Cryptojacking Servers: The Intersection of poor patch management and ICO's - Chuck McAuley
Show transcript [en]
i struggling for looking for a term for this crypto jackin normally thinks about mining in a browser we're talking about hacking into servers and getting them to mind for you today so a little bit about me I work at IKEA which is labeled a keysight company historically I actually worked for a company called breaking point which specialized in testing intrusion prevention systems and next generation firewalls and I've now gone through two acquisition cycles and ended up at this big giant huge company that has its roots rooted in HP back in the 1930s it's a cool place though I like it my job at the at keysight is to be part of the application in threat
intelligence team I wear many many hats we've got a bunch of products that we push our intelligence out - one is the intrusion prevention testing systems another one is for application visibility into a set of hacker brokers and tasks that we make and we also feed out threat intelligence on top of that i'm part of new product initiatives when we start coming up with new ideas of selling stuff I guess and I'm a developer presenter and everything or kind of so that's basically what I do I can't really put a finger on it because it's everything yep so today we're gonna be looking at for specific malware campaigns that we dug up out of our
honeypot logs and looked into how they worked and what they were digging up and how much money they were making while we do this they all use web exploit vectors we're gonna look at some networking data forensics that you can use and apply yourself if you're looking into this stuff or trying to find out if it's in your own network we'll look at the tools taxes and procedures that are used to the pull this stuff how they land it and then how they run it we'll even be able to get some partial attribution unfortunately it's just a big giant long number that represents a wallet but at least it's a wallet and not just nothing
and to sort of set the stage for this talk this isn't to talk about how to make mone arrow coins or bitcoins or crypto kitties or any of that stuff I'm kind of a pessimist when it comes to hold cryptocurrency stuff in general because I have to look at this stuff all day so I'm not gonna get into why miners mine you just need to know that they are mining and trying to find math beanie babies and then stamp them and say that they're theirs but you don't need to be a crypto currency ninja in order to understand or keep along what I'm talking about here this is primarily an exploit development and structure tuck
so when you deploy a massive honeypot network there was a talk this morning in the same track about honey pots you deal with a lot and a lot of crap a lot of events that just keep getting thrown at you all the time our honey putts tend to be low interaction we have a couple that are high interaction in general but the attacks that we're looking at here they are all hitting our web and SSH low interaction honey pots they the guys that are hitting these things take aspirin pre approach so they craft their exploit and then they spray it out across the whole internet trying to get to you some of them use tor to mask
their source but a lot of them just sort of used some server that they already broke into before to launch another campaign to go out somewhere else so they're trying to target massively deployed software software like Oracle whatever it is or Ruby on Rails applications or Apache Tomcat or WordPress plugins are the worst don't install WordPress just make it illegal and network monitoring applications whoever thinks it's cool to have mrtg stood up you now have another venerable vector you got it keep up the date on that probe otherwise it's gonna break and then the other trick they do all the time is brute forcing brute forcing wordpress plugins joomla plug-ins brute forcing ssh brute forcing CalNet brute forcing Simba they
just bang on it all days they get a socket they're not going to leave so that sort of sets the stage about the world that we live in and what we're looking at we actually have we used this for our own products and we push this with our feet out so I don't want to give you too many details about the whole thing works cuz I could get in trouble but I'll tell you because you're gonna see screenshots of Splunk so not only do we take the campaigns recognize the attacks and then feed us thread Intel we take everything that we get and feed it into Splunk and make it easily searchable through JSON so that's really
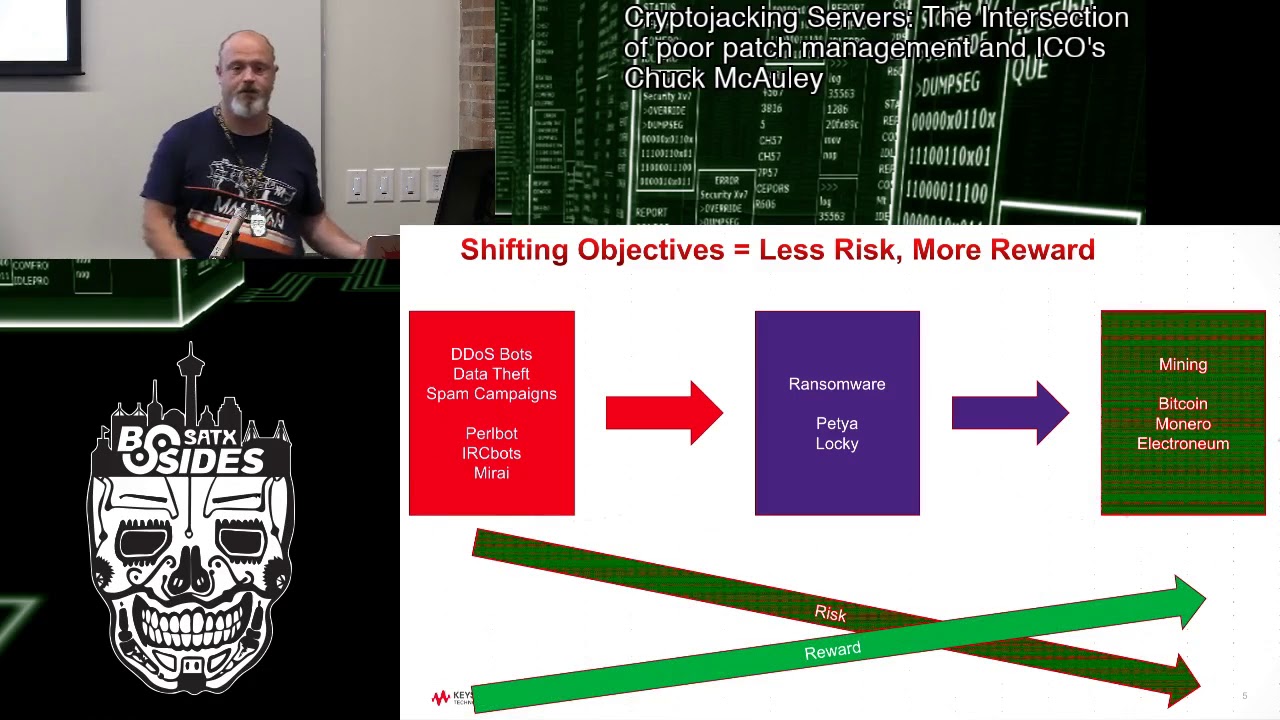
how we can easily sort of dig in and find stuff in there and look for new patterns to build and signatures for new stuff which is really neat so one thing that we sort of have observed is there's a general migration from sort of like hack in and steal stuff or use this server to do something else that's also bad all the way over to now it's just use the CPU and compute time to generate money so originally when people were doing this sort of stuff they were looking to launch a DDoS bot Network we see a lot of those govern normally by like Perl BOTS or IRC BOTS right data theft so if you are lucky enough to
land on Equifax in site you're going to take their data or if you get into target you take their data but that requires a lot more effort then I think a lot of these guys really want to put forward and spam campaigns has always been a big one right I bet if any of you guys have to do defense in your in your network environment that you support if that's your job there's been a day where you're like why am i blasting out all this data on port 25 off those PC and that's because it's a spambot now so I sort of classify all those sort of things is like Merai which is a little
different for robots IRC BOTS you know launcher script try to get the run so that then moved over to ransomware stuff there was a lot of noise made about want to cry of course but even before that petia was leveraging attacks over oracle and sequel servers to try to lock them up and demand bitcoins off of that so there's been a general history of trying to break in and then lock the computer up so this is more of a deny access and demand payment kind of approach it means you probably get paid more than doing extortion with DDoS or running spam right because now you've got a lot more people that are going to be upset that
they can't use their computer whereas if the computer is still working but poorly you might not notice and now we've seen it move over to just make the computer make me coins so what this sort of tells me in general is that what they're seeing is most of the assets that they go and break into and lock up or use for this stuff either have a poor internet connection get taken down especially on the far left probably get taken down brought back up the ones in the middle they probably end up on like people's computers that don't want to pay and just wipe them and reinstall them but this one they can just sort of sit idly
by mine coins and as long as you don't notice they'll make their money right so you sort of see a decrease in risk for them they're no longer trying to exfiltrate demand payment interact with you in any way they're just trying to drop this thing on there right on the far left a lot of these things could classify as illegal activities you break into anthem BlueCross and you manage to steal credit or socials or you steal credit cards from somewhere they're gonna go after if they can find you no one's gonna go after you if they find a cryptocurrency miners I'll just kill it and move on right and there's a greater reward coming out of this a greater
benefit in general you could argue that a cache of credit cards may have greater value but it's a got a lot more elevated risk as well so let's look at campaign one for example one this guy leveraged these were all scene from December of last year to now so even though if you're seeing really ancient CVEs this is not ancient news that I've seen this guy used CVE dated to 2012 and won the 2013 the 2013 one targeted Ruby on Rails and the other one ran was a PHP core vulnerability for a remote code execution there was also a neat little JavaScript injection attempt but I wasn't able to get the whole thing but I'll show you the details of it and I
was able to identify them all because they all had the same wallet ID so they all pitched into the same mining pool at the same wallet ID so that's the attribution part and it was a Manero classic miner or in that later so like I said this is accessible of the Internet this is a base64 object that you throw out Ruby at Rails and it runs it for you it's fantastic I wish I could get my computer to work so easily so yeah and if you base64 decode it you'll find that it basically runs crontab and reads in a script that basically tells it to do double you get for this thing called robots not text off of the innocuous
sounding website internet research is and yeah it inserts it in the cron says to run it once every minute and now we're gonna go see what the PHP one looks like and I think you're gonna be shocked to see that's the same thing so once again the details of the CVE are rather clear you post to a URL and the PHP script runs it for you keep going software developers you're really doing a good job here and then at the bottom this is that other one I was talking about this is actually from our SSH honeypot logs so we recorded a username password attempt of a JavaScript injection attempt I've done this thing I've got CVEs for myself on
this from when I was a much younger man net screen firewalls and what you do is you throw this at something and there's a web blog somewhere and it just shoves the JavaScript in there for you so it says user failed to login with authentication and it runs whatever is in there so that's obviously what that temp was I tried to grab that JavaScript I got very excited that someone else is also weird like me and looks at this stuff and unfortunately it was gone so I landed on a dead end with that JavaScript I bet you that that was an in-browser Mona or miner or something like it maybe tried to deposit a Exe so
the reason I was able to attribute this to the rest was the same URL granted other people could compromise the same server but it looks kind of suspicious especially with the timeline that we saw here so let's look what's in the crontab oh good this actually came up really good for you guys excellent so this is that robots.txt file so it's not really in the crime lab it's the script that's run first thing it does is it replaces the URL to fetch and run the next time in crontab so he's got this sort of neat persistence thing and in fact there was another one here but I didn't want to bore you guys with this same script twice but was kind of
neat is that he moved from using compromised URLs or his own domains to just using domains direct on tour so he's just hosting us on tour now so good luck finding where that script is hosted right it tries to kill off any processes it might see this one's not over exuberant about doing that and then you'll see this a lot in these scripts this is if you go like search Stack Overflow for how to mine currency the fastest this is what you do apparently so you do about justice octal x' and make your Linux kernel die or something and then we got like him trying to kill other miners that might be on the network on the system right got a got to
keep all that CPU for yourself and then it downloads this thing called dot SSH he gets both the 64-bit version and the x86 version because you know you want to make sure it'll run it was really neat that I liked here is he tries to run it and if it fails he sends a double you get to a URL that says failure and sends the user the you name in the user agent so you can keep track of his failed installations based on architecture and then make new architectures to execute and run them so that was pretty cute so we take that sshd script and this this is this is for the the young guys out
they were like how do I become an amazing hacker and do data forensics and learn Ida Pro and stuff I don't know Ida Pro I don't need to I need strings that's all I really need so I run strings on this thing and I pipe it to Les and then all I do is I search for the string Shraddha you know that Mon arrow uses stratum as a protocol to go and that pretty near there if this is a compiled binary that's got like default parameters in there then the other strings in the C object they're gonna be right near it and sure [ __ ] right there they are so you've got your remaining cool here a little bit about
Mon arrow here I'll talk more about it but basically you have sub pools that all sort of do a thing with another pool and Yahoo Finance gives it a market cap or something but basically they they sort of submit to the pool so they can pull out at the pool later and then this is the wallet that he's using to do all the mining for right so he's got a password on that pool to dig out and pull out the money later clear so far okay good so now we found the wallet we can go to the pool loan arrow hash vault something-something and we can find out that he's dug out eleven point twelve
XMR which is Mon arrow and we can see what his current hash rate is his performance everything like this unfortunately this pool later on I was trying to update this slide they now need you to supply the email address with what you originally submitted the wallets I can't find out how much anymore but this is what he was doing about a month or two ago and that becomes well how much real money is the fake money worth and at the time Yahoo Finance told me is about twenty seven hundred bucks so he made some pretty good money using other people's computers it's great here's number two number two is a kind of cute this is the
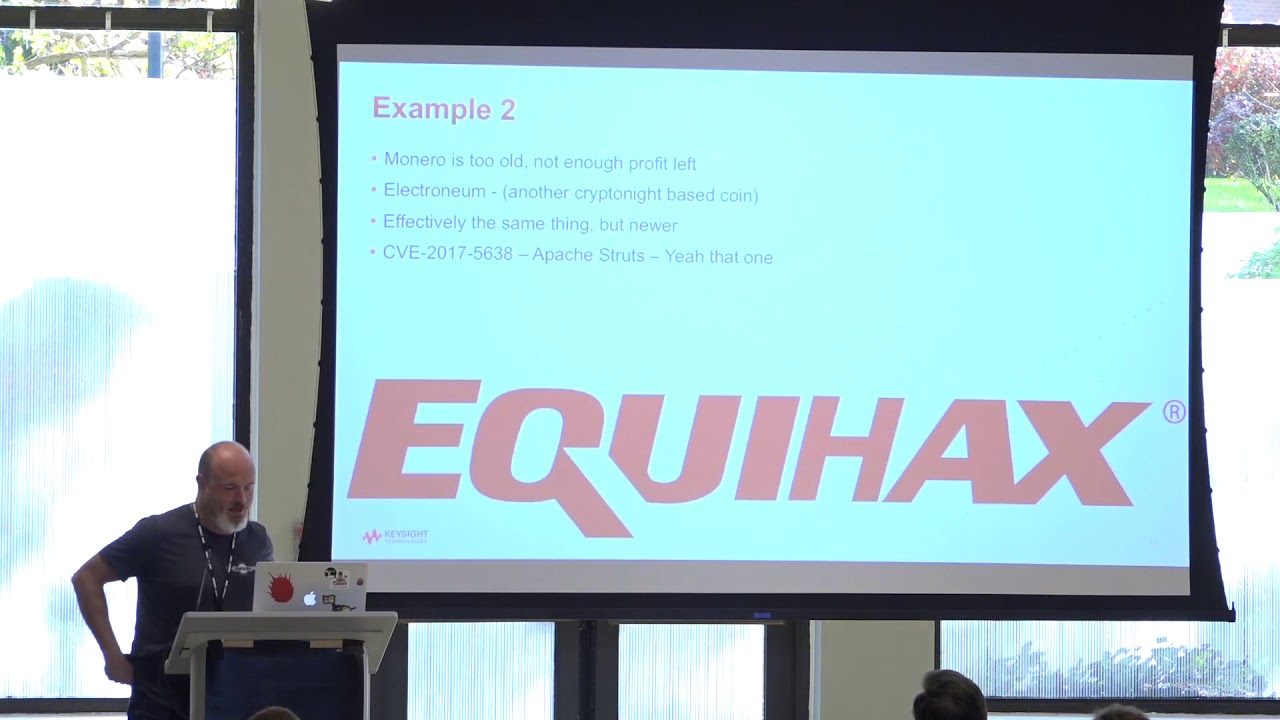
only one that's not moment Manero Manero is based on an algorithm called kryptonite if you go and whack that in the Google box you'll find out that kryptonite gets reset I think every seven days or something it's a reference platform Network if you want to make your own cryptocurrency thing you hear about how you can make your own crypto coin within a couple hours people basically wrap some api's around them on their kryptonite Baystate based network and then say here's your network so this one used something called electro neom which I'd never heard of before and like I said it's effectively the same thing and it used a CBE 2017 56:38 which continues to be a nightmare today I use
this because I look in the honey pots I look to see when they exploits stopped being used because that tells me that they're no longer valuable and they still use this one and this was the vulnerability that opened the door for all of our credit reports to no be credit monitored for us so if you're unfamiliar with this story you can google it anyway um so if you've never looked at the Apache struts vulnerability all you really need to do is run netcat on a public IP address and siphon stuff off for a couple hours and you'll get hit with one of these basically it's a DC realization vulnerability where you basically create a Java object in I guess the best way to
describe is serialisation vulnerability is that it's a combined byte code put back into source code for the java box to then make back into bytecode to run for you so what happens is is that you throw this big object there's content type there somewhere inside of Apache struts it does some magic thing where it says this is the thing I should run and all this like framing around it basically leads to I want to run exact ve or system or whatever you want to call it another con tab thing so it downloads a script and inserts it into crontab this seems to be a common way of doing this I've seen ones of these so if you see this this is
targeting Linux obviously but it actually tests to see what the system type is almost all of them do and if it's Windows it'll run you know command X E and tell me that you ran windows so collect that for data analytics later I have seen a couple try to do both offering systems at the same time but not very frequently so we go when we look into logo jpg this script is a little bit more advanced using X args and the power of pipe he kills off Apache he kills off any other miners he's basically looking to harvest all the CPU for himself and then this one just actually downloads straight up XM our rig renamed as K worker and then
passes a config file here so X MMR rig is the sort of default platform for mining Mon arrow and you pass it a JSON configuration object and then if you look inside the JSON and configuration object you get the stratum URL where to report your mind coins that you found and then your mining your wallet string so etn represents electroni 'm but this was problematic because if you just have an IP address and you connect to it in tickle it a mining pool will just report back with mining server online it's not really it's kind of HTTP but not really so this presents a challenge if I want to find out how many coins he's made but
then you can use this handy tool called passive totals which is part of virustotal it's part of Google you can give it any IP address and we'll give you a timeline of domain names I've been witnessed across the world from many many name servers tied to that IP address for you and right up at the top we see that this is new that etn pooled info so then you just get rid of those first three letters type et and pooled info into your web browser and you're on the pool and you can see what he's done so then we go see his stats and payment history if you can see here he mined a whopping
one hundred thirty one thousand one hundred and sixty eight electro Neum coins this is the same algorithm as XMR and probably roughly the same kind of compute power that he's trying to take right and this came out this lovely cryptocurrency trades at seven cents so that was only nine thousand three hundred sixty seven dollars but if someone ever decides that the electro neom is the new bitcoin you'll be making [ __ ] so this sent me on a tangent I was like what what the hell heck heck is electro neom and I went and found their website and they provided this timeline I went on forever both ways and if you go to their Twitter page it's amazing
they have this bright shiny new marketing team that were at Mobile World Congress in Barcelona and I changed the world some house and you can see here that they started an ICO in the first of September of last year and then they closed it out in October and then in the 1st of November then they decided to do some security stuff I don't know what hacker 1 US Department of Defense is y1 is related the other is but maybe someone can tell me and they're apparently meant to change mobile currency things and make you pay with your phone with their currency or something so that was like well that's interesting I wonder what the timeline
is of this guy between the ICO and when he started mining it and you can see he jumped right in in the middle of it all in September 26 so here's the thing you need to know about cryptocurrency if you don't know all the early coins all the early math beanie babies are easy to make they're a lot faster you make him a lot faster right and now like the difficulty rating for Bitcoin is up whether you need a power plant in China or something right so he just went off and ripped through a bunch of servers and made 131 thousand coins you can see like a loss of interest here as it got harder and I
went on another path of discovery here and found this place this form called overclockers UK just you know another PHP form thing with people talking about stuff and they kept they were all had mining rigs and they'd be like this week we're now mining this so they track the icos and then would switch which currencies they were mining over and over again to keep up with the cheap coins and the easy coins to make hoping that one of them paid out right so I guess this guy is sort of part of that sort of mentality of tracking that sort of stuff so yep so that was the electron IAM one so now we're on to example three this
one again is another Java bug you don't have to make your java look like that ugly o G&L stuff that you shove in the content-type you can also do it to soap with the Oracle WebLogic bug which was another big popular one so while this looks like kind of like those that PHP bug it's not quite the same thing here because really what you're doing is you're creating a Java object that then calls string passes three parameters bin bash tester see and then run curl and run it through a bash for me right and then the the vulnerable service up here was wlls w sack coordinator pork tape so it was some config problem thing so when
we go when we dig into this not a JPEG shell script we noticed that this guy really doesn't want anything else running on the computer that P kill went on for like four pages of just killing stuff off the server everything related IP address is everything related look he killed SSH well yeah well no actually that's probably trying to kill another miner looking at the relative directory so I may not make false claims here and then the other cute thing he did here was he kept trying to try to download different architectures and running them all so while counting how many CPUs he had and passing that as a parameter in there to make sure that he really sort of tuned
up the machine to run right I thought originally when I got here is like oh this is cool he's gonna try to like run the right miner for the right architecture and mine the right coin but it wasn't quite like that they all end up being just mo narrow and once again we just have a que worker JSON here so we open it up we find that he's using the domain so I don't need a new passive total and then I find Mike you guys beginning to see how this works right like it's what's once you get a pattern you get excited you just keep finding more and more of these jerks so this guy
also targeted Windows which I thought oh that's neat I'm not so good with windows so let's see what we can figure out with this so his string for this one same vulnerability if you looked at all the other framing it was all the same basically creates like a quick little visual basic script that creates an object to download a thing and then runs the thing that it downloads so what you can do with curl and pipe in Linux is this complicated and and Windows apparently but he also would also run this PowerShell attack as well to download a string called wind text which ended up being a window of EBS script to do the same thing as that up there to
download auto exe so what's kind of fun is that I have a lot of toys and a lot of friends where I work so we have a sandbox environment called cuckoo so we whack this in there and oh right there cool and I found that the wallet was the same while it is before so but then I went back and I realized if I used a forensics tool called bin wok I could just extract it out of the binary like that - so I've been walked it and I did this so put bin walk in your notebook can go download it if you haven't heard of it but this poor guy when we go and dig up
and find out how much he made he didn't make jack so he made a total of 95 u.s. dollars point six one XMR and this one is most recently so I panicked and I realized it if enough slides for my talk and I went found another one right yeah now here's example for this one's even more Monaro this was a little curious so once again he targeted that WebLogic bug wlls LSAT like the last guy he also targeted a wordpress plugin called cacti weather map which is nothing to do with the weather it's a network monitoring tool and then he also tried this weird cools dot PHP question mark ID equals if you do a google bang with that all you find
are honey pots which is cute some of them are probably mine but then here under December 12th to May 8th is when we saw the length of this campaign so it went on a long time and we identified it by the same hosting IP address there were different wallets used at different times of this though so reporters same cool so up here these are the URLs as shown in Splunk of what we found so you can see at the top these are the cools at PHP mystery ones I guess it worked for him I don't know and then we have the weather map ones they all try to download the same shell and run it right
or similar he kept changing what he was trying to download and run but it was all the same sort of stuff at the very bottom that's the vulnerability just saw the WebLogic one so if we look at this this is a Windows version of the WebLogic vulnerability and we dig in they all download this thing called miner XMR exe and it tells it to run it and then we also see this other way of pulling it off up here there's just different ways of doing the same thing really and this time I couldn't get it out of the binary doing static analysis so i sandboxed it again and it was a little frustrating I couldn't get it out but what I ended up
doing was running it and looking at the network traffic so I decided to approach this a third different way again so that I could get a handle of what is actually going on on that network so if you look this is the stratum protocol and it's run in the clear text it's not run over SSL so you can easily do Deepak inspection right in IDs rule to find this or something else if you want to find out in your network and from there you can find out who he's connecting to and you can find a wallet right in here again for yourself so even if our data forensics that are applied to this or data office Gatien that's applied to the
binary you can still just run it and look and see what it does this one didn't throw it up on a screenshot on the screen so I just went to the network data and I found it and that was kind of neat and this guy and June 8th had made 1,600 bucks and was still going strong I think that this time line right here yeah this time line right here is for the last day so you can't really get a overall feeling for his hash rate but you can see that at that point you're still making some good amount of coins over time but the linux version of his attempt remember he I said he did Linux
and he did Windows uses a different wallet and we went and dug into that wallet that he was using we found out that he'd made a paltry 0.03 XMR making sure that's right yes so you need a half an XMR in order to get your your money out of the pool normally otherwise they charge you more money this is according to a friend of mine who makes this stuff and then up here you can see I can't tell if this is some compiler artifact or Unicode but I have a feeling that this is actually some basic kind of data obfuscation in the binary because I saw capital H flying around all over the place in the ASCII
output so I feel like when it watches it probably D off you skates the strings it just doesn't do a very good job of it and so what we did was I found that pool and then sort of immediately below it I ran grep and I pulled out the wallet right here so that's how I got that one out so once again strings to the rescue and knowing the wallet size got me what I wanted so those are the four examples of guys doing dry by hacking dropping miners it's all the same stuff right it you know different vulnerabilities I guess but they're all just trying to achieve the same goal and and like I
said we see a lot of that we see it every day but there are some problems right so one arrow is difficult to mine so I feel like pretty soon they're gonna move on to other currencies to mind I got more guys are gonna be like the electro neum guy if this madness of buying these things and selling these things continues what's kind of neat though is I can go to my friend who - for actually not really to make coins but you just wanted to figure out what's it like how does it work and everything and we observe the hash rate on the CPU platform correlated it with some websites to make sure we weren't nuts
and then using basic math we can figure out roughly how many of that unit has been stolen by someone and probably how much electricity they're consuming well that'll be neat and add some more slides in my presentation so I decided to use the i7 the i7 is a little bit old it's a speedy processor for when it was made it gets about 500 hashes per second and I figured these guys don't get to pick where they drop their stuff they could land on a ten-year-old server they could land on you know my little website running on a DSL line or they could land on the mother lode like some giant AMD Opteron who-knows-what thing right
that's sitting in a data center it's all who knows where you're gonna land when you drop this stuff you have no way of knowing so but I figured if some of these sea bees they're targeting are dated to 2012-2013 then there's a good chance that the computer was stood up around there as well or maybe even older so by picking sort of this sort of it is a laptop chip but picking this sort of common denominator figure was a pretty fair assessment of everything so these are all the campaigns and we can see that the clear winner is the first guy I talked to you about you made 48,000 hashes per second consistently which basically equates to about a hundred
borrowed laptops and if you take 130 watts or consumed by the i7 that works out to about twelve thousand 480 watts I mean that's the most conservative you can get that's a laptop chip it's designed for saving electricity it could just as easily be I don't know 240 watts or something right but what I thought was really stark was when I took that out and I compared it to the the average household consumption of electricity in America that came out to ten homes per day we'll just ten homes of electricity consumes this is watts not watt hours right which is a lot of electricity to steal and take away from people makes me angry the other ones all sort of came in
last but they all consumed as much as a single home per day pretty much give or take depends where you live down in Texas probably closer and yeah and now you know you might be saying well I'm a really cool awesome guy and I've got my Moon arrows and my bitcoins and multiple wallets and I'm never gonna let the mount GOx people have my wallet and all that stuff monera is has anonymity for tracking payments and transfers of coins it has something called like putting chaff in there like basically fake transactions to confuse analysis and making it harder to find and track real payments there are other ways of unmasking that as well which look really neat but the pools
themselves and putting the coins into the pool if you can get ahold of the original guy and his malware that he planted then you have the wallet at least that did the payments into the pool once stuff goes into the pool it can be taken out by another one you can get paid out to another wallet I imagine so there is that sort of wash rinse thing right but still you can probably then just do payment tracking processes and other things to figure out where it goes which made me to realize that basically mining pools are effectively a neat way of laundering cash a good example is I live up in New England and there are some people who will show up
at the casino and they'll play two hands and then they go back and cash out and go back home and the money they came in with is not the money that they left with so yeah same idea right put it in the bank and so this is my conclusions it looks like I went a little too fast I'm sorry guys but I'm open for questions once I finish my conclusions icos and kryptonite based crypto currencies plus easy hacks equal dry by mining that's basically the formula you're gonna launch an ICO or you established coins like Mon arrow people are gonna try to make my money off your computer if they can get on the mining
pools being able to go to the pool plug in the address make it very easy to sort of unmask like what the impact of that campaign has been I didn't have to go off and try to figure out number of infections or do anything extrapolations or anything it was just there here's how much you made ransomware does seem to be fading in this space I wouldn't say it's fading all over the place right but I would imagine that if one a cry was around today there's a good chance someone would just make a moan arrow or similar dropper and use that as well to spread out they'd probably make more money doing that especially at that
time that was before the huge ramp up in Christmas right so robots are definitely fading away I think probably most of what I'm seeing is old compromised servers set up to just scan and infect other servers so it's kind of like sequel slammer or Conficker it'll just be there forever pure profit can definitely be made with reduced risk for these guys now they don't have to interact with you they don't have to try to steal something from you they just want your computer it's kind of like Amazon's Cloud except free and and when you start looking at this and the cost metrics for them are pretty much nothing now it's just your time to write the
code this asymmetry is nuts because everyone else is trying to fight against this stuff you have to do patch management keep yourself up to date put deploy firewalls proxies intrusion prevention systems antivirus endpoint security whatever you want to call it you have to deploy all that stuff manage it pay for it keep it up to date and all this guy needs to do is find that one server that you didn't deploy all that technology to right and I think asthma narrows difficulty continues to rise I don't know I think I've read somewhere Moe Narrows meant to always be easy to mine whether you're computer processor I don't know but I figure it's gonna get harder and as it gets harder there'll be
another coin of mine that they'll turn over to and what was really neat is that all the use the Stratton protocol that's pretty much the well-established way of doing it that's probably not gonna go away and they're gonna need to use that to interface with other people so you're probably best if you want a key takeaway from today is deploy signatures that identify stratum and block it and alert and that'll probably identify either people being cute minding their own currency on their laptop although that probably uses nice hash or it's one of these things anyway thank you very much [Applause]