagevino a octet x86 dash dash platform windows lcp payload window shelly versus tcp eddy horse lock ip party for lithium part five five five five dashes
there should be avoiding body character 0 0 so here we put dash b body characters avoided by the character 0 0 we will generate our shell coil we will generate our shell code avoiding by the character zero zero because this unique very characteristic for our vulnerable software is a zero zero so we generated our shell code avoiding by the characters zero zero
we have variable crusher character a multiplied by officer plus nsc 8 plus 68 plus 9 loops plus 800 plus loops in the below we have a variable period 2 [Music]
we have nsc8 our jump charge the b06 is our jump shot sc8 our new canopy our pop-up return sc8 our pop-up return
sc8 our pop-up return we have our egg hunter remember that aggie hunter is small piece of shell cody that will have directors for a bigger space where in this bigger space we put our shell code
so let's copy let's copy our new shell code in the paste in our exploit code
copy selection and write a button paste selection paste our new shell code in know exploit the code
have here payload 2 equals both our shall code below we have period equals other hd ultimate after all to come out period 2 two equals birth buffs as our shell code so after we the root will execute our payload two period two is because birth but fee is our show called together versus shell
so now let's execute our meta sprite framework to listen point five five five five wait for connected back execute msf console let's configure our meta sprite framework
let's configure our metasplaster framework use multi-handler setup multiplied framework set payload windows shell reverse tcp
localhost our ip we configure our metasploit framework to listing on part five five five five for our lock ib using a payroll the windows share reverse tcp tell any part of local part five five five five and the security exploit
execute exploit so now let's execute our exploit code if title x collector 6 execute our exploit code we have the axe violation pass access violation shift f7 the flow of execute is positive we have acceleration passed actually with 57 shift f7 and it press f9 or clicking button run flow of execution now is stopped in public ci we have stopped in bracket point pop ci pass for pci the i in the return if f7 f7 f7 to execute pop pop returning we follow out in groups we will pass looping p with f7 f7 and jump charge if b06 will pass with f7 f7 f7 f7 pass jump short we'll follow out in our aggie hunter we
have a small piece of shell called the aggie hunter we put right button in scans back punch toggle to stop the flow of execution scans clicking button run button run to continually flow of execution stopped in scans right about in the x right but in the x following them here we have our root this indicates that after after this watch will execute our shell code this means that after our root will execute our shell code because any aggie hunter is a small piece of shell code that will have directors for a bigger space where in this bigger space here in this bigger spaces will execute our shell code press f7 f7 jump pdi with f7
jump the i with f7 and now we have d8dc d975 this is our shell code our shell code as we can see in our exploit code as we can see in our exploited code we have here our shell code da dc d974 and we can see in our flow of execution of enable software the adcd974 is our shell code click button run to execute the flow of execution to pass flow of execution clicking button run and do we have a meta sprite we have a metasploiter versus shell we got a shell so we can type net user to see the user of victim user hotdogs and administrator user of the victim you can type ipconfig
for a cd ip of the victim is it so as we can see we have here in this slides step by step of how you can write the wrong spot code using i see e8 of variety with egg hunter technique remember that this egg hunter is small piece of the shell called that the wheel head directors for a bigger space where in this bigger space we can put our shell point to get the voice shell and the body characters should be fined should be we must change against the target this character sees the role of ffs to find it what is this bad characters for this vulnerable software because we need to avoid debate characters when we generate our shell
code so we need to generate our shell code without the body characters for
link for foreign slide for who won't reproduce this pokey you can download this slides on my linkedin profile and the executive the step by step of how can write a works party called using ic8 or variety with any hunter technique now i all prefer the questions thank you very much