PW - Poppin' (Digital) Locks - Devin Egan
Show transcript [en]
I packet the Sun body in order last you're actually I one guy coming from Beijing in China all the way Dramamine always participated passwords called for three days and then you went back to Beijing in China so no I short really yeah yeah yeah most amazing is not big okay so give it up with you perrin organizers for a venir today title nice talkin see is poppin digital locks so today when my talk about today I'm talking about bypassing digital locks I'm gonna discuss kind of a retrospective of digital locks to get us and get us in top of frame or the the mind frame of what we're talking about I'm going to talk about physical systems
that have visual logs web systems that have been a locks now move on a smart phone systems that's what that's what I'm attacking today so who is this guy thanks to the direction pair my name is Devin Egan i'm the co-founder and CTO of launched a launch key is a local startup I'm here in Las Vegas involved downtown project happy to answer questions about that Vegas tech as well and one isn't equipment about that launch key is a platform for allowing users to log in with their spunk say I'm going to speak in the past on blook on boot camp happy to be here as well a little bit of background about my top where does it
come from why am I talking about it why do I know a lot of stuff oh really it comes from art bub-bub valley and our polk county systems for those are unfamiliar a lot of companies is if I security companies encourage researchers to give us give us data give us information so what I'm presenting today are attacked some of these attacks or attack that came to us to the book behind it we weren't aware up until we saw them ourselves and I'm here to basically share them with you as well that's that just a shout out to the researchers who did didn't kind of lead us to some of these issues satish be has a great book out there comment this if
this kind of a friends but announced her pen testing is interesting to you I'm breaking smart breaking smartphone stuff i really recommend and his book it's not my book I don't make anything from it just recommend it and see the smart guy he's uh he's done bad things to our software Andrew Smith who cares well he's the launch team engineer he helped you with he performed a lot of the auditing performed with his top and break it for Coulson numbers growing on me up with left so thank you thank you Andrew did great job so digital log forgetting to start off a retrospective I kind of want to talk i'm gonna start talking about where we were at what lock systems were
familiar with some systems that we permitted with and then get into attacking the smartphone locks and then defending them as well so we're familiar with some physical systems and digital physical systems digital safes car doors alarm systems et ms what are some of the attacks that were are used to for these physical systems we see macgyver attack as might be aging a little bit MacGyver tech guy ever MacGyver literally shaved off some graph I from a pencil blew it on to a digital safe inside which you know numbers read a lot and it reduced the amount of entries that he had to do ATM physical systems we've seen Jack potted Barbie Barbie jack all right he
did you know did some amazing stuff by passing digital law to ATMs just to have spit money out we see default pins and passwords all the time on these new systems as well so so they they can beat act that way finally I don't get paying attention last week breaks as a super secure safe is up in the top left here maybe bypass when you put a when you've literally put a USB stick and that emulates a mouse and keyboard so these systems are still being attacked today weather systems again this is a retrospective this lot of this should be familiar you guys password pin forms are digital like a considerable loss the way that we've seen them attack in the past
is through SQL I now you see a password or PIN field in our nice little you know SQL I statement this is that close in recent years but still it's this to some extent XSS is another threat but web forms and web attacks this will come up again a little bit especially the man in the middle and in the middle attacks where someone's you know actively sniffing you looking for password etc these are the texts that we've seen in the past which leads us to bone loss and digital loss what I'm gonna be talking about today I've time I'm hoppin and poppin smartphone walks really again I wanted to kind of get retrospective of where we are at what
kind of systems have seen and and these new exists any new systems what kind of attacks are seeing against them and kind of what's going on so over the set up this might disappoint a lot of people a lot of these attacks that I am performing that they'll be talking about are on a jailbroken iphone so just be clear this isn't a non jailbroken iphone that i'll be doing some use attacks against it is a jailbroken iphone I'll kind of get to why I still think it's important to secure data mostly because it can be done and it's again secure against these attacks so 30 plus apps are audited we did when we when we
caught something we did disclose it to the companies that we that we found issues in much like people recorded our bug bounty you also wanted to share a get the problems here maybe how to fix it that for people that don't bug bounties that can go two ways we get a peel angry at up some people who are clueless so but anyway I just adds up what you start submitting a full disclosure people who aren't asking for it with my guilt anger as well but that's it sixty-six percent of the apps that we that we checked this is password managers this is dedicated this is digital bolts in our secret secret apps nem that has a pin interface we try to
find and we try to attack just to kind of see we can not only for really the benefit to figure out how to fix the problem so the reason that we were doing this the reason that we were interested in so that we could begin protect our map so again this is this is jailbroken near jailbroke jailbreak attacks specifically the jailbroken effects so the tools that we use to jump to test these you're familiar with the cycra it's a by seen that is the cydia jailbreak website or a jailbreak story that's one of the tools that we taught them today key dump is a Zach what it sounds like if you remember the key chain on the iOS world it literally just
dumps out a keychain data down in raw text and what we will see we'll see what that looks like stupid is essentially a graphical user interface sci crypt so it it's only a caveat it only runs at iOS 7 i'm 32 architecture but it is a it really it's like a click like a side trip that you just click around and then i must be talking to pick like about man middle proxy and that's where we'll see a similar attack that we see on the web already so what's the first thing we do we're going after one of these digital interfaces we attack abused themselves and familiar with smartphones development you have a view and then you
populate that view with you know with the content that your client so how you so how do you attack these really what we do is you're using a tool like psycho an attacker can dump all of you names and then guess or attempt is just missed equations so the end result is that the pins it goes away and what does it look like a quick demo here I'm just missing abuse a we found a method that we want to try p unlock screen just for an example RF isn't a little destroyed em I'll show someone else is up this is the launch get a user is trying to come to tap this and what I mean by attacking
the view is usually what's happening when people write these is that there's there's the view is the only thing between the user and application you drop that view and many times you're right in the application the scariest place I've seen this our honesty password managers sometimes drop them and be right in really scary so again to dismiss this view I'll kind of show this real quick that's all up there and I can read that at side crips essentially I'm locating the view that I want to dismiss in this case is this this interface put i'm putting that that view information set the variable P now I'm simply running in this case p i'll play outro vp unlock screen and went and
this is that this is a psychic tool when as soon as I want to miss a drop that view all I have to do is simply call that view display outro and that's what it looks like again this is just an image i have videos that i can show you but i want again I didn't want to show you someone else's dropping that's what it looks like literally you run that it goes away and then everything is in the cleaner the whole app is right there for you to do whatever you want with it's a it's a pretty major one and it's something that the first time I saw I was like just shocked no idea as
possible again to back up this is these are jailbroken mom is our jail broke broke breaking our broken phones over attacking jailbroken views the reason i think is important theft is that you don't know if there's going to be a zero-day that that does jailbreak you know everyone stole in the world 950 million androids are last week we're vulnerable so again I do think these are important things to protect against especially since we can't some of it as laziness or not even just knowing like us we didn't know that this existed so after you've attacked abused you can also attack the method you use of many times where's column at that's calling code in the background it ain't so so
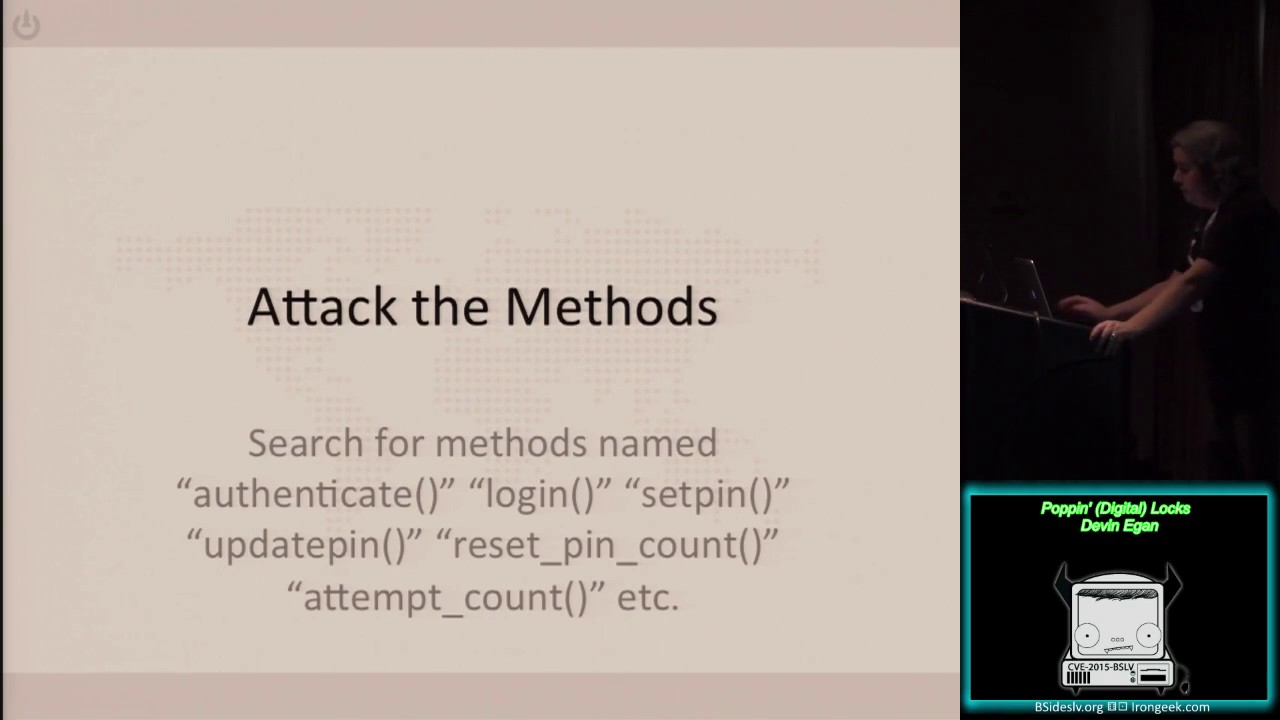
you can look for a fennec a login set in a pig in you can call the view it's call the method the view itself is calling i simply dismiss the view again or you can do some other nasty things with attacking the methods directly so we're tapping the code directly you can set the pin this is the number one thing kind of the easiest way to do it maybe if you if you're attacking your tapping and trying to get into an interface like this digital locks you can simply maybe set the pin itself so look through those messes methods if you see something like in we can attack that directly you set the pin till it 1111 go back to that
interface type 1 111 the V drops just like just like business another another way in tak methods that year I'm detecting is to reset the counter so what I mean by this is many many of these lost including euro usually less level have to have and you know a common mechanism is a lot about up X amount of details very common it's what's scary about this is that if its own is trying to root for sit if you take an atlas in this way they can simply reset the counter or set the counter to what are you know they might be a method for instance to set the counter whatever they want oh I only have ever done nine
I only got one left now I have zero and I can start all over so you can see this is a pretty that's another pretty scary one again this isn't as effective as just dropping the view set up in brute force and especially in this case of probably manual and be pretty brutal but it gives them a lot more chance to get it don't dump / set the pin in storage so this is another scary one and this is this is kind of the one that I really want I kind of really wanted to draw attention to because in the web world if you don't have your password it's like sacrilege and for some reason because of
this keychain thing everyone is so confident that that knows no one any pets eighty percent I think was the number of people who put data in tha don't even attempt to hash stuff that should be hash I'll get to that in a second but it's things like this common thing that we've been doing for years use a strong you know you just ran out of rhythm hash your stuff people don't do it we see this all time in one two three four so keen keep dumping on a jailbroken iOS let's do some really nasty things literally just dump your whole keychain data it's it's there's a lot in there it's really scary um I new
tool came out in the last couple weeks that we that it didn't have a lot of time to play with but it actually allows you to edit the keychain so much like setting the pin you can before if it's expecting plain text you can and it's that the pin right there directly the kitchen as well I'm talking about about iOS engaging with this this is where it also comes into android android a lot of time android doesn't have a key chain a lot of times it relies on user permissions storing data within a file for instance or the side of like SQLite file and a bacon on the permissions again of the Android to save
them give me some nasty league last week that new remote code execution that could also say ho hey i know this patrick manager doesn't match the data let's send it all ship all that back to me as well so again this is an attack this is nasty like where you're storing your data let's what some of these remember to hash hash stuff that's important and then finally the kind of the other way that every seen these attacks performed is by man and middle in these might sound familiar and that's because a lot of these digital locks are literally just web forms that are submitting to a web page min Gulen has a cell for this point but a lot of them
don't verify that input and thought about that so I'm on the fence how it kind of gets there are ways to verify this especially on the mobile platform that's really cool that you can hear app and say am I talking to my API you can be pretty confident that you are not or you can kill an average um and so part three defense in lessons again and this is where I've been talking to visually kind of how do we how do we prevent if your developer especially responsible for these locks how do you prevent this what do we what do we do what are the defenses and what are the lessons learned for the future so the first one
is to protect abusing that kind of a node uh and and you know just basically make it so it's impossible or a lot harder to just simply dismiss the view because it's very simple to do tokens and or non sins can be added to those methods of use when it could be a hard-coded crazy number that code calls it just one more piece of information that has to be passed along so it's not simply play outro it as we play altro with that makes sense you can hide the people together there's hidden flags in iOS and you can hide the view and all the view controllers inside the apps folder in this might make sense only to Pylos
developers and finally you can obfuscate the manifest files and obfuscate the functions themselves so don't make it really easy for someone to say you know oh login and may make it really obvious what those functions are the next you can do is don't roll your own inner don't roll your own pin lock there are third-party libraries out there on the week tested some that are good some that are terrible all be that all these attacks are applicable against had an OS level things like touch ID things like Samsung fingerprint SDKs know some people are aware the biometrics yeah not all phones have this hardware but really you can rely how many seemingly you can trust these a lot more those native OS
integrations then maybe yourself Todd so low level I haven't seen attacks against touch ID in stands up in your pic for instance if anyone has ever known another thing you can do you're really worried about this stuff is just jailbreak it his classic dealrate detection if you were you're saying okay I don't I'll just shut down the whole thing as soon as someone who starts us up and I won't worry about any of this stuff you can do you can you know get all uppers can put jailbreak detection um for users and I would stop jailbreaking your device an informal poll at our launch TM I think fifteen percent of fifty percent of us in the
office have jailbroken devices and I was kind of an eye opener this a lot of people still jailbreak your device and honestly not recommend it but anyways developers if you want to shut down the ability for someone to potentially pak-rat you don't feel great detection to it this is one of my favorite it's a honey pot meth interview so if an attacker is you know has access to your house x to the jailbroken app is attacking it you can add some really maybe fat methods reviews in there like authorize all the things or give me all the passwords something really attracted to a hacker and then when they invoke that function a function that would never recall by
your software something you know you can do a couple things a you can report back to you can say hey this IP is doing some really terrible things like a trophy pot you get alerted you help you defeat it into system system like my dad and sarah or you can do like launchkey does you could you can literally destroy that device of that device data so you can say oh something really bad we've been tech and attack unpair that data or delete all my data techno sanitary pads have that's another way I really like that one because it's a kind of a offensive attack is your only your only chance of someone's really poking around
you're out and doing really bad things to utilize the pin for encryption so this pin or passphrase whatever the knowledge factor is that you're getting from the user I'm use it to then encrypt all the data that that your apps Canadians does that make sense so it is the key to the rest of your data this is too full really cool because it turns your knowledge factor into a symmetric key it doesn't store the key even in a hash and you know in any in any way it's it's only used to unlock the data that you're absolutely so again that's that's a really cool um a really cool way to use the pin so rather than put it in
plain text into keychain use the key use that pin as the symmetric key so first ATF use that as they EES key data protection don't get lazy eye I kind of just started in this few minutes ago but if it seems so easy to lean on keychain or these permissions I know we're all developing some very very quickly but ash the appropriate data you know if you know even if this is a jailbroken device which rather see one two three four or jus rather see a hash in there I mean all day long um this you know this at least protects the password and for that knowledge factor is some way again with the keychain dump now or the keychain
editor it's kind of scary if they can guess your hashing algorithm they can potentially still just inject whatever passes they want and get in there anyway so that's maybe why something like could using utilizing the pin for encryption works really really well it's a data protection again don't get lazy hash the appropriate data for smartphones this usually means my recommendations gbk GF 2 it's one of the key derivation functions that probably if you've ever asked password you're familiar with all smartphones its iOS Android and 10 v WP use Windows Phone Windows pub they all support this this pension by the way the iOS is really fast a computer ktf to assume because of the hardware interlink Android is really
slow I'm just a heads of a beast articles and then finally as a self-tanning in man the middle defense so again for those web views that was talking about a very common way to attack those web views is that is if you're on a public Wi-Fi networks ate a conference and and you're sending data via via a mobile app to two of them API and one for instance to it to authenticate you there's a there's a method of there's a method called SL penny that princes afnetworking in iOS supports android supports this that that uses you the public key of your ssl cert to guarantee that you're talking to that to that server so a lot of times i don't
see this implemented where you see what you see is people sending no it is just again just trusting the ssl sending the data straight over if your man in the milling that data you know via mantle proxy or someone else nefarious you could you know decrypt basically you know setting up a middle middle ssl CA and getting all their stuff you'll be able to see everything if you do that with this self enabled it stops that connection so again the user won't won't have their password or the pin stole one another thing i've seen if you're not using a self in or you can't for some reason you can pre hash or encrypt the data before you even send it so again I
know SSL is this end all be all rooms like new ssl you're fine again in the mobile world or in public networks your traffic even at your work your traffic all your traffic might be decrypted so again it's app developer other people to protecting these digital is digital loss I'm pretty you know pre hash on the phone itself and then symbol not only does it save you computing power if you're your big big shop worried about milliseconds you can save yourself some computing power is you don't generate you not to compete that hash on your side and again it basically protects it in transit outside of SSL um it's kind of a defense-in-depth again Mike don't donors rely on an SSL it's
not don't rely on keychain if you can hash the data why not adds that extra layer of protection makes a lot harder to attack so that's it kind of the lessons of the past we see kind of applied to defeat to now with you know a few things like the web forms still kind of exists inside of these smartphones apps and and I think these new these new kind of digital locks with us to stay let's make sure we're implementing them well as make sure we're securing them well and that's all I got today [Applause]
thanks for time and any questions I'll be here I'll be here afterwards have any questions about vegas or anything else I'm available right yes yeah 3 minutes
so so he asked how reliable is jailbreak detection I think that's available of power over life but you know everything else everything I've seen is it's good but never guaranteed so like everything there's multiple ways to do it multiple ways to detect that and obviously the more the more different systems in the more different ways to look at and i definitely look at it you can do it the long story short is not under percent for sure yeah the questions yeah oh yeah oh yeah oh yeah touch ID I was you yeah exactly and and I honestly haven't attacked directly but of it and I was made them we wouldn't been able to but I'd like to talk more about as well he's
been done yeah is jailbreaking tag those people who you like or dragged out because I just want yes yeah you choose he has someone not somehow I was outside of of our own then then yes ki last local off and then it got work i believe obfuscate but yeah I certainly I certainly believe it's possible its mother recommendation for saying using it as at least at least those all these other things they won't be too worried about again the jailbreak world really is kind of scary what really would I think again what I was talking about and what I'm trying to get across that we don't know if there will be a jailbreak exploit for
the phone at some really bad could happen so if your app developers irresponsible perhaps please add this is protections really get it really a lot you don't know whenever your users will be jailbroken because again you know a lot of people generate the cluster yeah okay so yeah it was pretty though so touched your get it done very much [Applause]





