Shades of Red
Show original YouTube description
Show transcript [en]
so I try to keep this short in this 200 slides really quick about my that's me many years ago i've done pen testing red teaming wargaming i have a different industry than some people I've worked in retail or working in retail and finance I have also worked in local government but in addition I spent 17 years in the United States military I started a computer as many years ago on stuff like this and then somehow ended up doing stuff like this if you don't know what a corpsman is especially marine corpsman they're pretty much double docs they look kind of funny and they stand out but you tell them you tell marina de about their dog so when
the peacetime was around when there wasn't bad things I played games like this played with nuclear biological chemical warfare hot days and prepared for disasters like this good good good you all wanna know really what this is about talking about four games and one of the things that always happens either the military local government or anything else if you're not talking the same speak how do you know if you're still talking to same stuff we could go out there and talk to linux people and then you have a Microsoft person to spend more time trying to figure out just the commonalities and the differences than anything else so it was we dive into that we'll talk about what
a red team is and you want to hire one again back to that level setting we've got vulnerability scanning we've got pen testing we've got red teaming right here is probably where some people get a little heart there hurts feel it feelings but I wanted to define this for this conversation as well as the people we work with I heard mojo talk about how many people know about pen testing it's not a common thing so we're going to break this down we'll talk a little about their skill sets and their advantages not saying any of this is not valuable but they have their place vulnerability scanning is usually general to specialize depending on what you're going back for mediating
troubleshooting that understanding its automated you can go it across the enterprise it's fast but it's usually around an application or some type of software it's not going to do all the other things and its signature dependent just like antivirus it's what's been defined there's an 0 0 day we get a little bit deeper into the thing we've got pen test can be general can also go into specialized areas there are some people in here that have skill sets that I will not even touch I will never say I'm an expert in anything it's crossbred it's got an automation it's got manual testing it does do physical and human as we've already talked about social engineer but it's always that cause the
end result is really around information security it's slow and low the challenges is the scoping a lot of times they want this done in one or two weeks you have to learn environment turn back around and explain it to someone in two weeks very hard to do and there are many well defined industries out there have done this if you're looking for if you haven't done any of this i definitely look up some of these it's defined doesn't mean it's in a box just means it's defined then we get into red teaming red team is a total different animal this comes actually from the military comes back more from the Cold War red versus blue and actually having
that fight this is where they bring in everything this is that full a team this is orchestrated this is not just one one team this could be a multiple aspect ronik ethnicity I'll use that word so someone can drink cyber side as well as physical they do human engagement to mimic that they also do opt for which is operational form immense these or other military forces and they act like in Iraqi or Russia or whatever but this is everything social engineering and what you're going to touch making sure that when you get broken into and all your stuff stolen you're already prepared but we also find haystacks we find those needles but we also find those huge areas make excess
of center of gravity that will take down that one application that's been sitting in the back end no one's paying attention to because you know what it's running it's an old mainframe you take it down guess what you can't do your business we also find those elephants one other thing I'll talk about the shortly there's a little side off of it depending on where you come from
vulnerability scanning is what penetration testing is what red teaming is question is are you ready or are you not I can't tell you that I'm not going to tell you exactly what a red team is to to make it to find it's going to be what you need however you need to know thyself not really just anything else you need to know exactly what your business does if you have no idea what your business does you're already failing you also need to know where everything is as well as where your controls are and have them deployed and yes we've all seen this horrible thing and we all know at cissp and it's chuck norris approved as well but there's
other things other aspects that are technologically induced that fit into this which movement be information security be business security if anyone in here in a financial industry I'm not going to ask this is what you're held to this is basil this is what the stakeholders and those high-level CEOs are held to to make sure that they're able to run their business this is what the federal holds if you look at this and dig large enough we could just take the stock market the stock market's run a lot by by using network time that time base if it goes off just by seconds changes the chance for someone to get bids that can change an industry you can
change the world then you have an understanding of fully how to deal with all these pieces because if you brick we come in we tell you you're all broken and you don't do anything with it we've wasted our time and we don't know what your ruler is it's going to be dependent on you and you have to have that risk but I don't know what your risk is does anyone think this is risky what about this what about this guy here looks really scared over here but he's got a rope versus this guy or if you're really daring who would want to do that I don't know what your risk is I can tell you
one thing my background in life and limb was totally different in time of war the minimum the green was the people I would worry about first I try to get people back in there to fight in civilian world it would be the immediate the Waldos in black well unfortunately there was only so much time we had this could be your other risk just people throwing money or for this gentleman who's in a lawn chair flying over Iraq is that your risk I don't know but before the war before we come and tear you apart and you're not ready and make a sad you have to be ready the other thing I want to talk about is you can all see a little bit
older I've been doing this for about 20 years I grow up in this time frame where this was the cool technology nowadays we can spend all day about to do this and look like this all day I wonder what sound he's making that's all I want to know and as technology moves forward who knows what's going to happen I don't know if anyone's noted this but I'm also kind of another side of geek it's kind of cool so let's talk about a red team person they're a little insane because they also they have to know a lot of things they have to know what your business is they have to know the technology which and the the adversary
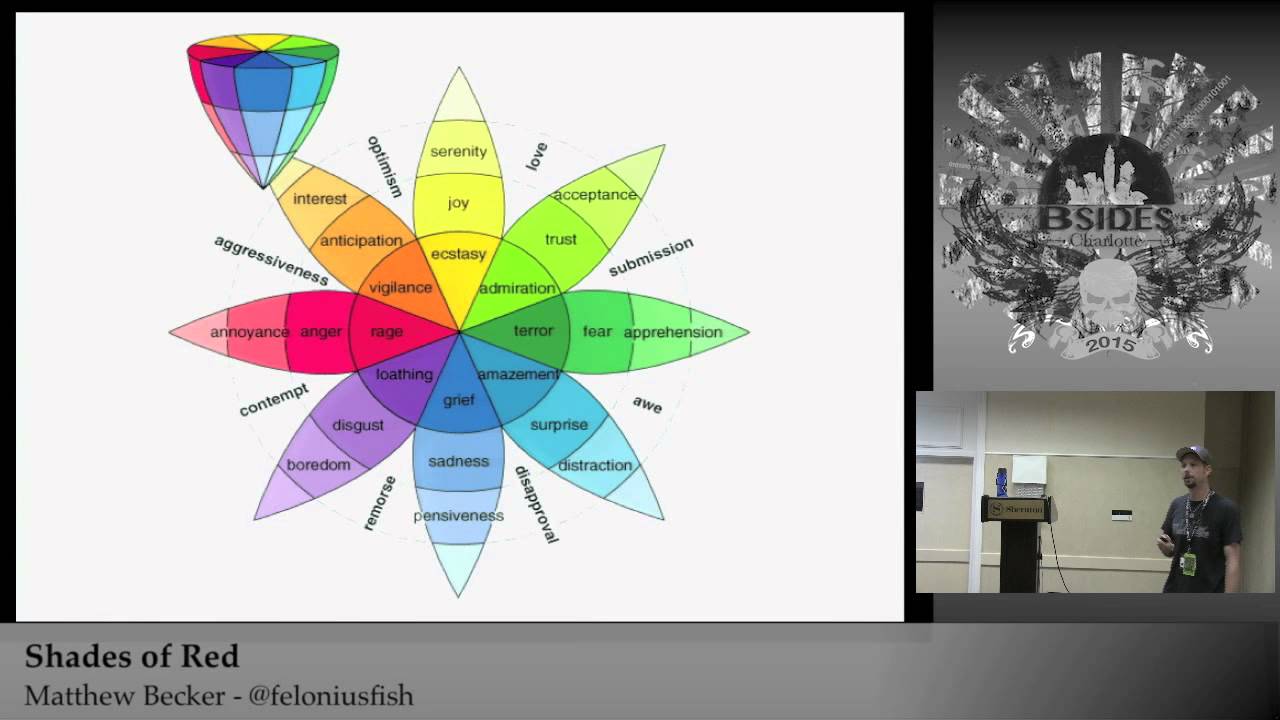
in itself we'll talk a little bit about the adversary part you need to know what is that what's that motorists operandi what exactly why they doing it what's the cause it's that why this person's no reason is different from these reasons taking it a little bit of psychology this is Maslow's law it will not go across the whole world but it does straight a thing that here at the very bottom you have to worry about your survival if you're in a survival situation you're not going to be worried about how pretty you look you're going to be worried about getting that food in those things as well as you move up to this there are certain
triggers but as a human that you have to do also back from the Cold War there was a way to try to turn spies what they used is they tried to figure out what were those triggers and they put that as mice so if you look down some of these crimes it could be a combination of these but if you look at it you have the money you have that necessity back to that survival what did you need to do why did you rob that bank or why did you rob that liquor store because of whatever that causes the green could be it it could be you decide to do criminal college causes because you want to be
rich as well as vices it could be that you have something you're trying to cope with that you need that money same thing in patriotic in the ideology this is that want that feeling that that that call to action we've got Patriots in which we've seen enough on the CNN and from either the uniform side or religious cultures as well as we got Julian Assange and the list goes on from there and with the whistle blowing and then we get into cohesion and when you start talking about corrosion and blackmail and particularly having an inside red team that gets really scary when you start talking about the possibility someone coming and kidnapping your kids in those areas it's
a hard conversation to have but it's real and it's been going on forever ego as well same thing it could be anything from curiosity Morris worm how many people are familiar with the Morris worm okay 1986 the computer buter computer abuse act was because of that Morris worm was basically a curiosity to test out this this worm that took down half the internet at the time and you can map those to those people what you're doing is you're now getting an understanding of why what exactly they're doing this not just someone say I do the scope I want to see if thumbs vulnerable what is their intent did you piss them off on the outside or is there something that
you're doing that they have that its value then you take us a little bit deeper you start looking at it and we'll start at the top here we look at the holistic time frame to do a cross-site scripting may take seconds but how long did it take you to find that how long did it take you to validate that to come up and craft that whatever that exploit is that's a simple one what if you want to do something more of a Jack Bauer it takes that time period to do that as well as is it repeatable then you start getting into finances and resources how much money you have is there a particular element
or whatever is required to do that attack that is not local in your area you have to go procure that or someone has to build it that takes that time your skill sets you have to do a gap analysis of yourself where you at now what do you need to learn as well as partnerships collaborations and levers it goes back to that that partners if you have more people joined into it it's easier then you look at how they're now they're actually doing it if you're going to do China look at what their paths are what are their what's their regular pass to use their tools they use then there's always the great debate between the the pirates and a ninja but
really what it illustrates is do you want to keep that money or do you want to go to jail do you want to be covert or overt and then how many adversaries do you want once you figure that out it's very dynamic so what you do is you spend most of the time trying to figure out what you've learned what's your rules of engagement what you've seen from oceans or what you've engaged from what you've learned and you keep making this decision over and over again it's not simple it just keeps going and going in addition every test you do you rinse and repeat you do this scientific methodology over and over that's just the adversary side then we get to the
business we need to know what you do what are your drivers what is key to survival for you because that's the keys of the kingdom we also need to what's important what's the most important what's least without having that we could be hey here's a vulnerability or here's exactly what we found as an exploit it means nothing to them you waste your time you also need to know what's good or bad and their worst case scenario what keeps them up at night so now we talked a lot about it and some of the things of if you're going to hire here are some keys that you should you want to do either if it's an external or
internal one you make sure that they have clear objectives they know what their scope is or not first of all it's also very it can be very perceptive if you do something you think you have the right get-out-of-jail-free card and it's interpreted the wrong way you could be sitting in court so there's part of that being played you also need to focus on quality not quantity this isn't something you just spit them out that's what the scanning czar for pen testing can be done as well depending on how flexible you make it you need to accept that challenge into criticism you need to learn lauren and lower you also need to synergize and partner having that
that report sitting somewhere is not going to do anything you have to figure out how to collaborate how to educate and change that culture and then be loyal to that red team having a lot of sport for that red team will give you a lot of value and have and give you some intense stuff and for those fellow red teamers right tool right skill right job pay attention to detail remain humble remain loyal that's key you have few if you build a red team and they're not ethical you're going to have a larger risk you've induced the risk plan rehearse rehearse synergize and then give back to the community the other thing I want to talk about is there are
number people talking about from the artist perspective red and blue makes the color purple it does but if you use a term from the military it goes actually back to this is the NSA and we can use that word if you want or not but this is really there OPSEC this is operational security and this is actually core to a lot of the criminals who do get caught because they don't look at certain things as I understand it and I'm not an expert on the Silk Road but he was caught because his instant messenger closed while he was in a store they could tell that that was the person who closed this laptop because he logged off and that was his
catch he didn't know who was around them he didn't make sure he covered his tracks that i think is it but i do think the synergy is put important as well as you've got to find that balance if you tell too many secrets outside or you're talking your friend and saying here's the vulnerabilities who else is listening and then you have a sad red team does they I want to talk about is semper Gumby it's once you have this plan and all changes so now going back to the war games perspective we talked about this a little bit does anyone want to play a game because you all seem kind of tired I've got the lucky of trying to wake you
back up and I hope this will illustrate why red team is important but the first thing I will say is I'm not going to say who or what or bastardize anyone on this this is an impact of it but right now this particular story has so many political stories I'm not diving into it and everything I gathered here is only from Intel that was on the line I don't have any other information so today is November 24th it's Thanksgiving time period for all frickin happy come on be happy and won't wake up people you're thinking about your turkey or if you're vegetarian your tofu turkey so you're standing around you getting ready you're thinking about leaving and you hear from
this reporter there's some information about your company online well this turkey that you are dreaming about has now turned to this and now you're feeling like this so the first thing you do is start working really hard to try to figure out what exactly it is damage control well and this is a great conference for the conference for this all your windows devices decide to lock up on this and you just stare and do this what do you do go to help desk well they get to work while you're stressed and you have nothing else to do you go and decide let's go hang out at the water cooler because you know what if she is broken
can't do anything then you hear about this you start feeling like this and you wish you would have did this two days have gone past you're starting to find out some information that's out there does anyone tell me this is good or bad just feel good you feeling like this then and this is me this is this is where we start shifting outside of technological you spent how much money on making these movies some of these movies have not even been released yet some of these are targeted for August to fit august of this year guess what to free free I tell you so you spend all that money and you're worried about your budget you're not getting that back and
your boss is usually like this you've got to work through Thanksgivings more like this and you want to do this continues start finding more information it's getting worse this is not even within your business now you're cascading outside of your business now you're affecting other people and they're like this in addition all your social media is getting compromised by this time this is what you're really feeling like continues the Calvary runs in and you receive this email and let's save you guys a time to read through these because this is important started talking about terabytes into information really right what's the biggest thing and it says GOP d and this is important in this case more data is going out yay
this is what you're seeing ask your finance officers what they'll think about that ask regulatory is what they're going to feel about that yes continues and a DAT to add salt to injury here's your global security guidelines of exactly what to do and all the people who've took training and their addresses and their passwords again you're starting to feel more and more like this and then screenshots like this go up online again what you can do pretty much with your network is this now wait you start getting more emails and this is why I think it changed if you look this is all sony but right here they started going after something that changed they went after your family and
when you do that you play with hearts and minds we all have certain things we were we talked about earlier we had a conversation about social engineering and the emotions but when you feel like this what does your team do there's nothing else you can do in addition for those hackers out there who or those who like to keep their privacy their network which takes a lot of work for them to go through hotels to avoid paparazzi and all fanboys have all been destroyed because it was there do you think they want to work with them what about their employees here's copies of it with their signatures going back to more cascading ideals here's the here's their contracts
that were cascaded out of it pretty much everybody else is pissed off at you as well this is only a few days in continuing on still GOP d they're talking about the FBI they start to get a little brazen those areas to give you a second to read through that but there's still about more of so many employees besides that one of the family and they started talking about terrorism so it's starting to escalate this to me kind of throw a wrench in a question these people showed up and they wanted something totally different now for me and you could just take movies or what any other story you why would you change your motive halfway
through and why would you add complexity of this going on and I'm not going to discuss these people which was a different attack and if it was coordinated would make it even more interesting but this was occurring at the same time continuing down the streak Laura comes in they get a Christmas gift or potential christmas gift it never actually came and then again getting more into the hearts and minds as you read through this the world of fear starting to call out 911 as well as saying if you live near these houses you should move this isn't a normal thing nor am i saying everybody's this is this isn't the fear uncertainty and doubt this is just really what happened this
is a good war game story if you were going to tell a story to your CEO or financial officer there are impact their impacts in here that they can see so what did that happen well all their contractors all the people to push out your product said you know what hell no hell no what did that force your business to do this they had to figure out a new way to push everything they've done and they had to stop because of life and limb injury which is weird because I don't think I've ever would have said life and limb and Technology together but this builds into at least that impact that threshold so there's tons of Sony impacts I'll talk about a
few of them just to give you an idea this is called attrition warfare this is basically stopping someone from being able to work this is basic sunzu type stuff and I don't know if you can read that but that's how many servers three thousand computers and 800 servers is that a good day in addition while the ax-cut well the attacks were still occurring there sony employees were suing them fast forward a few more you a few months you know what's still coming now we're starting to talk into the cascading effects and indirect effects that most people have a challenge to talk about because it's hard to say we've tried the stock options and or stock and set all the stock is going to
go down once in a while it does but it's not really a good metric but the legal fines and a simple fact that one that all these are still sitting out there now continuing I I know you can find Seth Rogen's email I mean but has he changed it how many other people that are not so many employees have changed there's one of their information is out there what other attacks that have occurred so if we do the adult friend finder is there Sony attack people in there could you use that to blackmail someone at a later date I don't know in addition it's also started to hit gender and right now in day and age of female
equality and as equality is everything else this is impactful this will weigh or sway your money makers your big-time people in addition so much I have I live with my wife and my 17 year old daughter they read more of this it wouldn't influence me but I'm sure someone reads this magazine and this makes their decisions of how they look at the world what about all those people watching soap operas it's just ironic this year happened to be there 50 year anniversary spend all that time advertising and doing this for a number of years and potentially could had that cancel change your customers the people you care about and unfortunately this lady here the whole most worst picture they could ever
find ever and I feel really bad for her at this time I can't condone what she did if you haven't heard about this she sent a nice little email to a friend about this person which is really bad but look where she SAT before this incident this is Forbes she was one of the 100 most powerful women she's been dropped ask your CEO if they wanted to be on Forbes I bet they'd care this person here total different incident but he feels horrible to this actually happened to be a CEO who his company happen to have some type of foodborne pathogen this is him in court not sure why this person still there that's a
whole other thing of male and female and I'm not here to say whether you believe Sony real or not it is a Black Swan event i will guarantee and if you don't know what a Black Swan it's that one off it's the rarity it's like a 911 it could happen when it happens it's really bad but what if one of these attacks what if just the malware occurred or your doc seen this is coordinated that's what I think also makes us more interesting is it wasn't just one attack vector it was coordinated to add to the complexity this was only a few months ago this was on 60 minutes this is the old view of
what a cyber hacker was as well as this and this God actually this is more the truth and there's another interesting factor in psychology so basically what this is is this represents what's called the hundredth monkey in Japan there happen to be a bunch of scientists who are working with these particular species of monkeys and they would feed them sweet potatoes they look they learned that the older monkeys would just eat the potatoes with the sand on it but a few younger ones would actually wash it off they watch this culture for a while and a document what happened is they learned that as they started to grow up into the numbers up to a hundred
monkeys more people start to accept it what they hit that pinnacle point that tipping point not only did they change here they changed across the other islands without interaction which was interesting so if you put a hundred bunkies a bunch of monkeys together eventually you'll get some kind of intelligent design so what it's illustrating is once people learn how to do stuff will go back to will use skating Tony Hawk has set set mines and it set the perspective of Mines for people to do amazing things when I started skateboarding it was just flake flat board and that was it it just changed your mind once you see something happen to changes it but the other thing
that's also added to it is tools are getting easier anyone know what this is I do not know what this is if you don't this was part of the anonymous movement what this basically gate is gave everybody including your grandmother's the ability to do a denial of service yeah
and we can use that point but I bet when most Linux people started here youtube and google was not the most easiest way to learn how to do things now it's easy but that's very good point I didn't get into that deep part but the ease of use is there is what I'm illustrated well also illustrating is original if you went back the cost for this ransomware was up now it's free now it's free which makes it a little hard again three anyone get internet but thank you for the information so the question is really going back to what would you do I don't know you now understand the differences between vulnerability scanning pen testing and red teaming you
can take this term if you want or not all I can tell you when you're trying to explain this to people it's already convoluted you add more to it not get clarity it makes your job even more challenging and this job is very much partnerships so when you hire the man to do the full rampage and destroy everything remember it's going to hurt but it's the lesson you get out of that that you that you receive and the collaboration you put together across these attacks with this different view and a holistic thing that will save you from being this this is a lot faster than I thought for 200 slides but get out there or if you're a business person
get out there there's a number of great sites on there on red team in itself some of them come from the physical size exclusively some come from the electronic side some bring the human you need to have that holistic view be completely flexible and thank you thank you also for b-sides and for sale for having you here





