Cybercrime Central: Vextrio Operates Massive Criminal Affiliate Program - Gary Cox
Show transcript [en]
morning everyone um welcome to the red track uh next up we've got Gary Cox thank you thank you to um good morning everyone nice to be at beast in a very sun which is which is awesome so as Tom said so I'm I'm Gary U 28 years of uh working networking in security um so I am older than a look honest currently working for a company that's very focused on dns-based security I'll explain what that is as we go through uh because you know DS is a dirty word to some people actually it's a thing that holds intact together that and bgp we won't talk about that today I'm currently a senior manager at info
blocks um I run the pre-sales team for UK and Ireland but I'm very closely aligned with our intelligence team and other parts of the business so anyway that's me today's topic so I'm going be talking about Bad actors in Supply chains now arguably some of these are Bad actors perhaps one face on here more so than others but uh we really shouldn't pick on Steven so yeah anyway I'll explain a little bit about what I'm what I'm talking about there in a minute and when I talk about Supply chains I'm not going to talk about Amazon specifically but I like to use this just as an example so that we're level setting what do I mean by Supply chains so
companies that have many moving parts inside their organizations and I'm going to talk about how the criminal actors are no different so if we think about Amazon they've got Logistics third party companies and their own doing Logistics they've got third party companies building packaging for them their job is to do really what some of the criminal folks that I'll talk about today are doing right they are finding Supply and so when we go on to Amazon what do we see we go oh you might like this based on your searching history right it's putting things together putting people with products and this is no different in the criminal words right it's finding victims for the different criminal
entities any Amazon's just an example just just a level set I'm not picking on them so context is good I'm a huge believer that anything we talk about we should always give context around it so we know what we're what we're talking about so most of the things that I'm talking about today are names that you won't have heard of right we're all familiar with the AP this and the such and such blizzard that and the Cozy Bear the other and the Atomic Kitten something else I think the last one possibly not bad actor anyway for the ones that we're talking about today you probably won't have heard of okay so it's something a little bit
little bit different hopefully for for you guys now to find different stuff much like Mr Liam niss here you have to have a particular set of skills and a particular data set to go applying those skills to and that's really what what my company and others like it do very very well we have a very good data Lake specifically of Enterprise DNS data to go and find interesting stuff okay all right these are the names that you probably aren't familiar with so we've got various dogs and pumers and seahorses and meats and lizards and Vipers and this is this is what we name them but behind each of these is a technique so in the case of dogs that
tends to be C2 Behavior it tends to be things like remote access troan and various other nastiness pumers are link shorteners and I'll talk a bit more about that in a bit seahorse anything to do with seame manipulation so if you're familiar with DNS a c name is a way of providing aliens so you have your normal record there's an alias going something else vipers are traffic Distribution Systems and again I'll talk about what those are um as part of this um you know lizards and meats it it goes on M cats are kind of interesting Meats is just scanning and proving tends to be Behavior coming out of China but again just say an entire talk on its own
that one so these are the ones you won't have heard of all right so let's double click in and see you know what some is doing now the one thing I will say is and maybe this is me playing outside the rules here a little bit normally when folks like myself submit a paper to do a talk at bsides or any other event there's quite a long period of time between when we submit the thing we want to talk about and the actual day of the event so when I admit this I was talking about something called Vex Trio Viper right one of these vipers down the bottom here um the world has moved on so it's not just Vex Trio now so I've
expanded this slide and you'll see it as we go through I've expanded this slide to talk about some of the more recent findings okay so hopefully that's within the rules of yeah Tom we're good all right you don't care move all right so it's all about the money right and let's put the cyber crime economy under the microscope just for a second so the actors that we're talking about are becoming service providers to Affiliates okay it's part of a supply chain like I talked about like Amazon they build these hosting networks they provide traffic Distribution Systems proxy networks they are the ones who are serving up the victim to the actor groups okay and there's there's
money changing hands at all parts of this cyber crime is learning from physical crime again having this network of people that do the things you need them to do right if I'm in the good old days breaking into a bank well I probably paid someone who's a really good driver to be my getaway driver I've paid someone to be the guy with the gun right I've paid someone to be my Inside Man at the bank right all that stuff fine no different absolutely no different the only difference is it's not in person now is behind the keyboard from halfway around the planet and crime networks are transnational by Design deliberately by Design right no one wants to make it
easy for the NCA or the FBI or whoever to track them down to find them to get to attribution attribution is actually really really hard in the Cyber realm so I mean certainly we the company I work for don't tend to try and get to attribution leave that to other folks CU normally by the time you get to attribution far far far too late as Defenders far too late all right the horse is well and truly boled at that point okay and you've got shell companies and all sorts of things going on in between the off thecate and hide behaviors are going on hide the real attribution of who these acts are okay let's talk about traffic
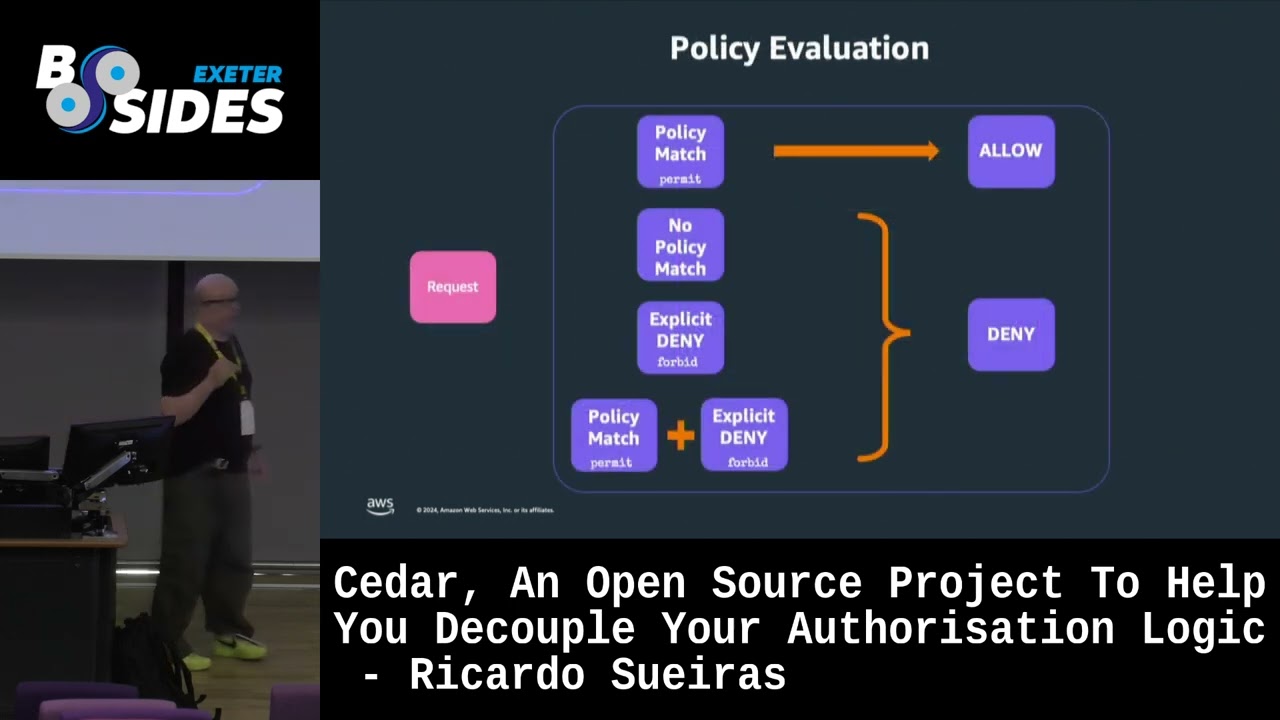
distribution systems for a second what do they do sit they serve up victims amongst other things they filter the inbound traffic so that only the profile of the particular target audience reaches the particular form of nastiness that a particular actor group wants you to reach okay think about that for a second all right you got this adwar and noise and you know someone's clicked on a fishing link or whatever the same thing doesn't necessarily happen to every single person who inadvertently clicks that link or redirects that web page or lands somewhere that's compromised okay different behaviors happen depending on who you are where you are in the world what type of machine you've got that's what these folks do they're
providing a filtration layer okay serving up the right people to the to the right form of lastings they can function as a low balance making sure that the traffic is directed and they provide protection they hide they provide obis to the actual active groups so if you're a criminal and you want to make some money we all know that you've got things like grants and we have hire and you can hire bot Nets and you do all this stuff right this is is a middleware player who is basically providing that middle ground between victim and and act and of course there's money flowing they can keep metrics on who do they send where and what
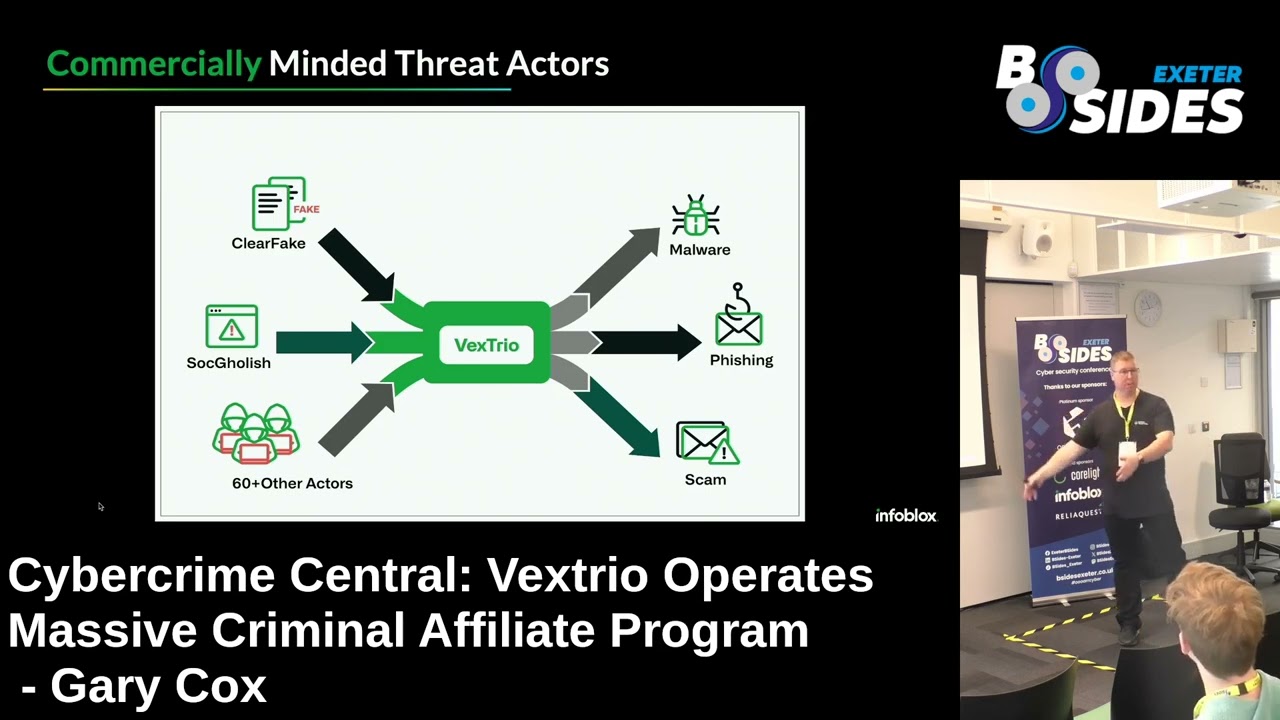
why that way you can pay out rewards okay now I would say this is no different really to any other affiliate scheme you know we've all seen sort of referrals like you know refer your friend to the bank right a link goes through great you're going to get 50 Quid in the bank for referring same with people opening up gambling accounts you know refer a friend Here There and Everywhere this ad took you to this right no different it's just now we're not on the legitimate side of the house we're on the criminal so let's talk about Vex Trio this is I would say the actor we see the most in something like 70% of our customers
traffic now let me put some stats around that for a second okay infox has got approximately 13,000 customers globally okay this is the who ho the footsie this and the fortune that whatever right so we see these guys and the various domains that they use it's not just one domain it is thousands of domains means inside 70% of our customers tra that's vast they have no business being there at all there is nothing business legitimate about anything that goes on inside this network okay so like I said we've got various folks you've got sock goulash clear fake there's form book which is X loer all of this is using this infrastructure so we've identified approxim 60 other actor Affiliates
inside this network so there's no it's not surprise really it shouldn't be a surprise that it's so prolific when we look at the traffic and like I said really all it's doing is inbound outbound right who is my Victim what form of nastiness are they going to get landed with it's all they do and these folks have been hiding in plain sight for so long absolutely so so long I mean I think these guys from memory I think were around since something like 2017 2018 when we look back over the passive DS data and start seeing the the behaviors that we see that identified so a very very long time and why has no one
spotted it quite frankly no one's been looking no one looks in DNS for stuff that just looks like traffic redirects do they no they do not we all worry about attribution like I said we've all heard of the Cozy Bears and the APS and the blizzard this and the blizzard that we've heard of that stuff cuz that's attributed someone's done a first find they published a report it's out there we know what it is we know what the indicators are we know how to block it not this stuff because it's in the middle right it's a bit like me saying to you which company makes Amazon's packaging anyone anyone no that's comp called D Smith they're based in the UK
but point being no one's heard of them we've all heard of Amazon same thing so someone asked me this morning you're doing a talk are you a geek I'm not but I thought i' put some geek like slides up for you um this is various different ways that that it it can redirect it can use text records it can use C Name Records uh a text record is basically just a a pointer right it's a DNS record that contains whatever string of characters someone wants to put in there and it's a way of identifying and then you know cause effect being able to supply a different answer point someone in a different direction provide a different
bit of metadata okay I talked about obfuscation hiding this is something else that these traffic Distribution Systems do on behalf of the Bad actors and I apologize for that's in the back of the room uh this will be tiny for you but I'll talk through it because we don't need to worry about the code we only need to worry about what it's doing and what it's doing is this right it is looking at who is the source where is my traffic coming from oh it looks like it's in a virtualization environment maybe it's a Sandbox fine I'm going to redirect you to a legitimate site no harm no fail right I'm going to look for is it in
Virtual box I'm going to look for is this scanning Behavior it's trying to basically hide from researchers it's trying to hide from people that might I uncover what it's doing and why it's there and again this is very useful to the Bad actors because it means that it's one layer of hiding one layer of obscuring them from being found out and from the FBI coming and knocking on their door so C records uh quick show of hands in the room uh who knows what SC record is I was expecting a hand up there okay fine all right for those who didn't put your hands up um a scena record is an alias record it it basically is a way
of redirecting to another name okay so normally in DNS we'll have the IP address which is the host the system we want to get to we have an a record which is our originating record of what that thing is then C name com in Alias pointing that a record okay these folks will use chains of C names to again hide things which makes it really really really easy to just change one thing and the traffic go somewhere else we can change the names we can hide behind stuff which is easily changeable okay so I would say and this is I'm going to throw this out as as a comment anyone working in security and or cyber security depending on your
preferred terminologies should at least know the basics of of DNS today just to know how this stuff plums together okay because it will help with analysis or it can help with analysis don't need to be an expert on it you don't need to be the guy that wrote the book on it right fine we've got him on staff so you can't have him anyway but it is useful to know what a scen name is versus n record versus PTR record etc etc etc Okay so now let's talk about something else um is everyone familiar with the term djas domain generation algorithms some okay let me throw an r in front of that for registers so a lot of the time with djas
and the thing with with things like domain generation algorithms is there are the way of creating hundreds or thousands or tens of thousands of domains to be be used by um malware ransomware whatever other form of nness traffic Distribution Systems Etc they normally don't get registered if you register a domain then you're paying to use that domain right it's not just some noise out on the internet you've actually paid a register to use it right so there's why would I do that if I'm I'm just got these throw away stuff why why would I pay to well part of the thing that we do as a security industry is we look for reputation right it's just got a
fraction more reputation if it's been registered because someone's actually bothered to pay and have a domain yeah but you can still run scripts and algorithms to generate tens of thousands domains and register them so our DJs or registered DJs is again it's a different flavor a different variant of nastiness and it's it's important to know stuff exists I I'll talk about why in just a moment okay but I want to introduce this as a terminology to to you guys today so I said I was going to bring this bang up to date so Vex Trio was a while ago okay if we look at the date of these so revolver rabbit 17th of July what we on today
27th 10 days ago vigorish Viper 22nd of July all right so I'm bang up to date for you guys and anyone else who's watching this in the years to come less less bang up to date for them but anyway for those in the room I'm bang up to date and the reason I pointed these two out and we'll go into big Viper a bit more in a minute but revolver rabbit is a rdga based so registered domain generation algorithm based traffic distribution system now let this one sink in for a minute they registered half a million domains now if I'm registering a domain I have to pay some money for that right so let's for the sake of
conversation in the room because we're amongst friends let's call it $2 per domain that I need to register okay half million times 2 any math geniuses in the in the room so someone has spent a million dollars just on buying domains remember they are middleware players someone is paying them to use their service someone is getting money from the victim right there is enough money in this criminal activity for someone who is just the equivalent of the people that make Amazon's cardboard boxes to invest at a bare minimum because I'm guessing their servers and there's stuff behind it right but just for the domains a million dollars let that one soak in for for a
second right that's a lot of money it's a lot of money for someone that we've never heard of who's just running infrastructure for other criminal groups to leverage in the case of Vig Viper and the reason we call it Vig is to do with gambling if everyone knows what Vig is in in in gambling uh it's basically the cup that the house makes right so this is all to do with gambling in in China so so gambling is is illegal in China and Great China um doesn't mean they don't do it there's just a huge criminal Enterprise there that benefits from letting people gamble that shouldn't or legally aren't allowed to gamble right same thing one of the domains that
this thing uses which is kb.com I think from from memory short one slides a minute um that domain alone one domain right not half a million a single domain that was changing hands for around about half a million dollars so again there is significant money being invested just in the DNS infrastructure that sits behind these criminal Enterprises which again when you think about that how many of you have the pleasure of going to your sea or your board or whoever and going have half million quid to buy a new control please have some money these guys are doing it so let's talk about V Viper just for for a second I'm whizzing through through these these slides a little bit
so I I'm not particularly a football person but there's some logos up here that like some of you if you follow football might be aware of if not you've probably at least heard the names Manchester United and Aston Villa so what's uh what's Manu and Aston Villa um and I don't know if the other one is some Dutch team I don't know um what have they got to do with Chinese criminal gambling these are legitimate organizations aren't they Sportsman running around kicking a ball spit on the ground hug each other or something I don't know but anyway what they're doing is there's these shell companies in the middle so kb.com yabu and so on right these shell
companies look like legitimate companies and they are effectively gambling companies they pay for [Music] sponsorship through the different sports clubs right so great they look legitimate their brands are seen on the on the banners going around the stadium they are seen on the sleeves of the shirts this gives them a degree of credibility so it means that then folks especially in in China who want to Gamblers Stu they go I've seen those Brands great yeah I'm going to I'm going to use those Services those criminal services they don't know that or maybe they do they don't care because they know it's a legal sit be doing but you've got this flow coming down from the folks at the
top who should do better due diligence on who their sponsors are all right fine you know they're getting you know money from these folks to have a have a logo I won't I won't knock them for that fine then you've got the brands in the middle here then you've got the domains that have been advertised so kb.com was one I mentioned earlier but you've got yo.com and so so on and so forth and then underneath you've got well you've got this you've got yet again a traffic distribution system using proxies using DNS using C names and what this is doing is it's figuring out again who is my audience now if I go to one of these domains I
will land up in a very different place to if my IP looks like it's in China they will end up probably in the right place probably depending on what systems they're using whereas I won't I'll get redirected to some nonsense right and again it's all about making sure my intended audience reaches the place that I want it to reach you follow the money now the thing with these guys is like I said these are criminal organizations uh typically registered out of countries that in fact actually I think the Philippines recently cracked down on it but um they're registered in countries where they can do business typically okay but behind the scenes here you've got human trafficking you've
got p pig roering scams all sorts of stuff because folks end up in debt with these criminal organizations because it's gambling and once they're in debt they start being blackm they start being leveraged so there's a whole lot of nastiness that goes on behind the scenes here and you guys thought you were coming to a nice light talk about DNS today right so all this stuff plums together my point to you is we can leverage Dess and intelligence if we're looking in the right place in the right way to uncover things that are much bigger than the sum of their past and this is an example of of that the other name one of the other names
that was on the ACT list was was prolific pummer so same sort of thing except what this guy does is a link shorting service so anyone use bitley or Al or anything like that you certainly would have seen it right yeah guess what the crims have got one of those as well and why have they got it cuz we're humans we're fallible we make mistakes right oh it's just a shortened link probably safe I'll click it anyway all right the guidance from whether it be r ncsc or UK gov same in in the US nowadays is be super suspicious about you know shortened links because you don't know what they are you don't know what's behind them
okay and as I said the Bad actors have got one of those servic as well right it's not just bitly and hourly and the others that are out there who aren't just but who knows anyone pay for their services but again this is what prolific pummer does it takes a shortened URL redirects to the original Badness okay so if you're not inspecting this stuff and think about it right chances are the shortened link isn't going to be in your protective feed chances are the redirect is happening further down chain so you know compromise compromise compromise so short s going to go too deep on on prolific pummer today this is more about the different techniques
right so as long as you've registered link shorten as a bad my job is done on that one but basically you know you users are wary of of strange domains they won't click links but shorten links somehow we bizly trust I don't know why I haven't delved into the psychology of it but somehow as humans we go yeah whatever right I don't know why this one is a malicious link shortener as I said you know creates links for other other other entities usually supplied through text messages that's one reason for having a shorten shortened link right if you're actually using an old school text message and when the users click on a link they will get redirected like so
many of these traffic Distribution Systems to whatever nastiness is floating around behind it okay now I wasn't sure who my audience was going to be so I five per a too long didn't read in here for you all um and this is could be true of traffic Distribution Systems or DS either way is good but yeah I know a guy who know guy who knows another guy right that's kind of how DNS and C name chaining and everything else works so throw that in there just uplo my audience now this is how we go about doing things I don't expect any of our customers to do this because quite frankly you haven't got the time effort energy teams
or data set to do okay but it's all about identifying these patterns this is DNS activity traffic out on the internet okay this is not a normal pattern a normal pattern would be fairly scaton right right because we're all Unique Individuals we make our queries and we're going out to the tin websites that we go to sometimes we see clusters behavior for legitimate stuff obviously Office 365 domains U Google domains etc etc etc we remove that from our data right we don't care about the legitimate stuff so when you then start to see clusters of behaviors that aren't the well-known websites well that leaves something that's worth investigating and this tends to be how we would start our
investigation right by double clicking on one of these clusters and figuring out what's behind it what's going on what is redirecting to what is redirecting to what is redirecting to what where is it going it's kind of like you know follow a rabbit down the down the hall right but it's important to have the right data Lake and the right people and Tool and stuff to to do this so what can you guys do you can you got the data set block the traffic Distribution Systems okay I'll go back to my lovely Amazon analogy if they haven't got any packaging they can't send the packages all right if you've let the air out the tires of the
lores yeah they're going going to need to pump the tire the tires up again right whatever bad analogies but same is true of tra traffic Distribution Systems if we disrupt them as an industry I'm going to say we I'm talking about us as an industry not just you guys as Defenders of your organizations but if we disrupt the tvs's it's making the cost of sale for the criminal actors higher okay it won't completely get rid of them of course it won't all right it's a game of cat Mouse the entire time you guys will know that but we can make it harder for them so summaries and takeaways criminals have Supply chains too they have for a long time the
industry folks like us and others are slowly uncovering extra bits of the supply chain that we didn't know existed right we've known about ransomware as a service for a very long time we haven't known about the traffic Distribution Systems that sit behind the stuff okay now we do these Supply chains invest millions of dollars in building and maintaining and refreshing this infrastructure okay and that's a key word this is infrastructure that they build own operate and post and resell likely the supply chains know more about DNS than you do likely they know more about it than I do okay we've actually been impressed as the wrong words when we talked about actors but I'm going to
stick with it we've been kind of impressed by how how they're leveraging DNS how they're using it to hide in plain sight and have been for years okay only once we build the algorithms of things to kind of detect the ways they're doing things do we start to uncover this stuff so it's all about the data science really okay traffic distributions are hard to find but be highly disruptive when we want them so with that that's me done hopefully I'm well within time well with time excellent I'm happy to take any questions but equally I'm also expecting stun silence because it's DNS after all so what regist are they using because most of the registar are highly
regulated through IAM so how are they actually registering this number of domains uh the question is what registrars aren't they using um so uh the reality is it's it's it's any and all yes there are some that are better than others um but yeah it's it's it's prolific some of the stuff becomes really easy so if you look at different top level domains people are doing you know xyz.com and toop and that sort of stuff that becomes really easy BL she go right fine but actually um prolific pummer I think it was in the colleages the back room might keep me honest um they were actually using one of the US reg STS who is a very reput
and comfort be registering all their stuff legitimately so a l of that abuse protection regist but they're just not doing expensive well again it's not illegal to register a domain name so very hard to say well you can register you know you Google so you can register a thousand domains on our service because you're obviously legitimately using them but you as an individual over that can't that would be a nice control to be put in place but very few do that because I said it's not it's not illegal to buy it but there should be questions asked I 100% agree with that as a statement because again same as the statement I made it's like what legitimate business
purpose is there it should be qualified but yeah it isn't good question do you think any connection between groups and groups yes 100% 100% so any form of nastiness whether it's ransomware malware fishing child pornography anything anything anything sits behind this stuff their job the traffic Distribution Systems is to pair victim with [Music] actor it's exact it's exact it they are a middle wear player which is why it's it's disruptive if we could disrupt them yeah any more for any I've got a question um so there's like various kind of home use kind of like free tools out there that do like DNS filtering blocking stuff like that Y is that similar to the service you offer but
just on an Enterprise scale is that the kind of I've been so good about not talking about product this is B size not inic um so yes in essence there are things like like py hole DNS filter and so on that we can use home um the reality is they don't have access to these type of dat sets so yes the methodology is the same I try not to worry too much about the blocking aspect because blocking is easy you can block on any control you want or just ingest data into the Sim and then figure out what's what in the you know who's who in the zoo inside the network so I don't tend to worry about to blocking but
essentially what you've said is correct is we have a a data set that data set can be applied to any DNS server thank you all right more more you show the slide on your traffic graph you mentioned you ignore google.com and off whatever because that's normal yeah um does that then mean that you would be ignoring C name takeover Texs where someone's got an aure service that they then deleted but not remove their C name okay so so no but it just wouldn't form part of the data set that looks at a tra distribution system so that's a completely different set of analysis you're right so you've got subdomain take over you've got all that kind of
element uh which is something we should absolutely as an industry focus on um but that's that's that would be a different subset of research to the tdss right but there's a nice little overlap in in the middle I'll gr I'll grant you that one but but no we wouldn't classify Google or an Amazon or an A or y y yada as part of a TS but we do look for um behaviors that go to their domains and subdomains which is um not normal could be or whatever so answer question yes yes something we care about but it's not doesn't fall into the research for
T no we're good thank you very much yeah thank you car excellent talk thank you