Zero2Hero: Red Team Tradecraft
Show transcript [en]
so uh welcome to my talk zero terror red team trade crap um quick display might finish these slides two minutes ago so i got way too excited when submitting my cfp and now there's there's a crapped undercover um there will be a blog post going through everything in a lot more depth more topics as well as i'll be sharing a full uh you know pre-recorded thing on twitter afterwards um but yeah so about myself i'm jordan j i'm 20 years old i've been consulting for a year and a half uh currently work with jumpsec and previously with f-secure consulting um i've only done the sixth form so my iq is uh i believe four and i have
successfully rick rolled the fbi i have the top one central highly just like everyone else on the platform and i'm currently holding you away from the bar so no problem so as you can see there's a lot of contents um the bottom two i've cut out just to save time i'm gonna try and rush through a lot of it as quick as i can um worth mentioning obviously it's a zero to hero the i've tried to take more so kind of fundamental techniques here and show you guys how those work because they take pretty much apply to any type of payload you know fishing uh post-sexual tape whatever you like credential harvesting whatever this is
mostly defensive so the first thing which is quite heavily debated topic is whether you should use staged or stages payloads right so there are issues of both and both are kind of useful in either situation everything in red teaming is situational unfortunately so the biggest thing in my opinion is stages are really dumb um they will make a lot of assumptions for example say use metasploit or cobalt strike it will uh assuming that the parameters are correct or there's a cookie that you're using or something that it's looking for it will instantly just send you the payload and the bluetooth now household payload just by mimicking your request um however stages payloads are massive if
you've ever used something like sliver or anything go related you're looking at easily 10 megabytes or above which if you're trying to fit that in a word document it's going to take you a while to paste it it will probably crash um so yeah there's advantages to both as you can see there i'm not going to read through all of those um yeah ultimately it's all situational and just being aware that both are an option is kind of key people typically forget stages payloads exist so just bear that in mind um yeah so the importance of encryption so here we have two pocs they are both very simple self-injection what that means is essentially we've got a piece
of shell code which is just like assembly or executable code but smallest bytes and we have made a section of memory or allocated a section of memory that is executable readable and writable typically you should avoid doing that for the sake of simplicity i've done it and basically you wait i lost my shirt i thought sorry um yeah so with encryption it's going to make you all very sad it's a lot of maths and everybody hates maths but i have a simple trick right we can do single bytes or all this does is toggles bits in our payload and for some reason microsoft haven't figured out how to detect this yet um they've had metaphors been out for
about what 12 years now um and for some reason they still can't detect it as you see at the bottom we just have a very default looking interpreter with https um on the left this is what happens if you try and compile it uh without simples or gel code on the right all it did was zoro it with the letter j um and then it bypasses defender including cloud protection which is interesting so now you're all signals right you toggle bits you do nothing else you bypass everything with these everyone else who's a try hard ais fanboy gets signatures slapped rental checks and you you're crying always and as you can see you know we have our shell called up
there um yeah just checking the fact of the notes and yeah metal split released in 2010 so for some reason microsoft haven't figured out how to soar it with all 255 bytes yeah um so moving on this is an example of southpaw uh of self-injection um essentially what this means is again we're calling virtual alloc here um i'm not going to go over exactly what everything in the windows api does tell me what the blog post etc does but essentially we're going to allocate a section of memory within our current process and it's going to be executable and readable and writeable uh we're going to decrypt our shutter code nice and ready that's been loaded
up there in shellcode.h and essentially that's just a default it's the same payload as last time um it's been pre-loaded with h before i put it in there for compilation and static analysis reasons yeah so we decrypt it we write it through process memory and then we simply create a thread of execution starting at our shell code um but what this will do also for those who don't know what a thread is essentially a thread is like imagine when you open a process it runs code right if you have if you have multiple threads it allows you to run multiple pieces of code at the same time that's as abstract as you kind of need it to
get the understanding of what's going on uh then at the end we make a call to wait for single object that's just a really fancy windows api way of saying hey we're going to pause for a bit because if our program were to close here it's going to also close our shell and then we've just killed our own shell and we're a bit dumb so again i'm trying to fly through this here because a lot so with create remote thread process injection this is a little bit more useful for us because we don't have to keep our malicious process open in this case i chose to target the blind text you can pick pretty much any process that your user
has access to typically you should probably pick something that's um more used for say or more commonly going through making network traffic uh so something like you know teams slack anything like that maybe a service host anything just lots of blind text um and again very very very similar concept except the only difference is this time we open what's called a handle to our target process a handle is like a way of establishing a channel of communication between processes in this case it can be between files it could be between a multitude of things on windows essentially it allows us to say for example view its process id its name where it's stored its child process what
dll's got loaded blah blah blah blah and again we call virtual alloc this time we call virtual x which means extended and all that means is it just takes a handle to a process so we pass our target victim process handle we saw our shell code again we write the shell code to the process memory and then we create a thread this time using create remote thread instead of create thread and then we can close our handle and close the process our shell code is now executing within sublime text and i don't think of a pc for that once it's very similar or a proof screenshot but yeah basically the same so moving on to another technique
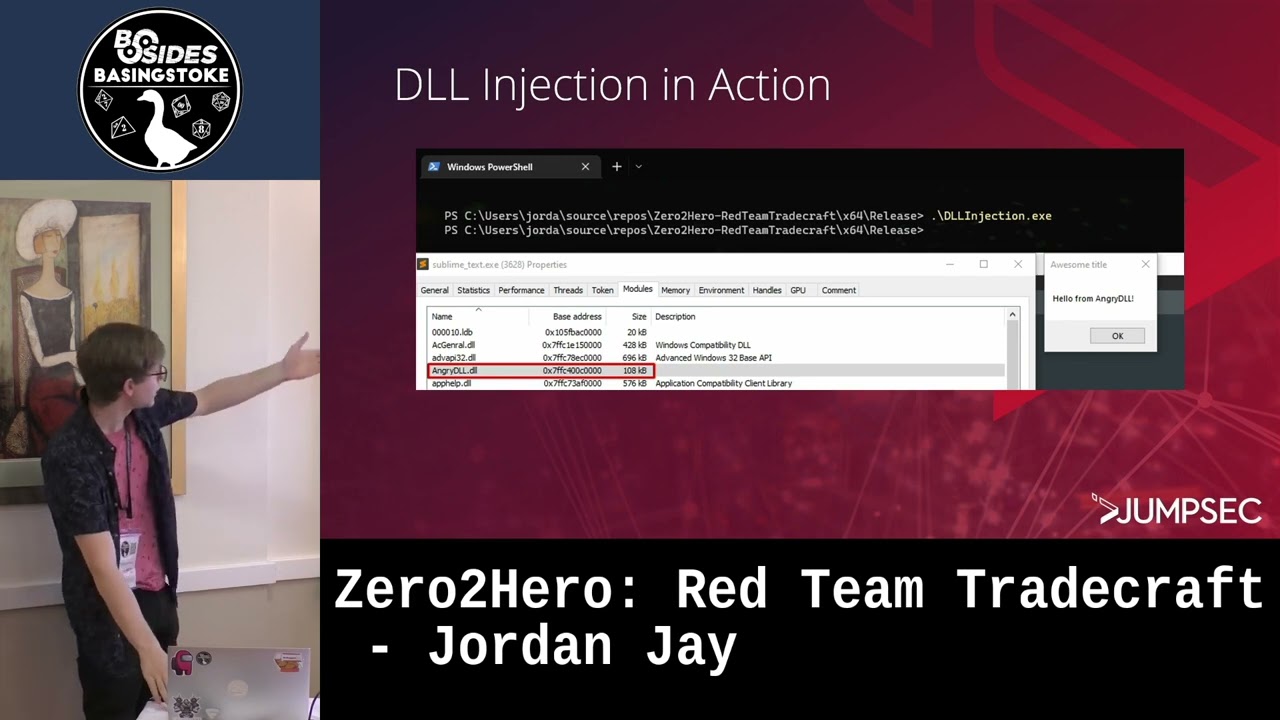
because those two obviously extremely common very simple um yeah so we should try something else because it's too detected so dll injection again this is very simplistic fundamental but it's key you kind of understand it before we move on to the more about stuff so every dll or at least by default will have a method called the other main ionization um and essentially what this allows us for this will be called as soon as the dll is loaded we have every dll when it's loaded is given a reason for it to be loaded i believe that's the new name for it it used to be called something else and i forget now but essentially it breaks down into
format methods you've got process attach process detach thread attach and thread detach in this case i've basically made a dll that when it comes when it's loaded into a process it's going to make a message box for us as a you know nice simple poc um i have a duplicated slider um but yeah so next thing we need to do is now we've got a dll okay it sits there on the file system but it doesn't do anything else so we need to inject into a process so this is a typical this is pretty much the most pog standard way of doing this again this is very well signatured as it's basically the standard way there
are theoretically infinite ways of doing this but the easiest is to abuse um load library a which is the method you usually call if you were to load a dll into your process the issue we have to work around here though is we can't actually load dlls into remote processes load library just doesn't allow for that so what we can do instead is we can write the string of the dll like the entire file path into memory of our victim process we then um as you can see we've got our process normal and then we allocate memory through it write it to memory etc we're just writing as if it was shell code but this
temperature supply and then we're going to essentially get where load library a is within our remote process or our victim process rather using that we can then create a thread that calls load library for us from within the remote process or the victim process and we can give it a parameter about the lr name because that is also now stored in that process and that way you've loaded your dll and then you can close your process and that's it so as you can see there it is in action we run it um sublime text now has angry dll.dll loaded and we get our message box to pop up nice and simple from here you know you
could do again weaponized further the reason this is such a benign payload is because the payload the way you would weaponize this isn't really specific to dll injection so i figured it wasn't worth much value um but we can move on to some more kind of the cool niche wacky stuff here so in so there are multiple ways and within.net there is a false reversal vulnerability for some reason and it's been known for years and never been fixed um but upon launch.net programs they're memory managed right and this means essentially there is a garbage collector typically we can actually specify our own custom garbage collectors which sounds great but only administrators can do this however due to the final
inclusion vulnerability for some reason they um they only check if you for example put like c users and then you put like an absolute file path administrators can do that but if you put like dot slashes at the start of the environmental variable um it assumes it's a relative path and it must be in the trusted directory and thus any user can specify a dll what this means is by users being able to specify this dll or not dll sorry specify this environmental variable they whenever a dotnet process is launched as you know there'll probably be loads on your system um it will now load this dll just by default purefunctionality.net so again we have
simple dll um the only differences are we're going to override the gc version info uh method what this is is essentially the first method that's called when your garbage collector's loaded so it's easiest without breaking things um and we have to use a version infrastructure because that's what it's going to be issued as set otherwise it won't actually carry on with anything and it will break but yeah again i've just used message box a to give us a nice easy proof of concept this is working and this is how you would actually make this happen so you hop into cmd you uh set your environment today with a bunch of dot slashes at the start and then you
pick your dll you run any net process in this case i tried just.net itself and there you go it runs your dll this is discovered by someone called amansek i cannot find the original blog post i think it got taken down or maybe their company change names who knows so the next thing and a lot more complex is process hollowing with shellcode uh what process holding is on an abstract level is essentially we're going to start a process in what's called a suspended state this is where a process starts and it has one thread of execution and it hasn't executed anything yet it's just sat there at the start of the executable ready to fire
and we said no no wait a minute and essentially during that time now suspended we're going to locate the um entry point or where this thread is going to start its execution relocate that and essentially just overwrite wherever whatever is going to execute with our own shell code we resume the process and now whatever process we had is now executing our shell code rather than its actual normal functions so in this case the first step here is obviously we're going to need to create the process so in this case i chose svc host svc host is very commonly used for process halloween um i probably avoid if you're going to be doing it yourself um the ox4 here that is the i've figured
out what the flag is exactly called but yeah not the creative spencer there's a parameter name i understand that but yeah ox4 is created yes yeah so anyways now we have a process that's created and suspended waiting for us to do things the next thing we're going to need to do is actually locate this address of where it's going to start using code so the first thing we're going to do is create a process basic info structure or object religion and we're going to call zw query information process essentially what this is going to allow us to do is get the base address of the peb the peb being the process environment block i believe
and an offset of 16 from here is essentially where our entry point to this thread would be or at least the offset from the image base so we need to find this under the image base so then sorry i'm not explaining this very well there we go so the next step now that we have that and we have the rest of the pv this is kind of what i'm trying to explain here i gave a diagram because i knew i wouldn't explain this to it very well but essentially we're going to read the first 512 bytes of the um and this will give us uh the dot headers and potentially we may read a little bit it's the
anti-headers 512 is just kind of the arbitrary value i gave because we need to read a lot of bytes um and as we can see we're going to simply read the process memory from there what it's going to do is give us all the data that is stored there and the b start and we need to essentially locate e underscore lfa new um e alofa new essentially um if we can find that we grab that value that's stored there and we add ox 28 to it this along with the pe image base will give us the start of that entry point of that thread that sounds like a lot of spaghetti but there will be a better blog post to
follow but essentially all we have now we have the entry point address it's very very very simple it's just the same as normal process injection we'll decrypt our shell code write it to that address that we've just found and we'll resume the execution of the thread and once that's done we have then bypassed defender we've got our shell back and that's with cloud server protection on etc even though it's a super documented method and yeah it's pretty useful and for some reason works way too well in my opinion um yeah so you can improve upon this you can combine it with other methods etc one would be for example abusing sign microsoft executables so if you've ever done red teaming or pen
testing or even used corporate network you may know of the concept of application wireless essentially what this is is typically it's a system for example in built on windows you have app locker where that stops people from running random random dodgy you know virus.exe it will only run for example trusted microsoft excusables um what we can do well sorry there is a picture of what will happen if you try and run something that is a non-trusted and that also makes everyone very sad so what we can do to get around this is we can abuse many many things for example from dll32 which you'll see a lot by cobalt striker's default and also um install util seems to be the kind of
go-to for those who like bonnet um i wrote ooh there to hurt you all um yeah so essentially all we need to do is override the uninstall method within install util reason being again it's kind of like the whole thing with the net garbage collector um every user on this machine can uninstall things with install util but only admins can install so by overriding the uninstall method we're able to kind of give ourselves two ways of executing our process so one malware runs it this avoids dynamic analysis as it will typically run it and jump to the entry point and this is fine they'll write ubu and then exit however in our case we're going to run
it with a story util and we'll call the uninstall method in this case we could have anything here typically i thought something to do with process following and that's kind of a nice combo it works quite nicely um bypasses i think so what's intercept text as well um and yeah so here we're gonna i think actually changes to a message box for the poc um yeah so as we can see so first of all you run it as normal this is how um a intrusion detection system would run said thing if it was to try and figure out it's malicious as you can see it just prints it will go okay well that's benign what's the point and in our case
we're going to be running it with in store util this is stored at the same path all the time um if you want the 32-bit version just remove the 64 off of the framework and it's pretty much the same path and then the slash u-flag this means uninstall and we will call this and then there we go we can see instead of giving us our google output it's given us a message box uh i'm aware in the poc sample here it's console right line but i change it to message box um i went through that very very fast but uh yeah
any questions and i was kind of a bit very fast but uh yeah yes sir it was the research
um but yeah that was all i could find i couldn't i tried to find the old blog post and everyone's like dissolved and dead [Music] do you have any upcoming research um yes so at the moment i've been messing around a lot with making custom packers because i feel like packer is kind of one of the more useful tools for a red team because rather than trying to for example obfuscate something like mimi cats or you know your cobblestone payloads etc etc you can just smack it all into one custom pe packer and it'll do everything for you so i've been looking a lot into different like for example um sandbox evasion methods such as measure using
your cpu temperature to check if you're in a sandbox or um stuff like measuring mouse movement etc etc people typically just do these in an automated terminal script so those just won't either read or won't exist um typically people use stuff like whether you're connected to a domain to check this kind of stuff but it's very significant and very easy to detect on a blue team side whereas checking your cpu which is a little bit more niche um that's kind of the stuff i'm working at the moment yeah why wouldn't you have to write something yeah um
if you like if you were to generate a payload with msf venom like default payloads or detect um if you put any effort in like more than five minutes you're probably fine um yeah i don't know just literally do anything other than default and you'll find you mentioned as well uh the process hollowing with the install util combination gets passed so far into the effect edius for that to work though you do have to use a custom https certificate because the default one in metasploit is signature so um deepak inspection on the traffic will show that but other than that it will bypass pretty easy