Writing Our Own DNS Tunneling Protocol, And Other AWS Misadventures, All In A Pen Test
Show transcript [en]
uh thank you everyone for coming um so it's tough to do 3pm talks uh it's afteron everybody have a boo or lunch but I promise you you're going to learn very little but have a lot of fun in my talk so who am I first right I'm a re jum uh with them since um21 used to uh deal with kids at a pan before cber actually um couple of times then we can talk about the past life um I like s ja and Ma Rock if you like those you're a cool person uh if you don't you're cool as well um I Heard meth rocks so um just chill uh for those who who is coming in I'm going to repeat the
disclaimer that you're going to learn very little but have a lot of fun it's a war story of uh P test uh which I usually don't get but U for when I do I have a bit of fun um CLE twist in turn chill and listen uh also thank you for the unnamed client who allowed me to uh talk about this on stage uh I retested uh the app on Monday and they patch everything un so yeah let's go uh also uh for the chill part last time I give it talk at bizes it was a rting talk about you know how to hack into Microsoft V65 is super try hard about you know what I do dayto day it
was reptin and it was very stressful because you tend to attract the most try hard crowd so you want to absolutely nail the tank and everything so but this time it's all chill chill out right so the app itself um it's built by uh people who used do rocket engineering Aerospace stuff and they were feeling you know uh requirement management is a lot of work apparently like how big the nozo is and you design the flow and everything after you know fits and pieces of numbers and if you tweet one number it changes everything else and you need to redo the modeling again so they sort of have this integrated pipeline thing that manage the
requirements for you know their scientific application and recently is you know couple of two three years ago I've been seeing more more and more of you know the app developers trying to push some sort of python sandbox in their application which is very good news for us or for me at least but um for the scientific types they tend to not sandbox their python features very well and this is one of the examples so U apparently for this very application that I'm talking about uh the users can link their own GitHub repos uh and whatever py script does in the repo can can be you know executed on the app itself I'm like in okay so you know B more background um
users can subete ithon and perform calculation simulation all that good stuff uh the UI or like the the endpoint only would return any numeric results like if you have three um variables at the end called V one W 2 w three and like they they come back as one two and three and they open display on the UI nicely like there like code and the value is so and so forth but if you have a variable that is called like um V4 equals some string then V for will be dropped by the app for example if you define a variable like I'm hacker and you will be draw by the application itself right so so to a hammer every
elongated object is a nail uh so if I see a common you know language interpret you no JS Ty PHP you know it's h you know Shelly time right so talk about the Shelly uh typically in app test getting to the YC is the hard part but in these sort of like Hy and S boxes it's actually quite rather straightforward if you do um pantastic aback or even if you are a programmer you would have you know some sort of favorite way to pass oh commands Into The Interpreter for example for me I love using A.P open because you type the least number of characters but you can use a process. run sub process. de
openen you know something similar right so now that the problem at hand is the app itself uh would only output you know uh numbers right number type no strings so I uh import OS and then I do a PE open Echo a number and then put the standard output as an integer and then you get you know voila output equals you know the number you've ACC so well at this point I I mean okay it's RCA technically but am I comfortable slapping a critical you know label calling a day you know get with friends I sort of want to do more when you could you know get these you know sort of juy bugs right in the
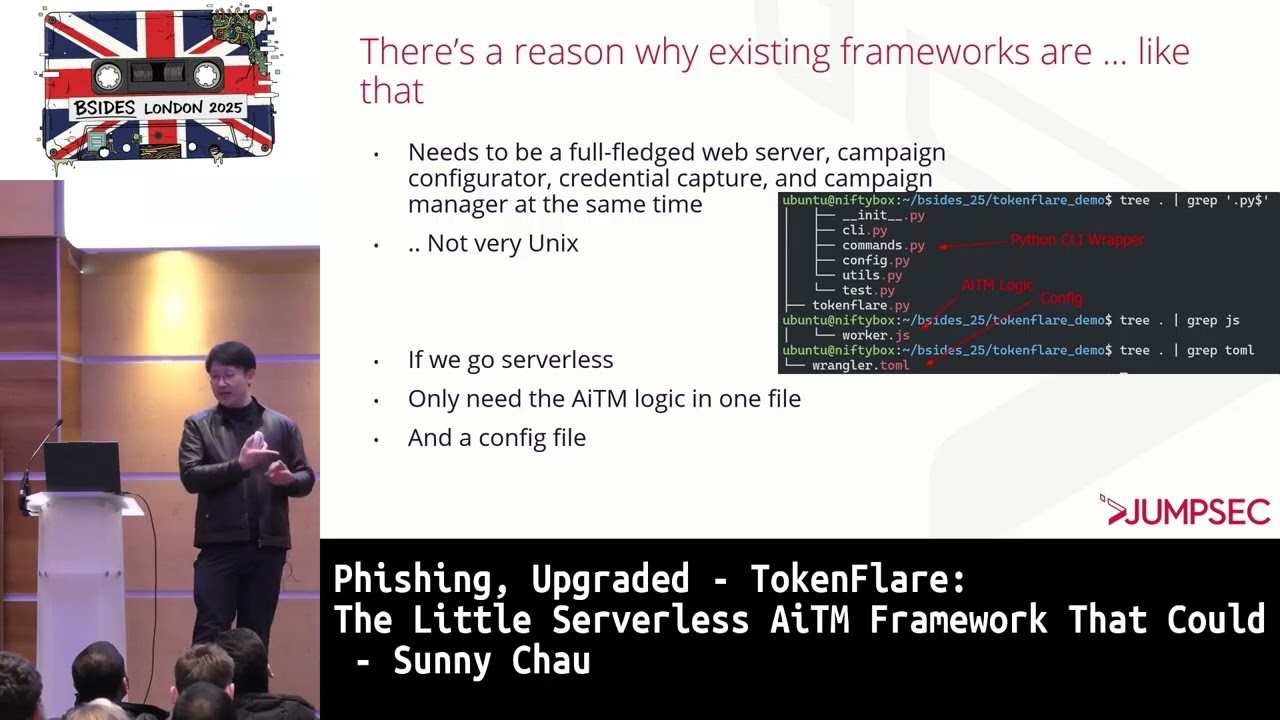
in the in the app so the first instead of encoding that I want to do or what I what I want to actually overcome is the you know integer to strength uh sort of problem right essentially an interactive or semi interactive shell is uh take command in in form of a strin variable length and then some sort of like data out the data would be in asky right so the app as said with draw nonumber outputs uh but within the UI you can't just use drain for example if I do OSP open um a command and read it directly would you know discard the output so what do I do right um so you need some
sort of like first bit of encoding no pun right strength of number encoding in um High run time which means you know 99.99% is UNIX right you you don't want to you know do Windows server and then do it you know p% box on Windows bless you if you want to uh so if you do pipon you don't you wouldn't possibly need to you know um handle like uni or something like that like 99.99% you're dealing with SK alone right so number and S key so ah SK table to rescue right so uh those who are not too familiar with it um you can represent each character in an asky table as a integer right from zero to
255 or you know in HEX um 0x00 to 0x FF okay uh so a number of them are not principle but you know the principal ones are all you know within this you know integer space that is um uh 02 255 okay so what I first fit first did which is complete Jank I I I warn you is to you know con all the integer representation of the characters into a uh you know very long integer for example a which would be decimal 65 uh B would be decimal 66 you might ask like the programmers here might ask why don't you just do hacks right so so they could all be like two characters uh but then the
application you know sadly only does you know decimal it doesn't do Hex doesn't do you know that stuff so I have to uh content be content with you know threee uh de uh three spaces or like like from 00 to 255 right and then um again the zero at the front would not be displayed because number don't naturally start zero they in the natural form you can c a zero and then you know top it up in you know three oh too quick top it up in sort of like two figures right so the the code value here is actually the output fori uh you can see like 115 is s 098 is B uh 120 is T so and so forth right so
cool I could get strengths out right so uh when you see you know s spxu _ u something um the bit of um Googling I found you know it's actually the runtime users for a a Lambda so a Lambda for those who not too familiar is actually a Ser function um uh sort of implementation for you know AWS right it's not actually the main application itself it's sort of like a side thing like API that it calls but anyway proping and side API is good as well so uh you do like a the screenshot below is not from my test just whole thing some somebody's um lock po if you do an uh like an ID on on Lambda you you see
your sdx user and then number number number number like there are hundreds of each SPX users in the Lambda nely right so the front end um sadly only would uh return 20 significant figures of U of A number of the output so when you look it up on you know sort of python uh standard specification the Max Max uh of type in is this number which is like 20 digits and you divide it by three which is you know each character I need you would actually need um like only each cycle of importing a script running the script decoding it you get you're going to get you know Sixx character out so it's sort of
inefficient maybe try harder maybe uh you know uh getting one cycle um right one one cycle for six btes I would be looking at like sort of the the round of 100 bytes per minute which uh you know defies my expectation as an attacker for you know good user experience so I had to try hard out of course so um when sort of Life closes one door look hard for your native networking capabilities so are there any sort of our our band channels can can I do HTTP and can I do DNS for I've forgot to mention the um app I later found out that the the python sandbox actually supports all of the Python standard
Library so whatever is in standard lip uh it's all good you could pull you know sockets you could P HTTP and you know the other you know s light goodies so as SP of a listener on webite collaborator listening on you know hcp and DNS and the little you know um do a URL open on you know my my subdomain on um B so so then it turned out that um the app actually interacted with the DNS but uh HTTP was no go for some reason I didn't know yet why then I something got all my you know neuron ju running at that moment I could pop something potentially here then the four that uh
for those who are not too familiar with how one you know steals data from DNS uh been talking to some uh good BLS here regarding how they use Tex records but here I use a records instead right uh basically you can think of uh the vulnerable app making a request uh to qu resolve like juicy data do you know attacker control domain.com and you know my name server uh which resolves that would you know get the juicy data in the query uh save the juice data in the query log and then you know feed the application some garbage data and you know off so so basically um to PC you know that I could get some St out right I did
a little bit of um uh two bits sorry for two thoughts I chop it up for the block to moove the Sens bits basically the first first thing was a Pyon strength um literal and the second URL would be you know this Echo some uh copy T some strength and I do two lock ups to you know [Music] sockets sorry I I will talk about it later okay this bit is uh yeah is just to BC that in the beginning right so so that that's why I did not run like stuff like who am I or like you know C the ET Chanel or whatever to bir right so okay I could do the echo I could do the string literal
um you know po as you said got my data and and sent it to me okay and then well if it ended here it was you know a good critical finding I I have RC I have you know strin out I have you know ex extran DNS interaction the client should be happy but I'm not happy because I still don't have a good user experience yet because when you if you use um bir a lot you know is Java and Java on Linux is very Jun and you you cannot easily you know script that unless you write your own extension you copy and paste is a lot of struggle and TCH is small and I
don't like it I I want more right so yeah so when I you know try to also when when I try to you know read more data through this pipe I get a strange you know sort of uh encod errors uni code error label empty of too long what the heck was that right so I did what a you know normal person do I Google that um copy that error and Google it and turns out um turns out some guy on um stack exchange asked the same thing before his program he write his own you know sort of uh uh web application and stuff and the first sub doain is too long and then uh uh you know pyen through this in
strange era so some guy who has who who had rtfm before uh told him that um the first subdomain cannot exceed um cannot be equal or longer than 64 bytes uh that would will be rejected by the DNS protocol and so uh during the test I just took it as okay I'll make it less than 60 and went through but afterwards to prepare for the talk I actually you know read the read the sort of RFC to see that I I myself rtfm and actually that person was wrong it's not 64 it's actually 63 it's super pretended by pring on stage um anyway so the uh the RFC rcf3 says the labels must start the
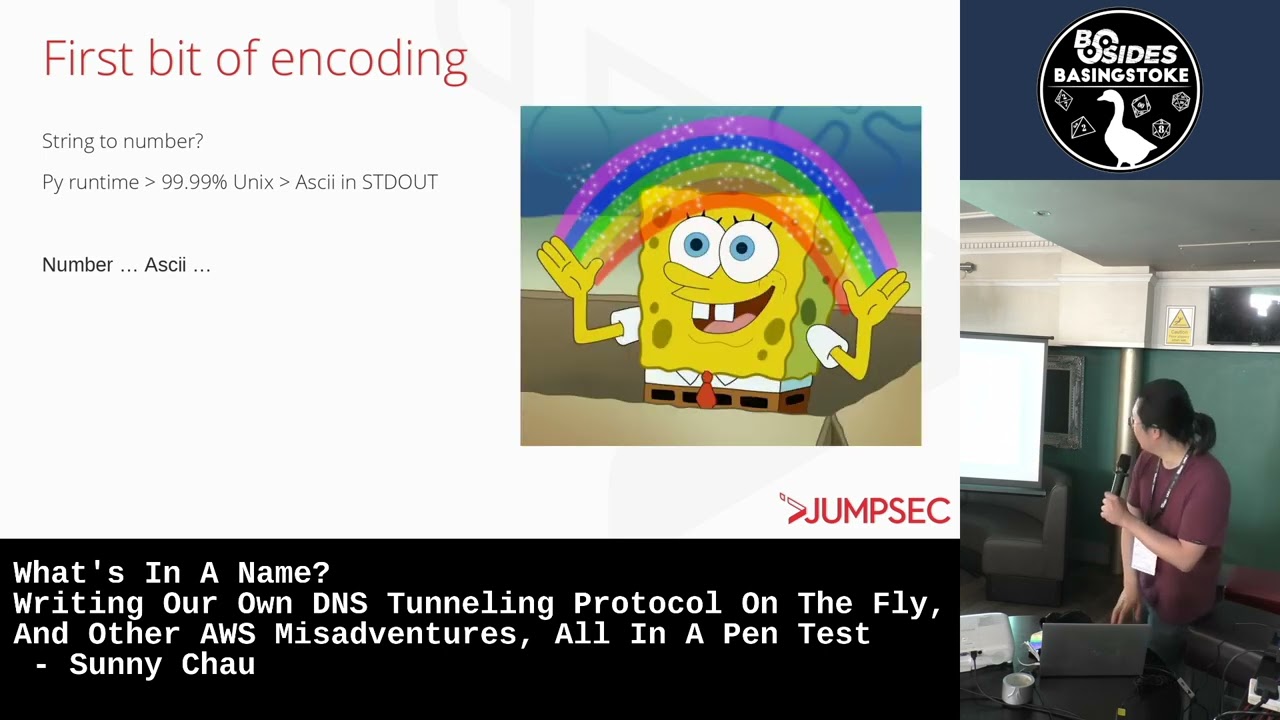
start the letter end of the letter or digit and have at least you know um only letters digit and hyphen and 6 C3 characters or less interestingly right so um so I've been thinking right I have poor user experience on B and I need to make something that's uh you the data is less than 63 byes per chunk I need to chunk them up right uh I I could only use letters numbers hyphens uh I need if I you know chop stuff up it might come you know at different you know time time St I cannot you know rely on the app to make all those um queries sequentially and receive those queries sequentially I
need some some something to you know order the the data by right and um also I don't want to as as the uh nice trap said I don't want to keep all my clients data to hoser so I want to run it on my own DNS server instead right uh and ideally I I should actually have encryption because DNS is supposed to be PL test plain text and you know have sessions even you know if you run command a and then the chunk of data coming out would be identify as command a and then and then command B would you know little each command would be a little nice session and then if you're R
humor in the sort of audience listening you think oh it's actually how cob strike does it or like your favorite C2 um uh C2 framework does you command control of course not as janky as how I do it but it's you know my principle is actually very similar right so um I was talking to my you know people in my team and like who has a good you know D server who is who who I which I can you know spend up quickly and does the job and um uh and ideally I could you know uh get the preck in real time in the terminal so I could just copy the whole thing and type it through
you know grab or whatever and uh decode the data right so um so some uh our developer initially gave gave me okay let me give you my custom made DNS server in go uh but then 5 minutes later his uh laptop didn't work so he couldn't you know he couldn't tell me how to compile the thing with his custom Flags so another red team person told me okay um you could use interact as message uh which is interesting tool by the people behind Team project Discovery is sort of um what you do with um three collaborator but it's free and open source and uh you can use your own DNS set for it but basically so how I implemented quote
unquote the custom DNS you know tunneling protocol I first encode the you know whole command output into one string uh because is sty and I basic SP and code uh the entire strength because it's s key I could you know basic SP and code it should end with only it should have only numbers uh uh numbers hyphen and uh and letters and actually although DNS itself is you know car uh case agnostic like like uppercase lowercase DNS would resolve the same but the server log would still get you know the upper case and lower case um as you know they receive it so and then I add a little sequence tag in the beginning like zero dot data one do data two do
data I could you know uh use my deing decoding script to you know decode the whole thing like sequentially right so um the rest of the you know good uh good to have um good to have features like encryption I was I didn't have time I was lazy um sessions I didn't have time you know checks some is actually good to have but you know again I didn't have time to throw right so this is interact s please let me know if you know how to actually pronounce that I interact who right so it's a you know useful tools if you are starting out with bounties and stuff because you know per razor actually requires 300 qu
per year uh it's a premium feature but interact s is free but then you are trusting their server to do their work so don't put you know sensitive stuff on their server right run uh run your own server for couple of couple of dollars per year which is more s so here we can see a screenshot of you know what it looks like right of course you can see the subdomain also blog post.com which is completely fake but um uh you can see you teral output of zero dot one dot all the trunks that 605 each and um I could just use the criative junly method of you know swiping my mouse through all this text
Data copy and paste it uh into a decoding decoding script and then you know get it do a card St so you need you but this basically the the screenshot the pH was actually the command output for listing um SL user SL bin because I want to know what sort of um tools I have inside of the sandb right so you have like LS M or CD all the good stuff there curiously you have curl but that [Music] g so with with that done it would have been a very good report at that point already like you've P the app you've Expo data out you've you you have achieved nevana of good us experience as
an attacker right but furthermore I knew that it was on Lambda right so what if this Lambda had an identity and then you can exploit this identity so this is sort of like what I usually do on the red team you compromise a application identity try to leverage it to move laterally to access what the uh app can right so basically I um triy to read the ads credentials on the on the app there's a couple of ways to do it um you can run you know the EnV environment command directly or you can um do as here uh reading you know/ prop enviral uh and you know get data out right so basically um when I did this is actual
screenshot J yeah so uh you can see the uh the session token and um bit of other ads tokens from the next streen S as well yeah so ads region secret access key key ID token and all that so so then you could log in as the application right so at that it was that point I become became the application itself so um to prove that I did this was done for Block post so it's not the client at itself uh I did a get color identity after the login and you know prove that I was actually being the Lambda itself and then you know what you do typically would be to enumerate to Pro forceable
sort of extra resources on dats that this identity could access so basically uh like any secrets any blobs any you know uses and all that good stuff but unfortunately in the job itself the identity could only access like uh use sh like public IP ranges so uh it was not very uh very impactful at that front um so the epilog was you know the client was surprised that you could get our found DNS like a tool and thought you know they thought they Inc has still sorry as extremely cool which I agree is extremely cool I hope you agree as well um but then the interesting part here was they thought that they blocked all
TCP and UDP ports outbound through narrow security groups if you don't do ads um n security groups are basically sort like ads firewall right so if you block all UDP and all TCP no DNS should be able to come out like theoretically so but could thing so it was that point and I thought ah yes I might have got a CV on you know AWS Lambda um or di right so turns out um uh on you know further reading up on how you could actually fully block DNS there's something called like Route 53 resolver DNS fire worldall right to you block people like me uh so if you have the same problem and you you
sort of want to actually lock down a quotequote air gap clown machine you need to actually set this thing up as well right I have a blog post on last.com you can you know pick a look at the steps it turns out like I'm like ah of course Jeff has thought of a way to pay War us to you know to to Wrangle us out of you know our hard earn bucks on the cloud bill is another thing another thing that you pay a couple couple of bit each month for to further secure your you know UDP 53 for lack of a better way to put it but then yeah thank you that's the end
of
story chill chill [Music] this is actually not my first time work but usually you have better user experience uh but it's you know it's a restricted sort of interface that forces me to you know WR protol and stuff but uh it's it's cool to be on to to need to be on uh to to be on stage and say you've written FAL but the the fun part is actually in you know figuring out the limitations because DNS is not supposed to be for data right it's for you know 255 bytes of an address that's all uh it's not like how you would want to repurpose a f to get on Silverstone right so that sort of engineering TR
just interesting and gets you to read the uh the actual RC itself which again I find it very fun not everyone does but I do find reading R is quite fun thank you enjoy rest day [Applause]