CTI; It's All About The Process... Or Probably Should Be !- Paul Miller
Show transcript [en]
excellent okay uh good morning I'm conscious I've got obviously got the lunchtime slot i s a lot of people trailing out there saying uh going to get some lunch I think now but that's fine so thanks very much for making the effort to to to miss lunch for another 10 minutes and uh have a listen to me um so I guess it says I'm going to talk about cyber threat intelligence I am uh I'm going to probably talk more about actual intelligence uh hopefully uh and by that I kind of mean the context of military intelligence uh kind of my background so a bit more about that then I suppose to you know I've just started
I'm not going to talk about CTI and then kind of he for CTI talk so so why or who am I and and why should bother listening to me so I spent um a decade in the in the military doing intelligence work lots of different roles lots of different things I probably spent over six months or so um being trained in it directly not because I'm slow but because that's how much training they give you for it um and then since there i s say I like to say I exited via cyber um and that basically meant a a bachelor's degree in cyber cyps and all sort bits and pieces and then since so left
in 2016 since then I've worked at like loads of organizations I spent a decade working at one organization and then eight years working at nine or 10 different organizations um but yeah it's been really good really interesting and I suppose the lessons and things I want to tell you about today I've been born out of the past 18 or so years of seeing how where and why people use intelligence and how they might do it better so it's for practitioners to some extent obviously you'll probably know more than I do because I'm not practitioning in the field but it's also for customers to kind of understand and how they might use it better and how
they might engage better okay so a bit about the why then um from my perspective so I think that cyber threat intelligence when it's put forward kind of comes like this so the thing I care about so when I came here today I I care about with was raining or not I wanted to know whether not to bring an umbrella whether or not I need to wear a rain coat whether or not I could drive whether I could walk whether it was going to be awful now feel sometimes like when ask that have a CTI function I get this they say you're interested in weather you're interested in cyber okay well it could flood there could be a d a
deluge could be a finado could be a tornado it could be the end of days cyber it's the end of days I'm like okay well all I care about is this specific day that I'm going to go to this thing you know is is this likely is this going to happen um and this tends to be you know again not everywhere not everyone but it tends to be you get this kind of you know Horror Story about what it is but in reality all I wanted to do was was know what the weather was going to be like so I need to think about what I where want to get information from having a look through that information
and then understanding it so I can take an action on the back of it so for this a week out I had a look at um what the weather's going to be like that's all I did it's like well I want to know what the weather's going to be like I don't need a picture of a Fino I just need to know what the weather's going to be uh and then I just checked it again I checked it again yesterday you know done and that to me my requirement answering my question answering my RFI answering the question I wanted to answer for that it it's done by that so it's a really simple information request and it's
really simply answered it doesn't require any you know anything extravagant or exciting no need to picture floods and things it's just that okay so and as it says there you know the intelligence side of it it is the forecast it's telling people what might happen or what has happened so you can give people reports of what the weather might be like you might want some textual information about generally at the end of August in Bristol it's going to rain um but but ultimately you actually want to know what it's going to be like on the day so what actually affects your organization and when it affects them um okay then uh a couple of briefer sides I suppose to kind of give
a bit of uh context with regard to terminology and um yeah and specifics around things so I'm really Keen whenever I look at subject kind of see what it actually means what does this subject actually mean so I looked at the definitions of the words these are from Creston Bank of England and uh they basically turn around and say we to start at the bottom so intelligence they set information more on that later it's probably not uh threat is something harmful uh and cyber is computers and computer networks so information about something bad that might affect computer networks that to me makes sense okay well okay that sounds about what it is um another say brief aside just to kind
of cover off some housekeeping I guess to some extent um this is the crest pyramid as to how they Define things so they have strategic at the top covering the most most things and then at the bottom they have operational basically the lower level more tactical what I'd refer to as tactical which is exactly I want to put the slide in because for me from a military context I refer to Tactical as the lowest level uh and sometimes when you talk to other people that confusion can make someone seem completely not credible immediately uh so if you don't Define that and and ens sure you're talking about the same thing at the same level people say CTI
function is useless give me the wrong thing that person doesn't know what they're talking about they probably do because they've had the audacity to talk about it um so chances are they're just talking on a different a different background to you so it's important you talk about this thing so just to cover that off um so intelligence context we said that information well you'll see here that information isn't the last isn't the last piece of the puzzle on the slide the last piece of the puzzle is intelligence and you'll see here the words are already used already which is collection processing analysis and dissemination um so going from a wider environment getting some data turning it
and converting it too information and then de ating and using intelligence to tell people an informant action they might take so that's the real important pieces that it's not just all the information that's out there it might be a times some quite you know specific lower level information but ultimately it's about giving something that's valuable they can action against um and you know it's uh it's it's known in this cycle uh a lot of people around the community I've been to a lot of talks some people slam this some people Rave about it uh it's a very simple process a very simple cycle some people say it's massively outdated uh and it's no longer valid in the context because the speed
it moves at I've used this cycle you know a very fast speed speed of real life uh you know maybe not Network speeds but certainly it's it's usable and I think the other point I'd make is that if this isn't valid uh so I was fortunate flash year to be able to do some analytics training data analytics training with lsse uh and they put forward this conceptual model for data analytics um and I was like hang on a minute that's exactly the same thing and this is being taught as an analytics techniques for data for the preparation work for AI machine learning whatever you want to call it this is is the fun Foundation of that to do the analytics
work behind it so ultimately it's the same thing and I'm not say that it doesn't require running at different speeds there's different Technologies involved in it but ultimately having a question and ending up with an answer is what you want to try and do and having a structure to do that can be really helpful so I'm going to caner through uh that process now uh and sort of talk through the different phases of it to give you an idea about what and how you might use it as I said it's as much around informing people who are consumers of it as it is maybe some practitioners who are maybe new as the field but but either way I think there
something we gain from it so Direction wise then um there some initial considerations so often it's referred to as like the air responsibility area of operations area of intelligence responsibility lots of things that the thing on the left is referred to but ultimately that's all your Tech where you operate what you've got and how you use it it's a theme across all of cyber and infos whatever you want to call it that basically you've got to know what you've got because that's what things people care about you know they always say things like are we okay is my network safe and what they what they mean when they're saying that is all that stuff that might
be theirs okay they don't mean all stuff that's not there it's outside of that and there are the things on the on the right of the um right of the slide there which effectively say you know you've got things in the area of intelligence interests so external actors other organizations other threats the things you might report on that might affect the things inside the organization but they're not the organization okay so that's where the horror stories come from they're the finados and things um ultimately care about what happens on on their Network and that's done through intelligence requirements so they need to have a requirement or an information or question to enable them to to
understand what they care about uh so there it says it's doctrinally it says a statement provides rationale priority for an intelligence activity and detail to allow CTI staff to answer the question basically is what it's saying how do we get enough information to effectively answer this question where do we get it from um and a lot of organizations I've worked for use that through priority intelligence requirements okay they're called a thousand different things at different organizations But ultimately it's a series of questions this is just a brief sample of them I've got about seven or eight slides with these on um that talk about the things as an organization you want to routinely answer as question for
your organization so things there like what reports have have been on vulnerable infrastructure for our organization um what recently disclosed major cyber disruption attack of vulnerability or explo has the capability to impact our organization but always about you and your network and your things your technology um because that's the bit you actually care about and that's a bit you can actually have an effect on okay so to answer the question then you need sources right so Crest put forward that there's 12 categories of sources um and yeah I'm not going to dwell on on specifics of all of them but ultimately they have defined that there are number of sources you can get information from
number of sources you can use to enable you to answer questions so things like the deep and dark web things like uh you know information from your own seam um things like messaging platform social media you know you've got bits on there like code repos and stuff there's lots of places you can get the information from lots of different ways you can answer a question but it's important you've got the question you're mapping it to a source say okay well if I want to answer this kind of question I'm going to go to this kind of source and if i' if you've been to that source and think can answer you can kind of say
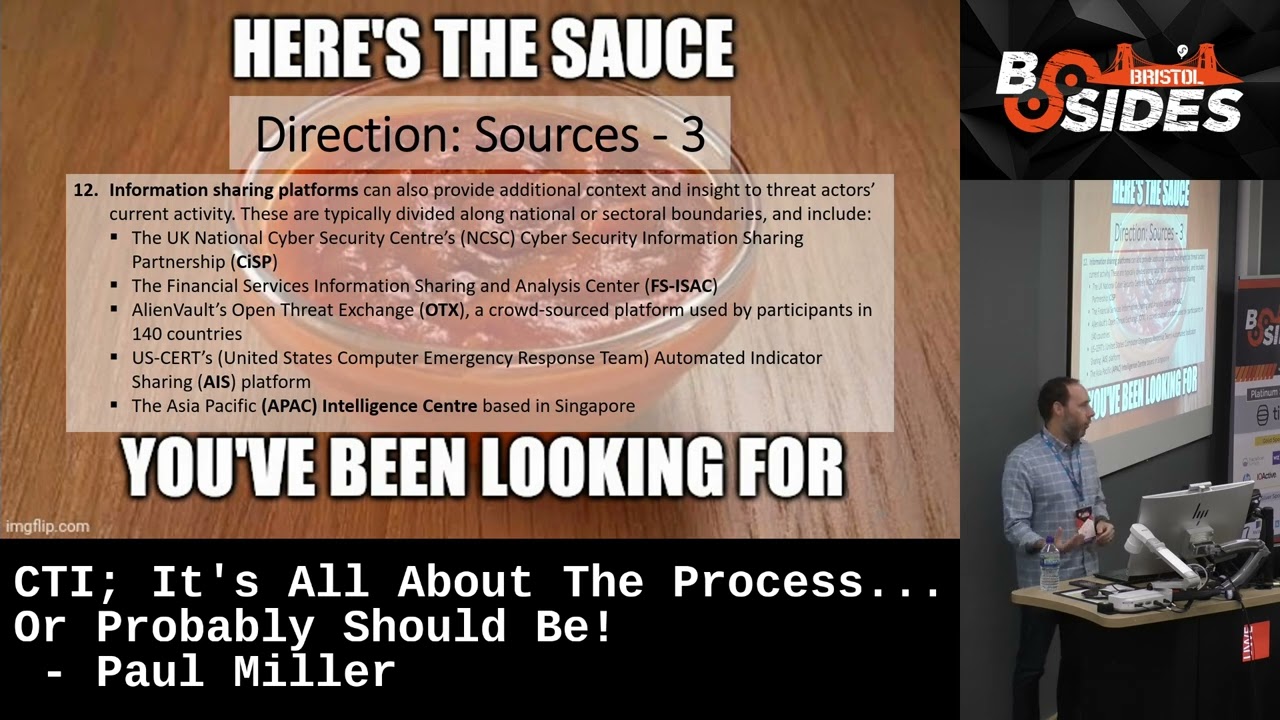
well there is no answer and if you can do that it gives you a lot more credibility when you're then briefing people to say we've checked all the viable sources for this there is no answer for it okay great keep it on cover find out if you can find an answer in the future um and then finally uh the last one they put forward is this uh is this information sharing platform so they can be useful some people have got you know negative things to say about them but ultimately it's a good place where you might be a to get more of a refined answer and maybe share some of your information from your network as well
providing you've got it covered um so a bit of a challenge there with regard to um how much might get shared and how much people are sharing and using in there but they're definitely use useful information repositories um so that's Direction it's the biggest part you'll be pleased to know but ultimately you've got to get that bit right because if you get that bit wrong you're going in the wrong direction okay so you need to be going in the right direction um so the next thing you need to do then is collect in collect your bits and pieces together you collect the information so you've got your questions you've got your sources you to collect everything you
need to answer that question um and this there are a number of processes you know from my sort of background training whereby we do things like um collection coordination requirements management information requirements management basically you need to have a way of bringing all the information together searching those databases quering them understanding what bits of data you want from what database and this is where the speed bits often gets challenged because it's well there's too much out there it's like there is too much out there you're right definitely too much out there this is where your tooling comes into and able you to do those things and to map the priorities um you know in the
products You' got to produ and things it's also an important point at the bottom there with regard to what you're collecting so priority wise three is enough right if it's if it's outside of three you don't need it you don't need it in your tip you don't need to collect it because if you're collecting it and it's not meeting any form of Baseline requirement you're basically just filling up and paying for storage and paying for compute don't don't do it it's it's just about move but yeah so ultimately that that's kind of that kind of mostly covers the collection once you've got your question you've got your sources you've collected the information for it you're then going to process it
it's a five-stage process to process um to process the information uh and effectively it's bringing all together again a lot of this collation stuff now is done by machine um but ultimately you do need to that to be you know encoded correctly to be done by a machine um evaluation there's there are some other slides have not included here but things like evaluating your sources it's really important do you trust the sources is the information is the source usually reliable is the information credible you know there's lots of things you can kind of look out there and you can grade sources information against reliability and credibility um again it's not an exact science it's kind of more of a a
guess and it's organizational specific thing um you then got to do your analysis again the only bit in here despite the fact that CTI practitioners are often called analysts this is the only bit in the whole piece kind of talks about analysis the skill set is much wider than just kind of does this look true is this right or is this wrong so it's important that you obviously have a wider view of of these things um integration so bringing it together going through that filter I've put on there and then effectively providing a so what factor okay you've told me all these things okay so it might be the case of you've told me about a finado
but you can give me a reason why you've told me about a fadoo because actually there's predicted to be one here today there's not one predicted to be here today but you know it might be the case right um so once you've done all that work all that good work it's it's down to dissemination now okay so getting the report out there telling people what what they what you need them to know they've given you questions you put sources together you've processed information now you're telling them what what you think they need to know on the back of that um there's a number of ways to put it out there the key thing to understand and to recognize here is that
the way you give information back to people it has to be how they want to receive it not how you want to give it which it sounds like an obvious thing but ultimately you've got to answer the question how they want it answered now that's not mean you've got to give the answer they want it just means if they want it on a one slide to tell them what the problem is you've got to get it to one slide if they want a you know a tone of of 10,000 words then then give them give it them I probably won't uh and and there's a couple of example types there so it might be that you want to have a
you know routine report that goes out summarizing everything or it might be there's just something really bad that's happened and this is where you know I and say you might just want to send that tactical report people go what you me my tactical report an operational report whatever you want to call it at that lowest level these are just bits of information that really valuable to answer these types of questions and requirements okay so that was a brief caner through the intelligence cycle um covering the direction which I think is the most important phase of things to get that right make sure you know what questions you're asking make sure you know how you're going to answer them
make sure you've got all the information together uh and make sure you understand where you're going to get it from so then you go and collect it from there once you've collected it together you're then going to process it through that five stage process uh of filtering it through um to understand exactly what you've want um what question what answers you need from it and then you're going to tell the customer and ultimately there will be a customer you shouldn't be just doing this for yourself um tell the customer what they need to know are the questions you've agreed with them that they W answered you're going to tell them what the answers are or what you think the
answers are okay so some key takeaways then from my perspective then so as I said there you've got to have the direction phase without that it's got to be collaborative okay you've got to work with operational teams you know people who work in it believe it or not you've got to talk to them work out what the systems are you've got to work out with Executives what they care about everyone's got to be involved in this now that doesn't mean they've going to get in a room together but it does mean they need to be informed because ultimately this is a function that's meant to be delivering some value so it's got to be done that way and that
I'm not saying that you know pointing the finger at CTI and say you've got to be involved I'm saying that to everyone the whole organization's got to get involved in this because it's no good just point the finger and saying no good um un unprocessed data information that's not intelligence uh although it'll often be termed it so again use of terminology is really really important because people look at and go you got given a bunch of hashes this isn't valuable this isn't in this is rubbish now in reality it's not it is valuable to the right person but the point is is that you've got to have that um you know kind of contextualized so that's so what
factor is really really key um I mentioned it already in the talk but it is somewhere between an art and a science you know it's there there's bits of it which are really technical you know whether or not you're using something like Jupiter maybe you've got python your script running and stuff maybe you're scraping data off the web there's lots of bits that are technical there's also lots of bits of it that are kind of hm what do I think about this is this likely or unlikely certainly at the Strategic level where you might turn around and say you know we think that you know this actor is going to do this in the future we've got no idea really
um potentially so train educate discuss with people make sure they understand what it is you're trying to say to them and what what the function does and how it does it um so as it says there you know what what does um sorry so means something different to different people we talked about the pyramid talked about the cycle talked about you know if you're operating a the lowest the most detailed level of operation tactical operating there is very different to someone who might write board packs of a strategic view of outlook for the next five years of what the country's going what the company's going to face um so so if you're not sure ask and share your
knowledge because it means different things to different people and then finally um just to close off I suppose on this uh it is a team sport I genuinely believe that CTI function should be communicating across the organization okay if it has to be done through other people do it but ultimately the worst thing that can happen is them you know getting the function together and sitting in an office quite on their own and just turning out reports going these reports are rubbish and know I'm saying the company don't understand what we do or the customer doesn't understand what I do okay well work together talk to each other tell them what you're doing explain why you can add value and how
you can add value and if they don't like what they're getting go back to them to the start and say do you have different questions is there something else you'd actually like to know how can I help you answer your questions and work better with you um that's me uh thanks very much for your time today really appreciate it I appreciate I can through it quite quickly uh has been said to me before do you actually breathe Paul um I do I can assure you I am breathing this is not this is not a facade I'm breathing but yeah thanks so much for your time uh and we've got some time now hopefully for some questions I think if there are
any yes so more of a technical question than the process one um do you have any experience or any recommendations when it comes to um indicator or intering platform for use within the company so for example one of the more popular Open Source Products is MP M yeah and that one is actually deploying and configuring it properly so do you have an experience with those platforms or so the main experience is people complaining they're no good right that's the main experience of people saying this doesn't work I think the real challenge is um is is understanding what it you want to ask of it so and actually understanding whether or not it can answer what you want it to ask and if it
can and and obviously delineate to some extent exactly what and how you're going to get from it so treating almost as a source and saying this is just another source what questions can it answer and how will it best answer them and if it doesn't I think what I've seen elsewhere as well is people just go and buy the tool first of all say we've got we've got the tip we've got the tool we' got we got the sources okay great what do you care about well just just comp everything you the whole organization so direct experience of integrating them in a better solution sorry no I think the key thing is critical thinking throughout the process to say okay does
this thing actually do what we want it to do does it we expect it to do is it suitable for the requirement and make you've got that requirement not the best answer I know but hopefully it's answerers some of your question okay thanks and you yeah so when cyber strategies is already quite difficult for some businesses to implement are you seeing resistance to this kind of extra layer or would you build out into that existing side straty business yeah so so I think sometimes people see uh I mean great question again I mean so I think sometimes people see there there's two different schools of thought gu some people say it's the first thing you should do which I think
is probably probably the right thing in one context but the wrong thing in other context so I you should definitely understand what questions you've got first and you should also understand what's in that area of intelligence interest I who's targeting you what you're doing and how you're doing it you should definitely have those bits in place but yeah i' certainly agree that a lot of people say well do I do I even need this that seems like a that seems like the icing on the cake I'm going to build the you know do the cake first and then afterwards we might get it if we need it in the future whereas I see it as that you know so how how would
looking part of your business really isn't it yeah exactly and I think the other point as well is that you know you you would scan the market before you engage with it you know if you're going to try and sell something there you do it so if you're going to put your you know your entire system up on the network which people have already done or up on the Internet which people have already done you probably want to know who's going to likely want to take it down and I think a lot of the time people people don't and you end up with this scenario whereby so we so most of my roles have been like it's always
termed intelligence Le and everyone all organizations have got it on their their website we're intelligence Le it's okay when you say that what do you mean where's your intelligence function oh kind of mean we Google stuff before we go out and do stuff and that's probably good enough isn't it um it's probably not intelligence Leed but yeah a good question yeah so this is actually a pretty good way of getting more resource really I mean I think so so so I'm an independent contractor so yeah ultimately often I I don't necessarily I don't CCH horror stories but I say look you know do you understand the following the areas around your business they're like no none of that we don't do any of
that you're okay well probably you should I mean the services I sell are GLC Services you know that's what I go out and do but ultimately it's kind of like what you trying to so sometimes they like oh someone said you have some login monitoring in place do you think we should it's not I don't know if you care about the fact that someone might be on your network without you knowing do you know who might be targeting your network do you know do you know you're actually in the you know the transport sector which is targeted by these these organizations is it really yeah here's 20 examples of where they might be targeted you're not Horror Story for
them just to say like these things do happen you should probably care about them and those PS I put forward there say I've got about six or seven slides of them on often set to organization say do you care about these things they like well yeah massive it's like again what efforts have we taking to answer those questions they're like non really like okay probably start there so yeah definitely thank you thanks very much thank