Operationalizing Purple Team

Show transcript [en]
all right good morning besides i hope everyone is having a fantastic day uh today this morning and this session we have george ortiz he is the cto of scythe and he's going to talk to us about operationalizing purple team so thanks for joining us and i'm going to hand it over to you thank you so much pablo and hello everyone good morning oh look at that jake cran is here i see cena uh aka cheerio hello hello hello what a pleasure to be here thank you to besides and the organizers for putting this together it's so much work to run a conference we really appreciate it and thank you all for coming that's a new talk i've put together so
um as we go through it please give me feedback i can see the chat so i already saw uh the first question there coming in from cena so that always makes me smile and i'm also watching the discord this is fully live uh so if you have questions post them and am looking forward to your feedback because whenever we release new stuff we want to hear from you see if you found it valuable see if you're using it and of course how we can improve so today's talk is about operationalizing the purple team i've spent the last about year year and a half talking about purple team exercises and bringing value and a lot of
organizations have done this they ran their first exercise which is awesome but then i get the question what now do we just wait and do another exercise or what do we do and that is what i want to talk to you about today thank you again for that brief introduction pablo my name is georgia ortiz i am the chief technology officer at scythe we are an organization a startup that builds an adversarial emulation platform when we love purple teaming so been there exactly one year now believe it or not anyone that's following me on twitter and saw all that uh go down um also love contributing and giving back to the community author and contributor
to the purple team exercise framework the c2 matrix spent 10 years in corporate america running the offensive security team at citigroup and i also teach at sans i'm actually teaching right now believe it or not today's day six of security 504 so it's the ctf day thankfully i have a awesome uh ta there watching uh what's going on and hopefully i don't miss too much but i'm here with you now very excited and let's just get to it right so one of the big things that we are talking about today is attack detect and respond right working together to improve and evolve as the industry involves i mean we've all seen this happen right if you're new
to infosec welcome you're coming at a at a very interesting time where we're seeing humongous impact of these attacks all over the place right uh when the dry cleaner or uber driver knows about a ransomware attack that occurred at colonial or jbs and they know that you're an infosec they're like what are you doing how are we going to help this right so i'm really big on leveraging threat intelligence right understanding attack vectors how are these attacks happening building from that cyber threat intelligence making it actionable and then attacking ourselves i've been doing 10 years of offensive security uh at an organization and we bring value right because we are improving we are trying to stay a
step ahead of the attackers and fix and hopefully detect and respond much quicker before we are impacted and of course to do all that we have to track our work long gone are the days where we all worked in little silos writing o days you know full disclosure days are over etc we are all working together and that's what we're going to talk about here so what does an infosec team look like today well um if you're wondering about these unicorns these are the scythe unicorns they are awesome um what we do is we have cti teams right many organizations have cyber threat intel teams right and they spend a time going through and understanding attacks
grabbing indicators of compromise grabbing attack behaviors and they want their work to be actionable by various teams we also have the red team that works across the organization finding uh vulnerabilities and uh emulating behaviors that might or might not work in the organization essentially they're attacking it before the malicious actors do and then we have the blue teams the blue teams are our defenders right they have a tough job they're working in the security operations center they're hunt teaming they are doing uh defer digital forensics and instant response and they're in charge of making sure that if there is an attack that they respond to it and what we've been doing is bringing them together right not
operating in silos working together in a purple team and we started doing purple teaming and introducing purple teaming as a virtual team it's a slide i've used before and now i'm putting quotes around a purple team is a virtual team where the following teams work together cyber threat intelligence does the research understands ttps provides them to the red and the blue team the red team is in charge of emulating those ttps the blue team is in charge of ensuring they have detection and that they know how to respond to those behaviors so through that we publish the purple team exercise framework as you can see there on the right starts with cyber threat intelligence there's a lot of preparation because we
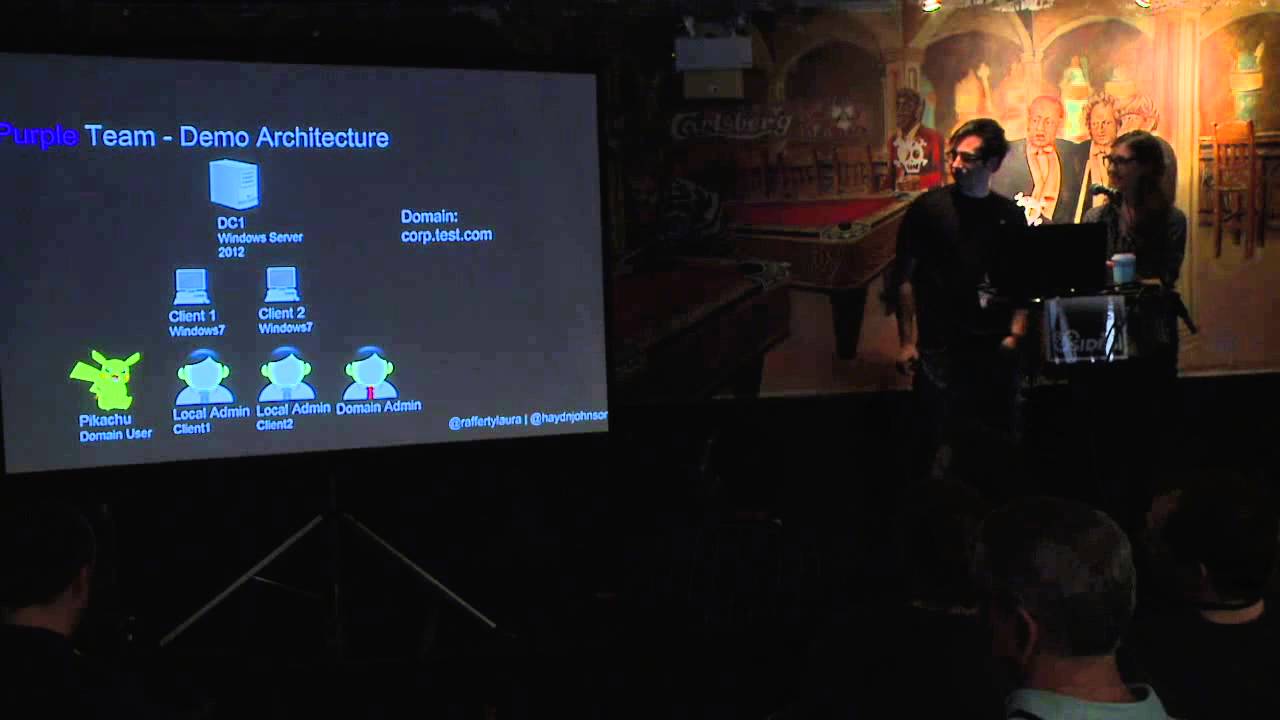
want the most efficient use of your time when we bring everyone together to sit through an exercise we want it all to function right so lots of planning goes on making sure we have target systems target accounts we're going to hit make sure we have an adversary emulation plan make sure there's an exercise coordinator attendees etc then we run the exercise we see and learn what is working what is not working and of course we have lessons learned so if you've never heard of a purple team exercise i'm going to level you up very quickly as we get into the next steps so in an exercise you have an exercise coordinator they present an adversary that is likely to target your
organization they present ttps tactics techniques and procedures those behaviors and the technical details about it then you all work together the red the blue the cti teams the attendees really interesting when you have senior management attendees because you bring up a ttp let's say downloading an iso from the internet what are the expected controls and one might say that's blocked we want to allow that what about um download or emailing an iso no that's definitely blocked or no they'll be caught by our proxy or that will be this right you have that discussion you set expectations red team then takes that ttp and emulates it does goes through and shows it on the screen a learning opportunity for everyone
there how do attacks work you're actually seeing it red team isn't working on their own over there in the corner and then giving you a report of things that work no they're showing it to you then the blue team after seeing that attack goes through and they follow their process they look to see if there were any alerts there was something that was logged here or there and they share their screens again another learning opportunity this time for the red team to see how the blue team functions and then if something didn't meet expectations or there are opportunities to improve we do detection engineering this is where you enable security controls maybe enable a log
or maybe a log was already there but there was no alert you tune that you want the alert to happen when the malicious activity occurs but not when regular activity occurs and then you repeat this throughout that day or that week however long your exercise is and of course you show value right you track all of this you track the ttps and these ttps are no longer something that is open or closed right those are vulnerabilities a vulnerability is patched or it's not patched it was exploited or wasn't exploited right open close very simple with ttps we are doing behaviors that users can do so sure there's some blocked behaviors but really what you need is for them to be
logged and alerted sometimes you have no evidence so you want to track this the image on the left comes from uh one of our partners plex truck which is a reporting solution tracking ttps no longer has open close but actually as alerted and logged or not logged or blocked and then on the right you have vector vector is a free tool that allows you also to track ttps and shows you uh how you improve over time so that is a 10 minute or less intro to purple team exercises if you want to learn more about purple team exercises we have the purple team uh exercise framework it's free you can download it um and we're actually working on version
two so we've learned a lot running purple team exercises from the consultant perspective because we go companies say hey purple teaming looks awesome i've never done it i don't know where to start i read the framework but can you help us and yes we of course can help you so if you're interested in stuff definitely let us know hit me up outside of this talk but if you want to do this on your own download this framework and uh check it out so great intros over we finished our first exercise high fives virtual double high five for all of you what now well now we need to operationalize this right we can do purple team exercises
maybe once a month once every two months once every three months etc right periodically but we know that we're gonna get new ttps discovered we're gonna see new attacks and what do we do with all that other time right the red team goes and works in their silo again the blue team goes and works in their silo cti ghostworks in their silo no we want them to continually work together one exercise is great but to get that collaboration it can't just be ad hoc so we are going to operationalize that and that is what we're going to talk about today if you already have operationalized purple teaming that is awesome where do we see this
going dedicated purple team as a group of people that have experience with cyber threat intelligence with attack and with detection and response and they work together understanding threats and detections it's a very tough job you need experience but through using a very simple step like i've just shown here going from a purple team exercise to operationalize to dedicated you can get there too so our focus today for this talk is how do we operationalize purple teaming as virtual teams working together so we built a new cycle the cycle starts when new cti or ttps are identified and anyone can do this it could be the cyber threat intelligence team that just read something new because they read
every cti report out there they're on top of all of these attacks it could be the red team the red team should be focusing on finding new ways to do things the red team should not be repeating ttps over and over because you can automate that the red team should be building new and finding new ways of doing attacks or the blue team might have found something they're going through their day-to-day and they see maybe the hunt team sees something hmm this is interesting i haven't seen this attack before anyone can provide and initiate this process right cdti red and blue working together you send this out hey check this out brand new cti let's review it then you assign a cti
member a red team member a blue team member to work together then over on the right step two we are going to analyze and organize these ttps if it was a full attack then we want to map that attack to miter attack we want to correlate with previous test cases are these really new ttps that we've never tested before or have we tested it maybe it's a new procedure is it the same procedure if it's the same procedure and we feel we have coverage we can verify that and your process can be over and for the short term but if it's new then we need to have a tabletop discussion this is how this attack works according
to the cti what is our expected detection response you have that conversation for the various ttps the red team will then understand the threat and emulate the attack one of the things i'll show you all the way at the end is a purple team maturity model that covers deployment integration and creation as you mature through it but the point here is the red team will emulate this attack while the blue team watches then the blue team will understand what detections they have they will see if they need to create something new if they need to integrate something deploy something and then repeat this once you do build out this new control new method of finding
something then you'll have to repeat that same ttp while you train your people right sock analysts right so far we've only had three or four people working together we want to inform the greater team let everyone in cti know about this new cti and how it currently affects the organization let everyone on the red team know this new attack method so that they add it to their library and add it to their automation and then the blue team knows about this attack knows that if they get an alert what to do about it so that is what we're gonna go through here and if you've ever gone to my talks you know i like being very practical
so let's get to it step one new cyber threat intelligence comes in right in this case cti read this new email this new blog post from microsoft's threat intelligence center a new sophisticated email based attack from nobelium cti team reads this says huh it's interesting let me share this with our virtual purple team email goes out or you do it through a ticketing system a tracking system wherever you can implement this i've seen it done in jira i've seen it done in archer we can do it on a number of different places the point is notify the virtual uh purple team let them know hey microsoft thursday this one was thursday afternoon uh their second one was on friday
afternoon right before memorial day right always comes in at that time right we can't get something on i don't know a monday afternoon no it always has to drop at the end of the week right so we assign whether it's self-assigned or manager assigned be like oh this looks cool i'll take it i'll be the red teamer that's going to take it the blue teamer says all right i'll take this one and of course the cti person that found this will be involved so what do we have we are going to initiate our purple team [Music] [Music] just sorry i couldn't keep a straight face on that one so a little comic relief there we get together now we need to do step
two analyze and organize these ttps what did we see well we have to read through this dense cti report we need to extract the ttps we need to map them to miter attack and then we need to correlate with previous tests so let's take a look if you haven't heard of this attack this was uh microsoft found this essentially uh this group this threat actor compromised the constant contact of usaid usaid is a legitimate organization constant contact is a legitimate email sending provider they are used to sending newsletters and emails to people that subscribe so you people that were interested in usa have subscribed to usaid they are receiving newsletters from them all the time the threat actor
compromised their uh their constant contact account essentially allowing them to build an email and send it to legitimate users that are used to and expect to receive emails from them they get this email and it says view documents what happens next well it was a spear phishing email it had an attached html that performed html smuggling that html smuggling attack downloaded an iso file that iso file had a malicious link a shortcut file that then ran a dll and there was also a decoy file in there so if we look at another screenshot here we see it loaded an image called d e class all in uppercase it had the documents.dll file it had an ica d-class.pdf this
is a decoy this is a real pdf file and there's a shortcut there called reports if someone double-click the shortcut it would execute the dll so if we look at the shortcut we see it was running this dll and opening it and essentially launching the command and control payload and establishing a connection to some server so thankfully this particular article this particular cti had miter attack mapping now when we do miter attack mapping one it's good to see it in reports but we're really looking for the procedure level right so in this case initial access tag two spear phishing via service new bellium used the legitimate mass mailing service content constant contact to send their email yep
in that email there was a url so there was a link that they clicked on it so that's t1566 excellent and then microsoft um decided to tag execution as t1610 deploy container a payload is delivered via an iso file which is mounted on a target computer i looked at this one and i thought this this isn't right deploy container is more about deploying docker containers so what do we do we go on the mitre attack slack right are you all part of minor attack slack you definitely should we have awesome conversations there some of those conversations lead to very fun polls on twitter so we debate this whether is this deploy container or not and
we reach the conclusion it's not actually putting a payload in an iso file is a bypass of mark of the web so even though this is amazing cti provided by microsoft a top security company amongst other things the mapping might still not be correct right and there's biases around here there's great papers around this and this is why you need multiple people working together because someone could have detected this but let's move on then user execution malicious link the user double-clicked on a shortcut file and then application layer uh for command and control dll connecting over https fantastic now let's analyze and organize this for our pleasure i like building little tables they're easy to read
so description of this new bellium the russian threat actor behind the solarwinds com uh attack compromised constant contact to send malicious emails with a weaponized iso file resource development this wasn't tagged before resource development is a new miter attack tactic right it came from pre-attack and essentially we mapped it to t1584006 which is compromise infrastructure a web service say compromise constant contact to then do spear phishing via service constant contact spear phishing a link a link that downloads and does html smuggling and then defensive agent t1553.005 this is actually the correct mapping of using an iso image because an iso image is not an ntfs file so it's not marked with mark of the web
which is mark of the web when you download something from the internet and you try to execute it you generally get the smart screen pop-up that says hey this is bad i'll demo that for you uh right now if uh when we got to the demo and then it actually ran run dll32 to execute that dll and it was executed of course when the user double-clicked a malicious file a windows explorer shortcut so this is also a small deviation from the cti's attack mapping and then command and control was the only application layer but i also used an encrypted channel so you can see that something net new can have multiple ttps for us to
take a look at so we have and we look at this and say is there anything new anything we haven't tested before well constant contact is an email service that people subscribe to we've never used that to deliver phishing emails then we have that hard discussion of can we even emulate that can we hack into constant contact and send emails from there or maybe mailchimp or maybe some other email provider probably not right maybe we can simulate this some way maybe work with them but this is going to be a lot tougher conversation to have we'll give that to our managers let them deal with it what we can do is take a look at t1553005 this is
subvert trust controls mark of the web bypass with an iso image so essentially if we create an iso image and we host it on the internet when you download that image you're able to execute it without any other control saying hey stop what are you doing something bad might happen so we can then inside of that iso include a shortcut that executes a dlo via run dll32 we've done that one before right run dll32 is used by like every single ransomware threat actor right but we can test that too and have we tested this before well we've tested run dll-32 before but we haven't tested downloading an iso image from the internet that's weaponized this
is net new to me i'm sure there might have been some other cti out there that's where you asked the cti team hey can you check into this while we build a test case so what do you do for a test case you've never done you do some research what's a great place to start atomic red team right atomic red team has a bunch of atomic tests a great starting point to see if there's a quick test you can do and unfortunately there wasn't an atomic test for this so this is a perfect candidate for our purple team step three let's tabletop this now we know that this was an iso downloaded from a browser
on an internet site what kind of expected detection and response would we have here well are we allowing iso downloads on the browser is our proxy detecting that an iso file is being downloaded and can we block it or maybe our next gen firewall can see this it's a good test case what about if someone's hosting a malicious iso file internally will the browser block that from being downloaded since we it wouldn't be going through proxies or next-gen firewalls have to see it i don't know do you know do you know if you in your organization are blocking isos at the browser level and then we also think about a little more test cases this was also an email what if the iso
file came as an attachment on that email have we tested that well maybe our external security provider blocks iso and image files coming from the outside i'm going to have to check but what about internal if someone internally sends an iso file that is malicious would outlook email allow that will our endpoint security allow that with the email server the security on the email server allow it i don't know what about mounting the iso do we have any detection for that how often do do end users mount isos probably never right i can see an i.t administrator mounting an iso but are end users do we detect this and then of course execution from an iso i don't know what about
unmounting the iso so you have this discussion of course i just did this role-playing here on my head on what i think most organizations would answer but your organization is different you see the cti you have to sit and think through these test cases so step four let's create an iso how do you create an iso that's a great question i mean i remember back in the day we would create isos and you can create a windows 10 iso with that little windows 10 thing but how else can we do it well i use twitter and i want to give a shout out to matt grabber matt station definitely worth following and very quickly matt wrote something on twitter that
that made a lot of sense adversaries choose iso and image as delivery vector because smart screen doesn't apply because it's a non-ntfs volume good that's very good technical detail in this test he created an iso that has an e a hello.exe if you click and load it it won't get prompted so thank you matt that was an awesome test case then did some more work my friends over at outflank mark smee and the whole team there had an article back in march about the mark of the web and getting um around this and then at scythe i actually had talked about this talking about defensive asian because when you download an executable from the internet you have the mark of the web
so we had a nice place to start but i want to emulate the entire attack so sorry for this slide that has a lot of words but this is the attack we set up command and control using https on 443 and we generate a dll payload if you're not familiar with how to do this first step check out the c2 matrix how to how2.c2matrix.com you can download a virtual machine that i built with sans you can get up and running set up a cd2 and create a dll payload in a variety of c2 frameworks many of them empire covenant mythic right all of these allow it right not the scope of this talk what we want to focus on is how do we
build this iso and weaponize it well i went online and found multiple ways of doing this and in particular i used the folder to iso project so shout out to them again not my work folder to iso is someone else's shout out to them we are working together and i hosted this up on our github you then copy and rename this dll that you created in step one documents.dll and you put in the folder to iso working directory then in the folder to iso working directory you're going to create a shortcut called reports and set the target to run dll32 documents.dll and the entry point then from a command prompt because i like doing everything on a
command prompt even though forward to iso is a gui app on one liner folder to iso take everything in the folder to iso and build out t1553.005.iso and we're going to call it the same d class then you have to add some other parameters there now we deliver this iso we host it on a web server we send it as a phishing link all the different test cases we talked about then when someone downloads this iso you can either double click it or you can mount it with powershell and you see i do a lot of things on command line you'll we'll get to that in a minute and then once it's mounted double click
the shortcuts and see if this works now of course i documented all of this because it's all about giving back right so demo time let's pray some demo gods quick uh quick uh item there so i'm gonna use scythe this is not a sales pitch i am literally just doing this for b-sides san antonio because this is the easiest way for me to create a dll i literally click next three times and we start a campaign we then download this dll select the dll download the dll yes keep that and we're done that's it now steps what do we do well we follow the community threats page that explains what to do we grab this dll
and we need to rename it to i'm gonna copy and paste because if this doesn't work it's because i fat fingered something not because it doesn't work documents.dll we're gonna cut that and put it in this folder so this source folder you can clone from github you go into folder.iso and you put it here now my decoy pdf is actually the cis security controls version 8 that just came out so you have uh some good decoys there then we look at this reports uh shortcut we go to properties and we take a look there what it's going to do it's going to execute run dll32 yep on documents.dll with its entry point perfect let's actually rename this to dll in
uppercase i don't think it makes a difference but i'm not taking chances on live demos so the next step follow my uh items here we run folder to iso take everything in folder to iso put it into this iso file and call it d class hit enter and it's going to build my iso so over here we have an iso look at that not too big 1.4 1.4 megs now we host this somewhere right let's simulate that because ain't nobody got time for that and then we go on to another machine this is called sky and i actually need to delete this one because that was my test so let's assume that someone just downloaded this brand new file
it's now on the downloads folder because it's an iso we can't mark it as mark of the web normally down here would say this came from the internet it's not now there's multiple ways for us to mount this we can mount this with powershell or we can just double click it right a normal user and how the us8 attack worked is they double clicked it so we double click this and it automatically mounts and takes us right here and if the user falls for it they double click this reports nothing happens you say huh that's weird well let's take a look at something else let's open up this file oh look the cis controls that's pretty cool
and nothing happens nothing else happens we are like all right that's cool we go back over to our attacker machine and there we have our callback we have our shell over https just how we created it and we run a little who am i just to prove that we are on that machine and we get the response back i think i sell five second callback so in a couple seconds there you go we got it working fantastic let's get back to our slides so we ran the test ran the test and it was successful so what hypothesis do we have well we have to do detection engineering now we would have if i had time only have
six seconds so i'm gonna speak a lot faster so detection engineering this is the part where now we know that this attack worked that machine i ran this on had all av had everything clearly a bypass smart screen bypass all our detections so what hypothesis do we have well an iso file downloaded from the internet by a non-it user is suspicious an iso file sent via email is suspicious and iso mounted is suspicious on on any user's machine that's not an it user process execution from a mounted drive is suspicious and a network connection from a process that runs from a mounted drive is suspicious i want to give out a shout out to cyber monk
he wrote an awesome post on detecting uh these iso images it was a two-part post so shout out to him reached out to him on twitter asked him hey can i show you some of this work and of course they said yes so cheers to you another shout out to randy randy wrote some cool uh detections here this is sysmon on sentinel but not everyone has that right maybe you have something else well let's look at what we got where was this logged did the proxy see an iso being downloaded if we would have sent this iso in an email would it have gotten through did we have visibility does the email server see that can we block that
extension what about antivirus antivirus doesn't catch anything right edr well depends on your edr this is why you have to test you can't just plug in your edr and say yeah we're safe millions of dollars spent we're good no you need to train your people you need to tune as new things come out hopefully you have at least this law ddr does a great job at logging this stuff but why isn't there an alert can we create an alert and sysmon you can detect some of these behaviors on sysmon it's actually what uh randy did over here and then of course you need to send these logs you have to send them somewhere if it's
an edr generally it's already being sent if it's sysmon you have to send that sysmon uh alert as well uh log and then you need to create alerts once you create the alerts you then train your people because detection isn't just an alert is someone seeing this and saying oh we just got an alert that this endpoint in the accounting department just downloaded and mounted an iso probably something we need to look into or better yet try to block it right only allow certain people to download these types of files right different things different ideas all recommendations and then of course what is the response so as i did this testing i had started with atomic red team there
was no atomic test for this so i built one i gave a shout out to carrie roberts who uh is super patient with my terrible ability of creating atomic tests adam machinshi who runs the uh red team uh the atomic red team and the open source stuff at red canary and of course red canary who uh are the ones supporting atomic red team so built this out on atomic red team did a bit of testing so now you can do that test now that test is a little different if we take a look at that test what does this test do well we actually created two atomic tests one mounts the iso the second one mounts
the iso and runs the executable so now you without having to set up a c2 or anything like that can come here and use this atomic test it has a prereq command where it's going to download this iso this iso that's on atomic red team is not weaponized it's not weaponized it does not have a dll it does have a shortcut but the shortcut doesn't execute anything so you download that shortcut that iso file and then you can actually mount it through powershell you can then dismount it atomic test 2 uses that that executable created by manifestation so same initial steps you download this iso called feel the burn you then mount it and of course this one
has to because you're going to run something in there you have to determine the drive letter when you mount an iso the drive letter that mounts is going to be different on every host depending on how many drives they have so it grabs the drop the drive letter and then it executes that hello.exe you then of course can dismount it and stop the process so now anyone that wants to test this can easily test this without weaponizing the whole thing if you're a red teamer though of course you want to weaponize the entire thing so if you want to follow step by step how to do this it's obviously on the slide but i've also posted it in our
scythe community threats github which are just that community threats number of attack chains that you can use to test yourself some of them require sites some of them you can do manually this one you can do manually of course the step one we cover how to do it with site you can do it with any other c2 how to dot the c2 matrix has abundance of resources for you to do that and last few things what happens next you have operationalized this new ttps come out you check them eventually we are seeing organizations building dedicated purple teamers so i always said that this was a virtual team but in talking to some of our more
mature clients they are actually building and having a dedicated team so the red team still focuses on building new stuff the blue team focuses on uh detections and this dedicated purple team works on looking at these new items of course you still operationalize this you're still bringing red and blue together but their main thing is to understand threats understand the attack and understand the detection so this purple team maturity model was created by tim schultz who works with me at scythe he's our adversary emulation lead and was presented at the purple team summit so essentially your purple team your people need to have a threat understanding and a detection understanding and as you build that out you have deployment
integration and creation that you do for each attack and each detection something i try to do here as a virtual team of course uh better have the dedicated team now if you want more content we love giving back to the community and that's we everyone at scythe uh the unicorn so we have a threat thursday blog there we look at bigger threats of full attack chains we understand the attack the adversary we consume cyber threat intelligence we map it to mitra attack if it's not already done we release adversary emulation plans in json for attack navigator as well as forsythe we emulate the adversary and we then do detection response and it's all available for free for you to see on our blog
so references like i said i did not do all of this on my own shout out to microsoft who was the original cyber threat intel on this manifestation for showing a brief proof of concept randy uh from uh binary defense uh he was pretty much my blue teamer here building out some detections for this um so shout out to to randy um and what else red canary of course red canary and the uh detection blog as well so all these references like i said didn't do this on my own we are a herd we all work together we have to collaborate and with that i think i did it right on time uh so i want to thank you for yours
and we'll take any questions that you have thank you again what a fantastic presentation george i appreciate you taking the time today so many resources within your presentation today it's fantastic do you plan on sharing that in discord yes i actually i'm going to plan share the references i am going to hold off on the slides because i'm actually presenting this at wild west hackfest on thursday so you all got it here first for coming to b-sides but i'm gonna present it there i want to kind of maintain it uh that way i know we had smaller audience here um so yeah do want your feedback though because bigger presentation there um and yeah you all got to hear it first
so let me know how it was if you enjoyed it if anything i can improve uh it's the first run i did so the timing was a little off i want to spend a little bit more on detection engineering showing some of the sysmon uh logs that show up and whatnot but i know uh i know what i got to work on and uh and yeah i'll share the resources though of course 100 i'll post those uh in the discord right now george uh i think uh looking through the discord chats during the session you got positive positive feedback everyone loves the energy and that you provided this morning so great great stuff regarding there's a
question in the chat here will the recordings uh be available i believe if george accepted the the ability to share the sessions then those those recordings will be available after the con so thanks again george i think you're going to join us on discord if i'm not mistaken right to i am in the breakout session what is your handle just in case uh some of the audience doesn't know and they want to reach out my name at jorge ortiz j-o-r-g-e o-r-c-h-i-l-l-e-s um i'm currently in track three in the clouds so thank you for those tags there i see cheerio i see uh volunteer hoop um but yeah you can send me a direct message uh don't be afraid i do not bite
um and or post it publicly however you want uh we're here and let's continue this conversation i this test case i purple teamed via twitter uh with manifestation and randy um who are you know very good detection uh engineers so uh so let's continue the the discussion and and uh hopefully we can all connect and work together we're a herd and i'm a hacker i'm also a security researcher and an advocate for hacking is not a crime and i'd like to share with you what being a hacker means to me because you see since i was a young young child i've always been a hacker i was the kid that liked to take my toys
apart to figure out how they worked and to see if i could make them work better when i turned 12 years old i got a job i saved up enough money and i bought myself my own computer and on that computer i wiped it clean started from scratch figured out how to build it from the ground up learned programming so that i could write my own software to run on my computer i learned modem communications and serial communications so that i can figure out how these online services that i like to use were working and so when i got into my career i took a lot of different twists and turns i started off as a penetration tester i
moved into consulting i worked at high executive levels building massive application security programs across a large enterprise organization i worked for product companies and resellers but through it all the one thing that stuck with me was this identity of being a hacker now we hear the word hacker thrown about in the media and it's usually connected with some type of criminal activity but being a hacker does not mean being a criminal being a hacker is all about this innate curiosity this passion to understand how things work and to see how we can make them work differently better create new things i'm reminded of a quote from a keynote given by jason street one of my colleagues in
which he said hackers are inventors and creators not criminals and freaks and that's the reality hackers are people who want to make technology better we want to make it do cool new things we want to understand how it works so that we can innovate we can make things better and we can make our lives all the more exciting through technology so i hope you'll join with me and with hacking is not a crime spread the message that hacking and being a hacker is not a crime we're not criminals we're artisan inventors thank you so much
[Music]
[Music]
[Music]
do you