BSidesPGH 2024 Track 1 John Dwyer Becoming Cybersecurity Bilingual to Build an Effective Dete
Show transcript [en]
thanks guys first allow me to congratulate you for staying in the room after a technical talk I was chatting with some of the people up front this uh this is a systemic problem in our industry is that we keep on deep diving into the technical world and we're not Reaching Across the aisle and we keep on finding ourselves in continued problems and I hope that you'll take a little bit from this and learn how you can be part of the solution right so I'm John DWI I'm the director of security research at binary uh defense I run this thing called AR Labs where we do adversarial research and then we try to build tools and capabilities to detect and respond
to those type of things there's all my uh Social Media stuff if you want to we put out like blogs and how-to videos If you want to get like into malware analysis I got a whole video series to take you through step by step on how you can kind of do that um I actually got started in my security career my buddy Toby's here we both worked uh when I was at school at Carnegie melon I worked at the SEI and then got exposed to C and then from there was a whirlwind I did research and development uh reverse engineering incident response consulting which was you know the hardest time of my life but I also learned a ton and
then I was building up threat hunting teams all over the world and through all that experience I learned you know two main things one I don't have all the answers there's like this weird Arc that you go through or at least I went through in uh your security career like first you start as this total Noob you don't know anything you're drinking from a fire hose and you're drowning and then you learn a little bit and then you go into what I like to call the the the black and white era where you have created all of these security Hills that you're willing to die on and then you as you learn more you learn you get to this
stage where you're like I don't have all the answers you've made a ton of mistakes and you know enough to know that you got a lot to learn right so everything I say there's always a different opinion and there's different ways to interpret that but I think that that is one of the main like things you can take away with this in terms of communication skills because what I see across the industry is that we have like the businesses over here and they do stuff and then you have security over here responding to what they do right and that is from a lack of communication across the business units what you can do in terms of your
career like not like this career advice is kind of ansary to like actually securing our organizations but from a career point of view attaining this skill has done remarkable things for me uh does anyone speak two languages in the room you speak two languages you can tell me that this is true if you are standing standing in between two groups that speak your two different languages it is your responsibility to communicate across the medium which they understand correct you also become the most important person in that conversation and then the success of that conversation comes down to your ability to communicate it is no different in cyber security if you want a seat at that table if you want to elevate your
career be involved in all these amazing things you you have to learn how to communicate across Technical and non-technical teams it also has the benefit of like making sure that your company doesn't get popped at the end of the day right so this is a win-win and I cannot recommend it this I'm on this like Rampage of doing talks about this right now and I'm like trying to gauge how many people actually stick around because I'm telling you I've been around the block more than a few times and we don't have enough people that have this bilingual skill and that's why we keep on finding ourselves in these holes right so here's what I don't think
everyone understands and I hope you guys appreciate my Eros tour memes here this may be a little inflammatory but I I actually do believe this but ransomware has done more for cyber security than probably anyone in this room and that's not to disparage anyone's work or like how smart you are or anything but but what ransomware did that we couldn't do was effectively communicate and quantify the risk based on a threat and what you see after that is a massive investment from ransomware right so they did it they did it because they went to the business people and they put them in their FA and says if you don't do X Y and Z you're
going to lose billions of dollars and we did it right we actually did it we made things actually better and people are having more Communications and security something that we talk about all the time now the bad news is ransomware was successful based on all the stuff we were talking about for the previous 15 to 20 years it didn't do anything different than what we were doing in the cting era does anyone work uh incident response in like 2010s yeah framework POS right Point of Sales system attacks stealing credit cards you guys remember when Target got popped Home Depot fun fact if you go and Google in 2014 the Sans Casino got taken down it
was politically motivated but if you look at the technical details of that same attack path as a ransomware attack in 2018 they took advantage of everything we were talking about admin rights domain admins logging on to workstations SMB open from our endpoints and they did it right but we all knew it was a problem we couldn't make the change in ransomware did it right so all of those actors in the cting era they just moved over to ransomware carried out the same attack and made tons and tons of money so we have to understand that this isn't a problem with them not caring or being too dumb or being noobs or any of that thing it's a problem that
we did not effectively communicate a problem and get Buy in right to do these kind of things to avoid it so like that's a hard truth we can't make that mistake again and we also can't waste this opportunity you know we are in a time of opportunity for security where we can actually quantify Risk by dollar amount and then actually they make change before I spent about seven years at IBM like I was at exforce doing research and uh we were able to calculate that the average cost of a data breach was a fantastic report comes out every year so it's now it's $4.5 million per breach right that's a great data point to bring up to your board and
your Executives right I can spend $250,000 on security we have now potentially saved $4.5 million right so this is where another Point hard truths hard truths we're going to go to I'm going to start with what we need to do to meet them halfway and then we're going to talk about how we communicate with Business Leaders when I go to companies all over the world and I ask them what is your detection and response strategy the first thing most people do is start naming tools they say we got this fancy whizbang EDR and the sore and the Sim and then we're always striving towards 100% miter attack coverage right guys like tools and a spreadsheet
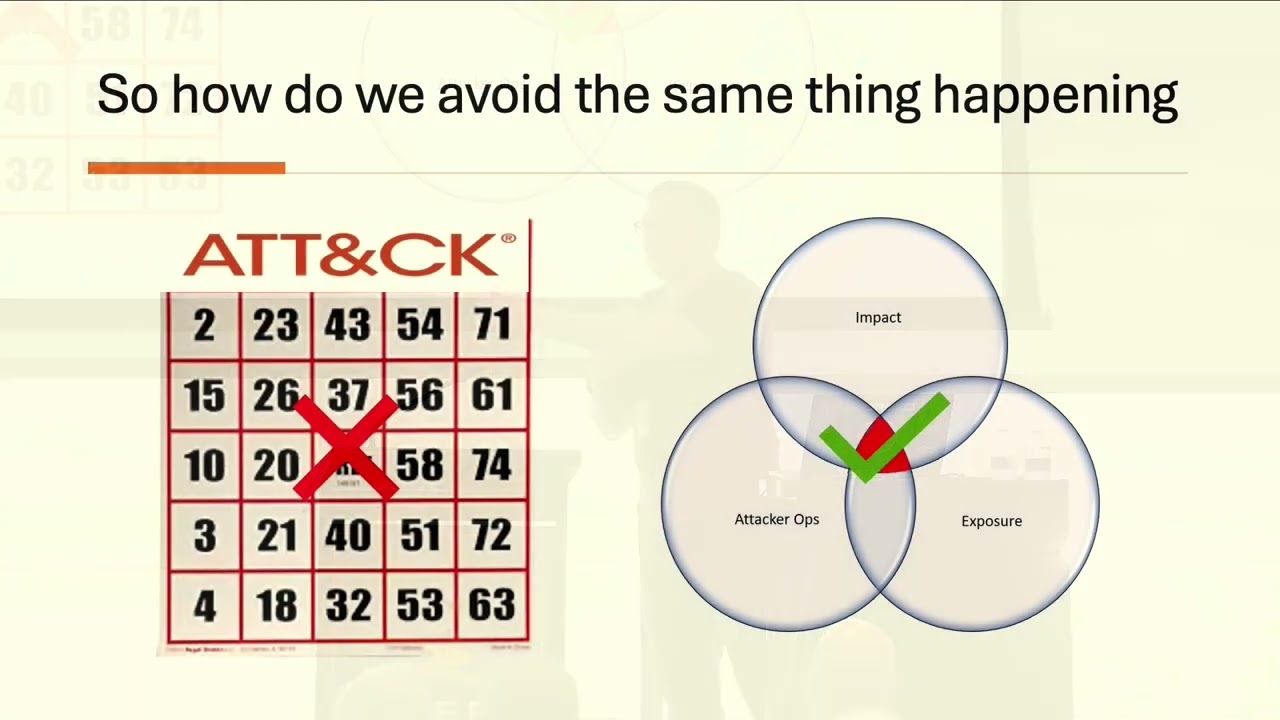
from miter is not a strategy those are components of a strategy but they're not a strategy and we end up playing this there's so many companies out there and I'm not I don't I'm not talking down anyone but this is like part of like we need to do a paradigm shift in our head about what strategic thinking is versus what implementation there's so many out there that they download their little Excel sheet and then they go and they're like we're going to make it green right they have the red yellow green stoplight chart on M your attack I have worked incidents in which they had a wicked green spreadsheet and they still got popped right so when you
do this what you do is you end up spinning circles because you end up creating detections that are really weak they have no context behind it you're triaging more of alerts and you have done nothing to demonstrate how you've reduced risk meanwhile if you take a look at this this is a very easy understand way to depict a strategy right we have our Vin diagram there of attacker oper operations impact and exposure and right in the middle there is everything that we're going to focus on this is the driving principle behind how we develop a detection and response strategy attack or operations we live in the time of commodity cyber crime most of these attacks are remarkably well
understood there's not a lot of innovation in terms of like how the attack happens after the fact there's Innovation and initial access vulnerability exploit and social engineering but there's not a lot of innovation after post exploitation right so we have a really good understanding of how attackers operate impact how bad is it if this attack happened this is how bad would it be can we tie that to a dollar cents can we tie that to a business line and exposure is what is the likelihood of that attack succeeding based on our controls that are in place it's not always maybe exposure is it see like I make mistakes Maybe exposure isn't the great word because immediately people
think about like RDP hanging out on the internet but it's say could be internal well how expose you to a particular threat if someone gets domain admin on your on your one of your boxes right what is my blast radius there now that's a strategy tangentially if you guys haven't seen me talk before we're going all over the map there's a better than good chance that I don't make it through all my slides and that's completely fine I've been using this analogy for a long time when you talk about like attacker operations and where this can you be used also strategize whose roles and responsibilities are but for your detection and response strategy like where do your service providers fit
in you guys ever been to Chicago and seen the bean you know the big reflective Bean all right I'm going to try this metaphor again it has not landed before but I think I got a new way to because I do think it's a good way to interpret the threat landscape so if you are standing at any point on by the bean what you see in the reflection is different I could be standing three feet away from you what I see in that bean is manifested differently I still see the same stuff some buildings are bigger some trees are smaller depending on where I'm standing the threat landscape would be like your third party they what we what we have is a great
unique Insight in which we can look across all Industries all companies and tell you what's behind you right on the landscape okay so you have your provider here they have a purview across many different spaces and they can tell you what's behind you but there's no third-party person I can't come into your network and tell you more about your network right that is where your spe specialty if you're doing internal security I should say no one's going to tell you that's really where your value is your value is that you can perceive the threat landscape based on your perspective on the bean and that is your slice of the threat landscape everyone is just a little bit different
everyone's got different stuff different configurations different things that are important and you need to be able to understand your slice of it to properly Implement something like this right and that's a strategy right so we're going to try to interpret the threat landscape based on the data that we get on how it applies to us here's an example of how we could use this framework the mft stuff uh hopefully none of your organizations got popped by it that sucked here's the thing though was like no one was talking about mfts before they got popped all over the place you know like I knew that they were a thing but it wasn't like we were sitting here
saying here's your crown jewel your mft right we knew what they were they knew that people had them but it was like we all took one on the chin whenever they whenever that uh zero dat came out and they ran off to the also another tangent guys if you uh we have a problem with uh misclassifying these types of attacks as ransomware versus Data Theft like they're both extortion based attacks this one was attributed to Klo who has done ransomware but there was no ransomware in move it so we have to think that as a data theft and that's an important data point whenever you read stuff and interpret it when you're building stats about what's most likely
to happen Data Theft not rans okay so let's take our strategy here and say attack or Ops right so Data Theft ransomware attacker these are generally the steps okay they don't all have to occur in this order they don't all need to be there but this is generally the attacker operation for ransomware and data theft and everything hasn't really changed since 2018 guys so like if you think about what mft does is it allows them to skip all the way to there and extract data right so this fits right in line with their operations we should have known about it why didn't we know about that why weren't everyone thinking about it if we think about
impact if you know what the type of data that mfts usually have in them they are designed to communicate across many different businesses a lot of people use it to handle sales orders accounts payable manufacturing uses it to make sure to distribute orders go to different places a lot of account information and financial records or transaction through mft that was the whole point of mfts before mfts Doug you remember this people used to spin up FTP servers everywhere and they were totally unmanaged and they were just hanging out there and then the mft market spun up and they're like no no we're going to take all that stuff condense them down into a single Enterprise solution now we have mfts
which is good this is this is actually good right but we never this wasn't ever bubbled up to like a cyber key terrain piece and if you think about the exposure piece is that they're designed to hang out on the internet right so they are designed to be exposed because they're supposed to do communication between three different companies now if we take our strategy there this bubbles to the top right if we use attack and we're just chasing down the stuff that we have on Twitter we're probably not going to care about mfts we're probably not going to highlight it and that's probably what happened you know I wasn't paying attention to it I'll own that I wasn't
sitting out there and telling everyone to secure their mfts or watch their mfts is because we weren't thinking properly about how to really contextualize the threat landscape in terms of like what's important to the attackers and what do they consider success we'll talk more about about that in a little bit so what can you get from attacker operations if you go back and you look at all the mass exploitation events that we've gone through over the last five or six years proxy shell proxy log on log for J any of them mft or the move it one and then I think this one yeah that's a netscaler one so that was a netscaler Gateway came out the
vulnerability Chang the exploit changed the technique in which they implemented that exploit changed but what the attacker did after did not change they do the same I almost a swore same stuff you guys is they put a webshell they steal data they create an account they La they launch some living off the land post exploitation command at Papa shell like that's what they do every single time so why are we waiting for zero day to come out and instead why aren't we saying I want a detection every time a script file is written to the web enabled directory I want to look for that web enabled process spawning a command interpreter right so w3wp.exe if
it spawns CMD Powershell wiimi rundll32 you would have caught move it right you would have caught the unau authenticated bypass right so why why are we waiting for this stuff to happen and it's because we aren't properly designing a strategy that and we have to design a strategy before we can communicate to business before the business invests in security oh final point I'm almost skip this this probably the most important part so the techniques change and they do change often but goals and the objectives don't right if you think back to like those don't change all that often and that's the stuff we should be looking for when attackers change their goals and the objectives that's where we
see Monumental shift in the threat landscape ransomware that was a shift in an objective they shift from stealing credit card data to trying to do operational disruption you know the initial access Brokers used to be banking Trojans they shift their goal and objective to providing access to ransomware operators and the whole world burned to the ground right so instead of like we can always use the attacker goals and objectives to be our driving light to our detection and and response strategy um and also like think about how many you guys get asked questions about what AI is going to do like how are attackers going to use AI right and everyone talk what's the first thing
everyone says attackers are going to use AI to do what I think we just heard it in the last talk actually fishing write emails okay let's let's just if they using you know the Terminator to write a fishing email did the goals in objectives change no so our strategy doesn't change our scale changes but bad news guys we've already been in the in the era of fishing scale for 10 years billions and billions and billions of more fishing emails are sent every year over year so we're that's our reality already so don't like when you have that in your back pocket they say like I don't care if a computer wrote a fishing email or a
human wrote a fishing email still a fishing email email it doesn't bypass the rest of your detection and response strategy because we can go back to our attacker operations and say okay they write the best fishing email on Earth everyone clicks on it they pop a shell okay we still know how to detect that they still have to go through the rest of those stages so our strategy Remains the Same and so I'm not going to waste time worrying about Terminator writing emails right if you don't have this you know buttoned up and you can't argue it or or talk to a business leader about it you're going to get sent down a rabbit hole that's going to take you
away from stuff that actually matters so that sorry another tangent but I get asked about AI all the time so like just saying like when you use this we can take the whole 98% of the threat landscape and boil it down to this really if we use the goals and the objectives of criminals to Define our strategies basically this most of the time it's like this covers quite a bit and the good news is is if you get buttoned up on these it actually mitigates a lot of other threats this is something you could take to a non-technical person and describe the threat landcape you take a miter attack dump and you show it to a chairman of the
board you might as well be speak speaking cling on they're never going to get it they're going to turn off disengage and then you get in that environment where it's like that's Security's problem and then the only time that you get to talk to them when something bad happens and that's not where we want to be you want a seat at the table you get a seat at the table by being able to communicate this effectively and saying all those technical stuff you read on Twitter all that kind of stuff okay where does that fall into the goals and the objectives of the threat landscape do I need to amend this do I need to change this are
they still trying to extort me they still trying to commit Financial fraud are still trying to steal our resources to mind Bitcoin okay does that make sense okay this is the Goss model though you guys know that goals objectives strategy and tactics if you guys uh ever come across this if not you really should because business people know this business people understand goals objectives strategies and tactics if you can communicate on this language they'll be able to they'll be able to understand understand what you're saying and that moves you in the right direction to being able to have an effective communication and get investment get head count get all the stuff that you need right okay well that's just half the
story right why we need Business Leaders in this we try to do that alone you're going to fail you know unless you are in those meetings making strategic decisions of what your company's doing and you try to measure impact on your own it's not going to go well right you need the Business Leaders to tell you what we're what they're trying to do in the next 3 five 10 years what strategic moves they're trying to take the business for you to be able to measure impact with that information now you can calculate and quantify what percentage of risk you have and that's the that's the conversation that they want to have we when I see stuff like
this I can't help but think that there was a communication break down anyone tried to buy a car while cdk was count down did you guys hear about that it's pretty bad right it was a single point of failure one application controlled the ability for thousands and thousands of dealerships to actually sell cars there was a single point of failure change Healthcare same thing Henry shine same thing we already talked about move it a little bit when this stuff happens that means that I can't help but think that there was a communication breakdown where there wasn't a you know a useful conversation about how we're architecting something based on what we know adversaries are doing because I can tell you this right
now while ransomware and extortion based thread actors aren't really changing their tactics the one thing that they are getting a lot better at is being able to identify levers of pressure within your organization for many many many years we used to track F like fins serve Financial Services is the number one quote unquote targeted don't kill me for using that word but impacted industry and then it excuse me switched over to manufacturing whenever extortion based attacks really took hold right anyone work in like uh manufacturing OT oil and gas or anything like that yeah oh we we've already T hey man it's good to see you yeah uh so we've already talked about this before but there's not and
he'll you can he'll affirm me here there's not a line manager on Earth that doesn't know down to the second how much money a company will lose if that line stops right that is a huge element of pressure that that takes it down to do I pay a ransom or do I do I don't to a financial based decision and that's what they want to get it to right so we have to preemptively identify those elements of pressure so that we can properly be able to detect contain and respond to it right does that make sense we need them like we need the business people you're never going to know what the business people are doing what they're investing
in unless you talk to them and you got to talk to them the right way take this for example so here is a gos model for a real estate company that I a AKA chat GPT wrote um and what they're trying to do is they're trying to break gain market share by going after Young buyers by doing an all online thing right they're going to do everything online you be able to do all of your business document transactions buy your house sell your house through an online system okay now I've been in many many meetings here where the first thing that security person says whenever they say they're going to do you know online digital
document management they're going to do transactions online that may require email right because it's what third party of you guys buy a house like stuff happens over emails not everyone's going to be a member of your portal you're going to email stuff back and forth a lot of the time security people the first thing they say is we can't do that we won't do that right we won't do that because of the risk now we imagine what happens then the company is going to shut you out you they're doing that because they look and they're like this is our financial future we have 60 70 million and you like well I tried and then you throw your hands up and then
don't like these idiots don't know anything about security that happens it happens a lot I've seen it so many times think about how much different that conversation happens if you look at one of the objectives there stop it says build trust with potential buyers right think about how different that conversation says I notice that one of your objectives is to build trust imagine how we could highlight that as a market separator if we Implement X Y and Z as part of our detection strategy now we can say that this is something that we do that our competitors don't and now we're aligned with what the business wants to do you still get to do your security stuff but now you have Buy
in because you're tying it to how the company can actually obtain their objectives that's a whole different conversation and that's really what we need to get to when you do that you will get buying because you're try you're now you become part of the the solution to them achieving their goal make more money business people love money we love money too though because like that's going to get investment it's going to head count you know how many you guys you guys how many of you guys work internal security how many people do you wish you could hire like you have you don't have enough headcount no one no one does right no one does and that's because
we're not tying ourselves to money instead we're saying you know everyone's always heard that that thing about like oh security is just a cost center you know you're just a drain on it you can flip that and say this is a market separator for us we do X Y and Z right we highlight this we we bubble security to the front of it and we have our security people out there talking at conferences about all the cool stuff that you guys are doing right you're doing all these implementations that directly align with the threat landscape you're pushing the envelope you're on the bleeding edge of Technology your name gets out there and now you drive
more business to the company that's a lot cooler than just saying I tried like this is what I'm talking about guys and and and uh I don't know if I'm going to be successful on this push to try to change the mindset of security people because we don't like to be told what to do I'm not telling you what to do I'm just saying that this this does work like I've I've done this I've sat on the table with a lot of boards after an incident and really been able to talk through how to incorporate their security team into their strategy to now tie it to revenue right and that's what we really need to do and that's what being
bilingual is all about is being able to understand this and say you know first you got to talk to them and be nice you know and then you get a seat at the table where you get to see this kind of stuff and now you can go through there and you can kind of highlight some of the things that would be you know what are some of the stuff that aligns with the threat landscape well we see email in there we see a SAS application okay that aligns with maybe some cryptojacking and some business email compromise we'll have private data so we got to be concerned about data theft and database extortion you know if we're
going all SASS and maybe we put rant somewhere at the bottom because it's still remains a highly window Centric sort of attack okay so now we have a little bit of a triage and now I can provide some some insight into where I can strategically have a conversation about how we can help them be better at achieving this goal it's even better when you can quantify it so in 2016 17 there's this Austrian company fac and this is this little box here is the stock price after they had that be attack then the CEO and the CFO both got fired you're talking about quantifying a risk to a business leader this is the kind of stuff it's not the boogeyman you
know it's like if you don't do this all this you know the world's going to collapse and we're going to be out of jobs this is that's a conversation you can have let me tie a dollar amount to it let me tie to someone's job now that's a good one it's even better when you find it in the business vertical a lot of these examples are out there and being able to have this and bring this to say this is our strategy this is why we need to do it and let me let me assign a dollar amount to that in terms of a risk calculation and this is what we can do to help you gain market share
if we do X Y and Z because you will gain trust you congratulations you just became bilingual right you're talking in a manner in which they have you're presenting it and easy to understand we don't need to I haven't mentioned really anything technical yet you guys all understand what I'm trying to say right and you guys are all technical PE anyone not technical in here oh you bunch of nerds I would really love if there was like a CEO in here who never like touched computer before i' be like oh that makes sense I would have been I should have planted one um next time okay so how does this actually how can we present this in a
way in which we can now prioritize together with our business teams right so I've already talked this together we can tie and impact the supporting technology behind it and this is the last piece to it anyone in the uh if you were in the military before you guys ever heard the term Mission mapping so Mission mapping for those who don't know is if you have a mission and you map it down to the people processes and Technologies in which that support that for you to obtain your mission right this is a hard this is not easy to do but if it's part of your detection and response strategy and you get buying from your company you'll find that
you'll get investment to start doing that so if I got to think about how do I align a threat to a Target technology what is the out outcome of this happening and I've definitely boiled this down way simpler than it actually is so don't crucify me but you can take this exercise out and start mapping this to Technologies and processes that enable that attack to be successful remember goals and objectives and then tie that to the technology that that supports the goals and the objectives of the business and now we have a direct onetoone relationship between that you show that right that's a productive conversation he like well we don't need to do everything right because no one's
ever going to have everything everyone's working within budgets and what the last thing you want to do as a security person is waste money right because you never get that money back budgets only go down if you can't properly articulate what we're going to talk about at the end so we tied this down and we like okay we can do this huh here's our strategy mapped out in a very easy to understand quad chart that business people understand if we take those supporting technologies that we just talked about I threw a couple different examples in there we have our goals and the objectives based on the threat landscape we have our impact and exposure and in the pop top right we can
bubble Technologies to the the top my man you go you can have this conversation with someone and they'll be like okay top right I get that I get a quad chart we're prioritizing this and it's Justified based on risk to the business and the the risk from the threat okay what do you need to do to do that right let's say they choose becc I wouldn't hate them for that I think that's not a bad thing and this is where this is where we can miter out you guys we can get into the tactics you know I'm 40 something minutes here and this is the first time I'm showing something technical really is now we can start tying this to
we can start saying okay now how do we Implement our security strategy go ahead use miter knock yourself out I think it's great it's probably one of the best security products the last 10 years but we got to know how to use it right we can't play miter attack Bingo we have to use it what it's supposed to do and that's bring context to an attack or operation right so I don't need to know every single command living off the land tool or command interpreter out there I just say t1028 right and now I know what that is and now have some context behind what our detection is for whatever it is that we're doing that's the right way to do
it in my opinion because I like I said I've been wrong more times than probably anyone in this room but that's my opinion on how to properly use it and this actually makes sense and fits into our overall strategy and finally what this does if you do something like this how much more secure are we the Golden Goose of metrics that people have been asking right if you it's really hard to do unless if you everyone if you've been scrolling Tik Tok for the last 40 minutes stop for stop for 30 seconds and pay attention to this this is massively important without a defined threat there is no meaningful security metric that you can derive
otherwise you're just grasping at straws you must Define a specific threat to develop a meaningful metric to answer that question right please understand that I've been I've been talking to people for so many years about that where they get asked this question about well how much more secure are we can you tell us how much more secure we for from what from asteroids from ninjas like what are we talking about here you got to know what relevant to you and then you could measure how much how much more secure are you what is our level of risk based on our exposure and how the attackers operate right all I'm saying guys is like this is I'm not
saying I have it all figured out but what I'm saying is is that the stakes are far too high for us to just sit in the corner and complain about the business not caring about security is that we can actually move the needle in terms of reduction of risk you know this cyber kinetic line that we have right now is becoming more and more gray I uh you guys remember like uh when we didn't have any toilet paper during the pandemic day yeah um what people don't realize is like during that time the adversaries were hyper aware of a how fragile our supply chain was and we responded to so many attacks in the trucking industry during
that time like you don't even know how close everyone was to not having gr like not having food at your grocery stores right so the stakes are far too high for us to not take the five hours it is a week to have a meaningful conversation with the business business because we that that's not their job right like we always the the thing that kind of like pisses me off is that like whenever people talk about like Suzie and accounting clicked on a fishing email like what an idiot like incur is a shared responsibility well you know we have a responsibility too in security we have a responsibility to the business and we know that that has a direct
impact on people's day-to-day lives so like we have to be able to meet people halfway you know get off our high horse and start having meaningful conversations in a way that everyone can understand so people like we don't have to have those issues I can tell like it's it's crazy man like like the the amount of incidents that I've worked where was like minutes like minutes away from a hospital going down minutes away from like ambulances not being able to get sent out like we it we can't do this anymore right and we have to like please even if you don't take this model and you think I'm an idiot that's totally fine most people
do just take away that you need to make an attempt to do something like this because we really need to like security is part of our life and we're all intertwined on this this digital ecosystem whether we like it or not and if we don't do this we're going to make the same mistakes and they're going to figure out a new ransomware way for us for the world to burn to the ground that's all I had for you um I can take questions if you have any um otherwise I can give you another example of why tools necessarily aren't a why we we may be going down the path again we'll be just yeah please so I come from an environment
that uh sometimes it's difficult to get by it because maybe you've already burnt that bridge you know what I'm saying so how do you repair that was just like I mean this is the people part you know the people behind the technology are the most important piece right like it it is the people behind it so how do you go about repairing it depending on the situation I don't know I mean like I'm not a mental health professional but I think like owning up to it like there's the the expression extending an olive branch is persisted for thousands of yours for how many reasons maybe you just go out bring them bring them a coffee or something like
that and just you know shoot the [ __ ] for a few minutes and just say hey you want to hear something cool and then have that open dialogue a little bit about security I don't know how you go about repairing information but I definitely know that talking down to them is not the way bringing something down to say hey I thought this was really interesting that you might be uh interested in Shameless plug on Tuesday I'm releasing uh a Blog on this piece of malware that I just got done tearing apart this one is called uh Ultra killer you could use this if you have a bad relationship use this let me know slide
it in my DMs on uh LinkedIn or Twitter and let me know how it goes use this and just say so this piece of malware is able to obtain kernel level permissions through a vulnerable driver and it basic goes through and enumerates all of your endpoint security tools and kills all the processes right and then it sets up a back door dumps credentials does this stuff and everyone's in the blind works against Defender sun1 crowd strike and semantic antivirus use that and talk talk to them about why you need a detection strategy and align it with the goals and objectives uh example I have and let me know how that goes hey John I appreciate this
conversation good to see you and uh I was very ineffective at this early in my career which is why this resonates with me a lot because because I had a hard time justifying security spend in these scenarios I'm now on the other side of the table and helping cesos do the same thing with their boards uh on the insurance side right one of the things that I've run into recently with uh with cisos is that they've gotten into the habit now of saying I don't want to do fishing testing because we know everybody falls for fishing and instead we focus on the controls now the insurance markets aren't quite you know hyped to that right now they still want
to do fishing testing just curious from your own perspective have you felt much because you mentioned this just a few slides ago that instead of worrying about you know this you know John from accounting clicking on a fishing link that rather we focus on having all the appropriate detections and defense and depth to prevent it rather than focusing on like we need to fix the point of entry as opposed to we need to fix it when we notice that something bad is actually happening are you asking whether or not fishing tests are still valuable nowadays yeah in terms of are you seeing a shift in the IND uh yes I am I'm I I do think that
most fishing tests are to check a box at now Point um I would like to see and I do see this happening in some of the more mature organizations where uh it turns into an objective based test that involves a fish and then use it as a as a mechanism to highlight someone doing good so instead of focusing on on the click rate they focus on the report rate and they're like okay people are going to click we got it we've known that we've known that forever how many people are going to report it we don't know okay well how many people report it and if they report it they get a $10 gift card to Starbucks or we give them a
shout out right I think that that I have seen that happen I do think that that works really really well and it's a good message to higher ups of like how we're turning all of our people into s anwers Doug yeah I think along the same lines the insurance companies are behind the Regulatory Compliance things are all behind and we're doing checkboxes like resetting passwords if you got a good MFA you know having an expiring password isn't really necessary anymore and but every insurance company in the world says you have to expire at every regulatory i i how do we help them and this is a again a long your topic here how do we communicate with insurance
companies and The Regulators oh douge great question and I didn't even plant this on him um I'll take the 50 bucks how many business deals or how much conversation or how much can you would influence policy and Industry across Executives through your executive a ton right and if you arm your CEO who's golfing with the CEO of a Bob's insurance I'm not going to to say an actual insurance provider name but like Bob's Insurance you just say hey you know what like things are kind of changing you know and you're asking us if I if I'm passwordless why do I have to Res reset passwords right to to get approved for this use UB ke or use a UB
key or something along those lines you use your Executives as a Communication channel to influence policy I mean like especially in the United States like there's a direct line between the higher levels of business and the government and in the insurance industry and everything will across that line right if you have $0 billion you say well you know what I'm going to go with Jeff's Insurance because they don't make me do that I bet you Bob's Insurance quickly changes their policy but we got to get the we got to get our Executives on board first this was a great talk um are you going to be around for more questions I'm here all day awesome um there are
cookies in the food area in the event center so we want to get cookies give it up one more time for John and I'll say one thing I learned a lot because although this happened in 1997 when I stood up in my first ever meeting with a CEO and the president of a company and I I was the security director and H I I said because we were working on this project and I i' had been there for all of a month and they wouldn't even listen to me and I stood up and I went you're both [ __ ] morons and I walked out of the room so that's an example of not how to do
it so yes I learned





