Hacking Into A Hospital During A Pandemic

Show transcript [en]
all right let's go ahead and get started um thank you for joining uh welcome uh this is hacking into a hospital during a pandemic pretty fun test i recently uh had the privilege of doing and happy to share it with you um let's go ahead and jump right in um so talk for this uh you'll quickly find out when we get to the who am i my background is air force uh and one of the things a really dumb joke to start off here how can you tell somebody's a fighter pilot at the bar they'll tell you right the simple fact is that uh fighter pilots are always loving to tell different war stories or you know there i was inverted
kind of stories um and while while that's annoying for most of us it does serve a purpose for one they're really interesting uh and for two that's actually how they make the make each other better so by telling stories uh they're able to bolster each other's skills learn different techniques or tricks that they tried and then other pilots learn those going forward right so really the purpose of this call is i think we can do that more in the information security industry so i plan to do exactly that let's tell a story about a recent test i got to do a very fun test of a hospital right in the middle of the pandemic we're all going through and
from that hopefully we can pull some lessons learned i hope this presentation is helpful for both red teamers and learning some different techniques and tricks uh that i employed and by all means if you had some more tricks for me to learn or things i didn't bring up that i should have hit me up in the chat i'm in the chat right now or at least i hope so this is pre-recorded right so bearing some a major emergency i should be in the chat uh and uh you know i would love to share stories with you also though for blue teams um and primarily for blue teams here here's the attacks that you're up against
uh some of them and some things that you may not have considered that i uh figured out in this test that that hopefully you can take some lessons learned my goal is for you to have at least one thing you can go back to to your organization and secure your network right that's why we all do what we do um we'll kind of finish with some general thoughts about uh the industry specifically the healthcare industry uh and uh you know hopefully we'll we'll have a good time uh doing so so first and foremost a little bit about me so um really the patches at the bottom there will kind of give you a good rundown of
a little bit of my story so i was fortunate enough to go to the air force academy so that first patch there is cadet squadron 11. i got my master's degree from virginia tech immediately after graduating college i was sent to england and while over there i had a blast i was part of a special operations support squadron and so my job was to be dropped out of a plane in the middle of a field uh and set up a network that supports unclassified classified nato classified networks for up to 1200 people in 12 hours right so really tactical combat com type stuff where i really got to get my hands dirty learn networking drinking from a fire hose and it was
absolutely a blast my wife and i went to 32 countries while we lived there after that i got stationed in what is normally sunny florida that just got hit pretty hard by uh hurricane sally uh but right there next to pensacola actually is where i was stationed and there i was part of operational test and evaluation and so we were the uh final check of a system before the air force purchased it right so you know one of the things i got to do there is do the cyber security evaluation of the integrated air defense over washington dc uh so making sure obviously there's no cyber security vulnerabilities that's going to cause one of those missiles to
to take out an airliner or anything like that so i learned a lot while i was there the next patch there is a wall station in florida i was right next door to the cyber school house and so one of the things that uh i was fortunate to do is i just knocked on their door every single day and said hey do you have any availability any classes that are open and one day somebody had problems with their security clearance because you have to have a top secret clearance to go through that and i was fortunate enough to get a spot so i am a fortunate graduate of the cyber warfare training uh and uh while so while there the last
patch there is i was able to deploy uh to uh qatar and i was uh actually in charge of the building where the backbone of the internet for uh all troops so uh availability was obviously a very big deal just making sure that uh the generators were regularly tested and nothing went down because uh it was the tier one network so uh other than that my hobbies i you know recently getting into big green eggs so if you have any recipes for me uh drop it in the chat and i have three year old twins a boy and a girl so when i am not uh doing uh security work obviously i'm chasing them around and probably pulling
out my hair uh finally there's my twitter or twitter hashtag or whatever if you want to follow me cool let's set the stage then so this test was a major hospital in the pacific northwest obviously due to non-disclosure agreements we're not going to talk about exactly what hospital was uh but you can just assume it's one of the major ones uh in somewhere in the pacific northwest so california oregon washington alaska idaho i don't really know what else is in the pacific northwest but one of those uh and we started with an external penetration test in february of 2020 so right when uh this all started and if you remember uh the pacific northwest was one of the
entry points one of the first kind of states hit hard by it so there was already a little bit of of concern and for reasons that we will go over after the external penetration test was done we convinced them or you know you know we had a conversation where uh it expanded into a social engineering uh and then into a internal penetration test the internal penetration test was done uh late june of 2020. so uh are some representative excuse me representative charts of the various states going through um you know coven 19 at this time and so as you can clearly see you know they're spiking so what does that mean well uh first and foremost one of the uh
elements of this whole thing uh and one of the lessons learned for red teamers is availability is absolutely imperative right our job or my job as a penetration tester is to balance giving my client a good understanding of the risk so that they can realize what type of attacks they are up against and how to defend against them but at the same time uh keeping their network running is is one of my primary concerns during a test so anything i do i'm going to make sure that i'm keeping in mind availability obviously we all know not to do denial of service attacks but one of the conversations i want to have is how do you choose the right exploit
for uh you know attacks etc so um that's the stage and and let's kind of jump right into it then so first is the external penetration test again this took place in february for those who are not familiar with the terminology external penetration test is essentially a hacker on the internet what can they see from the network is networks and services exposed is there anything that you have exposed to the internet that may be vulnerable and then further it also includes things like open source intelligence so doing uh crafted google searches um searching your social media to see if there's any sensitive information uh that maybe should not be there right so um as part of the external penetration
test we were enumerating everything that they had listening on the network and one of the things we came across was an owa server um so jackpot right so owa is vulnerable to something called timing based username enumeration and so this is uh really what it looks like here uh from the attack so um you can see that first arrow points to a failed login that took the server about three seconds to respond to me uh so from that i can ascertain uh that that is a invalid password attempt and it is not a valid user because as you can see with the second uh log in there that that user the a clark user for example responded
in less than a second still not a valid password right but what i can see is that that is a valid username so um with owa servers you can ascertain whether a user is valid or not by the time it takes the server to respond um there is other forms of username enumeration out there of course my favorite is just when uh you go to a type in the password it says this is not a valid user right that's the easiest um there's tools that are available uh primarily this right here is a picture of metasploit but there's also uh just using burp professional where you can enumerate things like the time of the response the length of the
response you can even do keyword searches uh for the uh invalid error code for example uh and in through that you can develop a list of of common users right so the first thing we need to know is what is their username convention so uh the first thing we did for that is we searched google and i'm looking for anything that ends in their domain so at hospital.com for example um so just doing crafted google searches for at hospital.com and i'm looking for things that are email addresses so of course we're going to run into things like info hospital.com and careers hospital.com uh but eventually hopefully we find one or two email addresses that are actual users
maybe from their uh local local social club or they're using their company email for personal or they did a webinar and they released their email that way right so through that we can make sure we know their username format and then the next thing we do is we took advantage of this username enumeration through the time uh to validate that that's right so we tried a few usernames that are common names as first name dot last name first name straight in to last name first initial last name uh etc and through that we can see that okay we have a pretty good idea that it is first initial last name for this particular client great now that we know that the second
thing we can do is we can use all the information available to us specifically linkedin right so we go to linkedin for uh pacific northwest hospital and we can see they have 450 employees available on the network or on linkedin so perfect let's take all their names and put them in the first initial last name format and now we have a list of 438 potential usernames great let's take it a step further though uh and let's take a list of the top oh 1000 most common last names and try every you know alphabet character a through z in front of the most common last names you know that gives us a list of uh what
26 000 plus the 438 that we think are valid put it all into one giant list and let's run it through this username and numeration and develop a list of valid usernames once i have that list of valid usernames i'm going to do what is a called a password spring attack so a password spring attack reverses the paradigm of a traditional password attack right so traditional password attack i might be doing the username administrator and uh trying the most top 1000 passwords or something like that uh trying to guess whatever that administrator password is uh in a password spraying attack though i'm reversing that paradigm instead of a thousand passwords with one username i'm trying a thousand
usernames with one password so this gives me several advantages one instead of trying to guess the administrator password which hopefully knock on wood is a secure password i'm only trying to find the weakest link so all i need to do is find whoever has the weakest password in the organization uh the other thing is i can avoid things like account lockouts uh you know account lockouts if i were to type in the wrong password for one of these usernames more than i don't know three times it's gonna lock out the account right uh but if i'm able to do a password spraying attack the end result is one invalid password attempt per user per time i run it right so
as long as i'm doing this once every 30 minutes i'm staying way below and we actually ran it twice every 30 minutes but that's still way below the account lockout threshold and lets me search for whatever that weakest password is without necessarily um ever locking out accounts probably not being detected the simple fact is most organizations or most alerting systems don't alert to just one invalid password attempt they should because it's actually 26 000 invalid password attempts from one ip address but each of them is just a unique username so it is not actually alerting so great so now i'm searching for the weakest password what is the weakest password well as you can see here i'm trying
spring 2020 and that didn't work and so let's try winter 2020 and again this is in february so oh what do you know we have successful login right so here's the thing when you're making your users change their password every 90 days you would be amazed uh probably 60 of the time one of them is going to have the season and the year why because it meets the password complexity requirements it's long enough and it's easy to remember so users are doing winter 2020 spring 2020 summer 2020 fall 2020 et cetera uh simply because they don't have to think up a password it's too hard for users to pick up passwords i guess right so
uh great now that we have the owa login let's log in and see what we have oh ephi oh man this is a picture of power chart which is what they use for their hospital records that's probably not good right so great we have a good finding the hospital is definitely going to be interested the fact that they have this exposed that their users are sending you know sensitive information back and forth um etc so great but i want to do further right so the ultimate goal of an external penetration test is to gain access to the internal network right because i want to try to break in if a think of a ransomware attack would want have to
have internal access uh yeah i can get some phi on the external especially from their owa but if i have internal network access and i can directly access these applications myself that's a whole lot more information than i'm able to see uh just from this user's email so perfect so my next target of course is the vpn and their vpn had multi-factor uh authentication right so close yet so far um you know a random disclosure here jarissa this is just a random picture i found on google right so don't don't be trying to risk that with winter 2020 and and uh you know hopefully she doesn't actually have that password but uh uh so we logged into the vpn and
immediately we're prompted with uh entering a second form of authentication right multi-factor authentication so we weren't actually able to break in there so this is great this is the strength for the report um so let's go on so you know let's talk about what we've already found so far so how do i fix this right so first and foremost this is why multi-factor authentication is so important we'll talk about it again when we get into the um into the social engineering findings right but multi-factor authentication by prompting their phone after the password attack or making a user type in a one-time password uh you know that is why multi-factor is there it is so important uh for that because the simple
fact is regardless of if your password policy was 14 characters 20 characters or whatever users are going to choose i mean 20 are are going to choose stupid passwords um you know we have certain clients that have 20 character passwords and they're um you know their password is company name company name company name company name or this is really stupid right so um the fact is users are always going to choose bad passwords and that's the importance of multi-factor authentication secondly uh increase the password strength right so um it's important uh for us as penetration testers um to not give a subjective opinion here uh and i you know i have yet to get through a
uh presentation without uh the client saying okay great what do you recommend for passwords then well we always fall back on the center for internet security right it's a standard for a reason so we should fall back on the industry standards say 14 characters you know that's what we choose to do at triaxia but most importantly it has to be combined with user education you know it is far more important than the length of the password is for people to know how to choose strong passwords and you know we give awareness training all the time and i love to walk users through exactly how we crack passwords and how to choose a strong password what i find is as silly as it sounds
users do not know how to choose a strong password users are doing things like their kids name with some symbols at the end they're adding ads and thinking it's making it harder for us uh the reality is uh when we're doing a password attack and just kind of uh some some inside uh how we crack passwords that tracks him um the first thing we do is we run through every uh password list we can think of so we have every dictionary word every uh bible verse we have every curse word every sports team name uh common phrases uh french phrases previous data breaches etc and so we just run through those and to put that into context it takes
our machine about i don't know 15 minutes to run through all the password lists we have we're talking about terabytes of data the next thing we do is add rules to those so we choose a standard password which is usually a combination of dictionary words sports teams etc and we'll just change the a's to ads we'll change the fives to or excuse me the s's to fives or dollar signs right we'll add one two three exclamation point at the end uh we will change it to uppercase lowercase etc really uh yeah that only takes us maybe an hour uh so you know by adding at symbols for your a's you're just making it harder for yourself to remember
uh and it's no harder for me to guess it right so um you know the comic on the right the xkd there yeah everybody knows that right but it still holds true um and i was actually reading an interesting uh article on it and it's basically like hey even this is wrong uh you know we should be preaching use password managers right so um password managers are basically uh lastpass one pass key pass you know there's no one is the right right one uh anyone will work but the simple fact is those password managers work as in you have a single password to get into your vault and then it knows all your passwords for you
uh so that you never have to remember them uh so for example if you put a gun to my head right now and ask me for my bank password i don't know it i know the password to i use lastpass but i know the password to my lastpass but that's it right so uh one if you needed that password if i need it for any reason i have to log into lastpass first and then get access to it so uh the point is we should just we should be teaching this to users and we're not the other thing is we preach uh past phrases right so if i take the password i have a yellow
dog named spot uh and set that as my password that is way more secure than any other type of password i'm going to be able to generate because it's based off multiple words keep the spaces whatever keep the punctuation and the capitalization perfect um that's 24 characters there's no way i'll ever be able to block it if i want to make it even harder just take the first letter from each of those and then add another sentence right so i have a yellow dog named spot we picked them out in 2015. perfect now i have numbers right so teach that to users that's the best thing you can do because the simple fact is if you make
uh your password policy 14 characters what are you going to do you're going to have a bunch of people writing it down on sticky notes or forgetting their passwords especially in a hospital right we can't afford uh to have users locked out of their accounts especially in the emergency room for example so um the other thing is consider a password blacklist these are becoming more and more popular but a password blacklist basically allows you to put words that should not be used as part of a password so you can put winter spring summer and immediately eliminate those most common passwords you could put hospital like or the name of your company right and that is going to do wonders to
prevent you to prevent people from choosing the weakest passwords because as long as you can guess the weakest link i can't uh finally configure alerts right as we've already talked about there's no reason uh why anybody should be trying 26 000 passwords from a single source ip address right so configure those to you know and that's a balance right so you don't want to configure it so it's crying wolf every time there's an invalid password attempt uh but there should be some sort of threshold below 26 000 where it's alerting you okay so great so that's a good test uh and you know that that's perfect but there's no real indication in there why they would want
to do social engineering or uh internal right uh yeah but just like 2020 but wait there's more right so the year that keeps on giving unfortunately here um so we talked about they have owa exposed well the other thing they had exposed was their servicenow instance so servicenow for those who don't know is a workflow automation process right so companies use it for all types of things in this particular case they're using it to assist in their help desk so perfect through their single sign-on portal i'm able to log into their service now application and you know as you can see in this screenshot i'm getting some helpful hints and tips on uh how to set up your
personal phone great so now i know they're using mobile pass for the iphone well let me download that app and see what i can do well no i still it's not configured to my phone i have the right application but i don't have the key so let's see if we can go further jackpot okay so here is uh requesting employee services so for new employees who want to request access to the vpn they fill out this form well not exactly but it says if you already have mobile pass and you're having access issues call the service desk at this number i obviously had to block it out right but call the service desk at this number
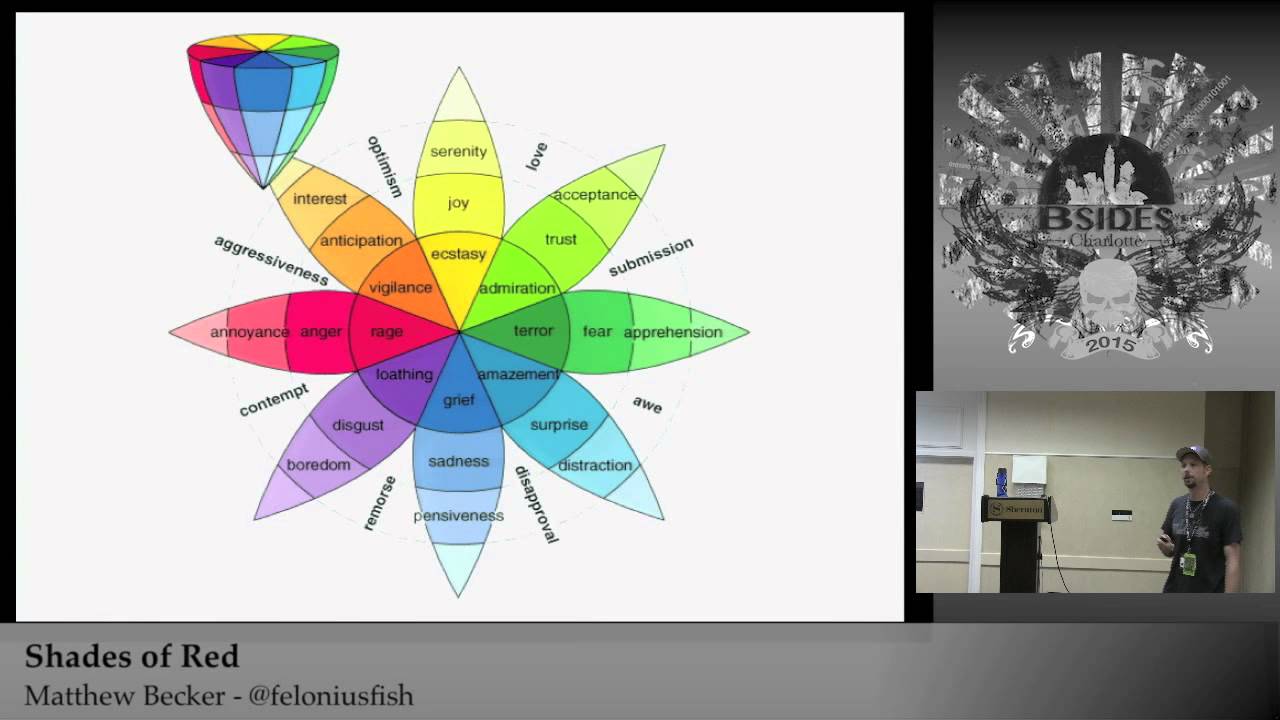
and we'll troubleshoot your issues so i saw this put it in the report and said hey i'm willing to bet uh if i called that number pretending to be a user they would send the mobile pass reset link to my email if i already have access to a user's email then maybe i could hypothetically use that to social engineer the help desk to give me access to the vpn and they said well yes let's try that so that takes us to social engineering social engineering is basically doing anything that takes advantage of the human element right so at trix and security we typically do three different types of social engineering anytime we do a social engineering campaign the first
is and our most successful is wishing right so that just like we talked about phone based um you know generally speaking we're about 80 to 90 successful when we're doing phone based social engineering uh the second would be spearfishing so taking uh all the information we have to craft a really individualized email to a user and seeing if we can't get them to click on a link they're not supposed to give us their password etc generally speaking spear phishing right around 40 successful finally we would do what's called bulk fishing and this is uh just sending out an email to a whole lot of people uh and hoping not really that tailored uh but just hoping somebody
uh falls for it right so generally 10 to 12 successful right and so that sounds good but all it takes like we just talked about is one user to give me their access and and we're in right so uh in this instance we were crafting uh this was months later right so the external penetration test happened in february and we're doing this now in june so that user password that we guessed we never longer had it so now we needed a way that we could get access to um more passwords and then we're going to take those passwords and call the help desk right so how do we do that so first and foremost you can go to google domains
and buy any type of domain you want to these new extensions and they're not that old like maybe five years old or so but these things are awesome because um for whatever reason users aren't that comfortable with them they're not seeing them that much in the wild but you can go and we can buy you know hospital.wiki hospital.website hospital.watch whatever it is you know hospital.portal training and we can go buy one of these and um set it up and it looks like us and for whatever reason because users aren't comfortable with them or whatever reason they think it's an internal portal and so they actually inherently trust it more because it's not dot com so great
in this particular instance we bought hospital or whatever the company name dot training and pretended to be a training portal so now um there's all sorts of tools that do this but we used go fish on for this particular sometimes we use social engineering toolkit sometimes we do it manually but we use that to clone their external login portal so obviously disclaimer this is a different hospital that i just found on google but it kind of looks the same as the portal we use so we clone their portal and um from that we send an email and so the email says hey new training portal actions required and uh we posed as the help desk uh so you
can see we just set up a uh google email um and that cost us i think six dollars a month but the first 30 days are free so uh good investment uh also forgot to mention on all these um uh domains here that these are a little bit more expensive right because i'm using hospital instead of the actual domain name if you get more specific with the domain name it's as cheap as like 12 bucks for most of these uh that i'm purchasing so great sending the email now uh good morning we're in the process of setting up a new training portal this will eventually be the centralized portal for all your ongoing training requirements
uh computer-based training and our compliance we need a few we're in the final stages and i need i've been tasked with getting a few uh personnel from each department uh to make sure everything is working correctly to make sure your device is compatible please log into this sign in using your network credentials and uh you'll get either a success or an error message and please reply to this email with that right so they go to the portal uh and they log in and this is an example of what we see so i can see the username and the password exactly when they clicked on it etc what they see is that bottom screen shot there that says
basically hey thank you for visiting the portal you're compatible please reply with this email and we got all sorts of replies uh including uh screenshots uh different things like that so this is fun uh the other thing that you know i will use the same exact campaign with like a vishing uh phone based right the difference is uh really i'll call them and so the reason why uh phone-based social engineering is so good is because of two things one uh i'm only sending it to people who pick up the phone right so uh you'll see in the next slide my stats really get hurt when i when people aren't at their computer or never even open the email during the
time window uh and and when i'm doing phone based i will basically call somebody and as soon as they pick up the phone i will send the email right away um and that way you know obviously my stats are only based on people who are uh picking up the phone uh whereas when i'm sending an email sometimes i don't know whether it got blocked whether their it team is you know told people not to click on it anymore or whether they're just not at their desk or on vacation or whatever unless i get out of office so you know we have to count it no matter what so the other reason why though is because in a phone based again i have
you on the phone i'm going through the same exact campaign saying i'm a help desk employee uh i'm trying to tell you you know exactly what's going on your only choices at that point are a go along which most do or b directly confront me right and i you know i've had users sometimes look me up in the directory to make sure i'm a valid user which i am thank you linkedin uh i've also had people check on my phone number to make sure it's really calling from the office i say i am which usually i am which is a tool called spoof card uh and i'll explain that and i'll show you a screenshot of that in just a
minute uh and you know but then other than that they're going along with it because they don't want to say hey i don't really think you are funny story uh one of the first times i used this exact campaign uh was for a fortune 300 client right so they're huge so there's no way they know everybody but i called uh pretending to be somebody i don't know john smith or whatever right and i call and this lady picks up and she goes you're not john smith i know john smith right so what are the odds so that is one of the ways you'll get caught but most of the time they don't know everybody uh in especially in larger
organizations um so it works like a charm so let's get to the stats so as you can see from the statistics here we had we sent about 500 email exactly 500 emails and uh we got message failed to send for 69 of them which probably means they're no longer employed there in the spreadsheet they gave us is a little out of date we had nine out of office emails so we cannot count those uh 349 i just don't know what happened to them they just never even got opened right so i don't know if the user was not there i don't know whether they you know word got around and they knew not to even
open it so uh unknown for 349. but you see there 73 of them opened it and of the 73 that opened the email 65 of them clicked the link and submitted data only eight of them realized it was this booth uh at that point so uh really that's you know roughly 13 but this all happened in about 30 to 40 minutes uh you know generally speaking another pro tip for the red teamers is generally speaking when we're doing a massive campaign like this we want to try to get those emails out as fast as we can right so uh rumor spread like wildfire and we want to make sure we're getting all of our emails
out slow enough that the filter or whatever doesn't block us but fast enough that uh our emails hitting their inbox before uh they are spreading gossip around and everybody knows about it right so the other thing is i typically pick a good time a day so you obviously don't want to do it during lunch time i think in this one we try to do like 9 a.m on a tuesday morning perfect time so so great so now we have 65 different credentials and again going back a few slides our main goal is to gain access to that vpn we talked about so let's do it so here's spoof card i'm going to spoof my number to pretend to
be an alaska area code and i'm going to call the help desk and say hey i lost my phone over the weekend can you reset my mobile pass and as you can see there again because they didn't have multi-factor on that owa server i have access to their email so i'm just sitting there waiting for it i call the help desk and they say oh sure yeah we'll send it to your email right because they think obviously only uh you know joe smith has access to his email so if joe smith's asking for a reset uh and then then i don't have to worry about authenticating him so perfect i'm sitting there uh one of
the interesting parts in the high drama parts about this test is um you know i had to sit there and wait and i hoped joe was not open look checking his email very closely right because this email came in and it says hey you're requesting your mobile pass gets reset so i quickly hid that as fast as i could uh it's hoping he wouldn't see it well it worked uh as you can see i gained access uh to their vpn you know this is another random google image but we did gain access to uh their uh multifactor so um so how do you fix this right so uh multi-factor is still important right we don't want to knock it but there's no
such thing as a silver bullet so if mfa was in place on that owa server it still would have been protecting um or you know so so the first thing is mfa is important right so we need to pull that owa behind the vpn or at least put mfa on that also that service now right there's no reason why people should be accessing that without mfa maybe this service hopefully not even that you should lock it in and then have users call their supervisor if they lose their phone or whatever it is um you know it's a balance of usability and security right it always will be second uh oh and while we're on that
first mfa one just you know there is no such thing as a silver bullet in security i have gotten past mfa through various means uh just recently last month uh a client had mfa and i tried to log in with several users and i think three out of five it was a push notification right from duo and three out of five of them clicked past anyways right they're just so trained so you know obviously the one-time password is better than a push notification uh but then also with duo if you have access to their c drive you can usually get to the c program files duo and the link for uh resetting and setting up is is right there in the
configuration files for duo uh well how do you gain access to their c drive well usually through something like ps exec on an internal if i have access to their computer i won't go into too much details there but but the simple thing you need to know is that share drive or smb does not duo doesn't support it so it all goes back to the point of there is no such thing as a silver bullet in security second stop providing generic awareness training that nobody listens to right so as security professionals blue team and renting we get maybe an hour a year uh of their time and we're wasting it we're wasting it with things like um
computer-based training that nobody's listening to uh you know random compliance type talks man that is our opportunity and one of the most important things we can do to help educate our users on how not to fall for these the simple fact is with the comic on the right you know uh funny but the simple fact is that uh users are considering when you tell them social engineering the first thing that pops in their mind is prince of nigeria right they're not thinking of some of the more complicated sophisticated attacks that they're actually facing um you know that's why they're so successful so you know statistically speaking 88 of data breaches have social engineering involved so during our limited time to do
awareness training we got to make it count uh and by that i mean i love to take pictures screenshots from the recent tests we just did and show them hey you guys actually fell for this of course i'm going to anonymize it i don't want to call anybody out or make anybody uncomfortable but this is the types of tests or or you know types of attacks that they're under and they need to be aware of it how do they know whether this is really coming from the inside what type of information should they expect it to what are the procedures they should be looking out for how does an attacker guess their password right so
um we have to make that limited opportunity to do awareness training and we have to make it count because um you know generally speaking we're spending all of our resources hoping that something bad won't happen uh but but that's one of our no matter how many bells and whistles we have awareness training will only be as weak as the winter 2020 on our network right so um make that count that's really you know what i wanted to hammer home uh finally or excuse me third layer defenses right so uh generally the best thing to do is to consider you know the analogy of a uh medieval castle right so uh how many entrances do you have you know
back the best medieval castles back in the day right had uh you know the moat around them with the crocodiles in right and so uh then they also had the drawbridge right so the only main entrance was the drawbridge unless somebody were to crawl through that and then put up a really tall lower ladder right so great so that is reducing your attack surface only having the drawbridge right so then on top of that they layer defenses you know if you're able to cross the drawbridge they have you know really hot tar and oil that drops from on high on you right so uh that's the next layer then somehow they have the giant front door that's barred shut
right and then if you get past that they have a bunch of troops sitting there waiting for you right so they have layers of defenses same thing applies to defending our network we have to have layers mfa alone is not good enough next gen endpoint protection alone is not good enough you know even those two combined are just not good enough and then finally uh the third is to assume uh compromise so i recently just wrote a blog on the the hat in matrix and so that's used for injury prevention basically when they're trying to figure out how to get cars to stop crashing into each other uh they use this matrix uh that basically looks at the pre-event factors
the event factors and then the post event factors right so the pre-event factors are things like this speed limit maybe the high visibility arrows you see on on curves that are coming up the flash the stop lights etc these are all things meant to prevent an attack from occurring or prevent a accident from occurring uh the second would be things that make the severity less bad if it does happen right so even with speed limits etc accidents are going to happen right so you have to assume what are you going to do to prevent the event from being so bad that's things like safety ratings in cars things like seat belts airbags etc things that are designed to
in when the event happens to stop it quickly and then finally they have post event they understand that people will get injured in car accidents it's just they're never get to point of zero therefore they consider things like having the hospital network and ambulatory services on who's on call so that an ambulance can quickly get to them aravax uh you know etc tow trucks to get it off the road etc so with injury prevention they use the haddad matrix to look at all the different factors that lead pre-event event post event same thing as security right we can borrow that and really uh make it useful for us in our jobs yes our main focus or not even our main
focus one of our focuses should be pre-event what can we do to stop the compromise from happening in the first place layer defenses reducing our attack surface multi-factor authentication better passwords etc no matter what we do we have to assume that events compromises will happen hopefully they're small what can we do to limit the impact to them well event would be things like segmentation uh also things uh like um alerting so that we can quickly respond and deduct to it and then finally uh go through an exercise of assumes compromise or post event uh what how much will it spread uh do you have segmentation on your network like fire doors is what i like to call them
to coordinate off to just one department or one area of the network do you have offline backups for a ransomware attack for example so that you could restore uh you know etc so really you know we should apply security controls and make sure that we're considering all three layers because things happen okay moving on to the internal penetration test so now i gain access to the internal network and uh really what can i see so uh first and foremost one of the things that's changed in pin testing a lot since the pandemic begins and one of the things that we've really been challenging to improve on is not relying on the same old spoofing attacks we always have
right so uh for those who are red teamers you know net bios name service local lake multicast name resolution uh is is an old go-to right so uh that's generally a way that we can get an initial foothold on the network really quickly but during the pandemic uh what we're seeing is a lot of times is that those systems are not directly on the network or users are working from home a lot more frequently and therefore that attack surface is not really as valid anymore right so i'm trying to come up with different ways and and trying to improve our abilities to get past and not rely on the same old yes it's still a problem yes it's in the
report and you know we should make note of it um but really you know diversifying past that uh a little bit so in this particular instance who am i kidding we're testing the hospital right yeah jackpot uh all sorts of exploitable vulnerabilities are exposed and a lot of these are critical like we can see so um you know moving on to the next slide here you can see that there is um all sorts of critical vulnerabilities here so we're talking about 40 different systems that are running windows xp this is very common at hospitals they cannot update these systems because it's running some weird x-ray machine that they don't support you know whatever it is i'm also seeing
a lot of microsoft uh rdp cbe so that's the blue key vulnerability that recently came out right so tons of those i had tons of ms17010 which is the wannacry vulnerabilities so there is all sorts of vulnerabilities uh exposed on this network that would allow an attacker to gain access so that's problem number one okay so now that i have all these systems to exploit which one do i want to choose to exploit and so remember going back to this i am plugged in to an emergency room my laptop is in the middle of the height of the pandemic right availability is key i cannot afford to take down their mri machine or uh god forbid something even more
important right so i have to make sure we're keeping these systems are up and so what are we doing to make sure a system is reliable and safe to exploit and so really with that and i think this doesn't get talked about enough from everything i hear is just man there's a lot of dangers out there with some of these exploits and so you know for example the blue keep and the ms-17010 i want to cry they both have about a 50 chance of working and about a 50 chance of causing the blue screen of death right they both you know could crash the server that is not acceptable you know for a lot of our clients
and so uh really how do i choose the right one to exploit so i want to demonstrate to the client all of the vulnerabilities that i can right the difference between a vulnerability scan and a penetration test is that we do exploit where we can but at the same time we have to take a measured approach to that right so uh this just comes down to doing your homework i mean consider the reputation if you go look on exploit db metasploit rapid 7's website uh the cde itself understand everything about it including the reputation uh you know who's talking about it has it worked in the past uh is this been around for a while is
this trusted does it have the excellent rating or whatever it is additionally we need to dive into understanding what the exploit does far too often we're just clicking run without really diving into the code or anything like that and understanding exactly what that exploit does and how it does it so you know in this instance when we're trying to avoid problems on the network i need to do things like uh avoid buffer overflows right that's overriding memory that's usually a very bad thing uh so and then finally use all the information available us to make the decision right so do i know that this is the exact version that is vulnerable do i know what this system is right so an ms-17010
that has a potential blue screen of death is maybe okay on a user workstation maybe not okay on the domain controller right so use all the information about what the system is what the system's running et cetera to drive our decision so in this particular instance we decided to go with a ibm websphere java serialization vulnerability uh really that's just an unsafe deserialization call in the apache commons library uh which really just allows remote code execution the actual exploit doesn't matter that much uh the point is it was one of the safer ones with a good reputation that affected the application more than the underlying operating system uh and we felt good about it we
confirmed you know at traction security we always have engineer huddles in this instance where we uh get together with everybody who's available and say hey let's talk about this here's my options what do you think and really you know uh come up with the best game plan before we go forward so uh it worked obviously we gain access to it uh once i gained access to it i done the contents of the local sam file and so the local sam file of course holds the hashes of all the local administrators and in this particular instance they are using the same local administrator password across all of the systems you see here uh so using that i can do what is called
a past the hash attack which i'm happy to go more into if you want to hit me up on discord but i'm kind of running out of time so i'm not going to go too much into it but the point is i once you gain access to one system i can gain access to every system that shares that same password also by dumping the lsas process i'm able to read the contents of memory directly from directly from the lsas portion of memory and so this is obviously a representative screenshot in the top there but i wanted to show you what it looks like so this is mimi cats mimi cats works well except it gets
caught a lot by antivirus so you can see that the bob 1password again representative screenshot but that gave me access to the clear text passwords uh for the red teamers on the listening to this you know a lot of times mimi cats will get caught by antivirus but if you're just using crack map exec with the tac-tac lsa option that dumps the contents of the lsas which has a lot less passwords in it but they still is some almost never gets caught so i've been using that quite a bit lately uh and so anyways through this we gained access to one of their domain admin accounts i gained access to the domain administrator represented a picture of
the domain controller for example and then right so now i want to demonstrate the risk uh so we gained access directly to that power chart that we showed earlier so so now we directly have access to mess with people's medical records to mess with uh to see all sorts right i can see all i can log in as the administrator and see all the different patients in the hospital at any given time i can see everybody's i can go to the hr folder on the share drive right and see all the access to uh all the different salaries by the way doctors get paid a ton we're all in the wrong industry they get paid well uh and then finally
you know this wouldn't be a pandemic talk if i didn't show you here's everybody in their hospital exactly which room they're in their medical record number and everybody who tested positive for covid in the hospital at this given point right also their situation report shows which things they're doing to minimize the risk etc right so all sorts of bad bad things so uh real quickly because i'm running out of time how do i fix this first and foremost we got to figure out patching right this just demonstrates why patching is important hospitals have unique circumstances which make it harder for them but still we need something we need to be able to patch these laps is microsoft local administrator
password solution that solves the problem of shared local administrator passwords for you it's a free tool provided by microsoft that will randomly generate different ones it's basically a password manager for those local accounts it will automate it for you go get that that's awesome that is a good link there on how to stop the memory from storing clear text passwords for example that lsas and the mimikats we talked about and then finally segmentation right so i already referenced it as a as a fire door but in this particular instance it was important for the um it was important for the client that i mentioned that this uh where my laptop was was essentially the same as if i walked into the
emergency room and plugged it in right in the lobby right so they don't have proper segmentation and they don't have proper port control so anybody can walk into that hospital and do exactly what i just did pretty scary stuff segmentation is basically going back to that assumed compromise you want to go and you want to put fire doors in place using strong access control lists such that if i compromise one area of the hospital i can't get to every area what i recommend is we start with our most high risk areas right so the domain admins should be in a separate vlan yes they need to reach out to everybody but nobody needs to reach them that way
i can't dump the contents of memories okay so with my little bit of remaining time here let's talk about uh hospitals have a real problem right so i went to the top five google searches no kidding this is just one through five results when i search for employee login uh excuse me hospital employee login this is the first five results that popped up for me so first ui health starting march 10 2020 you'll have we're gonna start doing duo two-factor authentication first of all thanks now i know it's duo second of all what was took you to march of 2020 that's a problem right next employee logins in the top right there first of all they are showing me all the
different chronos self-service login the webmail login etc that's really convenient thank you also i'm wondering if that's the same situation i ran into with my hospital where are all of those protected with multi-factor authentication uh you know finally that bottom right one well thank you for the phone number uh for the service desk uh and there's all the possible logins i would need right so great uh the next one here's the vpn here's the internet oh by the way if you're not using a company computer you have to use this link to get into the vpn thanks need that also possible denial service it says on there uh when you uh when you're done uh please
disconnect to let others connect well okay so that sounds uh like a potential denial of service and then finally my favorite possibly is community health gives me the entire list of representatives who are on the phone uh and so now i know exactly who's working their their help desk their i.t support so that's very helpful for maybe that social engineering attack we talked about so uh hospitals in general have a crazy need for availability they need to be able to access their systems they can't afford downtime they can't afford a emergency room doctor not being able to log in they just can't do it additionally as we've already talked about some of the operating systems and
applications cannot be updated for any for a variety of reasons because the applications only run on server 2003 or xp uh additionally they have increased demand for interconnectivity and sharing they need from the operating room to send the results down to the lab and that to be shared immediately and there's a whole lot of health reasons for them to share data back and forth and it's super sensitive data and then finally they have all sorts of shared workstations right so the nurses all use the same computer or same three computers etc they also have shared user accounts which prevent non non repudiation so i don't know how to solve it i want to open a conversation about
this because you know i've lost sleep over this uh but generally you know it's pretty scary stuff so here's some things that i can think of that would help it one segmentation or even micro segregate segmentation right so um one of the things i proposed in a small business initiative thing a while back when i was a blue teamer is a micro segmentation device which is basically let's put a a raspberry pi type machine that has a whole lot of security tools like a next-gen antivirus and a host-based firewall in front of these systems uh and so there's a uh you know a one-to-one connection between the xp machine and this device and then this
device could make smarter decisions about what data is necessary and what data is not necessary um so something like that just a micro segmentation to try to prevent it getting rid of passwords in the hospital so you know when you go to a bar uh or a restaurant a lot of times the receptionist just swiping that right to get access to the the console so stuff like that would still allow for quick availability without uh having the password like i saw the password emergency one a thousand times during this test um additionally things like in the military use a cac card and a pen so it's just four digits but you at least have the cap card for that multi-factor
uh we've already talked about awareness training has to count and then increasing the incident response capabilities i created a domain administrator account on this and they never even noticed so you know it just we have to work together to make this better um interested to hear your thoughts in the discord chat uh but i'm out of time for now so uh loved having this conversation with you uh hit me up at any point i'll share my info in the discord chat and we can talk more uh wish we could grab a beer together or anything but uh you know hopefully next year we won't be virtual thank you