Who The F Called Me by PUNICODE_STRING
Show transcript [en]
hi i want to say welcome to everybody this is my first talk i did some research for my uni dissertation and i just thought it'd be kind of interesting to show to people uh so basically a little about myself i don't know who on my slash full screen because that's going to be cliche windows nerd um i have some certs like oscp clt are not going to list them it's useless um i got first in a cybersecurity and digital forensics degree if you're going to go to uni the demographic isn't really for that but do computer science don't do cyber security so my motivations for this talk is i implemented an interesting technique and just thought it'd be useful so it's
basically about taking a return instruction pointer basically feeding it to an intrinsic and getting a function name and a modular sorry a module name and a function name without using debug symbols so basically um this is the content i'm going to be covering so first thing is stripping crt and win32 basically tiny binaries you can early load a dll into a process um so loaded translations use very useful to know as well uh caller module name exception handler record uh information gathering not going to read out the rest you can use your eyes um okay so this talks kind of intended for movies if you know anything about windows internals you'll see the content isn't too difficult uh i'm also
by no means an expert i'm a new i've only got like about a year and a bit of windows research c programming that kind of stuff um so basically the content of my uni dissertation is tiny but the stuff you kind of want to be interested in that i found interesting project management and literature view isn't too too fun so basically what ended up happening is i just took some sector seven courses to learn c and some hooking theory basically using like detours uh other hooking libraries like min hook um basically edr bypassing uh direct direct mass and like a uh assembly uh cisco's uh learned a great deal about process and memory based windows
internals very useful things to know um so basically my biggest problem that i came across was i could hook basically memory management process management uh functions but i didn't really know why certain hooks were being hit and i couldn't actually translate it into a way that humans would understand uh so as it says here friendly human friendly um some very useful information crt and win32 or the universal co2 runtime basically crt handles like exception handling like useful debugging information like if you screw up you basically get handheld way through when 32 if you know anything is basically like hardware from a high level perspective you can um basically interact with memory interactive processes etc uh as it says tldr basically you can
screw up bracelets [ __ ] off when you get handheld your way through and win 32 instead of like calling anti-api stuff which isn't necessarily possible different across different operating systems you get that abstraction layer so basically i'm talking about cleaning dependencies first so take this example is it like a less boring hello world for example uh you wouldn't expect much to be going on the background a simple pe that's not the case a lot of crt a lot of like runtime stuff that you can see dependencies from names i'm nervous but it is what it is um so you see here like the the range of functions are being used so we need things to actually depend on so crt if
you don't have crt stuff you come to issues so as you know if you don't have anything set up you fail yeah um basically you can take this a step further and you can strip crt and win32 use the custom entry point and i use process sake and the internal headers because they're beautiful and some very smart people worked on them uh so these are the steps to remove it from the visual studio project so basically get rid of run-time checks sdl checks uh basically just force a private private lib from ntdr and displaying progress messages is useful too um cool so as you see here i only depend on dbg print which is nice i don't have to have
anything loaded before me i can like kapc inject the dll into a process with gucci um you see it see here from an analyst perspective fairly any functions in our script binary loads of crt related functions here on the left so now i'm going to talk about loaded translation and contracts um so you see here this is like a typical diagram you'll see let's get out the way of the projector a typical diagram you'll see which actually completely abstracts the loaded translations the load the translations are ways of staying portable across different versions of windows and a basic simple virtual lock actually imports from a umbrella library or a contract library that forwards to kernels that you do and
then kind of called final base and i had to write like a little tool based on um someone's research which i can't remember the name um so you see here it was lucas g that was it uh these are some really useful resources and the api setting up cpu plus from zodiac which is um someone once again knows but it is what it is uh so you see here uh i came across these two products dennis fabkin very very smart man you wrote a project which is like kind of aimed towards game cheating where you can um create a driver an unsigned driver and as i said before okay abc uh load the deal on the process which steals the
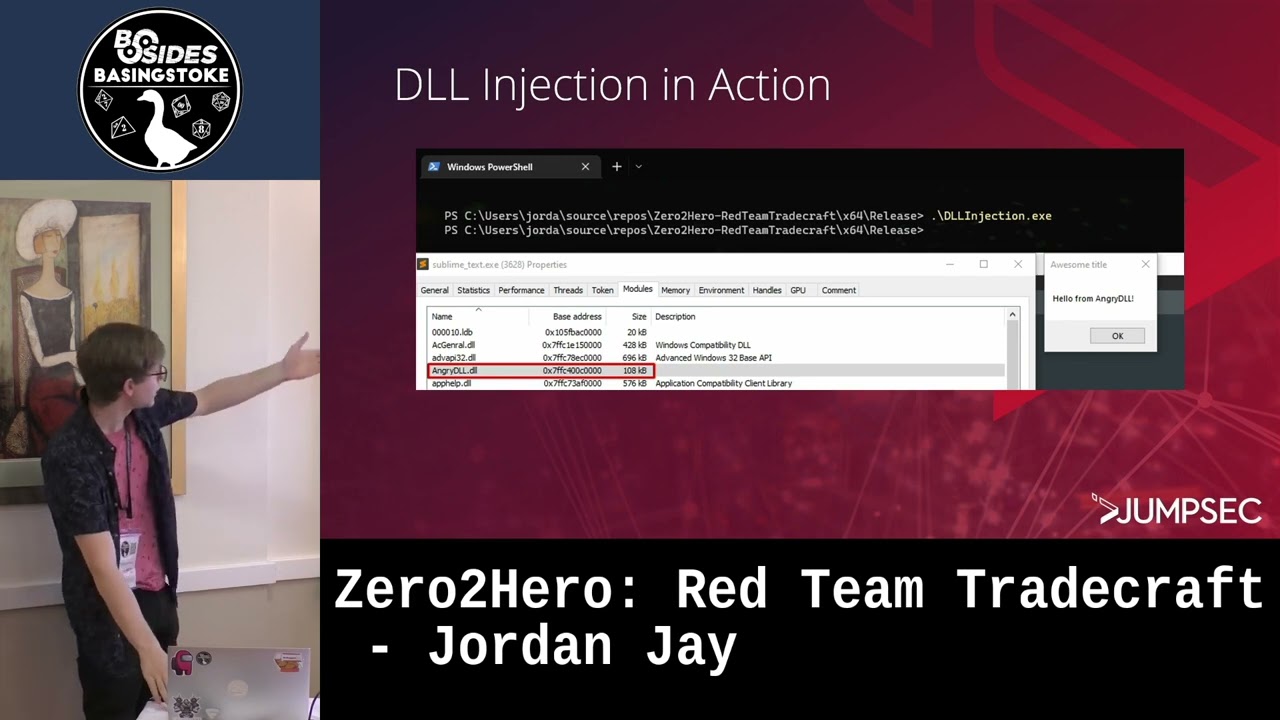
service um security descriptor from a known dll and basically allows you to uh bypass like things like sig code integrity guard and processes like uh edge which is cool really really interesting uh so i'm gonna talk about hooking now um so basically with hooking i was able to intercept and tamp with like most memory management function calls on windows like process creation as well and this is process introspection which introspection isn't a real work but yeah um detours was the library i chose but as you can see here with a uh a graph of what actually is involved it uses win32 so as we've seen before we've removed win32 from the process and as you see
it's a slight problem for us uh people [ __ ] on detours which i don't really see an issue with detours like save with they say with um threads you have problems but i didn't have any problems like tampering with simple malware um um yeah uh min hook was another option but getting min hook working in 2022 is just a bit of a pain in the ass it's like a 2006 2008 project and i didn't have the time to screw around with that um uh yeah so also w benny has another project called details nt and everybody says don't be a pacer but if it can save you time you can get the job done and you
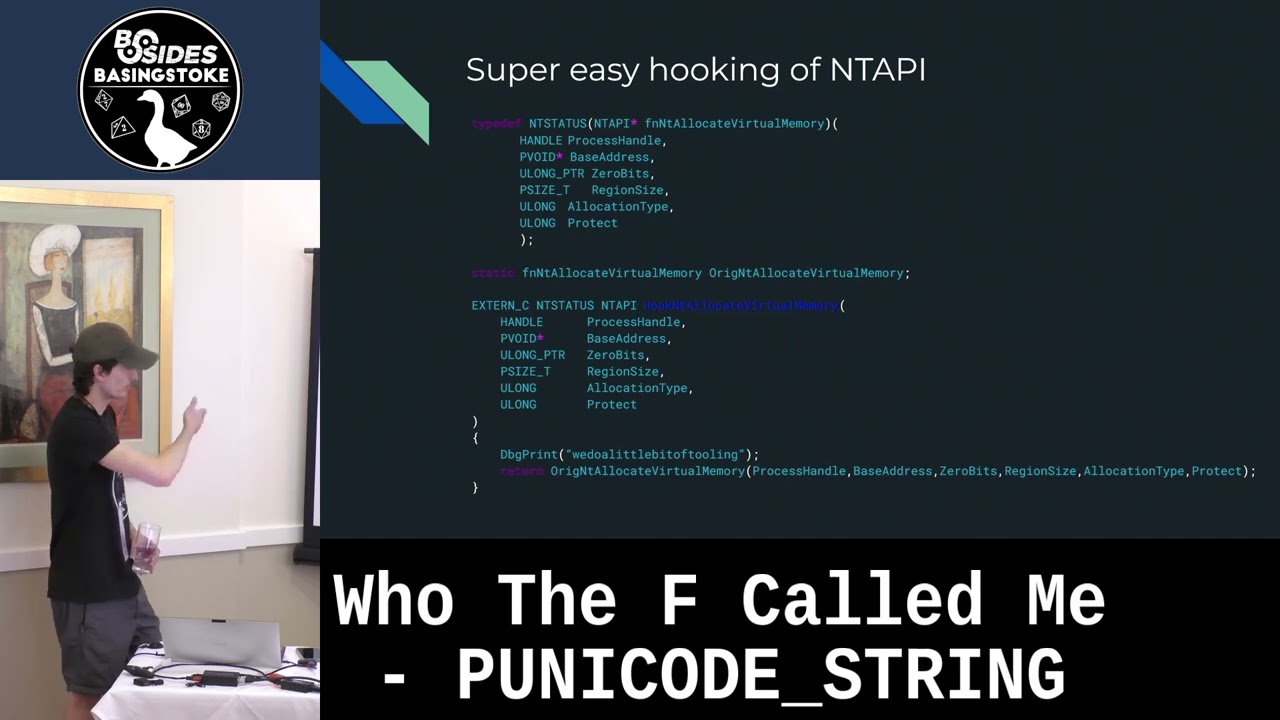
understand what it does i don't see an issue with it like as you can see here with the tool by lukas g now i can't remember his name uh you only depend on ntdr which is beautiful which does exactly the job you want brings back to the kfc point um so hooking like an empty api function is really really simple so you just basically get yourself a typedef basically have a function prototype which is provided by uh phnc headers uh get a copy of the original pointer and then basically you can sample with anything that gets passed you can print out parameters you can uh basically have extra extra functionality within a hook so this is the point where i was talking
before i didn't know how to translate into a human breed of war human understandable thing i just had things hooked i could do things in place of process in place of the process function i'm sorry um so we could use assembly to like walk the peb and then basically just get a past pe and then get your function pointers that's one way of getting the win32 function pointer from an ncd or dependent uh dol but i found a different way so you can use um you can use low to get procedure address which gives you a nice set of information such as like module handles and um so this sorry this is an ntdo equivalent
of load library get proper address so you get loaded load loaded load deal while unloading get procedure adjust and it does the job nicely depends on ntdo again um so this is where i was really confused i was like i was getting two or three extra functional rules from a like a process which i didn't really understand and i wanted to know why and so i took a bit of the dsor part of the awful pun so this would allow me to get meaningful information so uh memory addresses of hook that aren't useful to humans changed into a into a meaningful meaningful human readable string such as for a dom human like myself um so this provided the process
introspection visual studio used the debug information from the eas if you provided it but had a hard time translating a break point and like hovering over a memory address within a hook which is i wanted to understand why that was actually why i could sorry how i could do that if i wanted to carry out without debug information so i'm going to talk about caller module name acquisition so basically you can use the pad walk in memory or the module list and basically you get nice human readable information about the module such as say kernel based current x2 etc and this can consist of pointers to nice structures which have a lot of information which are friendly for me
this is really tiny um so this allows us to keep track of like modules loaded in memory and order kind of basic stuff if you know anything about windows programming uh so you see here these are the structures associated with the main important things are the dll base the full dll name and the entry point three things are really really useful for me in this project as you see here this is a wikipg output which contains a human readable list it doesn't actually go into the substructures within it but it's useful for a demonstration purpose uh so now let's talk about exception handling record information gathering um so basically this allows us to get a
pointer sorry before that i'm going to talk about a return address compiler intrinsic so this allows us to basically find the rip into a into a function called a function so in this case if i had this inside of inside a hook i'd be able to point to whatever chord hurts to say memory managers or a loader function called it i'd be able to understand why that hook got hit so from this uh i'm able to step into exception handler information gathering so the p data structure which was actually documented recently by modex he did a really cool information really cool post about getting ssn's uh basic cisco numbers from these these structures um it contains like a wealth of information
stored in the p data section of the pe these are registered for functions that basically allocate stack base or call another function aka from these functions so not at the end of the chain um yeah so nd7 has the poster of huddle link right at the end um so to get these actual exception handler records you can use artillery function entry which returns you runtime functions as you see you get a control pc image base really really useful things um from here we're able to get by the beginner address of a function which allows you to call open32 function without having to go through all this uh all this extra jumping through hoops as you see here this is a
intellisense basically hold hand holding so i've been able to see from like anti-allocate virtual memory this is actually called by virtual lock so i'll be able to watch the the cool hierarchy all the way from 132 all the way to mcdr as you know this is user mode hooking so if you use direct ciscos or unhooking you'd be basically able to bypass this this hooking logic but i didn't really care just for learning um there's one caveat with this there are certain things that aren't actually exported as you know by a pe so private functions such as rtlp functions or loaded key functions one step further if your actual target doesn't have any expected exported
functions you can't get this like name called this this hook basically so that would be in the case of like virtual protect and then you wouldn't be able to jump up to whatever works you protect um so to implement the full technique what you can do is now we have all of these steps we have all these steps completed we can clean our door from dependencies basically as i said before you can turn into pick cortana's okay if you see ready ready doll um we can return the module name and uh function module function name and i'll take off the list and we can trace all the way down to the kernel so implementation horrible to look out but it is what it
is don't judge more unsafe code this is just learning code as you know c in max voice like even the experts can't implement c and c plus plus perfectly what would someone would like six to nine months of see programming be able to do uh as you can see here we can step through logically it takes a pc value which is program count value yeah or rip basically which is provided by the intrinsic mentioned earlier you can step through get a runtime function for it if you get a runtime function you can search an address within a module that will allow us to get a uh that will allow us to get the point into the module which you can ee pass
basically passing is like day one stuff you learn um from that you can step through the exports and compare if that uh if address is within an export exported function therefore from that you can actually get the function name which is useful really really fun so now is a quick demo uh let's hope the demo goes from my side please be on my side oh sick oh this is really annoying because i've got a 4k laptop everything is like really really blown up i don't know how this is going to look as you can see that giant that bars at the top so we'll go with the non-clean binary so this would be a um
a pe which caused something this would be horrible to look at but it is what it is you can see here uh while i've got linkedin as we see here our process gets attached uh we've got no errors and anti-allocated virtual memory is called we can see the deal that actually called the function so instead of kind of 32 if it was explicitly linked with it with we're actually using kernel based because we haven't linked anything and we see virtual lock actually called hook empty allocate virtual memory virtual lock hasn't been hooked in this case we can see the logic will jump and we can get the return address which points towards the code so i want to
clean the binary up
controller
yeah so you see the return adjustment anti-allocate virtual memory we've got no errors and yeah we can see our print demo cleaning actually actually called the uh function because this was just using the function in itself from phnt headers uh cool go back to the slides all right cool these are okay that's a little show for secret club by the way that was intentional uh yeah so yeah these are the references i used some very very small people in here as i said secret club we've got so very very helpful helpful on this project special mentions of dennis barkin and robbie and then we've got that night yeah as well up and coming he's got a
talking still which would be really really useful really really good and yeah basically so if i were to do another cfp i've been trying to weaponize a driver lve and i've been writing a hobby state phones uh important so i might just talk about that and get a bit more experience yeah cool all right awesome
oh so warm today jesus all right listen yeah we still got 10 minutes left in this talk i don't know what you guys want to do
yeah so if you have a pe and you strip crt and win32 you basically get none of the none of the hand holding if you strip out win32 you basically have to use pyrex uh you can either as i said before get the win32 function pointers build yourself a type def and call it that way or just be the same person using your exports which should be done yeah that's basically one of the issues um so this was if i had a target like a piece of malware that i injected this doll into the doll that's being injected is tiny my target doesn't have symbols because it's a piece of malware so this way i
wouldn't actually have to use like a pdb that's packed with it but it may have references to pdb but it won't be available like yeah does that answer the question i don't know if there's any more that's very speedy talk cool thank you very much for watching
you