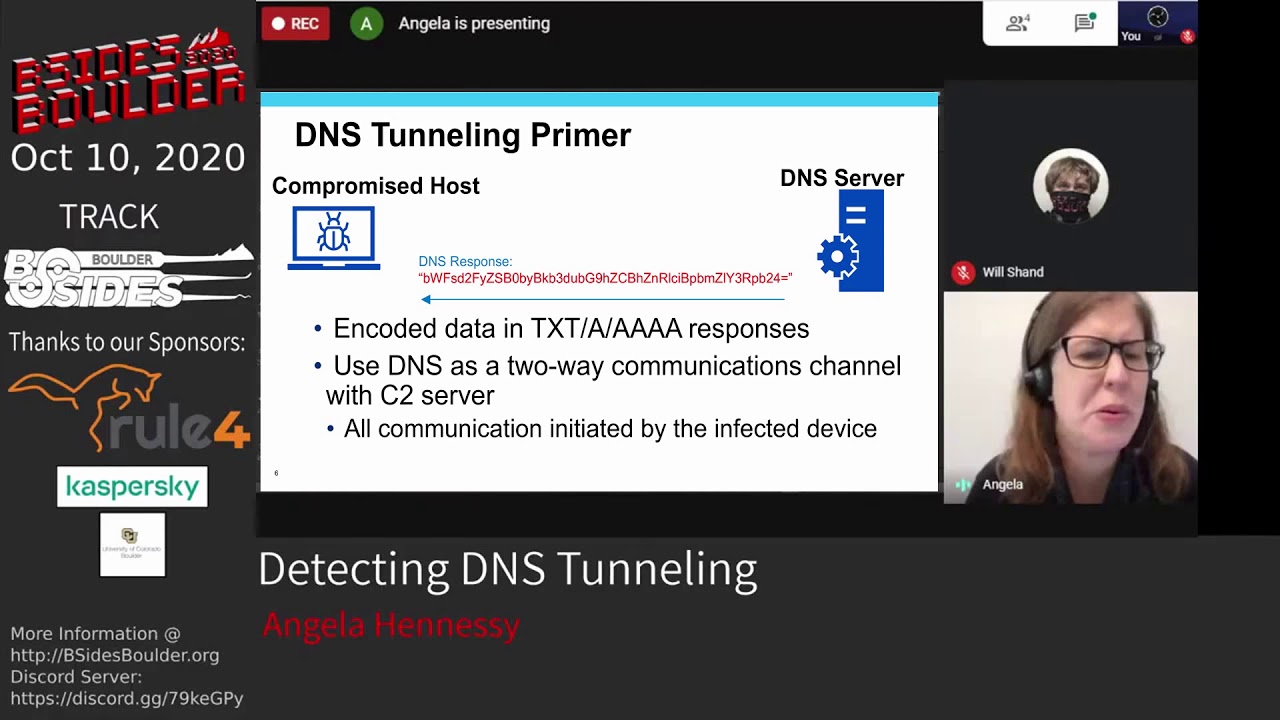
Angela Hennessy - Detecting DNS Tunneling
Speakers
About this talk
DNS tunneling involves sending encoded data in DNS queries or responses as a means of bypassing security controls. Using machine learning techniques, we are able to identify tunneling domains and track malware that uses DNS for C2 communication. Despite the ubiquity of DNS, too many security teams today do not adequately prioritize it as a focus for monitoring. Malicious actors make use of DNS tunneling as a means of communicating with infected devices by sending encoded data in the subdomains of DNS queries and in the DNS responses. Since DNS traffic is often not well monitored, this allows the malicious actors to bypass security controls and communicate with compromised devices within protected networks. When we began searching our DNS data, we had no confirmed instances of tunneling. Therefore we treated it as an anomaly detection problem. The initial features we chose were the average subdomain length and average entropy, or amount of information, contained in the subdomains. Domains that made use of tunneling tend to have queries with longer subdomains and higher entropy due to encoded data. Manually inspecting the outliers identified a domain used by the Ismdoor malware, which was tentatively linked to the OilRig group. Devices infected with Ismdoor send information to the C2 in the subdomain of AAAA DNS queries, and the C2 responds with hex-encoded data in the IPv6 address of the answers. Since an IPv6 address consists of 16 bytes, moving any considerable amount of data requires large numbers of DNS queries. We will describe the protocol used by the malware to communicate with infected devices, which takes place entirely over DNS. We will also describe how we found another active Ismdoor domain that had not been previously identified. After investigating more instances of DNS tunneling, we added more features to our model based on Natural Language Processing techniques. These include extracting words from the subdomains and measuring the difference in the distribution of letters from that of regular English text. Based on these additional features, we employed a semi-supervised machine learning technique to assign pseudo-labels to samples that were similar to known malicious tunneling samples. We trained a machine learning classifier using the known and pseudo labels, which we use to flag new domains for tunneling. This classifier identified several domains that appeared to be sending hex-encoded data in subdomains, and sending base-64 encoded data in TXT responses. Further research identified the traffic as resulting from Cobalt Strike. Cobalt Strike is popular threat emulation software that is increasingly being utilized by threat actors for targeted attacks and post exploitation activity. We've seen dir listings being sent to the malicious actor in the subdomains, and evidence of PowerShell scripts and Mimikatz being downloaded in DNS responses. We are able to automatically verify the Cobalt Strike domains by their response to a certain type of query that instructs the malware to download a DLL over DNS. After we verify the response, we download the entire DLL, which takes up 1,700 DNS queries. So far we have identified and notified 24 victims of Cobalt Strike activity within their organization.
Show transcript [en]
you