PW - Password911: Authentication Adventures in Healthcare
Show transcript [en]
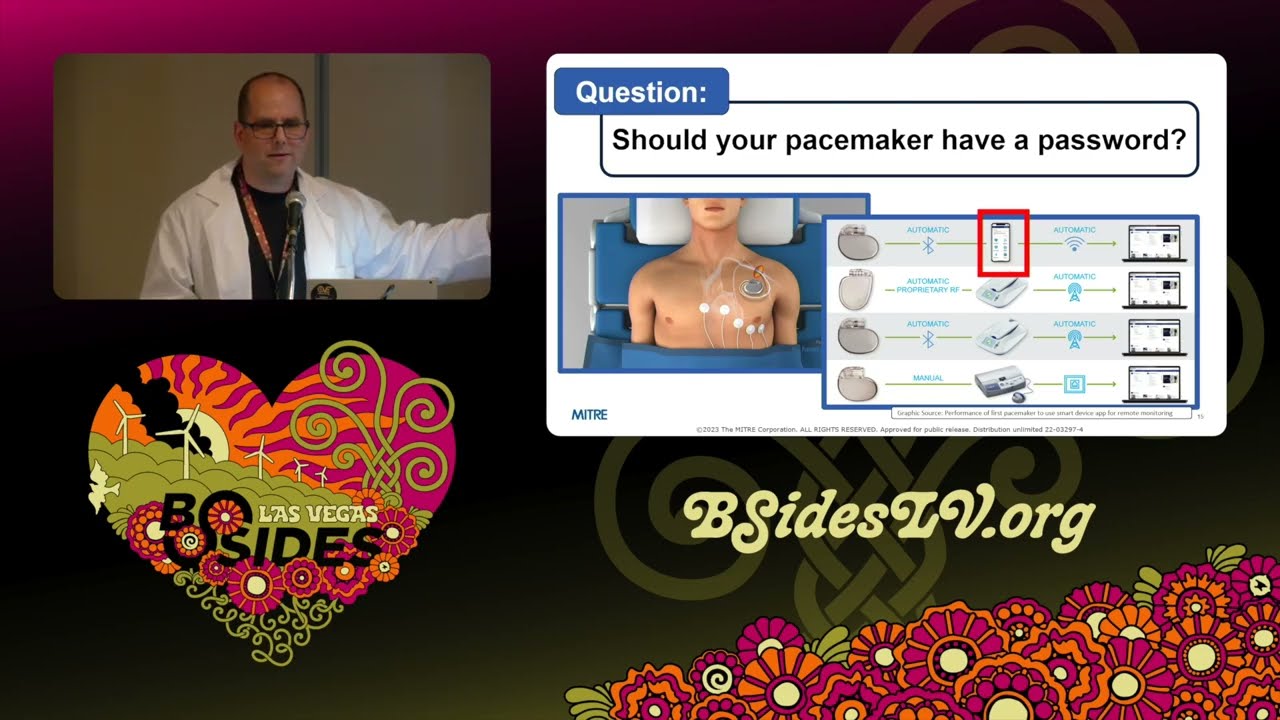
so the last speaker had a really good dad joke okay you guys ready for this you might have heard it I'm stuck on this now okay how did the hacker get away from the FBI he ran somewhere isn't that good isn't that good all right we ready Alex the colle all right good afternoon good afternoon we've made it through almost the first St besides Las Vegas how y'all feeling fantastic fantastic we have the amazing Dr Matt wear with us today this afternoon password 911 authentication adventures and healthc care so somebody earlier said he saw him talk 16 years ago so let's give it up for this man he's been talking a long time okay all right well let me get some stuff out of the way real quick first of all your cell phones turn them off again unless it's God or somebody's dying we don't want to hear it or at least turn the ringer off okay um I want to take a shout out for our sponsors the diamond Adobe our gold prism Cloud blue cat Plex truck Toyota all that good stuff so without further Ado Dr wear take it away cool well thank you very much it's good to be back at passord con um the last time I spoke in person was in 2019 in uh Pastor Con in Sweden and a few things happened in the health care world since then there uh so it's really good to be back here and talking about passwords and Healthcare which are two of my great big passions here so in my day job I'm a cyber security researcher focusing on trying to figure out the Cyber resiliency for medical systems so I both look at kind of the impact analysis side so like a vulnerability comes out you know what is it going to be the the clinical or the patient impact of this vulnerability I also looked at this from the defensive side as well of like how do we go ahead and Design Systems so when that next vulnerability comes out they still are you know resilient patients can still have care um and we can still go ahead and do a good job so as part of this too um I'm also a member of The biohacking Village uh so if any of you will show up at Defcon over the next couple of days uh we're going to have some medical devices for you to be able to hack and learn on maybe apply some of these lessons that I talk about here too um a side tangent um I was really pleasantly surprised by how easy it was to get medical equipment through TSA security like I I was coming through here I was like okay this is going to be the cover story this looks dodgy as hell you know you know how are we going to get this through here and um you know no problem they were like okay it's not bottle of water we don't care uh so just right on through um so um as I was mentioned a little bit ear I I have been doing this a long time I'm a longtime member of the John Ripper uh passer cracking team because while um I'm passionate about medical advice security uh I am absolutely obsessed about pass through crack so you know whenever I get to you know combine these two things together here uh it's just a great day for me so um kind of talking about how long I've done this here uh I was one of the first researchers to study the rocky password list so I was able to go ahead and grab it online uh I did published you know some analysis of this here other researchers were interested so I shared the list with them so if you're sick of the rocky password list I'm really sorry okay um but uh if you want to ever have some good stories about that talk to me afterwards about this so one thing though I I have a disclaimer here is I am not a medical doctor don't let this lab cope here you know fool you um I got my doctorate in uh in computer science and was really try trying to model how people create and use passwords and out of this came this pcfg password guess generator and I've been talking about that for a long time so this is the password's con so if you'll just you know uh give me a little bit of latitude I want to talk about this a little bit more oh and also before I kind of continue uh if you're asking like why I don't actually get any work done you know it's because of these uh you know two little Helens here uh so they're always walking across my keyboard and generating really good random passwords for me so when I talk about the you know pcfg password cracking you know the kind of the base question is you know what actually is that and so the the official term is it stands for probalistic context free grammar and this probably doesn't mean anything to anybody here unless you're really into computer science or a grammar nerd or something else along those lines and so I went ahead and I renamed it uh the pretty cool fuzzy guesser and this kind of better describes what this actually does here uh so basically you train this on a sets of disclosed passwords it uses machine learning to go ahead and figure out probabilities associated with all the different types of mangling rules that people use so you know sometimes you'll put you know uh it capitalize the first letter they'll cap or but they'll also capitalize the last letter at a certain probability you know people usually add numbers to the end of their password but sometimes they add numbers to the beginning or they replace letters with numbers and so what this uh uh pretty cool fuzzy guesser does here is it goes ahead and takes all the information and then generates passwords in probability order so it'll get generate the first most prob password guest the second most probable password guest and so on and as you can imagine this is really useful if you're trying to go ahead and crack passwords so I'm not going to talk too much about this because I really want to focus on medical device cyber security uh but there has been some work in this uh here that I just want to briefly mention so the the first thing I've had really recently here is a default Russian rulle set because I believe in kind of sharing this all around not just focusing on all of us English speakers uh so it's got a lot new support now for you know cracking cerlic passwords and you can find out more about that if you go ahead and read the developer guide I also added in Honey word and synthetic password generation so what this does here is instead of generating the most probable password guess and then the second most probable one it actually generates it according to the distribution that you would normally see in a normal population so it generates essentially fake password dumps so these are passwords dumps that look very realistic to what you find in the real world and the question is like why would you want to do that there and really the kind of main use case for this here is being able to help provision quickly large deception environment ments uh because no one wants to go ahead and you know generate a thousand you know active directory user passwords by hand and so this is a really good way to be able to make that you know be able to fool an adversary uh based upon this though uh I also added in what's called a weighted random walk guest generation so this generates password guesses the same way so it will go ahead and just kind of randomly walk through the grammar and generate password so by default it'll generate you know the most problem password guesses first but it kind of go walks around and it causes a lot of you know duplicates as well so the question is you know why would I go ahead and do that and the simple fact is that the pcfg password guest generator is slow it's really really slow so like it cracks passwords but you know you generally want to go ahead and use other attack modes if you're not targeting something that's really computationally expensive with this weighted random walk though um it's fast you know you don't have to keep track of state so the memory requirements don't change over time uh it's highly paralyzable because each guess is independent of each other and what this really means is that it you know it really kind of hopefully scales to a GPU password cracking type of a a message there so just to give you a preview what I'll be talking about next year hopefully is I really want to go ahead and get this included into hashcat there so that's going to be kind of my go goal there but that's all really kind of to the side you know because you know what I really want to talk to you about though is passwords in hospitals uh because this is something that's really important there you know with password cracking you know we're we're getting better you know that's I won't say it's a solve problem the next talk we're going to hear is going to be really trying to get into that last hard part of it there um but you know there's a lot more problems here with you know trying to secure hospitals you know how do we go ahead and uh be able to provide care in a kind of a hostile thread environment and it definitely is a hostile thread environment too hospitals are absolutely under attack so the the primary people that are targeting them right now is your standard kind of ransomware type of uh you know criminal organization there uh because they like the money and hospitals have money I mean that's really kind of what it comes down to there so you know kind of if you look at what they're doing right now it's kind of the standard that you see across any other industry there they they they break in they they encrypt the files they demand a ransom payment in order to decrypt them um in order to do that um but um hospitals have luckily and this is a really good development here have gone better at being able to respond to this because being able to provide uninterrupted CL you know clinical care is kind of cord to their mission so unfortunately the attackers they don't go well okay no this is getting harder we're just going to walk away and Target other Industries uh they've definitely been going ahead and changing their tactics as well uh so recently we've been seeing them go ahead and start trying to Target like Hospital support structures like Voiceover IP systems and you know it's really hard to run a hospital if you don't have a phone um you different departments need to call each other patients need to be able to call it so when a phone system goes down in hospital it's a really bad day uh the other new tactic that's really been kind of popping up lately and this is a really um just horrible one is extortion of patient medical data so they'll go ahead and they'll break it into the the hospital they'll steal very sensitive patient data and then the hospital won't pay them because they're going ahead and they have recovery procedures in place to be able to respond to that there so the hackers then reach out to the patients and say hey look we're going to go ahead and publish this very very sensitive data about you online and then tell everyone you know about about that sensitive data unless this Hospital over here that has all the millions of dollars goes ahead and pays the ransom and so they're getting the patients now to try to you know pressure the hospitals in order to pay the ransom so that data doesn't get leaked and so you can see this is a this is a really important problem for us to be able to solve because we're all future medical patients hopefully you know that we you know if we live long enough we are going to go ahead and end up in these types of systems here and so and so same goes for everyone that we love and care about uh so being able to provide safe and effective Healthcare is a really important topic that I'm very passionate about now one thing and one of the reasons why I want to give this talk though is because our Solutions have to fit into a clinical setting um there's no if ANS or buts about that there and so it this is really causes a lot of problems because a clinical setting is very different from your typical enterprise system there you don't want you know someone to go ahead and reboot the you know the uh infusion pumps or something like that there when you're in the middle of get receiving treatment there you know you don't want your anesthesiologist to forget their password as they're trying to log into their computer or something like that um you don't want you know password change policies are suddenly break systems that are providing care so trying to figure out you know how we can go ahead and secure the system and apply you know strong password you know policies and authentication uh mitigations into this here is really important so I could keep on ranting about this but I'd really talk rather talk about you know case studies here so the first one I really want to talk about is control substance infusion pumps so these are very common devices you'll find across hospitals and they're used to dispense pain medication uh so you know any of the really good drugs uh there that you can think of there they they generally fall into this here and you don't want patients just go ahead and open them up and start reaching in and start squeezing that you know bag of morphine really hard there uh so pretty much the defining feature of a controlled substance INF Fusion pump is a lock and key so like here's one model here there's where the key goes here's where you know well I guess that's a lock but you know you know there they go for that so if you go ahead and see a device with like you know dispensing drugs that you know has a key that's probably a controlled substance infusion pump so this is probably the most you know Common basic security password type of a you know Paradigm ever you know you got something that's really valuable you don't want people to go ahead and just grab it so you put a door on there you put a key on that door or lock on that door and you call it a day so this is pretty kind of a standard uh you know password type of a problem so what if I told you though that this is also kind of a standard issue that comes up a lot is about key reuse and specifically it's a common practice across all these different manufacturers here that they will use the exact same key on all of their devices so uh for example like if you go down to the hospital down here uh on the Strip uh you know you know what type of infusion pump they have uh you can go ahead and get the key really easy and go ahead and log right in open it right on up and as as I said this is very similar to for all these pumps so this is a pretty much a universal say I'm not trying to give you know individual manufacturers a hard time uh the only kind of disclaimer that I have is that you have a lot of these kind of thirdparty you know plastic cases they put on there and there's not really standardization of the keys for those simply because there's not standardization between the manufacturers so this is the audience participation part here to talk but is this a problem okay we have some you know you know important stuff we don't want patients going ahead and squeezing it we don't want people stealing it we put a lock on there we use the same key for every single lock all around the world um is this okay no well I would actually argue it is okay um because you know you have to be physically close to this in order to be able to do this this is not a remote attack and if you start going ahead and opening up these infusion pumps and squeezing that bag really wicked hard you you know the nurses might want to stop you as well and you know so you know this is not a huge problem and at this on the other side there um Physicians and nurses and everybody else need to be able to get into these pumps very quickly and so these Keys have to be very reliable uh because you don't want that to jam when you're going ahead and trying to go ahead and change you know a patient's medication uh you also can't really change your treatment plans while that key is locked as well so you have to be able to unlock it because you don't want patients pressing that button as well so making sure that lock is really reliable uh that can be open to all types of situations it has a you know strong failure mode and stuff like that there they have to worry about is really important for providing patient care so there's not really been any uh you know uh examples as far as I know either of you know patients actually compromising this so you know the chances of someone you know having that key around their wrist when they get in a motorcycle accident is pretty low so this is kind of an acceptable trade-off that you know most people take when it comes to passord security or you know authentication issues when it comes to infusion pumps so let's take this up a notch though should your pacemaker have a pass password I know yeah everyone's kind of sucking in like yeah that that seems like something that' be really important there you know we don't want people just going ahead and logging into pacemakers and pacemakers are absolutely very connected um like right here you see like a a cell phone okay you don't want just everyone you know walking by you know logging into your pacemaker there and this this is very important to enable people always ask like why are we enabling this well this is providing information to your your doctor uh about you know how that pacemaker is functioning uh often pacemakers need to be tuned around and stuff like that there because it's you know it's a it's a very delicate type of a thing so being able to provide that level of reporting saves lives so we can't go ahead and just say we're going to go ahead and disconnect all these devices make them dumb devices we have to be able to enable this but like even looking at this like how does that pairing work like there's not a button on there I can push like you know when I go to like pair my cell phone that do I do need to do like 15 minutes of cardio or something like that there in order to like get my heart rate up and uh you know accept that request and I mean the short answer and there's a couple different ways that to do this here is that you'll have an app you'll go ahead and you'll enter in your serial number into that app it goes out to the the manufacturer and the manufacturer gives you kind of a rotating pin that you can then use in order to go ahead and pair your cell phone with your pacemaker so I know we have a lot of Security Experts watching this right now and you're like okay sms okay that's a problem sometimes there's there's challenges with this you know how random is this serial number that there actually being generated for someone to be able guess there's a lot of different rabbit holes that we can go down into the security of this here uh but before we do I just want to point out another different use case that will kind of uh negate a lot of that and that is the pacemaker physician programmers so the cell phones generally just report data about that that operation there uh but you know Physicians need to be able to to modify that treatment plan of those pacemakers as well so these programmers not only can they read data but they can go ahead and set the settings of your pacemaker as well and so that's really serious and the other challenge is that often these devices need to operate in kind of an offline environment you don't want to say like I'm sorry we can't deliver life you know giving care because our internet is off uh so you know these Pace these pos position programmers need to be able to access pretty much you know anybody's uh Pacemaker and this can happen whether you're here in Vegas whether you're at home whether you're in Australia or or anywhere else you might want need to be able to receive a medic care and so these uh programs are kind of interesting each manufacturer has a different one so you'll often see them like just kind of stacked one upon each other in the hospital there uh each of these will also be running you a bunch of different apps on there for each different model that they want to be able to be able to support if you look at that guey you're like wow that's really old yeah you're right it's about you kno





