Adventures With Internet Telephony Appliances - Darren Martyn
Show transcript [en]
all right so hi everyone so um this uh we're going to be talking to today about uh internet telephony appliances so um firstly uh I'm Darren I do security research previously was a gainfully employed security consultant type person and now I'm just a freelance uh [ __ ] who messes around with computers I guess um and that's where you can find I'll have stuff up next week like uh supporting material on the website and GitHub um so that's the web address and all that for all that um so yeah there's a bit of a backstory to how this talk became and this project became a thing so um after I was done with last year's
kind of being a little bit unfair to Cisco um I heard this rumor about somebody selling a net border remote rud o on one of those really sketchy um shitty like onion forums andage isn't it what it's your homeage don't tell them that um the so they were offering this exploit for 80k and then they were offering ss7 access or like ss7 network access for 10K a pop and I was like this seems like an interesting rumor to follow up on but because I don't have ad Grand to you know throw around um I thought it'd be funnier instead to like go find the product download it reverse engineer it and see if I could find it
myself for free um cuz yeah um so I end up with this like wild Adventure it turns out these products so badly put together that it's like the OAS top 10 but as like a product offering um so yeah so ended up with a bunch of different full chain exploits to go from unauthenticated internet user to remote route on a bunch of products by this uh specific vendor Sanga uh so also um because this vendor is really crap at handling disclosures and I really can't be [ __ ] sending bug reports to a random Gmail address on their Wiki which just doesn't seem like the best uh you know disclosure route and because they've ignored responsible
disclosure of um attempts from other people last year um you guys are all the first to hear it
um you have about two days before I publish all the stuff online so you know if you want to go take over any telecoms uh you do have like a first mover advantage yeah I'm not a lawyer don't do that so yeah so I picked a bunch of these uh Target products from Sanga um cuz I noticed a bunch of the products were similar and also because they were the ones that was able to download from the vendor FTP server where you know they offer their software up for downloading um so the products are the S NFC which is their net uh net board session session border controller or n border session controller which is also
sold under apparently another brand name as the Vega session border controller um and I suspect they've a few other different white label brands for their for their products um because I've looked around at similar products and they all kind of look the exact same so I think they're just kind of rebranding it and you know um there's also their netor transcoding Gateway um their ss7 media Gateway um their vo gate way and their video MCU the video MCU I don't actually know what it does I found the iso for it the other day and took it you know looked for it found a couple of bugs it and I was like neat don't know what this does but that's kind of cool
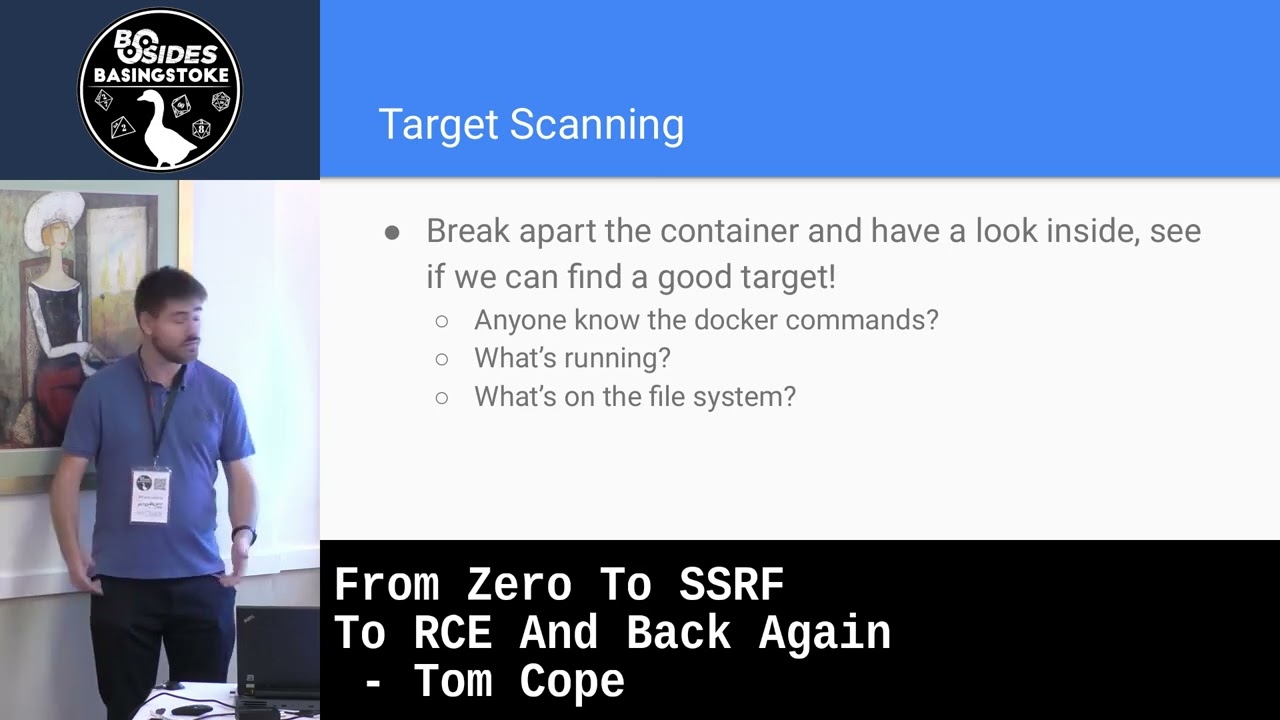
um for context um the session border controller in particular is quite interesting because without getting to to the Weeds about Telecom stuff but they kind of live in a very privileged Network position in telecommunications networks um so they're kind of important um they actually provide some security features to telecoms um and you're going to see that trusting this vendor with your Telecom security is kind of a horrible mistake so we'll crack on into the uh good stuff the general process is how um I and found the bugs was step one was just W everything from direct DP server um and then install all the appliances in VMS and then figure out how to get you
know SS access to the appliances so I could you know start the process of um you know looking for bugs now in this instance um it was easy there was no like there was no jailbreaking needed you know you could just ssh in and get a shell um and you know start working from there on some other vendors appliances you end up in like a restricted shell and you know you to [ __ ] about with editing like boot parameters and Grub to like you know do stupid [ __ ] but here it was easy uh The Next Step was starting you know doing basically code review and config review on these appliances um and
that's hand waving away a whole bunch we're get in that minute and then the kind of biggest step that took most of the time was um basically looking at their web interfaces [ __ ] around with burp um using p by 64 to like hunt for command you know command injection issues um etc etc um that was kind of the process and you're going to see that not much more work than that was needed for um and either fun were they hard to viral no they just ran in VMware um there was no so with some appliances it could be a real pain in the ass to like virtualize them but luckily with these they were
just isos you could just boot them um with another vendor whose stuff I'm looking at their stuff is an absolute nightmare to get working without like calling their customer support because I'm not one of their customers I can't do that um the the examining config files bit actually does a that's kind of it's a it's a big heavy lifting statement because oh yeah just look at all the config files and see if there's any problems uh you'll spend hours so the interesting bit is with some of these they had multiple web servers installed but only some of the web servers were running or they like multiple different Apache config files and only one of those Apache config
files actually being used there was a lot of time spent like figuring out which process is the webs server and which of the [ __ ] config files the web server is actually using and which one it's not actually using um cuz a bunch of them like a lot of their appliances shipped like dormant Services because they literally just copy and paste a crap from their other stuff and switch stuff off as needed um so there was a lot of like messing around looking through proc PID like FD and you know basically trying to figure out what files has you know what the what the hell is going on here um it was extremely frustrating but extremely
recing um as for the code review aspect um basically just download with this it was just download to my local machine start looking at it um real code reviewers and real programmers will probably use like an ID or something you know that have like a nice setup with like Visual Studio or something for me it's just grapping and opening things in Nano um because Nano is the best text editor [ __ ] them
the uh for other appliances you for other appliances I've looked at in the past uh this step of code review is involved like decompiling stuff and disassembling stuff but in this case luckily enough all the relevant to my interest code was in PHP in Python um there was nothing OB fiscated there was no there was no magic needed you know um so um the probably the most uh the most profitable part of the whole Enterprise was this very straightforward process that whenever you get a proprietary vendor Appliance and you get SSH a through shell it download a py it's um it's uh it's a tool that basically it it's kind of like Sison right for Linux basically um it'll
basically print out what commands are running in real time you know it's like it'll just dump out what commands are being executed at that time and then open burp and start clicking on [ __ ] and start putting in unique values into Fields like put in uh you know random number here and then check the P by output because quite often these appliances are kind of strung together with just shoving things into subshells and like executing random commands based on user input and this is like the fastest way to find Shell command injections um there's a quite trivial way of automating this um it's not hard you can write a a uh what's it a a b check script or you
can write a full burp extension depends on how much you hate your life or how much you enjoy Java um to literally just iterate over inputs shove in random values and then parse like a log file afterwards to do correlation um there's a few different ways to do it uh it's kind of the homework for anybody who wants to you know build their own automatic bug finding machine is just do this uh I might open source my implementation in a couple of months it's absolutely [ __ ] clarify you're looking for those values in a new execut yeah so you AR ex yeah exactly arguments to exact so you could do like you could do the monitoring side
of it with like BPF filters or something um or S trace or what have you so the first discovery was uh I found with the session controller and the Gateway um they both used pretty much the same codas for authentication I'm pretty sure it was written by on crack the trans coding Gateway uses an older version of the same code base which is actually completely safe um and I also don't know why it's completely safe um but I'm going to talk you through the horrors of the authentication process on the sangoma net border and you're going to you're going to begin to get a feel for like how fractally [ __ ] the whole platform
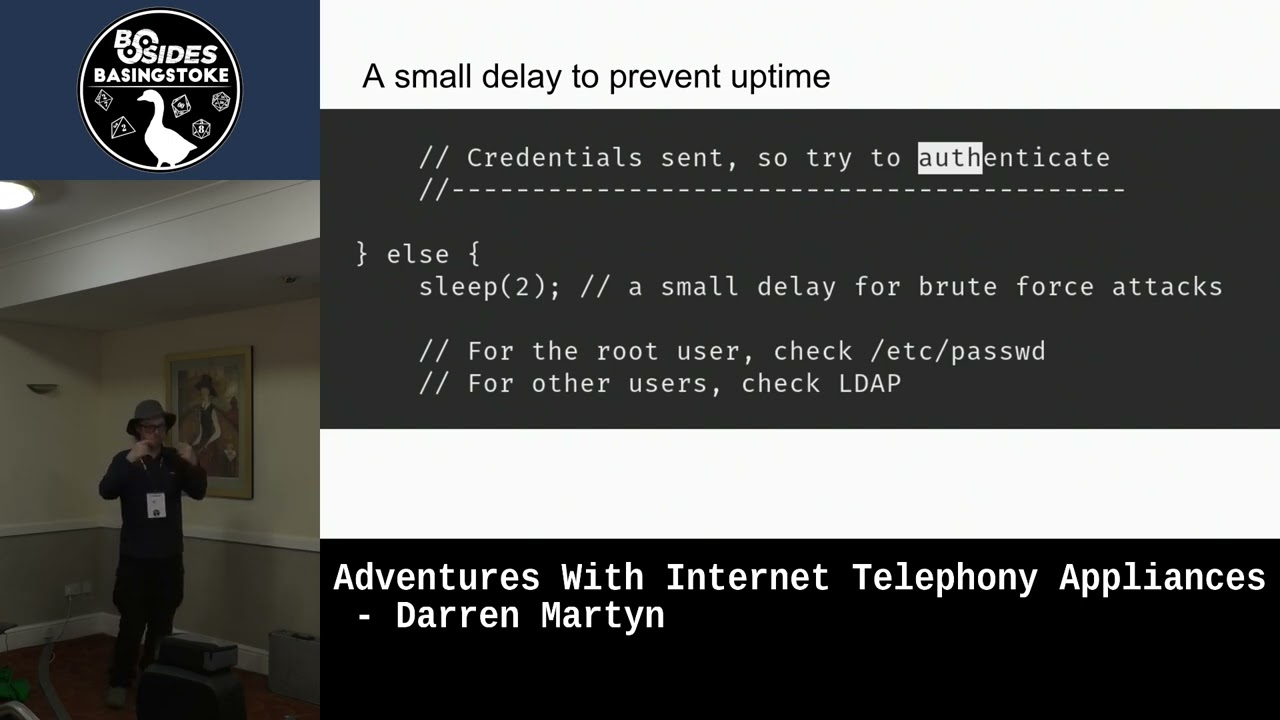
is so the first thing is um also the comments are always in really weird places in the codebase but the first thing they do is they take uh post parameters reserved username and reserved password and they don't do any any stripping any escaping when you put in your username password there's no there's no fil there's no first pass filtering um and then we do this which um ABS Fu so it's like you know when you try when you go to log in it sleeps for two seconds and this to prevent Brute Force attacks but instead all it does it hangs up that thread in the web server for two seconds so if you make I think it's 128 login
attempts the entire Appliance shits the bed and becomes inoperable and you just have to repeat those threads every two seconds and it just it'll just hang um so I guess they just [ __ ] hate up T just a delay course doesn't mean again you know it's uh and then they did this and unfortunately the only way I could really step through this with a screenshot of code and I know that's kind of horrible to look at but what happens is they take this binary right or in what it really is a python script and they load in their own custom version of shellac from this uh shell x.l. PHP and then they go okay we're
going to run this command sng user management and then they take the password that you put in they take your username they use your username as an AES key to encrypt the password so I mean that's a whole [ __ ] thing over there and then they construct this command line string putting in the username and the encrypted password with D- action equals login D- user username encryp password the password they execute that and then they check if the return code of this uh command they've ran is zero you're logged in otherwise get [ __ ] so yeah so what they how it all works is we're going to take the username password from the post request
we're not going to do any [ __ ] checks we're going to put in as sleep today for two seconds cuz uh you know we're going to encrypt the password and then we're going to stick it in a command line and then if that command exits with return code of zero you're in otherwise any other return code get [ __ ] um so I started to look at the custom shell exac implementation and all it does it repeatedly calls Escape shell CMD on inputs and does a couple of like slightly tricky string parsing things so that's what the command that's executed looks like it's you know actually login us it blah blah um the escaping in place
so the first thing that I started thinking of was argument injection when I saw this I was like okay they're calling Escape Escape shell CMD we're not going to be able to stick in like back tick you know run whatever so thinking oh maybe we can put in some arguments and make it forcibly return zero but because of the escaping we can't use spaces and this it turns out is where I tripped over somebody else's bug from 2018 and 2019 which they reported both times and VAR instantly fixed hence the escaping that deleted the ability to put in spaces um um those the wonderful people in AO had reported similar issues um so the escaping that de Bata
to deal with their bugs kill you know cleaned out you know the use of space to do argum injection however tabs and spaces happen to be the same thing as far as your shell is concerned so they've delete they've removed your ability to put in spaces but you can shove in a tab and [ __ ] We're Off to the Races at that point boys so in 2019 they ejected dashh to call the health function and in 2019 uh calling help calling for help gave you that return code of zero um it doesn't do that anymore um however today if we do d a info it'll return that zero exit code that lets us in so if we put in the
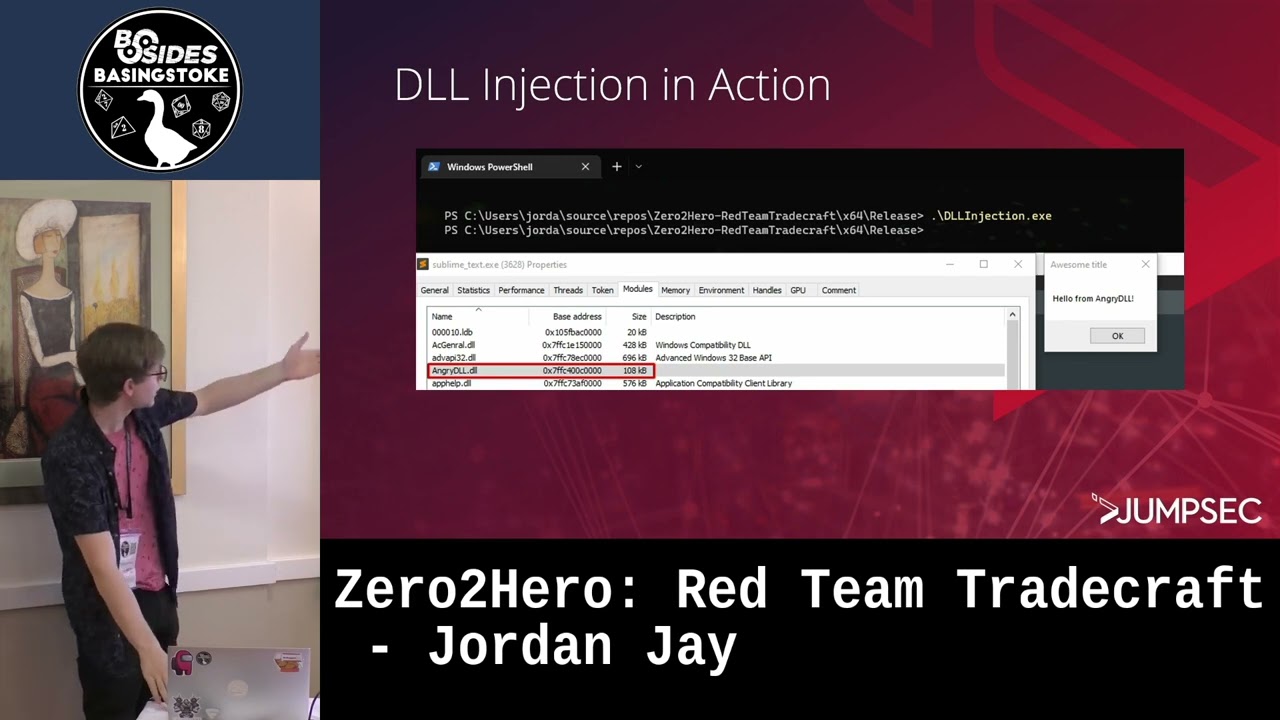
username field rout tab d a tab info and any password you want just whack the enter button you're ready um so this is the small python snippet that uh gets you in um so less than 10 lines to bypass off on a whole bunch of their products um you know have fun um super super sophisticated exploit writing here you know um The Next Step obviously is getting code execution so these wonderful people just take a host parameters and just Chuck them into system um so if you send to one the when you're logged in if you send a post request to one of the pages with the they just with uh the parameter interface they just don't do any
escaping on that they don't even use their fancy custom Escape shell CMD crap they just you know ye it straight to system so there is an immediate post off once you bypass the all you get straight away you know there's an instant easy route to code execution um as an unprivileged user I might add well we're going to get to the next bit so the you combine this with the last shitty piece of python and you have a full you know remote code execution for the because you know you just send your command to the machine after you know bypassing the login and Bobs your uncle Dr off RIS so at this point you have a shell as
used web config which is basically just a renamed Apache user so you're like you know not a very privileged user kind of um however the web config user is in the pseudis file and the pseudis file is quite possibly one of the most amazing things I have ever seen like the amount of commands the unprivileged user can run as route is incredible um it's like every time something didn't work they was like [ __ ] it we'll just give it pseudo PRM for that you know so it's like we've ended up with this there's like this whole magical Wonderland of ways to get root at this point and uh we'll just go through a couple of examples um it
really is kind of a Choose Your Own Adventure though and it's actually a great learning thing just to go through all the options and be like oh how would I get rude if I pseudo access this command um so they for some reason give you uh sux the Comm noop so you can just you know call a shell straight away you know okay might as well have just given you you know pseudo Su at that point um but also they give you pseudo access to Yum and there's a very standard GTFO bins method to get a root shell from that um they also give you pseudo access to Tar and there's a very simple way to get
root using a pseudo with tar uh so you get you know guess what another root shell um they also give you pseudo access to PhD you know it's hard to say if these are in increasing or decreasing M yet and open SSL that actually took a slight bit of effort because there's no compiler on the box I did have to you know put in like the mildest bit of effort but you can also use the for some reason they allow you to do pseudo open C so you can just load in a custom engine shared object get a shell that way um flag you know it's like they could I you'll get to the config file in a minute I've
got I just put it in three different screenshots so so [ __ ] uh they also give you pseudo ACC to the command Service uh it turns out that also give you a sh um and then there's a bunch of others so ah the screenshots kind of but like this is this isn't even like the full list of commands you can run with uh privileges as the web config user this is literally part one of three um so you can run everything from like cat MV CP zit TCP dump Z tail uh net you know shut down service Chone CH mod whatever and yet there more no idea it's literally like they just kept adding crap you know for
compatibility reasons you know at some point they should have just been like like [ __ ] it let the web server run his brute it'll be faster and they did spoiler alert so we ended up writing a full chain combo exploit that you know you run it it'll upload and execute a it'll use one the command injections drop a webshell use that to upload a Prest use that to upload a troan which will call back um and I kind of put together into a really nice fully automated Funtime package um which you know just gets you super reliable shells um using uh my favorite back door in the world tiny shell um nobody's written a better piece of
Linux malware since 2003 I'm sorry that we peaked in 2003 with TSH um nobody's done it better yet so um and now for something completely different but exactly the same the NSG suffers the same authentication bypass also suffers post authentication post off command injection plus all the previous local trives bugs but it's also got something that like I think they were huffing paint or like like like eating lead or you know something that day in the development shop because there are some there there are some things that will you'll see because they run an entire second web server to run a whole second bunch of services cuz they've got a paty running with all that crap that we've got the
alt bypass and all the code injections for and then they decided they're like oh that's not good enough we also need to run Fusion PBX which these people also make we need to run that but we're going to stick that in engine X and have a patchy reverse proxy through to it but for various reasons we're going to modify Fusion pvx do some absolutely demented things um and you'll see in a minute what I mean by absolutely demented so in Fusion PBX in checkout. PHP they patched in this uh this this very questionable piece of programming where if the request parameter embedded is set it just sets your session username is super admin and your session groups to admin member and
super admin it just goes oh if question mark embedded equals true you're the admin now um
it's like I've been I was questioning my sanity when I saw this like why so we how many customers does this these people have quite a large company we have to assume that they've been breached already like their products this is absolutely horrendous where was this code R if can tell um so there are comments all over the place for there's code dating back to 2006 this code from this code like from last year the latest version of their product was pushed out like two months ago um and it's also still completely [ __ ] got to be made of people just off the street it can't they can't have any coding standards or design well when you see when you see a
comment saying Echo session username you have to assume that they don't even use an IDE yeah to don't to [Music] debug I don't know what a debugger is it's like it's like they're hand it's like either so and a lot of this code's like quite old and new match together so it's not like I can say oh they just asked chat GPT to write them a tele a telecom's product you know this is like somebody sat down and wrote this decided they were proud of it and decided to build a company around it to clarify on the uh scope of it it's not the customers it's the what the customers doing that those devices are
sitting on ss7 poti on TI to everywhere they they're where you can just redirect SMS messages from anyone in the world at that point that's the thing these are like privileged telecoms positions like if you compromise one of these devices you can because the way S7 networks work to kind of gloss over a bunch you can now do stuff like SMS interception or um call hijacking tracking people all sorts of terrifying nation state Shenanigans um are now yours because somebody can't program a PHP apparently you might wonder by the way what checkout. PHP is used for and I'm glad you asked because it's used for this thing uh this other thing called vx. PHP which
checks if the group is super admin which we already have super admin from the question mark and beted equals true thing and it goes access granted as it com otherwise it'll Echo access denied and exit PHP exit doesn't do [ __ ] in pH P so I'm not really sure what they were getting at here um I'm not sure the person who wrote this new how to program PHP it feels like a pearl programmer had to learn how to do PHP real quick uh I should check that after this I'm pretty sure they probably have a bunch of the shiny um letter numbers cuz they're pretty big vendor um the VXX thing though it offers
you three options you can run a shell command you can run a PHP command or you can run a switch command for the ss7 switching stuff um the shell command does well it it disappointingly does exactly what it says on the T um the single most dising uh remote route exploit in the world go forth and have fun um the you can can also if if shell commands aren't your jam you can also just run arbitary PHP because it'll just evow whatever [ __ ] you put in oh but it does it
does kind of cross scripting here everyone else satisfies the be uh Innovation um there's also more you can upload and download files uh um because also why not like they'll just Chuck in like a file read and a file write for free there's another one that I didn't even bother screenshot where you can just run SQL queries um cuz you know we're going for the full OS top 10 here you
know as for remember that that command with ram rout right well these Geniuses when they decided to slap the second web server on they were like no no no we're not having engine X run as an privilege user we're going to run the [ __ ] as route cuz it's easier I I guess the that's probably [ __ ] it that's probably exactly it they got sick of adding commands to sudoers they're like [ __ ] we just going to run this [ __ ] as rude um the oh yeah there results that lovely post author root shell the one that's slightly more complicated and you know we just we put together a lovely super reliable exploit for that while
we're at it um cuz you know you might as well make a small bit of effort to you know stop yourself feeling so disappointed in the product um so the As for the Post althor C it's like vaguely interesting because they've got a function called validate um that's supposed to do some filtering I have no idea to this day what validate is supposed to [ __ ] do um because you can just it I have no idea it cuse validate on like some parameter but the parameter that goes into the command line is a completely different one they've written a validation function which is like some Rex crap in it but then they don't use
it on anywhere anything where it's remotely relevant so you know they clearly had like an intern in that day who knew how to code you know some poor like you know seconde uni student was like ah going to write some input validation and then somebody was asked to implement it you know after like they probably let them go or something I was like yeah I know where to put this I'm just going to stick in some random parameters and not the ones that actually matter um so yeah by the way when this is the output from py the thing I mentioned earlier on which is really handy for hunting down these shell command injections um cuz you can see all the
ARs and you can see see like in the ARs where your command injection is happening um and helps you really rapidly figure out what's being stripped or escaped um so the adventure so far is for the nsse we've Al bypassed code injection and peses for the NSG we have all bypass code injection forests we have all bypass feature abuse and for the NSG we also just have that straight remote route because the question mark and beted equals true I was like well at this point you know the we need like an automatic instant remote route for the NSC right cuz you know otherwise it's it's feeling a little left out right we need to you know make sure there's
exploit PIR here you know so um oh yeah the NSG by the way when you're when you're logged in it also just has command injection as a feature um it just has one under like the configuration menu it's like oh just run command for when like you know you've Mis Mis administered the system so badly you just need to Oram something um oh yeah so this by the way this uh this uh command executions a feature actually explains the embedded equals true hackery from earlier the thing that was baffling me um so the NSG admin interface on Apache uses the embedded equals true Al bypass on the fusion PBX under Eng next run command's route cuz and it also use
that to hand off a load of its file editor stuff um and the only reason that they're doing this as far as I can tell and this is like after like a lot of scratching my head and going why is they couldn't figure out how to pass a session between Apache and engine X um that was too hard like the cookie gets passed along you know but it couldn't figure out how to like share the session variable or like the state between the two web servers so they just went we're going to stick in and off bypass to make life easy that's just that's by the way that's my best guess at this time um cuz
I noticed that like your cookie gets passed along but the other web server has no idea that you know that there's a session that's like the only logical explanation of found so far um oh yeah so the NSC right we need to find an instant remote route from that so it wouldn't feel left out it turns out there if you go to the path SL SSH on it it's running this thing called gate one it's like a SSH terminal interface thingy and if you [ __ ] around with the web socker messages you can spawn a root shell without bothering you know doing things like login um all you need to do is open the script console in
your browser and paste in a couple of WS stop message thingies um I couldn't be asked automating this because I just don't like websockets um somebody who hates themselves can probably write an exploit for it um but it's not going to be me uh um yeah some honorable mentions from their other products the video ncu and the ntg um because the oos top 10 is in fact a checklist there is a external XML entity gobin xxe um that also gives you srf uh there are info leaks due to a thing called PHP CIS info being exposed for absolutely no reason there is uh more post authentication code execution there are more post uh file right and
reads as r and there's a bunch of cross- side scripting uh the funny thing about the MCU and the ntg the their kind aable mentions is they use an older authentication mechanism which calls out to a binary written in C that inexplicably is the one piece of secure C code I've seen in my entire [ __ ] life it has not a single problem it is perfect it is like 100 lines long or so and it's completely you know it's like the best piece of C programming in the world and inexplicably runs on these and handles off and has no security problems whatsoever um and then they decided to replace it with this janky construct a
command line in Python garbage um they should just sto programming you know a while ago but um yes this you know just cross scripting [ __ ] all over the place you can pop your alert boxes you know you can probably get your bug Bounty money with this uh what kind of monst zero really yeah yeah it's alert zero why everything broke Dar didn't alert zero on the internet oh crap it was my first day at Crow strike to I don't work for anymore I'm the official QC R for this is why they ignore your responsible disclosure because they're expecting to one suddenly it makes sense you know [ __ ] software they just it's company that does this so
there are a bunch of other vendors um and I'm already looking at their competitors and they're they're just as bad to to comment more about it like PHP written it looks like Pearl it's about the time when these things were designed the time technology came together so standard of code is going to be replac software archology there is definitely Vibe of that like where it's like looking into the past almost um oh yeah there's the infak there's this like handy page you can go to the tell you like Ryan crosses and all nice information about the system and I just thought that was nice they were like we got to finish that checklist L you know
we got to put in sensitive info League somewhere um we've got the xxe we've literally got the most textbook um xxe it's actually really interesting cuz it's like they implemented the you know the example xxe almost there's no there's no hard work or effort going in it's like here is buggy soap interface you know from like what's that what's that thing it's like uh Dam vulnerable web app or something that's kind of The Vibes of getting off it um so the the fun thing is like with these it's really you get this Choose Your Own Adventure thing and I did actually have a nice graph of all the different routes to get a rout shell but
I forgot to save the [ __ ] graph after spending ages making it but you can just picture it's like a do here of unauthenticated random person on the internet a lot of routes and Route and it's like you know um you can literally mix and match the bugs though and that's actually where it kind of gets interesting from a um if you're a threy thread actor type you could pick your combo of the day to avoid exploits being fingerprinted cuz you could just pick a slightly different one from like the 20 different variations which would probably give like threat intelligence people a really hard time because they'd write a signature for one and it never show up
again because you'd be using the slightly different one there'd be some person writing snort rules you know smacking their head off the desk the impact of this is um well they're in really quite privileged positions in telecoms and telephony networks um the session border controller specifically has like a security function for preventing like bunch of Fraud and Abuse stuff um so they're kind of important and you would think don't put these in the internet um and I was told by somebody else oh these are never exposed the internet well it turns out you can actually check with Showdown or census searches and no these [ __ ] are exposed the internet all the time by all
sorts of interesting people um there is some evidence of in the wild exploitation of some issue in them and it it's probably not even one of the bugs that I've told you about because there's about 20 different bugs that I haven't found yet um there is some evidence of exploitation though because there has been an optic in weird incidents of S7 abuse that could be linked to somebody hacking sh doing Shenanigans um and yeah like um there it's right for abuse you know there's a lot of there's a lot of risk there's a lot of potential shenanigans that can happen um as for the what next um so the cobase appear to be shared around a bunch of products and
a couple different brand names and I a sneaking suspicion they have some other brand names I just have yet to figure out what they are um a brilliant introduction to cyber security project would be doing a audit of some of these products um you'll come up with brand new exciting findings um uh what's next for me is um I've written a bunch of nuclei scanning thingies for vulnerabilities that wasn't HT I have not written Med exploit modules because I [ __ ] hate Ruby um you could deal with my shitty pipon scripts instead but maybe you know somebody is probably going to implement a MPL module for some of them um and yeah questions comments and abuse
if anything works for the telom company uh I'm just going to run yeah I guess have you tried have you tried just even though success uh no somebody else did last year for different bugs and was ignored repeatedly um you should still said this oh probably send to on Monday I'll give everyone here a head start uh yes I just want to say thank you for making everyone in this room feel much better about their job security it almost feels like someone broke into the systems in in the early 2000s and made all this [ __ ] like have to work with and justed there's probably some NSA guy who's like [ __ ] we' have
nothing to do here I think we can blame God for putting the simpler times before the more complicated times H cons I'm testing some of these sbcs on Monday can I have the slides uh yeah I can I can do one better and I can give you some of the I can email you the explo code on
Sunday so the the other thing of like um we talk about like sometimes these Services time files and things for those that left kind of systems Turn Services are an excellent way to try and get access to internal services so you can basically use Town Services which are designed to allow like stuff behind mats to talk to each other and often you can use that then talk to like local post or other things on the same network yeah you can use turn as almost a proxy literally people written like um socks proxies to turn proxies you is it like Turner or something exactly yeah yeah yeah so where do you kind of find most of these ss7 bridges are they like uh
while this internet people when like sell Towers can in to the like the text message Network so a lot of the ones I found on the Internet seem to be small telecoms companies like little you know tiny um like telecoms companies in um not First World countries and some of them are um large telecoms companies in definitely First World countries yeah they're you'll like everywhere like the weird thing is you find like I found these being ran by like hobbyists as well as like government so you can just like say that somebody's roaming on your network and get all T yeah you can oh yeah so if you do the S7 Shenanigans like after gaining
access you can do stuff like reroute messages to through you um and other Shenanigans like that that's a whole huge topic though um that I'm not the most qualified on I think in generality one one is what was useful here was correlation between what's passed on the network and then what gu run running the system sometimes people have visibility of one Inus detection system right small will defect the particular exp be much more effective I could find it in generality if I correlate those unique streams with what's coming through the system called ex specifically um string that need to be done bit more how defensively actually up that these things there's probably something interesting to be done with
like um Network proxy logs and your edor logs there's something there's something there that you could probably do yeah that could be quite interesting umis CIS Cally lo you that with your IDE second thing just me now is um UK and other countries they have reference like so every time you publish a book it's going to go to Cambridge Oxford Glasgow Etc um why why doesn't some organization probably under thees of the MS security Center uh have some law that if you have if you make an appliance and that's being used you have to send send that Appliance you know physically to to this organization and give them the support access to be able to
AIT I mean they could Outsource some of that
do that kind of I'm going to share like some ideas for detection but because these products you can't run meteor them so you're kind of [ __ ] uh yeah I'm going to write some I've got like a couple of attempts at snort rules which are really bad at writing but like I've got like here's what you should be looking for we could have yeah no we could we could absolutely like write something something at least for the blue team people at least you swap the prods out done uh yes um I do have there's sbcs from another vendor I'm not going to name them at the moment but I've started reviewing them and I've already found
some kind of grim Grim things uh not yet but if I can get a hold of their software um the big issue for me is actually getting a hold of the software to audit um so if anybody happens to have any nice telecoms Appliance ovas or images you know just drop me a line we'll do a free security review and you know not short their stock before full disclosing want to volunteer to be the the people that intermediate and say that you give this if you give access you might find out about nice way
all right one last question com at this from a finance I'm used to you must be this secure to drive requirements is there is there nothing equ with the ss7 network you can be someone who wants to join it uh at the moment it does seem to be like if you have money it's like the the gate to like becoming a little Telecom company is literally have you money and can you get another telecoms company to like Bridge you in which is just a question of M um there are a lot of dodgy little telecoms companies based off certain islands off the coast of the UK that have previously been implicated in like allowing Bad actors access to that
Network um hypothetically I'm not naming names great talk um you win goose you