BSides Iowa 2018: "Threat Intelligence Collection Strategy"
Show transcript [en]
afternoon everybody everybody successfully gets themselves into a food coma hey if so come to the right place all I take a nap while I talk my name is Chadwick Smith I'm a senior cybersecurity analyst at Sutter Health in Sacramento California Sutter Health has been undergoing a massive transformation in our cybersecurity group we are in the process of building out an entire fusion center where we're taking our cybersecurity group the physical security our security operations a lot of our IT privacy risk management and everything is being funneled in together and we're spidering all of the information out to all the different groups and one of our initiatives in that is threat intelligence this is a relatively new area for us we've only
been doing it for about six to eight months so I figured that I'd share some of the stuff that we have went through to develop our collection strategies and define where we were going with that how many people in the room are actually doing actively doing threat Intel currently
to give you a starter one of the first things that we did with our threat intelligence program has developed our priority intelligence requirements these are the basic defining blocks of what we're going to gather for data to define the intelligence that we're going to feed into the different areas of the corporation the two major pieces that we do are technical tactical which include our i/o CS tactics techniques and procedures threat actor tracking the other part of it is strategic a lot of the strategic goes into assigning risk to vulnerabilities that are announced evolving threats some of that threat actor tracting and how they are impacting our particular sector which happens to be healthcare but we spread
out quite a bit in healthcare because it is the most regulated industry we have HIPAA all of the finance stuff sarbanes-oxley varium levy all of these different regulatory requirements there's like four hundred and thirty regulatory requirements that we have to abide to in healthcare so in defining those priority intelligence requirements it can be really broad-based and if you get to broad-based you're looking at a lot of information and depending on how big your cyber front intelligence team is it's gonna be overwhelming for them so one of the main focuses for our collection strategy was to try to get our priority intelligence requirements narrowed down to a scope that we could handle currently we have two threat
intelligence analysts on our team and when you look at companies for example like Palo Alto who are seeing a million new samples a month that's a lot of data to ingest so defining those down getting our strategy in and running that through the intelligence lifecycle that was these are our main priorities right now to get that narrowed down how we collect that data we had to define that what are we using to do that what sources are we using and after that we have to define our periodic reviews of these to make sure that they're fitting business need so P IRS actually asked the questions that define what we're actually going to gather for intelligence to help the
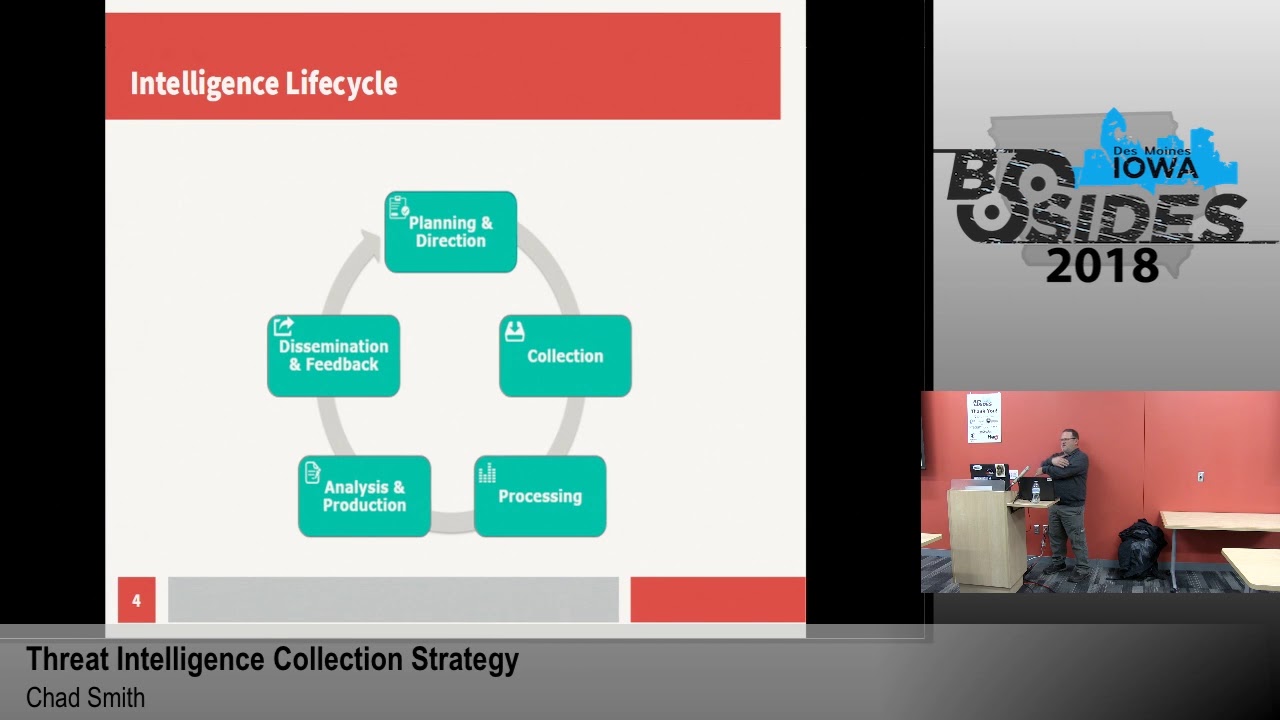
corporation or the entity mitigate the risk and to minimize the impact from threats so as we go through and define those priority intelligence requirements underneath that we ask a whole lot of questions under those and those are our collection requirements what we're doing to answer those questions the those strategic level priority intelligence requirements we use them to identify those questions than to define the data and that goes to support our actual production of actionable intelligence the with the intelligence lifecycle defining that in this will help kind of guide where we're going with that collection strategy we start off with our planning and direction if you're starting out in this spend the appropriate amount of time in this area
yet you're planning in your direction done define what you're going to do how you're going to do it where you're going to do it because that's your building block if you don't spend enough time here everything else and the lifecycle is going to fall apart after that you have your actual collection this is the data that you collect where you collect it from from there once you get the data collected you have to have people that are going to analyze it and they're going to look through it and determine what actually is useful for the entity after the analysis and production we get into the reporting what types of reporting you're going to do where you
going to do it who you going to disseminate that to the dissemination of where that information goes to is a big definition because you need to get it into the hands of the people that actually make the decisions and if you're getting it to the wrong people it's worthless and the last part of that feedback always talk to the people that you're providing intelligence to and ask them if it's doing them any good and what they need a lot of times they're gonna look at you and say I don't know what I need I want you to tell me what I need you got to work with them you got to ask them the questions and keep working
through it with them to find out where their priorities lie when you're looking at from a strategic level your CSO is trying to make decisions on where your program is going to go what kind of policies and procedures need to be in place as opposed to your sake analyst who's looking for IO cease technic techniques and procedures so that they can actually identify the threats and map them to who they are who it is that you're is attacking you if you send the information in the wrong direction it doesn't do any good so you got to make sure and keep asking them questions so that you can further define what they're looking for planning in direction as we
talked about it ensures the proper people you get your processes your technologies in place that gets you your proper operation of your threat intelligence program and you build from there make sure you define what your objectives and who those QT consumers are the PIR our PIR s that you have derived make sure that you again I'm going to reiterate make sure that you get those to your decision makers and they meet their needs and from there continuous improvement you're trying to get the guidance and then define new requirements and refine those requirements as time goes on so that you're producing actionable Intel all of the time within the collection portion we're gonna identify the sources at that
point the sources are somewhat going to be defined on what our intelligence requirements are and the questions that we're asking to meet those needs we want to provide a full coverage of potential collection sources for ourselves some of those are open source threat intelligence feeds whether that be IOC s or the tactics techniques and procedures blogs news articles vulnerability announcements all of this stuff is freely available you can find it you just have to collate all that information and find out what's usable for you internal sources can't stress this enough when you're when you're working with your security folk when you're working with your networking for your server folk all of the logs that you can
collect the morale logs you can collect the more internal data you have the more actionable intelligence you have because these are things that are affecting your network every day more internal sources is awesome get more internal sources vendor data these are your external vendors there are a lot of threat Intel vendors out there many of them have different specialties you have to go through the process of valuating them and finding out what types of threat until they provide and whether that's going to fit with what you're looking for for your intelligence requirements there are a lot of them that specialize specifically in deep and dark web some of them are looking at a crime some of
them track threat actors very well some of them are really good at providing on-time actionable I OCS you have to decide where those sources are and which ones are providing you the best Intel and the only way you can do that is to evaluate next one is Intelligence Sharing partnerships there are a number of Isaac's for any different number of verticals if you get the opportunity to do that join them these are people who are doing the same thing you are every day in your space if you can get into your Isaac's get in there there are people that you can contact when you're having troubles getting through process all of the stuff that I've learned has
come from other people getting out getting into that information sharing group asking those guys questions I'm like hey I don't know how to do this what are you guys doing when you get into the Isaac's they're more than willing to share that information when we get into the processing processing you converting all of that raw intelligence into digestible formats and that processing again you got to decide which direction that's going is it going to your technical people or is it going strategic up to your senior level management filter that data compile it centrally store it somewhere if if you're just starting out in this a threat intelligence platform may not be an option for you at that point find a
database get some type of repository whether that be some type of document repository like a wiki anything that you can do to actually have somewhere to centrally store that data because you're gonna reference that data a lot over time as you're evaluating different threats that are coming in and that's where the spoink comes in analyst can then compare the data from previous campaigns and incidents within your environment to gain additional conduct context on what they're facing today the analysis production cycle synthesizes all of that data the whole goal of that is to evaluate the reliability the validity the relevance the timeliness of the data that you're getting to make sure that you're answering those primary
intelligence requirements for your organization timeliness of data is a very important thing particularly when it comes to IOC s today's threat actors are constantly changing what they're doing on a minute-by-minute basis when you're having a particular phishing campaign if they're actively monitoring it they will actually change what their payload is within that they start out using our URLs they might actually start throwing attachments on there as different things get blocked they'll use revolving URLs they'll change the URLs in the phishing campaign if they notice that they're getting blocked so that timeliness of that data is very important and when you actually store that data make sure you put it into logical sequence for global organizations make
sure you define a standardized time that you're going to use within your organization particularly within your security group because if you're going over multiple time zones what somebody posts as 1700 on Monday up he's in the UK that was 1700 UTC 1700 and Pacific that's 7 hours later that doesn't be any good so as you're going through this make sure you standardize on a time set for what you're going to do for your logs and everything else dissemination some of the dissemination vulnerability reporting make sure you get your reports out on those vulnerabilities evolving threats we routinely on a weekly basis are sending out somewhere around 5 to 10 reports outlining critical vulnerabilities that are affecting different devices within
our environment with us we have a lot of business devices we also have a lot of medical devices so we're watching all of these different feeds come in we match them up with the vendors that we have identified that we have in our environment and then we send that information out to the different IT teams and our biomed teams to make sure that it's valid if it's not valid we don't have to produce the report on it but if that's a vendor we support we're producing a report on it to let them know that it's there in case they missed it now we're reporting we work with our Incident Response Teams heavily on this as we see incidents that come million
they're writing up their reports on the incident we're taking that data we're collating that into monthly and quarterly trending so the Incident Response reporting that's another place that's another source of data for us in our collection strategy we utilize those reports heavily because that gives us trending that we can send up to our strategic teams senior leadership it also gives us a lot of I OCS on active threats in our environment that is the most valuable intelligence you can have threat actor reporting this is mostly strategic however our technical teams also use this because if they see certain tactics techniques procedures in attacks that are going on in our environment they can actually map those back with where we've collated our
data and identify different threat actors that are utilizing those particular TTP's and potentially map to who it is and utilize that information to see what other types of exploits or malware they're using and potentially identify additional threats beyond the one that they're looking at in their incident response campaign reporting mostly strategic again we go over the different campaigns everything that affects our environment we report on it we do trending we do tracking on that and we send it up again this is heavily reliant on our sock on our incident response teams we also rely on our Isaac's other organizations that are seeing those same threats they're reporting them in we count that as an incident we start tracking all of those
that becomes trending for our actual vertical strategically our senior leadership wants to know that most senior leadership does they want to know what their threat profile is and as I have been talking about extensively incident reporting in the collection planning identifying those CRS those collection requirements those are the questions that are going to guide that collection process determine what those sources are create the source portfolio we actually have a cumulative list of all of the sources that we're utilizing we mapped those to the different P IRS and where they actually answer those questions to give us that priority intelligence make sure you map your sources because you want to have at least two sources for every one of your
collection requirements to be able to provide at least partial answers for it that way you have a redundancy you don't have a single point of failure in your intelligence program conducting the vendor evaluations in that planning process again thread Intel feeds thread Intel platform if you go into those different areas whether you are utilizing all open source there are a number of threat platforms that actually offer a community Edition where you can actually put your threat data in look them up online there's a number of them that do it collection operations the initiation of those source data collections where are you bringing them into how are you collecting that data once you have that defined start bringing in the data store
your results get them put into the knowledge bases keep up to date with your evolving threats proactively address social engineering techniques these are one of the primary points of impact within most organizations today phishing fake tech support scams these are all big things we see about 90% of our incidents revolve around social engineering stuff pay attention to all the security layers servers switches workstations everywhere that you can be on your border your DM Z's collect data from everywhere you can
continuous maintenance within the operations we go through on a regularly set schedule of every three months to reevaluate our collection requirements and make sure that they are properly answering and identifying that intelligence we have to provide to people when they're telling us this is what we need we want this information we have to review that we continually go through this it's a regular cadence for us every three months we reevaluate our collection requirements and our priority intelligence requirements if something's not providing us the right data we make a change to it it's just the process to go through always always improve your processes make sure that everything is supporting the business when you go through that
quality review make sure you ask all of the questions to identify whether or not that data is actually producing actionable results is it providing specific guidance and answering the questions in the P IRS do they collect enough information if you're short on information got to add more sources or potentially your collection requirement isn't being met properly internal external data is it being collected and tailored in the proper way are you identifying the right sources again are you getting the redundancy in your sources if one of your sources is not providing good Intel is your redundant source to answer that question actually providing it collection make sure the finalized intelligence products are providing coverage across all of your
priority intelligence requirements when we first identified our priority intelligence requirements for an example we had eight when we went through and we're actually identifying each piece of thread until that came through and categorizing it on our PI RS we noticed that our last PIR never got hit because by the time we had made it through the first seven everything had been categorized so that PIR was sitting out there doing nothing and it was causing us a lot of headaches because it looked at data across all verticals so it basically opened the door for everything coming in we had to eliminate it it was it was causing too much overhead on what we were trying to analyze and all of our
other requirements met it so it wasn't necessary make sure that the obtained intelligence is in a useful format for the people that you're providing it to you can't stress enough strategic tactical if you provide tactical information to your seaso or a CEO or a board of directors you're gonna lose them it's worthless of them because they don't want to know how that malware was reversed engineered they want to know if they have a risk in their environment and whether it's going to affect them certain organizations have certain guidelines on how they produce or how they produce those reporting make sure you're following the guidelines for the organization some of the organization's like to see things in a certain format
that's how they're used to reading it try to adopt into those formats and how you do your reporting because if you get stuff that's familiar to them they're much more likely to read it and digest it properly
any questions
so at this point we're doing a lot of human filtering however we're starting to actually develop some automated processes that go in there I'll give you an example for our fishing mailbox we have mail box anybody that thinks some gets an email that they think is phishing they can send it in there that mail box gets three to four hundred messages a day when we're doing a spam campaign twelve thousand a week we have one analyst going through that mailbox you know when that comes in we got to pick that up we're looking at ways to automate that we're looking at ways to bring those emails out strip out the headers strip out all the IOC strip out
the attachments run them against reputation filter that out get rid of all of that manual work because that opens up time for actually analyzing the data yeah we're working on a lot of automation yeah and the other thing is is getting to know your environment know who your vendors are know how your network is set up know your public IP addressing space know your internal IP addressing spaces all of this information is valuable information for you to be able to take that data and know whether something is going to affect your environment or not and it helps you identify those collection sources
I do myself yes that is not something that we have set up within the organization simply because we don't have the manpower to handle that we're looking at some third-party solutions to actually help out with that some of our threat and tell vendors actually provide some of that data for us so right we actually are constantly looking for new third-party feeds to help augment that analysis for us because most threat intelligence groups don't have the manpower to do it all you gotta rely on some other people to help you out and that's where Isaac's come in also be honest with you were just in the process of evaluating all of them so right now I
wouldn't be comfortable to tell you what my my favorites are at this point hit me up afterwards I'll give you some information or you contact me after that and we can talk about five yes point should have business start looking at this as any like size-wise so if a business is like just very very small only one person's just doing all the computer stuff or would it be like a couple of people that are among the IT staff instead of doing this that's a good question and I can't give me a good answer for that before I went to Sutter Health I worked at the University of Iowa healthcare a number of the people in our group we had a team before
everybody on that team was constantly watching over the source stuff so we were doing it we were doing it at home we didn't have an actual manage process that we were doing it everybody in this room on any given day is actively going after threat intelligence you're looking at news you're looking at blogs you're reading different sites getting information on different fishing campaigns that are out different vulnerabilities that are out that's threat intelligence you're all doing it every day most people just don't realize they're doing - but I also work in that organization so do you have any like we we actually are in the process of setting up some of our own dark web monitoring that's a
long process it takes a long time to set up an actual that it dark web presence most of the websites out there you have to know somebody to actually get on it somebody's got a vouch for you to be able to get on and actually participate in that forum or that marketplace so developing those personas keeping them secret it takes a long time to develop at this point we're mostly relying on third-party vendors we're setting it up ourselves but it's a long process there are a number of people within the different Isaacs who actually are actively doing this it's a really good source did you reach out to some of those people because they're more than
happy to help you out with that process as you go along but some of the open-source things that we utilize for example pastebin i think everybody knows what pays fitness they offer an annual sale you can get a lifetime membership to pay spin for twenty bucks that allows you 15 keyword searches those 15 keyword searches infinitely valuable put in your organization's domain name put in different email aliases that you use any time those come things like that come up on pay spin it's gonna send you alert you can go look at it I have a large number of accounts at this point because 15 is not enough summer has about 300 different domain names that we
monitor so that gives you an idea yes sir
yes so a lot of your threat intelligence platforms for example are going to give you a confidence level and a lot of your threat intelligence feeds also will have a confidence level on that mileage is gonna vary they're gonna they're gonna score them differently you're gonna score them differently than what they're scoring them there are some of the stuff that we actually automatically ingest from our phishing mailboxes that when they go through the confidence scoring in our threat intelligence platform it comes back at a twenty on a scale of one hundred all right we need to do a just that because we know it's active it's attacking our environment so that becomes a 90 or 100 for us yes yes we
actually do risk scoring we have developed our own risk calculation calculator that is worked in conjunction with our Incident Response Team so every threat every piece of information that we analyze we risk score that and we risk score that based on a number of criteria as far as what type of threat it is whether it's a direct or indirect internal/external what type of where it's at for example and kill chain process where it's at in just different models so we use a couple different threat models diamond kill chain a couple others that were actually working on developing for our own internal environment and we map to those and we risk score based on that what the
projected impact is in threat intelligence Incident Response we have a number threat intelligence we got to use some estimations to figure out what we think the potential impact would be and then we risk score it at a particular risk score we it gets escalated immediately other ones we just report on
any other questions comments feedback all right thank you yeah
this has become a very big conversation topic in the last two to four weeks within our environment because our Incident Response Teams actually utilize who is passive DNS information for initial lookups on a lot of the things that they see we utilize it and thread Intel also with those changes those that aren't familiar the Europe has passed their gdpr which is basically their individual privacy rights which are kind of muddying up the water because a lot of people in the u.s. didn't feel that they were gonna be subjected to those but come to find out it's kind of overreaching in that if you do business with a European entity or someone from Europe visits one of your websites for
example you are subjected to G GD P R and one of the things with GD P R is protection of the information on people who have registered domains so that Whois information that we utilize on every one of our domain and IP lookups to figure out where things are coming from and where they're going to that information is going to start being hidden from us we're still evaluating that I I don't know what the answer is but yes it's going to impact us
absolutely absolutely yeah we have entire vendors that are completely dedicated just a passive DNS information for us
any other questions related to this or any threat Intel questions at all all right thank you all [Applause]





