Mani Keerthi Nagothu: Decoding Cyber - Supply Chain Risk Management through NIST
Show transcript [en]
[Music]
[Music] all right um thank you everyone for taking time to attend my session today so my name is mani kiriti nagothu and i'm a cyber security professional based out of vancouver canada i work with i work with consulting firms before my current role as security lead at ballot power systems i specialize in cyber security strategy cyber incident response and developing security initiatives i have a passion for implementing uh security frameworks and bringing balance between security and operations i have recently started um a linkedin conversations which is a thought and cyber to share thoughts perspectives and cyber security um i'm also part of visa's western canada athlete which is recently started in march 2021. outside of work you would see me
strolling in stanley park or playing badminton or trying in extreme sports if i'm traveling so let's look at the agenda for today all right so we would be touch basing on recent cyber supply chain attacks that happened and uh looking at what is what exactly cyber supply chain risk management mean what are the recent challenges or the challenges that have been taking industry uh or firms with regards to csrm and how do you build a cyber supply chain risk management program and based on the content that we discussed in the first half of the presentation i'm related to a case study um which was carried out by nist and this is an actual case study uh that is
being carried out by nist uh in their initiatives from 2015 2019 and also now um finally the concluding thoughts with regards to where are we forcing csrm to be so what's the big picture here we're dealing with so globalization outsourcing and digitization had made organizations rely on a number of suppliers to support their functions and suppliers have become essential linked to run businesses a compromise on one of the links through a cyber attack can have a disastrous impact on the business as quoted from nist ir8276 an incident response report published in april 2019 by carbon black highlighted the use of island hopping by fifty percent of the attacks so what is island hopping so island hopping is an attack that
focuses on impacting not only the victim but its customers and partners especially if these partners have network interconnections so organizations have no longer protect themselves by simply securing you know um their own uh organization because electronic parameter is no longer meaningful that actors intentionally target the suppliers of more cyber mature organizations to take advantage of the weakest link organizations have been working to address this challenge for some time but many still struggle with recognizing the challenge deciding how to deal with it and getting started csrm or cyber supply chain risk management is an overarching function that includes concepts such as third-party risk management as well as external dependency management so you have an uh an extract from nsr
report right on the slides that you're looking at so what you're seeing on this slide is a report from melissa which is european uni agency for cyber security that was published in july 2021 the report presents an analysis of cyber supply chain attacks from january 2020 to early july 2021. um the analysis focused on publicly known supply chain attacks as you if you look at the slide the year is you know 2021 and the impact is in some of the cases it's global and the attributed group uh if you could famously recognize one of them is revel so revel went offline or anonymous after kesaya attack and they were back in september on september 8th or 9th of
this year and a couple of days back i guess they went again anonymous so what what do we expect from all of this is that uh supply chain attacks are going to happen more and we can expect more of these going forward also what makes this interesting is that a supply chain attack is a combination of at least two attacks the first attack is on the supplier that is then used to attack the target to gain access to its assets the target can be the final customer or another supplier therefore for an attack to be classified as a supply chain one both supplier and customer have to be the targets so this is another extract from nsa
report the same report i was referring to earlier the report answers to the questions such as what are the most common attack techniques being used in supply chain attacks what are the main customer assets that attackers are after and which is the relationship between attacks and the assets targeted timeline of supply chain attacks reported from january 2020 and july 2021 the month indicated in the figure refers to the month the incident was reported and not when the attack happened so from the report analysis it was clear that most of the techniques used to compromise supply are unknown followed by exploiting software vulnerabilities in terms of supplier assets being targeted most attacks aim to compromise code
and data as well as processes so the compromise supplier assets are used as an attack vector to compromise the customers and those attacks are mostly done by abusing the trust of the customer and the supplier or by using malware independent of the technique used most supply chain attacks aim at gaining access to customer data key people and financial resources so what exactly is cyber supply chain risk management so let's let me quote something from nest standard publication 800 161 what does security integrity quality and resilient mean in supply chain context so security provides the cia triad confidentiality integrity and availability of information that describes the supply chain and that transverses the supply chain so it's basically when i say describes
the supply chain it means that information about the part of the product you know both logical and physical traversing the supply chain i meant by that is the intellectual property contained in the products and services itself so what does integrity mean in supply chain risk management the reason why i'm going through these trends a bit detail is that we're going to see this in our case study where the customer focus was and where the supplier resources are based in so integrity info is focused on ensuring that products or services in the supply chain are genuine unaltered and that products and services will perform according to the supplier specifications and without any unwanted functionality additional unwanted functionality
so what's resilience um resilience is focused on ensuring that supply chain will provide required products and services under stress or failure quality is focused on reducing vulnerabilities that may limit the internal function of a component lead to competent failure or provide opportunities for exploitation cyber supply chain risks cuts across different risk management functions um again underlining this piece because we will be talking that in the case study companies need to approach with a straight strategy that will enable them to manage these risks holistically an enterprise-wide basis from the discussion about we noted that interaction is definitely necessary in cyberspace to create modify exchange share information most of the time software is built from ready-made components such as
proprietary code open source components and third-party apis which are application programming interfaces it is common to come across an application that is not built on its own but is built on reuse software the process of bringing a product from design through production looks simple from the outside but a number of suppliers can own part of the process and their risks because of this complexity sometimes we are unaware of where and how third-party risks can impact the organization a simple example would be you're using the supplier and your supplier is using a sub-supplier which you're unaware of if i give this from a sort to type 2 context it's mostly called as sub service organizations if i can just
bring in an analogy there so one key question here is what makes it special about supply chain attacks what is it so is that an organization can be vulnerable to a supply chain even when their own defenses are quite good and therefore attackers are trying to explore new potential highways to infiltrate them by moving to their suppliers and making a target out of them so we have seen a lot of examples in the recent times which is uh if i can famously quote is one is solarwinds and then we have kasaya and then we also had code cough and you know number of um attacks that we have seen in the earlier slide so supply chain so supply chain risks
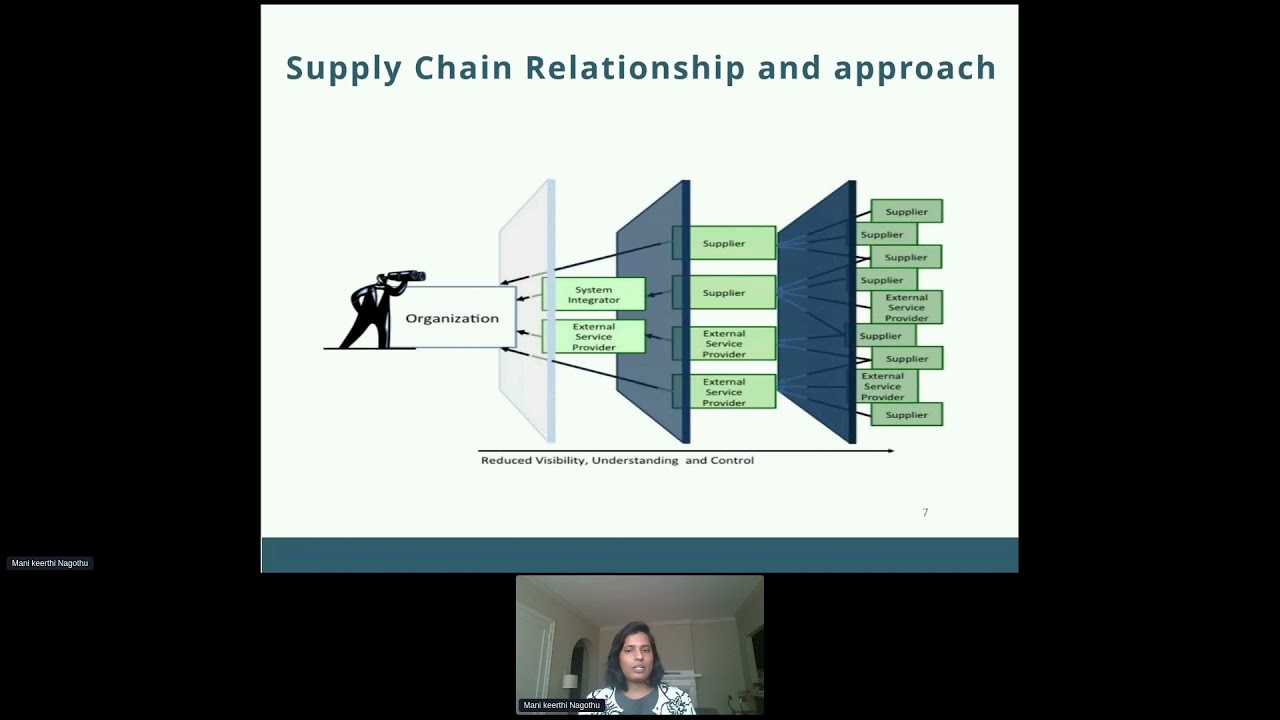
are associated with an organization's decreased visibility and understanding of how the technology that they acquire is developed integrated and deployed they're also associated with the processes procedures and practices that ensure the whole cyber supply chain risk management cycle which is the integrity security resilience and quality of the products if you look at the threats and vulnerabilities it's effectively managing cyber supply chain risks require a comprehensive view of threats and vulnerabilities so threats can be adversarial example tampering counterfeits or non-adversarial for example poor quality natural disasters vulnerabilities may be internal example organizational procedures or external uh part of organizational supply chain so how do we uh face this challenge or what is the solution to this challenge
is basically a pro approaching this uh by twofold process one is internal to an organization the other is external to an organization and also looking it at an holistic level which is the holistic approach so within the organization there needs to be visibility and understanding of what our critical process are how they interact cross department wise who are our suppliers and what is the supplier role and what's the impact in case of a compromise it may sound simple when i'm talking about one supplier two suppliers but in the case study that we'll go through in the rest next half of the session um i'll just explain the risk profile of the company and the number of suppliers the company
deals with so at the supplier and did we evaluate suppliers for the security process such as governance incident management information protection and did we include these details as part of contractual agreements as we finalize our supplier have we risk assessed against our organizational requirements so the first primary question is did we define our organizational requirements uh how do we how do our security requirements integrate with the suppliers so this could give us a holistic approach of how well we can manage any supplier risks and impact on organization it's more of a proactive approach than a reactive approach so coming to very content heavy slide which is the nest uh focus areas key practices and recommendations uh i'm not going to uh
read all the text that is there on your slides i just put it across on the slide to make you understand what's the relation between focus areas practices and recommendations so this focuses on focus areas the four of them foundational practices which is basically intersection of information security and supply chain management existing supply chain and cyber security practices provide a foundation for building an effective risk management program so enterprise-wide practices so effective csrm again is an enterprise-wide activity that involves each tier that we'll talk in the case study as well um organizational level mission or business process level and information systems level and is implemented through the system development lifecycle and risk management practices uh
processes sorry so csrm should be implemented as part of overall risk management activities that involves identifying and accessing applicable risks and determining appropriate response actions and you know implementation plan to document performance against that plan i just want to make a note here that uh whatever the content that we are discussing today is um already it's nothing new it's already there as part of your risk uh management process that you have in the organizations it's something to deal with specifically with regards to csrm program to be you know incorporated within again all the content has been leveraged from the nest website so this is freely available documentation that is available on this website that you can
refer to uh the last one is critical systems so cost effective supply chain risk mitigation requires organizations to identify those systems or components that are most vulnerable and will cause the largest organizational impact if compromised so key practices published by nist in february 2021 uh presented that you know you can implement a rob a csrm program or function at any organization of any size scope of complexity these practices combine the information contained in existing uh industry resources as i said with the information gathered from 2015 and 2019 list initiatives so nist has been doing a lot of research in this area right from 2015 and before that as well in different means uh but but the extensive case
studies or the case study that we discussed today would be from the initiatives that they have carried out from 2015. so each so the important aspect here is that we need to build a base which is the focus areas trying to identify where we are with regards to focus areas and relating the key practices uh to the focus areas that is the eight of them that you're looking at right now and also mapping it to the nest recommendations uh let me say that it's not a one on one to one uh mapping that you're seeing from key practices to recommendations because the recommendations are around 24 and what you are seeing on the screen right now are only few of them
so each key practice includes a number of recommendations that synthesize how these practices can be implemented from a people process and technology perspective uh as i said uh there could be one is to one mapping or there is no one is to one mapping and one key practice might have many recommendations that i'll just show you as a glimpse in the next slides but however like going forward like it would be something like you build the base you identify the key practices you would also look at the recommendations that apply to your organization based on the size and the resources available to you so if we look at a glimpse of how the key practices are mapped to
recommendations uh you have it here on this slide is basically on the left side you have recommendations and on the top uh top row you have uh the key practices so the eight key practices that we have looked in the previous slide are on the top top row and the next ones are basically telling us what they relate to so for example established supply chain plus councils that include executives from across the organization so that has been mapped to the key practice integrate csrm across the organization then establishing a pharmacy a crm program as they have been ticked there so the last two columns are not checked off because the recommendations do not fall under that key practice i have
intentionally kept them there to show you the difference so for the next few slides whatever we have learned till now uh with regards to the content um although it was not very uh you know broad explaining how to how do you do it but what are the concepts that we have learned till now we will use them to relate it to a case study uh that has been carried out by nist on cyber supply chain risk management as i have mentioned earlier uh this is an actual case study an actual company who has shared the best practices of csrm that they have performed and we will also identify the key themes that have been successful at that
particular organization and also add on add-on put you know resources that you can leverage to implement csrm program in your organization so let's look at the case study itself so the organization in discussion is named as abc i have intentionally redacted the name of the company here for our presentation but it's available on this website that you can go and check it so abc is basically into designing and selling high performance ip network products and services worldwide uh so they offer network infrastructure solutions such as ip routing ethernet switching security and application acceleration solutions um just so the details are given just for you to like understand the size of the company and the operations that they have worldwide
and also the last one uh the annual revenues so the revenues are more than 4.6 billion so let's look at the risk profile of abc so abc relies principally on five contract manufacturers and original design manufacturers for all of its manufacturing making supply chain essential in the whole of the process so there are about the 300 suppliers with more than 2 000 sites across the world that manufactured 24 000 parts used in abc product so i just underlined uh two terms there that is contract manufacturers and original design manufacturers these are very specific to the industry that they are in and the product that they deliver so that's the reason why i might say like cms and
audience and the case study discussion just to you know keep it keep it very small and then you know discuss and refer to them um which is which is important because uh the way they do their cyber supply chain risk management program is is very detailed um and the reason why you're seeing particular details is that about 300 other suppliers 2000 sites because it's that big so when i um mention about doing a risk assessment process probably for one supply it's very simple but when we are talking about as huge as this let's see how they do it so the first key theme identified for abc was organizational approach to cc scrm so when we discussed in the content
before in the earlier session as well we pointed out about holistic approach having an organizational approach to csrm so all functions at abc all the functions that touch supply chain are linked through supply chain risk management council which meets on a regular basis to review risk exposure the council is continually scrutining the overall risk environment including inherent product risks compliance risk and what is needed to reduce those risks the team also scrutinizes current activity and prioritizes areas that need attention so the supply chain risk management team uh coordinates closely with other departments to be underlined as the interdepartmental discussions so the first one is corporate risk team ah which is primarily responsible for the financial risk and insurance risk
and few other risks physical security team which has responsibility for manufacturing and product security so it's basically um organizational approach but decentralized execution supplier management team which has a responsibility for sourcing strategies and maintaining close connections to the vendors itt which addresses uh both the supplier id security and supply chain server security quality team for component quality and manufacturing quality so ideally for programs such as what is the business case for supply chain risk management for abc so if you look uh at what's the purpose so why did the business have a particular you know interest in cyber supply chain risk management does that so for them uh it's basically supply chain risk management goes beyond
logistics and on-time delivery so the business case rests on broader business base of product integrity customer service and corporate responsibility of course so abc abc ensures that all components that go into systems have accountability and traceability so these are the two key terms uh which creates high confidence in component integrity so we will we will see like how they have implemented these in their products as well as in the whole process so key elements of supplier management program so abc supply chain risk management capabilities are built upon the foundation of a solid supplier relationship management program so when i say solid supplier relationship management program is because relationship with suppliers are developed and strengthened through a
number of program elements including regular performance reviews strategy alignment sessions and performance metrics supplier risk management uh abc outsources i think 100 of his manufacturing as i discussed in the uh risk profile through top tier contract manufacturers the cms and odms about 90 percent of the suppliers are managed through a direct agreement uh what does that mean so they are selected using the sourcing strategies for the engagement of the engineering teams based on the requirements so in reviewing suppliers for potential risk they could pose to supply chain however abc you know also looks at percentage of risk and percentage of spend so what do what do i mean by that so a supplier may be as small as percentage
of total spent but critical enough to have a major impact on a product shipment so that's very key that is why every supplier gets vetted both in terms of dollars as well as criticality so some of the key elements of the supplier management program include supply performance evaluation so abc has developed two primary tools one is suppliers excellence framework and business continuity maturity metrics which i'll discuss in the next slides as well verification and audit so abc conducts on-site audits of its contract manufacturers and audience to assess and evaluate the performance certification so each supplier must certify compliance with abc code of conduct and requirements uh internal accountability so employees at abc recertify their understanding of
compliance with abc's code of conduct on an annual basis training abc employees with direct responsibility for supply chain management are trained in general risk management again that's very key trained the company also is also planning to implement at the time of case study additional employee training you know including you know related to more requirements on standards so as i mentioned as part of the supplier management program abc has supplier excellence framework so when when i say about a supplier excellent framework abc has implemented a multi-point supplier framework to lead and measure supplier performance so the wheel of supplier performance breaks down abc's expectations of its suppliers into specific metrics again important for kris and kpis from
leadership and management commitment to training and risk management um prospective suppliers are vetted by a number of teams so again inter-departmental conversations sourcing risk management engineering and security as you could see on the wheel if suppliers cannot or do not want to meet the requirements their sky their scores are likely to drop i apologize for the noise in the background uh if suppliers cannot or do not want to meet the requirements their scores are likely not high enough to allow them to participate uh because they have had the benchmark set and the reason is that abc deals with so many suppliers across the horizon it's difficult for them not to have the standard baseline established
once suppliers are accepted into the avc supplier team a secure a team of security specialists often located on site onsite works with the team continually to strength brand integrity and address any gaps that's again key so if we look at uh business continuity maturity matrix so abc ranks and tracks performance whether for its suppliers or itself along a continuum towards uh you know right starting from basics till to world class i'll show how they have arrived at that a glimpse of it for example in the area of business continuity abc measures its suppliers in four areas that you are seeing on screen management commitment to business bcb program dcp readiness in production selection and readiness of alternative
locations bcp program structure and documentation and training so some of the key some of the key elements that abt tests for include degree to which management is involved and committed in demonstrating world class performance in pcp when i'm using the term world class it's basically a term which is specifically used by abc in their maturity metrics how proactive is the suppliers planning versus just reacting when the crisis occurs are key players who could be called upon in a crisis identified and do they know their individual roles during an event so these are some of the key questions they're gonna ask the suppliers to you know rank them in the maturity metrics so if you look at a glimpse of how the business
continuity maturity matrix um has been carried out at abc you're seeing that right on the figure so we have management commitment those are the dimensions that look they're looking at and then we have you know different that's basically the ranking what are the basic are they driving basics are they mastering basics are the world class suppliers so if you could see the difference between driving basics mastering basics and world cup suppliers it's basically no preparation to having an established and you know mature process as an example you could see uh management commitment so in driving basic basically management is seeing the need for bcp preparation but if you look at world class um column you
would see you know pushes the limit of being proactive bcp through organization and before being requested by the customers so that's how they kind of rank the suppliers for abc specifically so abc understands that its suppliers often have to start out at a basic level and develop a strategy to become virtuous because it's not overnight that they would become from basics to white class and the maturity matrix kind of creates a common framework for understanding what world class means and how to move along the rows to achieve that as i said before the score is uh being done for every supplier as as they are in driving basics or in world class so supply chain continuity so
from a quantity point of view abc is continuously monitoring what is going on around the world on a 24 7 basis it uses an outside vendor and that's that's also an important part so it uses an outside venture to monitor global events and visibility down the supply chain also enables abc to identify and mitigate the risks of you know single source failed you know kind of choke points the vendor maps abc's entire bill of materials so what is when i say bill of materials it's all the products and materials and the components that are made by suppliers in their factories and call it collects them that information in a central database so the tool basically provides the data to
assess risk at a component level at a supplier level location level and financial level so risk managers can see at any point in the time what the supply chain impact of disruption anywhere in the world would be and that's very key because you youtube they basically automated the process and all they had to look is pull out the spreadsheet and look at you know how how our suppliers doing it are the suppliers going above our risk threshold are our kpis and kr has been met so supply chain security so there are three drivers of abc security strategy um like brand integrity rather than brand protection so that's a very key term for this particular company because
brand integrity is proactive where the more conventional brand protection strategies tend to be reactive in conventional brand protection for example the focus would be on identifying and investigating counterfeit products and tracking down uh the problems this approach does not address the root cause or conditions that allow that counterfeit to enter the marketplace in the first place so brand integrity requires life cycle threat modeling identifying and proactively addressing weak points from product development through production to shipping and warehousing so it's more of a proactive approach than a reactive approach customer focus so on behalf of uh its customer abc carefully manages and audits whether these products are authorized by the manufacturer whether the suppliers contract contract
only from authorized channels the document of origin of the product and who has touched the product in the whole distribution process and if the legitimacy of the product has been confirmed with the manufacturer the last one the driver is basically the life cycle approach so when the design and production process are largely invisible and finished finished box pop out it is difficult to have a high level of certainty that nothing has been compromised or corrupted so abc kind of breaks the whole life cycle into smaller and more transparent pieces so each of them are tested for potential weaknesses this approach basically enables abc to focus on how risks to product manufacturing is mitigated uh rather than you know at the
manufacturing site itself so this is basically the software design and security so software design and security another key aspect with regards to how software design and security has been managed at at at abc so again here the life cycle approach is being carried out uh right from the product uh initiation to the product end of the life cycle how the product is being rolled out into and then the next one is the component integrity as i mentioned earlier the component have is always tested for any faults or any errors that happen in the whole life cycle facility integrity is basically dealing with the physical and the transportation security associated with the manufacturing on loading or offloading
and on loading of products shipping and warehousing again the chain in the process you know how the product is being shipped how the various checks are being made and how they're being warehoused or it is basically having those uh resources to do uh specific audits or spot checks uh to do the you know bring the product from initiation to the end of the life cycle um it is also said that abc is training uh people on the floor to identify some of the audit mitigation activities or the risk mitigation activities identified as far as the audit to be careful and also preparing them to you know how to do the audit in a right way to answer
this um the next one is um standards and uh abc basically has the list of uh standards that you're seeing right now uh iso iso are the ones that would specifically like you can realize that okay these are related to information security quality and environment management the last one the c t p a t and a u o are very sector specific because of the way the products are being manufactured at abc the reason why i i made sure that i mentioned this particular standard here is uh i'll go through some of the additional resources that we have from nist and try to show you like how these all relate together when you're selecting cyber
supply chain uh standards for example selecting the right standard so how do you choose your cyber supply chain standard so selecting the right standard should be based on your business needs overall risk management framework and understanding your business your sector and customers so when i say sector we just saw like a sector specific kind of standard for abc and finding out your specific role and priorities in the supply chain so why do we have multiple standards so cyber supply chain risk management is a multi-disciplinary problem or a challenge and successfully addressing it requires lending practices from different organizational silos industries excuse me and vocabularies as well so how do you uh use the slide right you
know that you're seeing to choose your own standard for your own organization so there are three key questions so the first one is what cyber security standards and frameworks do you currently use so that is basically the upper upper part of the roadmap to guide you and then what is your industrial sector which is like sector specific uh row that you could look into and where do you want to focus with respect to supply chain risk management so use the rows on the lower part of the map to mark by the large gray arrow so each column in the figure starts with a source document so if you do not currently use a framework um based on the size of your
organization and the volume of business um you can start with this framework or or a framework that fits your bill draw additional resources from other columns if you feel it's necessary it's acceptable to use multiple documents because you want to argument your practices as demonstrated by many companies so if you like to argument your current program with additional resources you can use any of the relevant documents from any column again this is like unless resource that you could see on this website so again um let's let's let's look at the concluding nodes on this area so uh a few one of the primary aspect of cyber supply chain risk management is basically um that it's a huge program that needs to be
incorporated with the risk management side of things uh but the key aspect is it's based on the business case it's based on the cost and the resources are available to you based on that uh you need to take a call with regards to the how big the program is and how much investment are you going to make in each of the areas people process and technology and as as i said like csrm is an evolving discipline and the threat environment has been very dynamic in the last couple of years so few of them is basically looking at centralized risk management teams as i said the organizational approach would give you a more holistic picture as well as
having that decentralized execution within the departments so keeping pace with technology change and evolving threats is key because as i said um the key thing about supply chain attacks is that it attracts the customer as well as you know exploiting the relationship between the customer and the supplier and also the fact that you know attackers are you know attacking the suppliers to enter a cyber mature organization because they want to exploit the weak link other key aspect is that hiring training and retaining expertise that is very key because knowing the business of the organization as well as uh tailoring to the needs of the organization is very key uh we cannot use all the frameworks because one size
does not fit for everyone so if somebody doesn't have an automated tool to manage suppliers and they just have like two of them an excel spreadsheet would work so it depends on the business case as well as the business that the organization is in again the other key the last key aspect last last but not the least is understanding the return on investment uh we cannot invest on on a tools which would uh not benefit us you know if the if understanding the whole concept of cost benefit analysis so in this research uh uh basically concluded that csrm of course and is an evolving discipline while varied practices exist at mature organizations less mature organizations are still needed further
practical guidance and methods for implementing and evolving programs and practices so some of the resources that i have used um from nist are here um that you can refer to um and thanks everyone for taking time to attend my session i'll just open session for any questions now
yeah do let me know uh because i know we have 10 minutes of time so any questions or thoughts that you would like to share thanks rob
thanks shelly so i have a question from awake so it's do you see organizations focusing only on parts of the supply chain risk directly related to delivery integrity of product and not on the vulnerabilities in the borrowed code long term system that's that's right so i think uh most of the organizations like big organizations which did not have a hold on their suppliers with regards to visibility into what code is being used is it propriety or open source they're facing problems with that because there could be an errors in codes that just come into your organization um without any notice so it's basically organizations are looking things from supply chain perspectives in silos because the supply chain program
has to be uh to a level of maturity which it has not been yet um so gloria that's a good question so i think for me like uh with the boundary or the scope of the discussion that i am associated with um i guess the legal contracts so there are a lot of discussions that are going on in industry with regards to what should be the supplier obligations in case of an instant response and then how much time they need to respond you know and and various other elements of legal terms i cannot speak on the legal aspects to it but it's time that we have conversations with inter departments as extensively as possible whether it's
with legal department or whether it's with supply chain team because that integration is missing that's what is causing that much gap in in the whole supply chain environment um it's it's because okay we are saying that the supply has to inform us but the question is where is it written so is it in the agreement is it in the contract isn't it the time to like update the legal contracts to help you aid in the process of risk management process so one of the key terms uh maybe i missed a mention but yeah the contracts and the agreements that you have with suppliers is very key
yeah so that's a good question vivek so the question is how many layers deep does the supply evaluation go example a supply supplier to primary supplier or further along the chain so um i'll give you two perspectives so first one is let's say you have um you know 10 suppliers and after them there's just one supplier that's key to you and that runs on player basically uses sub suppliers right sub supplier subservice organizations you know let's say the chain is too long if it's critical to you that basically determines the business for you like the business continuity of your organization in terms of some sometimes it's it could be as simple as you know supplying
microcontrollers for an organization who is doing in the manufacturing so how important is the supplier and it's necessary that you go into that depth and i can relate this to uh actual compliance which is soft to type to report so if you look at the standard from sae 16 to ssa 18 there wasn't a specific mention of subservice organizations controls in ssa 16 the stock report standard but if you look at the sae 18 it has specifically asked to look at the sub suppliers controls so when you don't have a stock report like an insurance from the supplier you definitely need to go into the depth of you know who are the sub suppliers most
of the cases it's mostly like you know a supplier sub supplier and there is a third one sub sub supplier so it might sound tedious at this point but it again depends on your criticality of the process or the program that the supplier is involved with your business
yeah so so yeah that that basically answers the question as well so that's that's how we do the risk management aspect right so what we are seeing is a gap because we are not able to relate the business risk you know and and aid in the risk management process because we overlooked that whole supply chain area because i have not considered the scenario where uh you know it's a risk to my customer right so as a supplier so if i'm using a product i should be aware of what i am using what controls do i have in place it's as simple as um you know having aws or azure product or any other cloud service product that you
use have you configured it from your end what are the controls that you made sure that there is no unauthorized access uh that has been given to the um to the adversaries or attackers or to any you know maybe an accidental disclosure of information so you have to always look at it like from a supplier so from a customer point of let's say i'm getting you know i'm giving a service to a customer so has that been defined again agreements what service i'm providing how is i won't i wouldn't be looking at how critical is my product to them but i would be looking what products am i using for my organization hope i made sense it's a little
confusing when i talk about customer and supplier but yeah as as i said again uh there are no questions right now in your mind or you if you don't want to ask here you can always reach out to me on linkedin uh it's by name monique the n uh i'm i'm there and i'm based on my career um so yeah feel free to reach out for any questions or queries





