Making Security Smarter through Decentralization

Show transcript [en]
all right thank you guys for coming we're going to get started with this next talk we've got Nathaniel who's going to give a fantastic talk most of you know him but I will not steal his uh Spotlight so over to you awesome thank you so much John welcome to the fifth besides I'm me we're halfway through the day so you've already had the welcome but I mean this is five bides wer five pretty awesome um yeah so thank you again for letting me present um very happy I was kind of like oh you want to present yes I slid right in Under The Wire um they kind of like the idea so hopefully you all do as
well um so what I want to talk about today is how we have this whole security framework and how we share information so this is like a thread Intel talk but it's also like how do we actually use thread Intel um and then what can we do probably better with it um so my hypothesis is we could use decentralization and so we'll talk about talk about that a little bit about me um I'm the F of twist uh you can call me Q simple first letter my my last name um I'm the co-founder of a company called uh trust security but I'm not going to sales pitch you I will ask for something at the end but it's up to you if you
want to do it or not I I don't mind um I am a threat analyst I have been in the industry for a little over 15 years um I've worked threat Intel I've worked uh threat hunting sock I uh I've worked in government worked in uniform I've worked in private sectors and corporate and I've kind of been around a little bit um I love puzzles any way that you can throw a puzzle I think it's amazing I actually prefer wire puzzles just because I like the clinky sound my wife hates it but that's a it's like I got to solve it I don't know um and I'm a huge block chainer I first heard about
blockchain back in 2008 had a mining rig in you know 2012 um and just playing with with blockchain uh I love the idea of blockchain I love how it fits how it works um and I think there's a whole lot more real world use cases that we can have for blockchain it's not just for cryptocurrency um so we'll talk about that email there please shoot me an email uh get on Discord I'm on Discord uh and Linkedin happy to follow and share and talk with any and all of you so the agenda that we have today is um I believe Intel sharing kind of has a problem today and I'll go through that um security vendors what is their focus
does that Focus fit you and match what you need as an industry as a company as a person um how do we do information sharing now how can we possibly do it later and then how do we make that smarter how can we actually uh make Intel sharing just part of your daily life and make it fast and actionable and meaningful and then we're going to look at the other side of the coin um little blockchain sort of thing there blockchain part of this so kind of fun all right so Intel sharing has a product this is the only Doom and Gloom slide to me it's like super doomy and gloomy um but uh it's also important to
see what we're looking at very beginning of 2022 ransomware 105% increase over the year previous Q2 of that same year of 2023 72% increase over the previous quarter right so we are massively increasing the amount of threats that we're seeing this one was pretty scary becc attacks grew 72% in the United States and 123% in the UK between April of last year and April of this year okay we're seeing massive increase in the adoption and usage of very fast very active threats 43 to 80% clickthrough rate on AI generated fishing eving okay but no joke things are going to get more pervasive more easy to click on we have to be able to react faster to
those threats when they're coming in little bit of Doom and Gloom here everybody knows MGM got hit by Al black black cat that was $150 Million worth of damage okay it 30 terabytes of data that were xfill from that and it was two-year-old malware just saying they have an average annual estimated guess of $39 million a year for security two-year-old malware still popped it okay so we are super slow in how we're responding to threats and how we can react to threats so that's how do we change that this is fun malware this is just ransomware this is fun data um this is just from the year previous to this um there were 250 lock bit 3 events
basically 250 all the way to about January um you know so lock bit is definitely the one we all know about FBI spend a lot of time focusing on them some of these other ones like clot black pasta other ones like beond uh beond L um two pretty good hundreds hundreds of compromises in a quarter okay if we add that all up we're looking at 5,200 successful compromises like published like these people were compromised in the year that's about a 100 compromises in a week FBI is doing stuff thanks FBI they stopped lock bid in January of this year the same this following quarter the exact same amount did they stop them not really um FBI also released a thousand decrypt
Keys like uh in the first week of this mon just a week ago a thousand if you look at the total number of victims they have there's 200 still some missing right so this is just kind of scary slides but just shows you the scale and the the verocity of of what we're up against so attackers have to be right one time Defenders have to be right a thousand times right every single time we have to be correct we've all heard this right many many times Albert Einstein had a really cool quote we cannot solve our problems with the same thinking when we created them and we have to think differently we created a lot of these problems we're creating the
open ex you know exposed endpoints we're creating a lot of these problems for ourselves we have to think differently about defending them the first step in my opinion means I'm a threat Intel analyst I like looking at threats I like seeing what what they're doing so we have to know what we're up against you can't defend or make any action unless you know what the target is or what you're trying to change right so let's first Define some of the risks basically there's indiscriminate attacks and then there's target attacks two buckets pretty high level don't hold me accountable for for like well you didn't not show you this thing it's like we're staying pretty high indiscriminate attacks basically
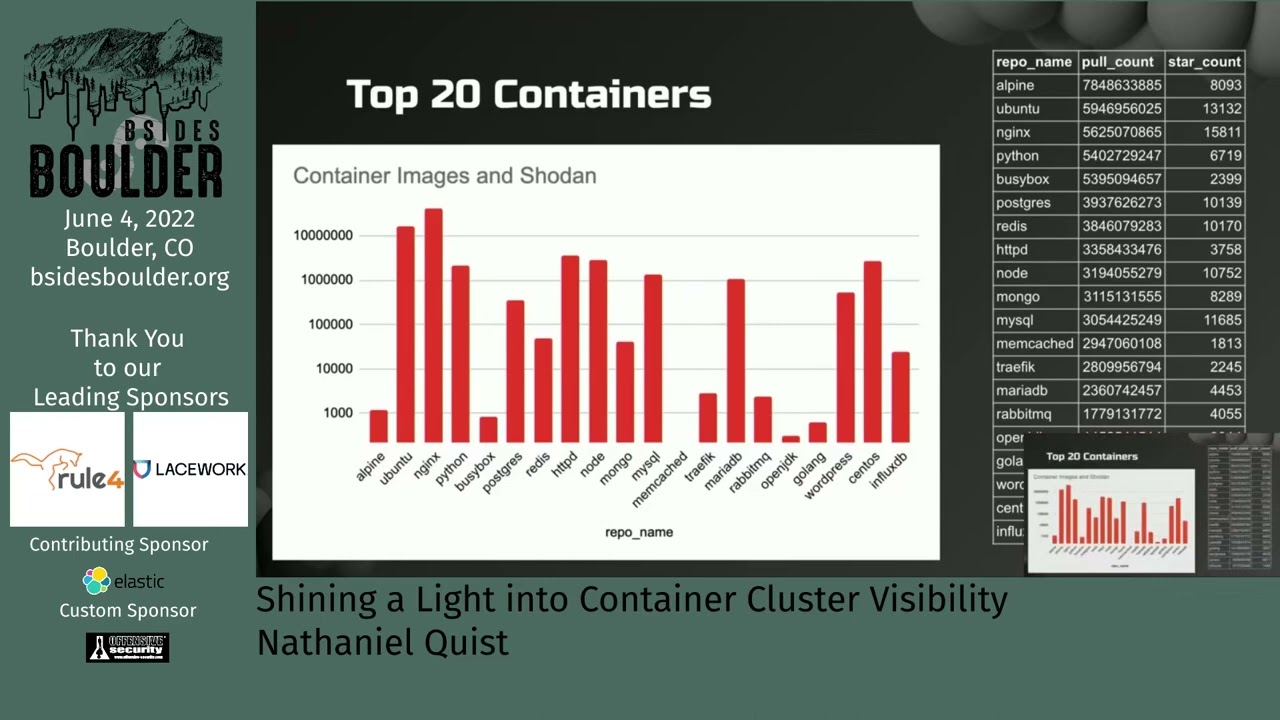
scanners bot Nets misconfigurations vulnerable exploitations things that are just openly random you can just go to showan and say I want to get onto whatever HP cam that's available in Korea and then here we go targeted threats primarily focused on industry primarily focused on Personnel fishing attacks BC things like that they're they're focused on data they don't care about the easy open threat they'll use that stuff but they're really targeted they're looking for specific ways into your environment so the threats for indiscriminate attacks basically Rogue endpoints you have an increased operational cost you get a crypto Miner and an exposed inpoint you know and you're just going to have now a thousand crypto miners using that same I access
management key and your cost just went up 100,000 for your Cloud cost this month and you're like oh is AWS going to refund me that or no um so then you have footholds for Target operations some of these things these these open-ended things um they go on the dark web your creds go out sell you can go buy a 50,000 you know I am keys for like you know so they're they're going to make money some way or another usually it's these uh end points that are just wide open and flapping around the risks for targeted attack this is where you get that internal data loss you get that those extortion attacks you get reputational damage um which doesn't
seem to matter sometimes you can just say hey I got popped I lost 30 thou you know 30 terabytes of data and people are like yeah okay I'll still invest in your company and you have a plan to go forward so sometimes some of that gets weird but um there is reputational risk look at change Healthcare reunited Healthcare holy crap that was scary and they paid a $21 million Ransom that's fun it's good payday and then the actors after that anyway different story we'll talk they they completely hosed their their internal operators people who actually to compromise change to get into it the owners who got the ransom just left them all high and dry so no
one got trickled down ransomware it's it's fun all right so nation states um if we're looking at targeted attacks we're really looking at industry level attacks okay if we're looking at nation state attacks we're looking at defense industrial base we're looking at Aerospace we're looking at government um education sadly is like super high on this list K through2 organizations are hit a lot when we start looking at becc or fishing fishing smishing all that large the industries kind of change a little bit the large organizations we have a lot of indust uh Insurance Consulting energy utilities the medium side starts going into the hospitality Healthcare and energy as well uh in that environment I have links if you want to
see sources for this basically stat statistica and and fora and different places um producing some of this stuff so who's attacking these things with the nation states I mean their motivation is really going to be more like that Regional base they want politically motivated they want to stabilize environments um they you know they want to escalate military confidence conflict or do pre military conflict in these environments um when we start getting into the becc and smishing attacks it's really more of that initial access those fishing emails uh maintaining access again financially politically motivated usually get selling or using these things in AP style environments um but it's really the industry and they they just go across an entire industry uh
think about using geni now just to say how many companies in this geographic region are in this vertical you know they'll pop out a whole list for you it's like okay cool I'll start crafting fishing emails to Target these people um that's kind of kind of what we're looking at so now the question is for everybody here how are you protected are you protected against these particular threats what do you focus on what do you rely on to protect yourself are you relying solely on your security vendors my security vendor should know what what I'm up against they should give me those detection alerts so I can you know protect myself are you relying on your
advance sock operations to build those detections to do that Forward Thinking to look at all the news that's coming out and saying these things are big I should have protections against that stuff do you have specialty teams like threat hunting teams IR teams that can handle that that particular aspect if you're a large Enterprise or even a mediumsized business you might have a few people in a threat Intel role or a threat hunting role if you're a small mediumsized business or you're the sole security person do you have time to look for all of that stuff okay then you are reli on your security vendor to do that or whatever security provider Intel provider you're looking
at so what is the security Intel what is their vendor Focus first off a vendor's Focus might not be your focus okay if we're looking at what a vendor is they're playing in very specific Fields you have people that are focusing in vulnerability sector like TBL and um you know Artic wols rapid sevens you have malware focused you know Trends micros carbon blacks this is not a comprehensive list don't mail me for anything um and then you have a network focused there's really only a few vendors at the very center that kind of focusing and hitting all of those areas but are they still hitting everything that you're interested in in that aspect so really
their data and their research comes from their customer base their data what they gather and analyze is how they offer protection to you and every single vendor in here on this list especially I'm to just pick these two because my current employer is Palo Alto and crowd strike going to point at you because you used to work there good for you for leaving I'm kidding um so you know these two do you think they're going to share information on their adversaries that they're looking at probably not that's their competitive Advantage so what does that mean means we have intelligence silos we're not sharing information with each other in an effective way so we have an intelligence focus at
the top tool coverage on the bottom we'll kind of get to this here in a second so now each vendor inside of that vendor they have specific teams looking at specific threats okay some vendors vendor one here is just really looking at e- crime and some you know crime Weare they're they love rans somewh they're not going to pay attention to APS or something like that okay yeah vendor two they love AP but they're only focused on China and Russia a you know vendor 3 they're only really focused on Middle East all right again we have these security gaps where you want to be in here you want to have all of the protections from all of your vendors you
don't really you know if it worst case you kind of want to be in where they're kind of overlapping and and meeting your needs right sucks if you're out here there's somebody that nobody's even looking at like the very bottom list you have a question s doesn't exist sure but what we're trying to do is z the Z is Zen a goal a destination Zen is mindset if you're a Buddhist right but it's so it is really like where the more you practice Zen if you if you are a Buddhist um the more you practice it the more easy it is to achieve Zen and you can be in the moment now so what you're
looking for is you're looking for all of your bases to be covered I just use Zen as a I mean I'm saying I'll give you example I've got a half dozen systems all with some systems that overlap each other systems different from different vendors and I don't have that single pain of glass to me Zen is that single pan glass right it's a it's a great point so so it's either the data where the data comes from all your tools speaking the same language you know how do we get to that point so again let's go back to the vendors talk right here they have teams they have Team compositions they have Team Focus looking on specific areas
they have customer bases that are feeding them that they're using to augment that data or to influence uence and help that data what happens here is again we have intelligence silos we're not able to get intelligence shared across a a wide customer base because not all using the same tools not all having the same teams give the same data or helping other people if you're if you really like this you're really interested in Middle Eastern you know events but you're security vendor is just focused on criware you know you want that data how do you get that data you know you have to build it yourself because they're not going to share with each other all right there's something that I
call the vendor analysis cost cycle it's a four-step process vendors need to have customers to supply data that data grows and grows and grows and grows you need to have analysts now we're in analyst sections right here you need an analyst to go through that data may not be analyst human analysts we might start investing a whole lot in AI we might focus on machine learning if some sort that is a cost you know uh requirement to spend on that and our costs just keep going up higher and higher and we need to lower the cost somehow how do we lower cost well we get more customers to offset load more customers means more data more data needs needs more analyst
more machine learning more machine learning needs needs lower costs and this vicious cycle can just keep going and going and going so what happens to your security products you know the poos CR stgs mandiant all those in the world I mean there they're raking in lots of money and they're always in a way to try to decrease their money and cut costs and spendings and what get cost and you know cut and all that stuff so this is a cycle that gets very difficult to maintain now if we all had a single source that we're all using for one source of data that collected all of the information and analyzed all of the information and we're all a part of the
exact same very large ecosystem you know maybe that's a different story but we're not how many vendors were on that side earlier it's a lot of vendors how many vendors do you have in your environment now you have a lot so what does your vendor look like what does your vendor customer base look like are you in an environment if you are the only agriculture company in a security company that is only financial regulatory banks are they going to be able to provide you with data their tool may be whiz hot awesome you know and it can detect all of the things but you know can it protect you is it looking for what you're interested in
it's a question for you to answer so let's talk about information sharing we're getting into the decentralized aspects there are 4.7 million Global Security ANS professionals worldwi okay more than half of them 66% participate in the professional Community bides Defcon black hat 44 % of them share their insights it's pretty awesome we are a kind generous willing to sacrifice our time and energy to make sure we are all okay that is what we do that's why we're here most of us some stats some very big notable stats alen involved otx 19 million ioc's a day from 250,000 different sources that's pretty amazing okay it AT&T bought alien volt for $600 million it is it doesn't make any money
AT&T wants to spend it off because it doesn't do anything no one wants to buy it no one wants to use it they want to use it for free but that's it right what happens where did it go there it is all right buyus total awesome I did not know did everybody know that Google owns virus total did everybody know that yes everybody should know that but I just learned that yesterday I was like what I didn't know that makes a lot of sense makes an awful lot of sense but you know anyway three million samples a day five million URLs analyzed a day unknown number of sources but a lot how many people use virus total is there AV tool
AV tool yeah you know I've never seen this hat before what virus to what do you think oh okay maybe we should block that you know I mean that happens right you know it happens uh any run pretty cool 10K samples a day 300,000 users now depending on your bar your level of stuff there's a lot of people that use this and donate to these things tools like infragard 3,000 members critical infrastructure if you have any critical infrastructure you're probably a part of this group in some way fash abuse CH always awesome um 30,000 samples 20 you know 20K spam samples a day spam house you know 5.7 million IPS a day that are analyzed uploaded and looked at it's
pretty impressive you know these are impressive impressive stats what's the context what is it is you know what is it do you have a hash value where was it seen who submitted it um you know what are the uh the you know virus totals really good at saying here's a hash value here are all my IPS and domains that it calls out to and it gives you a whole rundown of what it is but it doesn't tell you industry it doesn't tell you target of spam attack it doesn't give you some things so the cont of what you want from a Spam URL you want to block you know fishing in your environment right is that fishing you want to you're
going to take five seven million you know fishing URLs and block them every single day you know it's like can your security tools handle that you know do you need to block 7 million do you need to block just the ones targeting your industry or do you need to block just the ones targeting you know your type of person out I mean those are some questions how do we filter that down make it useful is the purpose of that Intel sharing that you're Gathering From is it actually clear and useful abuse CH has been around for a long time block list has been around for a long time um you know you can use them in your
environment but there's always this tag this caveat use at your own risk you know you could block things that all of a sudden you should never be blocked or you may block things that just may [ __ ] your security tool because there's just too many things so you know how do we mitigate some of those things so this is how we talk about making security a little bit smarter this is what I feel most organizations are today they are a very Stout rugged beautiful horned elox you know like you know mus and we got two circling ABS or whatever around us sure you might be able to take one of them out no problem
bam you know gone you have all this wool you can you can protect from plaws and scratches and stuff like that but can you really survive a pride of lions I don't know wouldn't it be more beneficial would you had more of a herd mentality we have multiple people look at these lines they're like oh [ __ ] not maybe maybe tomorrow see you you know so how do we reframe how we're thinking about security my belief is that we have more of a decentralized approach so what does decentralized look like we have all these little FL these spaceships up above never mind my company's logo right there it's just you know it's a sales
slide okay but I'm not saying it's the one and only thing but how do we take all of these different sources this could be fires total and this could be pal Alto and that could be crowd strike and then you know how do we take all of those pm2 so where this group of people the the people who need this the victims how can they decouple that intelligence that they're providing and have agnostic intelligence routing you're interested in exactly what you're interested in you're protecting yourself from exactly what you want to be protected from regardless of the source you want to be able to use data from this place to this place and use them together okay now there's a lot of
hurdles and cost and you know everybody's like licensing oh my God there's a lot of things that go into that we'll get into that later this is where the true power of decentralization comes from it's not from all the different sources it's actually from each other like you saw a malware that hit this industry you post that say this malware hit this industry at of this time you work in that industry so you're kind of like well cool I'll take that protect myself from it within hours minutes of it being released with me so far this is a pie in the sky dream and this is take a little bit of we have to like change our
thinking a little bit essentially what we're doing is we're using organizations as our own endpoints for each other we are creating imunity for each other what one sees the other sees but what's really cool about it is that you can sell that information and make money off of it which is really awesome we'll talk about that so what does this kind of look like so a financial bait guy hit with a spear fishing un what do we know about that you don't know anything about you could be like computer illiterate and know nothing I got hit by a spear fishing email you still know stuff you know what happened you have some attack metadata you know what industry you're
on you know what geographic plane you're in you know who it was targeting you know the systems that it was going after you can know these things just just run a entry just look at the you know the IP header whatever you go a step further you can see the initial access you can see the source email addresses you can see email headers you see where it came from you can see the network data I you know user agents you can see domains you can see the lateral movement who it went to after that you have droppers ioc's you have hash files file pass file names destination IPS command and control IPS and domains all those repositories that
it's pulling down to get new droppers or new payloads you can pull that together you can compile that together into what we call a product of some sort I love Json anybody not like Json oh Jon's amazing okay so timestamps titles this one is basically cold strike so just is an example you have the author who produced it so you can start searching on specific authors that you may or may not like may not you know and be like hey I really trust this author whatever they say is gold I'm going get it malware's you know Source was threat fox in this particular case there's a there's a reference to it hey it was on
a report this is where it came from you start seeing tags Cobalt strike all that stuff financial industry region USA Colorado all the indicators that it has you can easily dump that into a security tool right you can just use the API of that that system push it on in there there and now as soon as that hit the system as soon as that hit the chain essentially anybody who's looking for that type of thing any of these tags any of those regions any of those authors whatever criteria you want to have pull that down and immediately stick it in your security tool subscription model so this is the other side of the coin this is what we're looking
at so how do you perceive security do you need to perceive from every you need to be protected from every single imaginable threat that's out there I don't think so right or do you need to protect yourself from specific attacks specific types of uh events happening against your industry against your personnel against your applications I have a whole bunch of Apache systems any new Apache vulnerability or any new exploit that's in the wild witness that's attacking this what are the IPS that's coming from what are the URLs that's hitting that that's what I care about right so here's the use case you hear about a zero day I just kind of spoiled that one a little bit didn't I so uh you
have a zero day against Apache it is actively being exploited in the wild Pache is one of your applications wouldn't it be nice to have a daily hourly schedule that is looking for all new ioc's that is targeting that particular event that particular version that particular application and automatically pushing that into your security tool to ensure that you're not the next victim this is a fun one your CFO runs into your office losing their mind about an ad that they read an article you know so the latest ransomware campaign has took taken out a thousand businesses in your industry and you're like boss I got this I saw that earlier I already did a query I already pulled all of his ioc's
I know the malware that's going after I know the ioc's that's happening I already put them in my security tool and I'm also looking for new things that's happening we're we're cool you know that's gold for a security profession being W I got my job for another day at least right you know it's pretty nice now granted there's also the standard operation it's not this the the you know it's not the Silver Bullet for everything you're not save yourself from everything but you you can answer the questions when they need to be answered with the information that you need to be answered with and you're doing it from sources that you trust or if you may not know
them you know those authors or those particular sources that you're pulling this data from this is decentralized right so anybody could be giving this information do you trust the source do your friends trust that source does the industry in general trust that Source how many likes do that particular user have how many downloads do they have how many you know people are using that and talking about that stuff on Twitter you know you can start social engineering your you know your protection base these people talk about what I'm interested in these people talk about what I'm interested in this is data that I want it's been downloaded 100,000 times probably probably okay right start doing things like
that so but then also you can be the source of data you can be the protection for other people you got popped with ransomware yeah okay hopefully you don't lose hundreds of millions of dollars but you can take that intelligence and you could give it back all of a sudden your sock team could now potentially have an income you can actually bring in Revenue like I found this in my environment I sold it you don't have to give away any of your private information you can just say what region you're in what industry you're in you can say you can give yourself an anonymized Source I don't care you know whatever you want to do
somebody is going to say oh I'm in this region I'm in this industry I care about this ransomware I'm going to pull that down I want those C2 nodes I want those IPS I want those hash values of the latest dropper you know you can start selling to those people so you share the attacks that are targeting you you sell that information to others you share with the community it lifts others as it's lifting you we start creating a homogeneous ecosystem and then now you have a security team that can actually produce that profit how many people who security teams actually create stuff and sell stuff I mean do you sell stuff I want to
talk to you okay that's um but you know most people like give stuff away on GitHub right it's just kind like I found this really cool tool new tool here it is on GitHub you know go use it and it's like we're all like cool all right we'll build that into my whatever system I'm already running so a trust that's what that's what we're trying to do right we're trying to be a dedicated source for this idea of decentralized thinking of decentralized security I'm not going to try to sell you anything all I'm trying to do is we have an alpha tool we're Alpha Testing we have an API we have a UI that is doing this and if you want to
look at it if you want to all I'm asking for you is just to to bang on it and hit it and say hey this is doing what it what it's doing um let me you know and then shoot that information back to us via Discord it's usually what we're working on because we're kind of blockchaining blockchain people use Discord security people use slack whatever it's all the same stuff um so we're trying to create this this digital decentralized ecosystem talking about those things I have some time would you like to see a demo kind of how it
looks all right so look at this fancy fancy UI um So currently right now we've been up and we have my prototype up up and running for about 30 about three months-ish like super early this data is about 2 months old we're pulling about 53,000 uh products that big big test product that we're talking about um we have 235,000 indicators IP addresses hash values things like that okay hip toop categories tour just is a huge data feed so much tour um you know ENT malware beacons AP things like that um you know different author types uh you know open fish obviously one abuse CH you know D rad um there's essentially this kind of how it works so you can look at I'm just
going to take DB ra it opens it up does a search start searching live demos that's the Perpetual curse of live Dem it is it is awful Bill Gates's blue screen of
death it doeses want to do it hold on one second what's that the time frint maybe is no so it should pull stuff back good thought though again Alpha testers I'm building stuff this works when I'm like when I'm playing with it and I'm looking for indicators and I'm kind of like hey this is cool and awesome I love on CS um so yeah you can see from my URL right there that you want to copy that URL you go hit it okay but but it is locked down right now so now you can't hit it it it might not be I might oh this is why look at that go through my iPhone make sure that I have this
open try because I'm done five digits someone can guess it get into my home network that'd be fine still is not connected to my phone oh well maybe a mute point which would be sad there refresh I might just skip ahead not F nice see you again I need testers
Alpha seriously man promise something and there it goes all right so now we're
searching so right so um DV raw is a is basically a bot net that's out there just pulling down a whole bunch of stuff got a bad of Grandma's dude all right so we got demios we got some uh DC rat got some silver got some Quake bot showing up in there you got some cool things on the side here you can start doing some some additional queries like uh you know looking specifically for Amazon AES looking specifically for silver you know all those fun things start clicking on these things you start getting your ports and your IPS that you're interested in those particular particular pieces um you know stuff there's domains that go through
through these uh particular sets start investigating some of these you're like hey I like that one that one's pretty cool I really like quick bot yeah those are a lot of ports and a lot of ips I want to make sure I have those go ahead and select that and you can just go ahead let's export that let's look at that some some of that stuff when you export that we get this nice little Json blob uh that you can look at um you can use you can start uh you know really really messing with it and uh pulling that into your security tool what you're looking for um we do have we call it a trust agent we're
working with Splunk right now so all we can automatically select those things automatically adjust that into a search or an alert S A Splunk environment I think it's pretty pretty helpful other fun things that you can do here is can you go back so are you saying your the spun's coming to you or you're going to spunk going to Splunk so I have your you know obviously it's your Splunk it's not my Splunk so um you know when you're signing in uh to your environment you have your security tools that you're using you have your own API keys that you're using into that trust your trust agents not my trust agent has to know that um and it just configures
wherever you host your IPS wherever you host your domains and your hash values in your index you got to configure that index but then once you have that key set out anything that comes through here regardless of the source automatically gets dumped into your Security on an hourly basis minute basis as soon as it shows up once a day six six hours a day whatever you have correlation guides based on based on ID or event type yeah yep so so you have you like in the same way that you make that query whatever this query is so like you have authors tags publishes Industries regions you make that query and then your agent is looking for that query
pulling down that that data and dumping it into your to so um then we also have some beautiful truss truss API documentation get an idea of what truss does start using the API that we have so we've got some some data that we're actually already using here's some good queries you know you want to have you know indicators you know I want to see that IP address or one of these URLs or you know file name of ghost or you know whatever you're looking for um put that query into your API and you start start looking for it hold on so I'll show you see if this works more more trusty that's a backwards bracket so we'll fix
that I'm G to build it in here just because that's the way I want to do
it make sure that I have the right bracket make sure that I have double quotes on everything and I don't know I've never done this particular search so it might just completely fail we'll see I'm sure there's a faster way to make that happen but that's what we find
There You Go funny these particular addresses now we can do some really fun things like we can start seeing oh that looks like al5 that's scattered spider mled Libra you know you can start doing some cool things from a research perspective that's it's very helpful I I actually go to this for my day job just being like well do I have that yeah look at that I do you know so pretty nice stuff um but you start finding those those particular pieces muddled Libra skittled Network so that's it questions and the intelligence that you're feeding to an audit management system like spun I'm I'm say thatly you know but can can that inform your event event log
management uh dynamically instead of instead of having a sta list of auditable events that you're looking for in the system um can you dynamically say well I don't need to look at for that today because because the threat the the threat space is not not attacking that so if I understand your question correctly the data that I'm adjusting in can I not take action or take action on it or yeah can can can the can the the threat intelligence data that's being ingested into the tools just say tools dynamically inform those tools as to what they should should and should not be looking for so that I can reduce my cost yeah so I mean that depends on how your
Splunk is configured right so there's always going to be issues you you throw millions of alerts at Splunk you know to look for these things your Splunk bills you know it's going to go especially on the cloud service you're just going to go up so have to have some framework um thread Intel data like this right this is very time sensitive you look at the parid of pain and your ioc's IPS domains hash values even are super Emeral for a better lack of a better word right they're only alive for you know a few hours couple days a week you know so you want to know what your time frame is if something is six months old in your
environment and you're really focused on ioc detection you're not going to find you might find some good stuff with hash values you probably won't find anything good with an IP address you know stuff like that so it really depends on again what is your target set what are you worried about what are you worried about protecting against um and so our trust agent can go in and it can delete the alerts that it's put in there it can modify the alerts if it found a change to them uh it can just create new ones it can do a lot of things like that so so Mark about the monetization piece how do you you address maybe validation and D
duplication of these I's as they come in at scale yeah so um the the duplication aspect is is a little bit hard we haven't quite solved that piece yet um but when it comes to the submitter we know you know every submitter has an you know API key that is bound to that user so we can see everything that user has created um we are looking in really mirroring uh how blockchain proof of stake operations happen where you have validators that validate particular product sets before they get built into the block right so um having validators that actually validate data and say chice Waterhouse Cooper as an example I'm not saying they're on board I'm just
saying they could be an amazing example or they could be Auditors they could be like yeah this data is this is good solid scatter and spider data you know stamp of approvement you know and then you you as a person could look at that be like oh well this company or this person validated it I trust them I'll use that what they say is cool um when it comes to the monetization piece you have your submitters you have your buyers one thing I didn't show you um in here is when you sign in you're signing in with an actual wallet so blockchain wallet it's your wallet it's totally Central to you it's your own private key it's very large encryption
key you have to sign into it the data you have to you know you pay a monthly subscription for it um it comes out of your wallet any time that you have subscript subscri subscribers following you you get a monthly fee into your wallet goes into your wallet you can use that to to do what you want that's how we're planning on doing it right now it's more of like that social media aspect this user does a lot of really cool stuff I'll follow and like them I'll subscribe to their chain and then follow that data so along those same lines if you're automatically downloading thousands of products and ioc's yeah is there some kind of
automated feedback mechanisms or are you expecting users to go in and manually like upvote things that they like or if they download something and it causes a million false positives they have to go like download it yeah they would have to download it in that particular aspect um that one I mean these are awesome questions that's where a validator comes in you can be a validator again we want to create this model of in of incentivization right you are selling your product someone is going to buy that product someone who validates that product is going to take a portion of the selling cost of that product so if you validate a thousand things you know and you know
999 of them are awesome and only one causes a false positive more people are going to trust you as a validator if you just validate things like I just want the money you know we can slash you off the network and then you lose that that money that you you put into it so there's following the blockchain model if you're going to be a validator you have to buy in to be a validator you have skin in the game and if you suck at validating we're going to slash you and take your money to and now you can't validate [ __ ] anymore if you're a if you're a bad actor that's continually just posting garbage up
there we will stop you from being able to you know you have this many down votes you have this many terrible things in your environment no one's going to buy your stuff so you're going to take an economic hit anyway and then if you're just a malicious actor we'll just slash you off the train that's how we're we're planning on solving that problem so yeah so does it make sense am I thinking correctly here um I could stand up a network of honeypots and actually make money off of them right okay so it doesn't have to be like human generated I system the goal is how do we take this I mean now I'm thinking like
two years in the future um and and this is where I start to get really critical so now you have to like say okay now anything I say from here this point on you can't guarantee this truth because I'm just going to start rambling saying um I want I want this to be fully automated I want us to have like my company trust to have an AI behind it saying you're in this industry you're in this region this many people in your industry and the region said that this was bad do you want that you know and give you those prompts give you those things in the same time you have all these automated generated queries looking in your
environment I'm looking for patchy I'm looking for Tomcat I'm looking for you know VN you know VNC for whatever reason I'm you know just looking through all these things as soon as those things show up in the environment boom they're put into your your system I mean within minutes right of it being broadcast globally anywhere in the world you know it goes written to the chain you can see the chain it's a public thing you can go scrape the chain and look at all of it if you want to look at it right we actually found that this type of data is super small and we can write it to a chain without a large overhead
we create one megabyte blocks fully transferable we become an indexer of that and we just provide services find detections faster make it easier for you to use [ __ ] you know you can upload at API scale we can download at API scale you know like get this meantime to detection meantime to response like down to minutes right use stupid stupid like you know product terminology but uh yeah that's the goal right because we're seeing things faster 100 like Ransom more attacks in a week that are successful you know it's it's crazy all right that's it any other questions hit me up afterwards join me on Discord uh I have my contact information uh hit me up
on LinkedIn trust is on LinkedIn as well um I don't have it linked because I actually still have a day job um and it's not directly competitive I'm just trying to keep separation of of entity but this is how we can talk about security I think this is a very valid very easy is the wrong word it's it is a mind shift that we need to have as an industry and I think we can do it I think this is a solution that's pretty pretty awesome so there we go