BSides Boulder Pre Event Live Stream

Show transcript [en]
well good morning everybody um this is uh the b-sides boulder uh pre i guess pre-game pre-show um meeting kind of uh get a preview of uh what uh what to expect during uh the b-sides boulder event uh this year um and as would happen you know we are also making sure that everything that we are you know all of our setup is correct and that we don't have any technical glitches through this and of course i am having technical glitches in my ability to uh share slides right now so um that's fantastic um but uh i guess we can go ahead and just kind of talk through what the plan is uh for this um for this talk
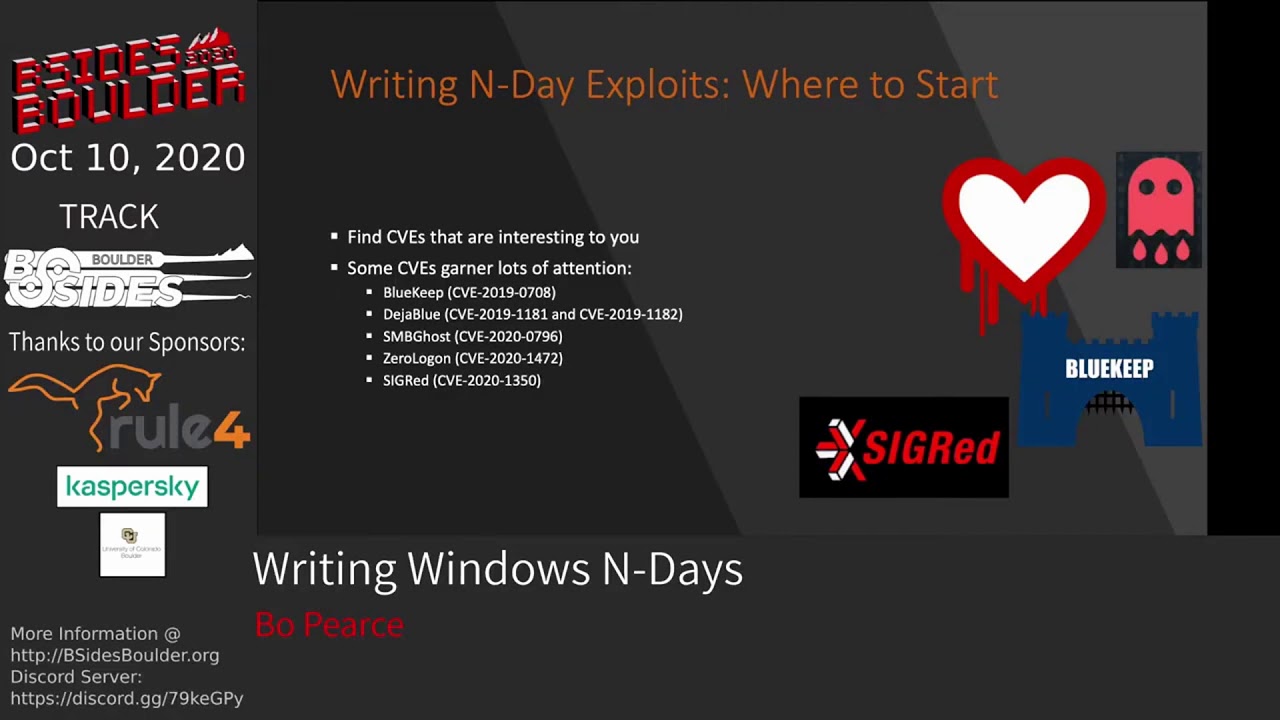
for this uh event um you know kind of going through how uh how did we get to where we are today um what's the plan for uh october uh 10th uh and you know kind of what so what kind of things do you have to look forward to um you know and we'll be able to get a preview of some of the talks uh that will be presented we have a few speakers online um so we'll get some uh some live uh previews there and we'll also get um we have a couple of video submissions for for some of those that we're not able to join us this morning so kind of how did we get here
to where we are today on is it august 15th now um back in september uh 2019 seems like so long ago uh we decided that it was time for uh b-sides to have an event come to boulder i mean b-sides has been in denver for quite a while and we felt that boulder also had a great security arena that that uh could be tapped and uh wanted to uh get an event in boulder um this was really started uh with a great team like an amazing team of volunteers you know with uh tyler bell james mickey little shands matt revell see robin paulie uh myself there were a few others who you know helped out
tremendously through the cfp process yeah and you know others that were able to help us out along the way as well and originally we planned to have the event in the spring um on april 19th and we had a great venue set up at cu boulder and started making arrangements for catering and speakers were lined up and at the point really where everything was just about set up and well then things kind of got a little weird right with covid so um we really wanted to have an in-person event so we kind of postponed waited you know waited to see if cu boulder was going to open up again and um when it turns out that uh the the limited
capacity that we were going to be able to have we decided that um we'd take it online and you know kind of go virtual so that uh that's that's what we did that's why we're here now um we do have a great uh lineup of speakers and you know we appreciate all their patience in enrolling with the changes as they came you know originally again they were planning on speaking on april 19th but now been moved to october uh october 10th um saturday uh so the plan is um the streams will open up uh early they'll open up at about eight o'clock um and you can go ahead and jump on there grab some breakfast grab some coffee you
know make sure all of your stuff is working uh and then opening remarks uh we'll start at nine o'clock uh with uh followed by a key keynote from erica um there will be eight sessions across two tracks um and the closings will be probably around uh 3 30ish you know given uh the time frame so you can um finish your day up hang out with the family you know have a good rest of your weekend after having an amazing you know saturday learning all of this great content so what else uh we uh do have some um uh we've sent out we really wanted to say thank you to all of those um people who originally signed up
for the event and um kind of you know stuck with it and stuck with us and you know understood that you know there's there are a few things that we can control right now um so we're sending out some some swag for those people we also have an updated website um just fresh hot off the presses this morning james was able to to make that happen uh thank you for that at uh besides boulder.org uh on there it's um fantastic it has the uh all of the talks you know the schedule you know so that you can kind of choose which ones you want to see live and then you know which ones you want to come back to
and revisit those talks uh a bit later um and you know the speaking of the the live liveness of the event there will be you know a discord channel set up so that we can interact with each other interact with speakers you know part of you know part of it just like any security conference is you know really just hanging out with uh with other like-minded individuals and you know um asking questions and getting those questions answered so those uh will be available there as well um i think really that is all that i have to to set up ahead of time um we have i mean see now we have a few uh speakers that you know wanted to go
ahead and give a talk about or kind of give us teasers and previews about what uh what they were going to talk about so um i guess we can start uh with uh al and jason do you want to go ahead and chat about yeah absolutely yeah happy i'm happy to um sure my name's jason um i'm a red teamer at a social media company um we're going to be talking about moe's which we'll get into in a bit al is also going to be talking with me so let him go ahead and introduce himself yeah my name is alexander strahman i'm an old co-worker of jason's um and we've worked really hard to kind of put
this together i currently work as a security engineer with sandia national labs where i do uh some internal pen testing and uh as well on the side and bug bounties with jason so yeah take it away jason sure yeah so effectively um we've been the stewards of a post-exploitation tool specifically uh targeting configuration management systems um if you've ever been on an engagement against a larger organization you've probably come across these and so yeah essentially we're just going to be uh talking about the work that we've been continuing to do in that space and uh we are going to be releasing functionality for the final uh configuration management system that we hadn't supported previously so we're
really excited about that and um yeah that's that's what's coming up from us yeah nice right super exciting um all right do you want to go i guess um i haven't said hi good morning to most of you now um sorry about that good morning to all of you and thank you for jumping on this morning um is it terry riordan yeah terry hi um so i'm tripping burden nice to meet you um i am a senior threat analyst and shift lead on the vmware carbon blacks managed detection team and so part of what our team does is actually looks in customer environments for new and emerging threats and the most exciting one that we've
caught so far is the first known use of the blue keep exploit vulnerability and exploit within a customer's environment and of course that's just the initial stage right so after that we were able to see what the attacker was attempting to do including scraping credentials moving laterally they dropped a post-exploitation route kit as well named as nymcodic so we are going to go through from the initial exploitation to the attempt to move laterally and also scrape credentials and walk you through each of the tools and actions that the attacker is doing nice apologies and um it's not just me that will be presenting also adam valencia will be as well and he's actually the analyst that caught the attack initially
nice so will we get like a toolkit that we can start uh using the the blue keep for ourselves um no unfortunately well actually there's already one out there there's actually a module in metasploit for it so okay nice well i'm excited to learn a bit more about that as well yeah and then um we have a great keynote um for this event and erica is uh coming to give our our keynote so erica go ahead and introduce yourself and yeah so uh yeah my name is eric norenberg and i actually work with teree at vmware carbon black i've been there for a few years and i'm a senior threat researcher there so i mostly do um
malware reverse engineering um and some threat detection thing like that uh work with therese team um hand in hand and i'm gonna be doing keynote i'm not gonna go into a lot of detail but basically i want to talk about lessons learned from failure and how you can learn from them and how personally i've failed hard especially in the last year and the lessons that i've learned from that and kind of just keep it a little light hopefully to uh introduce the conference great great yeah it's uh so important that that we don't um hold ourselves down after after failing right and just take those lessons and and move forward absolutely if you're not failing then
you're not trying hard enough i agree absolutely and then james you are also speaking um do you have
here come the videos hello my name is james mckee i'm the global developer security program manager at trimble and i wish i could be with you live today but unfortunately i'm behind the scenes making sure that the stream is running properly but come october i will also be presenting to you on beginning pen testing android applications as part of this we're going to sit down and talk through the process of what it takes to get started working with android application penetration testing everything from setting up a device so that you can work with it to setting up emulators so that you can work with and for doing testing capabilities additionally we'll talk about extracting apk files from the android device
decompiling those analyzing them so that we get a good understanding of all of the permissions and items that are associated with the android application we'll talk about analyzing certificates for signing use extracting source code from the apks setting up an environment for doing dynamic testing and techniques for doing dynamic testing as part of it and where you can go to help improve your skills and get a little bit better with this so with that said i'm super excited to be one of the speakers at b-sides boulder and i look forward to seeing you all in october
hey everyone i'm greg foss senior threat researcher and security strategist with vmware carbon black excited to join you all for the first b-sides boulder and dive into the trends that we're actively tracking in relation to destructive malware and attacks specifically the evolutions that we're seeing across nation-state actors and targeting critical infrastructure systems with impunity and how crimeware groups are adapting their strategies to ensure profitability from their attacks adversaries of all kinds are leveraging modular and increasingly more capable malware command and control infrastructure and marketplaces to optimize their profits we'll examine these trends the underground markets they operate in and how the playing field is transformed i look forward to seeing you all there
cool well um for those of us that that were here we we didn't get to see those but it's great for those of us here we can certainly this is um going out live and will be recorded so if you're interested in seeing those talks as well head back and you know catch the link on there and then of course on the website there is a full list of all of the talks and the schedule for um for the event um let's see and i guess really finally the last thing that i have is uh the event you know again is october 10th um kicking off at uh 9 a.m again the streams are opening at 8. but you
know hope to see you guys there and you know thanks for stopping by here if anybody else want to you know talk about anything have any questions about this
if not i think we're good this was uh quite a bit shorter than um than expected but um thanks everybody for making time and um uh joining us on this saturday morning yeah thanks so much