GF - From Vulnerability to CTF
Show transcript [en]
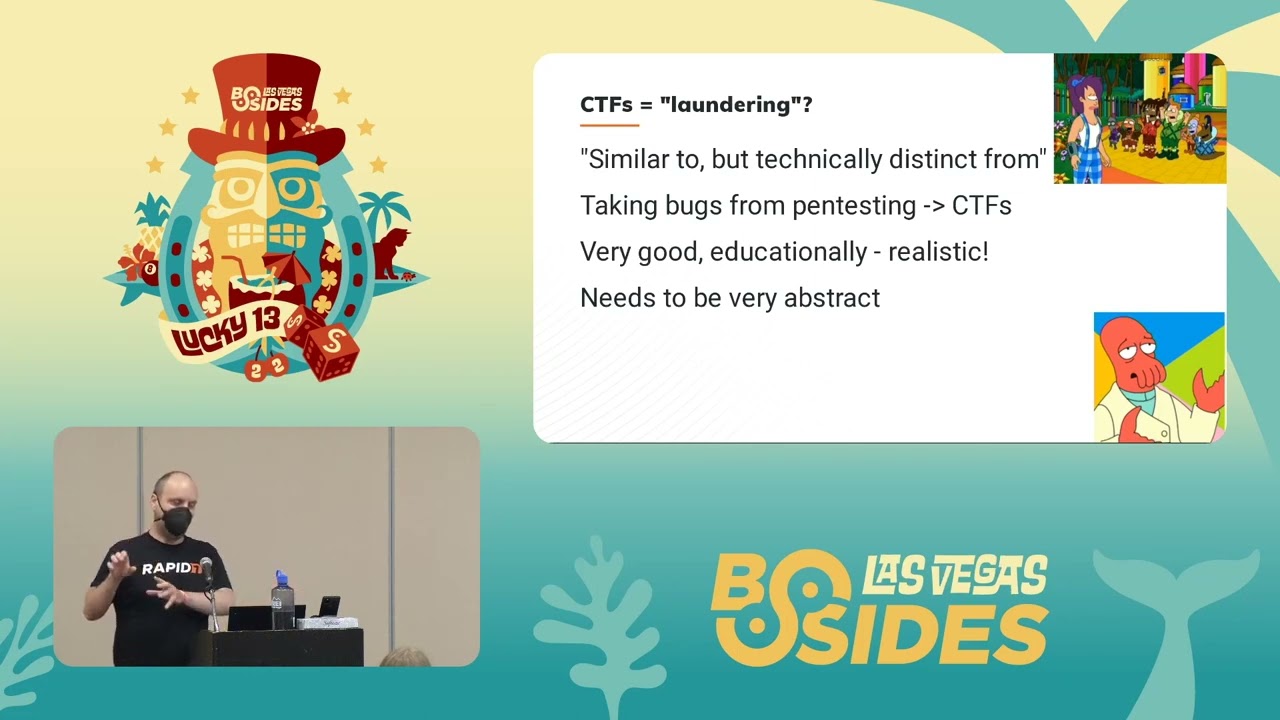
I want to introduce to you Ron Bose lead researcher at rapid7 and for the next session he's going to tell us about from vulnerability to CTF hello everyone um thank you all for coming this is the first talk I've done to a live audience in like three years so my only Quest is laugh I make jokes because that way I feel like there's actually people around I've been talking to a webcam for years and it's been awful so yeah thanks all for coming this talk is basically going to start off with me talking about myself and uh but what my background is what I've done what I do now stuff like that then we'll talk about ctfs capture flight challenges I've worked on ctfs in a bunch of different contexts over the years and I think a lot of them are there's a lot of good things about ctfs that we can really learn from then the kind of point of the talk is I want to talk about vulnerabilities I want to go over I think five or six or seven vulnerabilities that either I found or I've known about I've turned the CTF challenges that's where I talk about the process of how I do that and I think bones are cool and I want to talk about them for an hour and that's what we're gonna do another thing I want to say about what we learned just to wrap it all up so who am I I am Ron Bose as our empty Santa my rapid7 I'm a lasikiri researcher which is the fancy wave saying I'm a uh I write blogs and recommends playing stuff my handle everywhere is Yago xa6 uh Yago from Shakespeare Othello nx86 from the CPU you can find me on GitHub on Twitter on Steam on pretty much every platform I do that there Elias so I want to share with my family first just you know let you get to know me um I have a husband who doesn't like his picture public and I we have two birds together they're both green cheek conures gcc's and because they're gccs we named them playing a shark so flying on the left we've had for about two years and sharp is brand new we hired for we have him for like a month Spock squawk thank you uh they love joining my video calls and stuff at work it's a lot of fun they're here are the little troublemakers if I just want to show them off every CTF I make has them in there in some way now so at the level open source development and uh I kind of got my starts doing like researchy stuff working on edmap and Brandon who's in the front row being able to end up together back in like 20 2009 2010 and he dragged me a tour trying to do a talk in like 2011 and I got to talk about nmap and that was kind of cool my first big talk these days I work on the medisp flight before time I research vulnerability stuff like that I'll talk about that more I've written tools for like hash extension attacks um yeah I do lots of Open Source work I've done a DNS Factor DNS tattoo so you might have heard of uh my last three jobs it turns out they're all kind of the same thing uh 2013 I moved to the States from Canada to work on to work at Google um I would we would do among other things reviewing our own products finding bugs in Google stuff and then disclosing those bugs to the product teams and they would fix some stuff very much like internal then I jump to counter hack which is uh run by let's go this is sort of a affiliate ascends in that counter hack we would do pen testing for customers which meant finding vulnerabilities and customer software and then setting up to the customers and what's really cool about counter hack is we would also do ctfs which I'll talk about soon and the vulnerabilities from customers would feed the ctfs as like ideas for challenges which it talks about and then the the trouble people had or the things people applying on the sea of challenges with feedback into our pen test business so it's a really nice two-way street and that's okay gave me idea for this talk and then about I guess in April this year I started working at rapid7 so I'm very very new there and representative I do all the same things I take software I find bugs and stuff but now I just released it to public I can talk about it I write Vlogs I play plugins um attackerkb.com is where we post a lot of our write-ups it's a really cool site in my opinion as an employee but also we do really deep Dives on uh vulnerabilities it's a it's one of you okay look at things it's a pretty cool site in terms of CTF um going back to like 2009 or so I've been playing ctfs a large use for skull space which was our um hacker space in Winnipeg by hometown and later on the I did Defcon CTF with stratum or her uh some of the folks from that from that team are here somewhere so yes is a player for a long long time and then I gotta started doing ctfs as a Creator so I make the Beats High San Francisco CTF along with uh Brendan and Daniel and some others um my previous job we made that were CTF which is like it's a paid thing concerns again me and Daniel work on that together and then Holly heck challenge 20 holiday hack challenge is a free thing that that sounds and kind of how to do every year and that's a huge video game CTF which we're really proud of again me and Daniel worked on that I should mention I'm gonna put this I LinkedIn slides on the last slide so you'll be able to get there if you want them I should mention what is a CTF uh CTF is a capture the flag challenge basically if you don't know there's multiple different kinds I don't get into like a nitty-gritty things but they're very short versions that players solve security related challenges for points sometimes we just give them a question answer sometimes they attack each other's like infrastructure either way it's security challenges or points and see if you have time tracks I love the ctfs most CTS probably all of them so I want to show off a little bit of History because I think it's kind of cool the first CTF I did as a player was called stripe CTF in the 2010 apparently and one big takeaway from that CTF was the final challenge was a hash extension vulnerability at the time I'd never heard of hash extension ever and the concept of it just blew my mind and there's no tools for it there was white papers but no like easy to follow documentation so I read the white papers I wrote code I hated it it was really hard I'm not very good at reading academic stuff but I got through it and managed to write a proof of concept exploit for md5 shot one shot two days six Etc I made a tool called hash extender and I wrote some Vlogs and that's now like the best known tool for it so I can really thank CTF for getting the idea to do that I learned something I'd never learned before uh the photos on the right are from a 2013 CTF called plaid CTF I just put them there because like the story the kid in the bottom right hiding behind the brace acting boxes the name Ethan he's my buddies kid and he came with a cape on and I said why do you have a cable on Ethan and he says I'm a dinosaur I was like can turkey with that so I think about 7 A.M after working all night on the top right I had to keep on I don't remember why I thought it was a good idea but it was also a dinosaur so in 2010 as a as a hacker space me and skull space worked on quality hack challenge 2010 uh that was back when Daniel was an intern there and we won and Ed wrote like you guys totally rocked you did awesome you're making cool stuff happen and that was in March 2020 2011. so it took three months to pick winners which pretty much is how we always do it um what's cool though about this is that 2011 it told me how good I did and then in 2017 I was working for him so I'm really proud that I was able to kind of turn doing ctfs especially doing them for like Ed into part of my career and that's like one of the reasons I like talking about this is because like CTS has done so much for me that I think it's really cool to talk about um this is the first idea of I wrote this is my playing notes I actually dug through my pile of notebooks I found this and I wrote notes for how I want to make a CTF and I don't want to read all these you're welcome to download the slides later and read them but the funny thing is I rented these I'm thinking oh yeah I made this challenge again and again and again there's a few things I really like making challenges out of and as far back as 2011 I was still doing it but the first big CTF I did was B-side San Francisco and I'm almost done talking to myself I promise um the story behind this was I was out I met Reed Lowden who's somewhere at this conference I don't think he's in the room and we we went out for lunch or something when I was in San Francisco visiting but he said hey you don't make ctfs do you want to do rctf and I was like sure and we did it and I recorded Brandon and Daniel and others to help make the CTF and it ended up being like fairly successful and we've been doing it for five years now and each year is better than the last so we do that every spring I think we're doing this one in April so it's really cool to uh see we get to do a big CTF and I'm really happy that that besides San Francisco sorry gives me the the time and Trust read basically says to us like make a CTF let me know what you need and then it goes off and we do our own thing for six months can we make a CTF it's pretty cool so let's talk about why ctfs are valuable I think I've touched on this a lot already but I feel like I should do more than just talk about vulnerabilities although I like talking about vulnerabilities so this is the best open open licensed image I could find this sort of from a easy Google search to say kind of like people learn a little bit of what they read and a lot of what they do and then even more of what they teach so ctfs are hands-on experience for things that people don't typically get hands-on experience doing but not everyone especially if people are younger or new in their careers are privileged enough to like be able to hack things like I've been able to as a pen tester or as a researcher or whatever so like being able to teach people things and let them actually do and get Hands-On work is super super valuable and Bug bounties these days kind of fill that role too but not gonna talk about those also with CTS write-ups are very much encouraged and that's where teachings where it comes in for Holiday hack challenge we would do we would value evaluate People based on their write-ups not based on what they actually did we would have a hundred people finish here to a thousand people I don't know the numbers but a lot of people finish it and then would write out submissions of their Solutions and we would pick the ones that are our favorite technically and our favorite creatively so this is just an example I found not just from Googling around he and like he runs into the travel log I believe and it's really cool that people will then take the things they learn and share with others and like for myself I would always wrap some of my CTF challenges as an author and as a doer and I think it's really good to like really really learn things well I think it's funny you were talking about as laundering and that no one told me I can't use this word but it feels a little bit weird but basically as a pen tester we often do work for customers and they often have really cool bugs in their software that we can't talk about because they're customers but feeding those bugs into like what's the core of this bug there's nothing to do with a customer but that we can teach people as a lesson so that when they see this bug they'll find it so I'll talk about some of those after what's actually really funny about these is oftentimes bugs you find your real stuff are too simple or too silly to really be bugs you see in ctfs people look and go look there's no way that would be a real bug it's just too silly but a lot of real bugs are that silly this is kind of a weirder concept when I was young I had a couple slides about this I removed because I thought it was just too much talk about myself there's already too much talking to myself when I was young I did a lot of video game hacking a 2017-18 or when I was 17 18 19 I got really into Blitzer games and regrow cheats and stuff for Starcraft and and Warcraft 2 and Warcraft 3 and stuff and like reverse engineering how those games worked and how the logins worked and how their profiles work they have their anti-cheat work and stuff I learned a lot as like a 17 18 19 year old and you that those those systems don't exist anymore they only use the same logins anymore so being able to share those with others and say like here's where I learned how to do this here's where I cut my teeth here's what I thought was interesting and being able to wrap it up into a challenge is really cool um so I feel like I'm kind of honoring the vulnerabilities by showing people kind of how they worked we'll talk about a couple of those so now I want to talk about vulnerabilities this is kind of meat of the talk and I think I have about six or so vulnerabilities I want to talk about and we're gonna go pretty quick but on each one I have links to write-ups about them I have links to the source code I've got a couple live challenges ready to go if they don't mess up if I do mess them up I still have slides with screenshots so the first vulnerability I want to talk about is CV 2020 1388 uh this was a this is the first thing I worked on at the rapid seven and I'm just going to click on my analysis to show off if you want to read this I have a lot a lot a lot of detail about how it works including assembly and clean proof of concept like I wrote a lot about this but I'll give you the sort of 50 000 foot view if you're interested in seeing more that's cool if you can't read the terminal text at the bottom that's just a screenshot from the page I just showed you so you're absolutely welcome to just read it yourself basically fi's big-ip device was vulnerable to a uh authentication bypass and that's a pretty common vulnerability class because it's really easy to mess up Authentication so the way the authentication works currently even like to this day um basically there's the F5 server I I do it a size two different servers but really there's two Services running on one server the first the first service is a reverse property the reverse proxy would do some types authentication not others and then there's a backend that runs on localhost and that does a different type of authentication but not the others so like whether you're using a password versus whether you use a token are handled by different Services which is a really strange way of doing things I'm sure it's historical reasons ultimately but what happens then if you applicate with a token so you'll see at the bottom I send the X5 xf5 off token equals blah blah blah um if you're thinking with a token the reverse proxy sees a token and says I only had I don't know how to tokens that's not my thing I'm gonna forward this onto the back end so when the back end receives it it goes is there a token yes okay I'm gonna get this token and if it's wrong I push back if it's right I accept it sort of simple the back end does the off the second pass authentication there's more than two there's like three or four different paths it's just ludicrous but the second way is if you say using password as an authorization header if the proxy sees using password the proxy goes oh this is my job I should validate these and they use a pen module so it uses the Linux authentication mechanisms to validate the two same password by itself and if they're correct it removes the Usain password and then forwards at the back end in the back end receives something with no authentication it goes oh this must be already authenticated and accepts it which makes no sense but that's how it's done so if the back end gets something with no token and no authentication it accepts it as valid which that's bad so it turns out and I didn't know this this is this was new to me there is an HTTP header called connection which I was aware of which usually has the values of keep alive or close keep alive means keep the connection open and close means don't but turns out there's a third value for it which basically says a list of headers the name of the header to be removed so you can tell a proxy to remove a header while proxying so now what you have is the same scenario except now you send the X5 off token as a connection header the uh the reverse proxy gets this authentication it says is there a token yes there is so I'm going to forward this step back end then approaching his mod proxy says oh hey I'm supposed to remove this token so remove the token and it forwards it and then you win the back end things are authenticated and there's a endpoint that you can't really see probably but it's called TM slash utilitarsh bash bash bash which takes the command to run so you guys run ID and it tells you root so this is like remote route just by removing a header and I thought that's a pretty cool vulnerability to like learn from because like this whole connection header thing I had no idea I spent like a week trying to find the actual core issue of this vulnerability and couldn't figure out why it worked until I read the Horizon 3 Zone who discloses it until they write Horizon 3's exposure and they mentioned the connection header and I was like oh today I learned so I made a challenge for B-side San Francisco 2022 which was two months ago give or take um called refreshing and I posted a source to all these things if you want to see these challenges we open source all of our B-side challenges so you're absolutely welcome to see how we wrote them but um basically I wrote a web application firewall reverse proxy that if I saw it if I saw Quarry string with any illegal any weird characters it was at a security header and say this is a dangerous request and then on the actual server it would check for the header and say if this header is here alert alert alert this is bad so I made a so I made this Challenge and if the user can remove the header then they could uh they could run close they could uh pass reversal in this case do a very obvious controversial attack so basically the solution to it was just to curl and then set that header and I thought that was a really cool way of teaching because I've never heard this before I think anyone who solved that challenge probably learned something because I mean some people I'm sure I know that but I sure didn't so Sutter's rfcs have weird edge cases I think Brandon's really good for that he'll he'll dig into like file formats like the zip or raw format or something and look for like weird ways of hiding data so it's like it's a cool type of challenge to like look at specs and make a challenge based on them so that's the first issue I want to talk about um the second one and that's okay by three for the price of one thing and I do want to do these ones live-ish um I have screenshots if they don't work but I could I could go test a little bit live so this is where holiday hack challenge 2020 which me and Daniel worked on and this was our two polling Birds you see there's a bird that's calling cell phone um and I can confirm owning a bird they love being on my head so the artist it was a good rendition of what burden would do so basically if you haven't played holy hack challenge it's like a game you hop around this virtual world there's talks there's music there's this is a whole game which my old company counter heck Adele can confirm they put so much time every money into making this free game just because our boss Ed just loves the Christmas challenges and it's really really cool that we do this for the community like I'm I'm a very cynical person who comes to advertising and I think this is a super cool thing that does hands does it doesn't have to but anyway uh one of the things was to open the door of a room and we have our called terminal challenges in this game and the terminal challenges will give you like a





