Spying on your employees using memory
Show transcript [en]
uh called sans instructor and um all-around smart guy uh new companies uh renditions infosec rendition netflix rendition info second jake is gonna be thomas how do you spy on employees using memory forensics so with that welcome jake williams
i want to make sure oh yeah that's good that sounds great so all right so mark gave me an outstanding introduction but of course i wouldn't be here for him for mark and lawrence and all the other great folks that uh all our great folks will focus on really really appreciate their uh and their great effort so i've always bring one uh barefoot here uh it's raining cats and dogs on fort gordon i just wrapped up sam's class stepped out right into a giant puddle and thought about uh speaking for the next hour and uh soggy shoes and i thought you know what this is family it's b size i don't know how to pull us off a black hat or defcon
right somebody's stealing my shoes if we're black hat or deathcon right but i figured besides we got the worst case uh old tomboy back to the uh tomboy back to the house so so again jake williams uh mal or jake on twitter i occasionally even tweet out stuff about memory uh memory forensics i know this is the red team track right i know what you're thinking why is there a forensics talk in the red team track well i wouldn't tell you that i started out i think in the blue team track and i got shifted over to the red team track so but that's okay we'll talk about how to use this offensively right let's suppose
that i work for this little uh gosh what we call a little three letter agency uh they go to church all the time we'll call them christians in action let's say that we work for this little uh agency called christians in action and uh and this this uh this agency uh despite what the name might imply uh might desire to coerce a certain people maybe then we could use this in an offensive fashion no joke though during my pen test i regularly use regularly used memory forensics uh to uh pull out the blog pieces of data uh that a lot of folks just don't think are there so we're able to pull stuff out hibernation
files and hibernation files go back to the bottom shadow copy what's not to like right so who am i that's all that you don't care right oh but i am hiring so if you're an infosec and you're looking to make a move and and here's the key this is where this verb was like 90 of people and you're willing to travel right and you're willing to travel come talk to me afterwards because again i am definitely hiring and if you're not interested in that i'm looking for interns so take your pick right in any case come talk to me after the presentation i'll be more than happy to talk to you so memory forensics in real life
but the number one problem that we have traditionally memory forensics be it blue team be it red team is getting somebody to take take the memory image and this is unfortunate because for the longest time we had folks in law enforcement and folks in instant response and what do they say right hold the plug all right pull the plug and even now already managers who are like we can't leave that machine on the network hold the plug right you take nothing else away from this don't pull the plug go high range falcon machine all right at a minimum well okay first don't pull take a memory image but if they say it's got to go offline right
now hibernate the machine at least the hibernation is hibernation file is a memory image unto itself and we have to love that we can crash on files as well right so there's an offensive use here as well as they have all the messages a lot of times when i find my root kit folks loading up they're loading up their rears in the memory uh it turns out they screw it up all right what was dr watson in kernel space blue screen adapt right or if you're on windows 8 the purple brownie face right because we had to recolor
and there's an amazing amount of evidence actually placed inside of a crash shop all right so obviously if we get a full memory down rock on right if we can do a live uh something like a live audit again if you're their pen testing you're gonna be able to live on it you should do just that right again all kinds of stuff with a whole lot of memory so again how do you prep to do this if you're spying on your employees because again the original i guess they were going to push on this i can swear i was in the boy team track when i submitted this but but again we don't care right
blue team red team whatever walk away understanding the power the power of forensics here uh you know and even possibly for offensive and coercive purposes but what first thing we want to do in this case is enable hibernation of our workstations laptops high range is always on right very frequently hibernation is not on not on our desktop machines i'm going to tell you hibernation files have pulled my butt out of a sling more times right more times than i can remember over the last two years going back into a volume shadow copy and how do we do that well mr tim tones he just left he's like after this man i'm out right so tim holmes right and
mark baggett who introduced me here a minute ago uh wrote bssm.dvs all right phenomenal piece of visual basic script that will help you uh jump into a volume shadow pop your two ways to do it manually all right and so we can also configure the power settings to automatically hibernate the machine when it goes either right this ensures a steady state of hibernation files very frequently as i'm doing investigations uh or when i jump on a box jump on a box during a pen test i find out that to find out the high ranging files are actually being backed up in the bond shadow copy and i've got six seven eight ten of these things so that i can go
parse through the pen test about four months ago jumped onto a box lo and behold right this company had taken a policy of making sure that all their machines right after they logged into them with administrative credentials that they would reboot the machine so no administrative credentials there but one of the volume shadow copy and sure enough there's an admin logged in all right admin logged in and that was cool it was from two weeks ago and so use mimikats offline mode and evening by the way has a windows debugger extension so we can use an offline mode also there's been a volatility plug-in written for this and so we were able to use this in offline mode without holding
this three-gig memory image back i i made the box to all the processing performing and when i had not that's that much right i went ahead and pulled out that plain text password from the administrator the administrator and so again it's got stuck in the hibernation file it wasn't the admin was still locked in all right the fact of the matter was yeah and had logged in we're set to go right okay so so what are we going to look for we start getting into a let's suppose we're going to come back into the coercion thing because it's going to make it float up a lot better uh forward we're going to just want to fire an employee
nail the butt to the wall right i want to look for like what are they running right uh maybe they have some chat program fragments i love it when folks tell me that we're safe because we're chatting off the record i love that right right it's encrypted and it's off the record it's not being saved anywhere and i'm like you don't understand how memory works remove your machine as a matter of fact pull the plug on your machine right when we're done with that when we're done with this little chat not ever doing anything illegal or incriminating right since i'm sure i'm being reported here somewhere right okay but active and terminated network connections this is a big big boom for
us as well right you may think you got in and you got out and nobody noticed you and you're set to go those terminated network connections hang out in memory we can find those as well encryption software man this one is totally for the win uh you know that nice pit locker a bit walker to go thumb drive you plugged in and was mounted and then you have to jump on the planes you close the close the laptop now that key is stuck in the hibernation file we can pull that out of memory and decrypt that usb drive offline right we now have the keys to do that and it's not just a bit walker to
go i don't want to just pick on microsoft they deserve it but right food perfect as well right who in here is still using true print that's okay you don't have to admit it i wouldn't either right okay so seriously if you're using proof or go bit walker is definitely the way to go um so we want to look for evidence of evidence of execution right file knowledge artifacts and internet browsing history you know i got to tell you number six number six has got to be the biggest one right because this is the only one up here that passes the mom test somebody can order the mom test mom test is whether or not jake's mom
knows about it right and so jake's mom actually knows about private browsing right and asking just is your private browsing well it's all and just how private reported in memory right all reported in memory even if it's not written back to disk so even after you close the browser again all still present right if my mom knows about it your adversaries know about two and you better believe that they're using it right let's look at an acceptable use policy violation right so we've got this is a fairly common one we've got a got a user who decides that you know they really like that music but it is kind of expensive and clearly we're not paying
them enough well we know what needs to happen here clearly the only answer is peer-to-peer right here file sharing and we see in this case uh we suspect in this case that our user is running peer-to-peer file sharing we're told to go remotely apply our memory image so whether we do that with encase enterprise or whether we whether we go go acquire the uh physically uh walk over the machine and acquire covertly at night while the employee isn't there it doesn't really matter right we want to find out what's being downloaded proved first off the user actually had knowledge of this and then prove indeed that the user is downloading is complicit in downloading downloading
these programs with peer-to-peer right so what i want to do well the first thing we're going to look at is potentially finding out information about information about the image right what's the operating system uh what's the kernel version any service packs in play and we want to find out potentially the image copy plug-in this is uh all going to be done with volatility initially i might use the image copy plug-in to convert from a hibernation file to a raw memory format because well let's be fair right there are way too many tools to accept raw memory formats with raw memory we can string search that as a matter of fact if you're not familiar with the bulk extractor you're missing
out all right bulk extractor is this awesome program written by a guy named simon garfield and every time i hear the guy's name i always think about some guy playing in some folksy band right but but the guy is a brilliant computer scientist right one of the many things that he knows how to do or he's written into this under this tool the ability to extract packets right back out of memory all right packets out of memory you can pull packets out of a page file right so this is stuff that's actually getting sent into the kernel pool it turns out then that we can actually get a p-cap file get a picture of the power of this by
the way right being a little pcap file things that happen on a box but you didn't really run tcp up there to grab it i mean that's awesome that's one of those things i just i feel all warm and fuzzy inside every time i think about it right okay so we also want to look for want to look for a process listening i'm all about that right but but oftentimes i want to find out what did the user do before i got there it was turns out we can find terminated processes sometimes as well let's take a look at how this plays out with our core user here we go ahead and convert his uh
hibernation file button convert that out to raw memory down so you can process it with some other stuff right because i'm i'm way too lazy to just use volatility only for this investigation and we see here that service pack one you know sometimes here we ask for ask for the image information sometimes we get some really weird uh several different results but this thing down here the service pack is always crown truth so again this is kind of a pattern matching deal and then the service pack's always ground truth it turns out that whether you're using server 2008 or windows 7 it's all the same kernel honey badger don't care right okay so start walking the process list right
what do we find emul is running well look that's good i feel like i can nail the user to the wall because let's be honest that's what i want to do i'm nailing the wall but you know the problem with this the problem is soggy right sogdy is the only person with more frequent flyer miles than me all right sorry i know this because saudi shows up at every one of my cases before i get there does anyone remember that soggy in real life nobody's feeling soggy are you kidding me sorry stands for some other guy who did it right and he shows up at every one of my faces it wasn't me it was clearly soggy right
so so we're stuck now we've got emul running there we're stuck now proving that it wasn't soggy that it was the user or not sorry so i always see the email process let's see if we can push on there when was the process launched who owns it right what files is the given process accessing then we want to look at network connections as well got a tool from redline here now this is a maniac tool i know mandy had helped uh man he had helped a little mania fire eye of course you know uh definitely help out the community here they served a lot of free tools otherwise everything is a little restrictive though right so they're free
but they're not free to me because i'm a consultant if you're a consultant they're not free to you either turns out that mandy and fireeye have a professional services division and they don't really want you to compete with them so not using their own tools anyway all right so you're free to use a red line providing you use it on your own cases right but as a consultant you can't use it on somebody else's cases but that's okay this is a demonstration we're able in this case to enumerate the security id right the security id of the user and we can now tie this back to a local user logging on the machine this certainly uh certainly looks like uh
looks like our user we can certainly confirm that obviously analysis absolutely yeah and so we were able to do that because we took the hibernation file and we use volatility to convert the hibernation file to a raw memory image by default red wine doesn't understand how to use how to use a hybrid or how to read a hibernation file so we have a good idea now either there are active downloads processing right we also can see that our suspect we have the right machine i'll screw that one up right they have the right machine is mark lucas the user mark is our suspect has logged on so we see multiple parts here uh multiple parts of of these files
we don't really know i don't really understand what those files might be i do have a good directory though that i want to go check that downloads emul temp directory for some of my partial downloads i also know i'm kind of thinking about maybe downloads email might have the whole it might have the bold files when they get completed uh and i might do a little search uh search within the strings here uh maybe look for downloads emul right and it turns out that this user is hiring ed sheran music right i don't have any teenage girls in the audience so i'm guessing nobody knows who has taran is it's okay so um if you have a teenage girl you know
where taran is anyway all right so we see indeed some of these and they're in the incoming director now we have to test to make sure that the incoming directory really means incoming but but okay let's call space fade here right what about networking connections because the user might say well that looks bad but i put those files there right name if you think that sounds ridiculous you haven't worked some of the cases i've worked because believe me the kind of stuff that people try to pull in their jobs and or when their jobs and or freedom are on the line is absolutely off the hook all right okay so so in this case here we see uh we see
some some closed weight meaning these are connections that are actually closed out they're no longer uh are no longer present we can see the remote remote server right so we might go look up that remote server and see if it's associated with associated with our emulator email activity and it turns out here we see that the process is well is actually emul.exe so it sure does look like that's going to be some of our some of our file downloads again of course we can run that to run that to ground what about this snipping tool dot well that got cut off right because there's only 15 characters available there's really a snipping tool snipping tool.exe is that my review snipping tool
yeah what does that do screenshots why do we care about screenshots
yeah there's all kinds of reasons we could use a screenshot right what what what's the big threat right i actually have a giveaway here somebody tell me what the big threat is that we deal with with sniffing tools that's right exfiltration all right give that man a uh i don't even know what this is i believe a raspberry pi courtesy of rural technology good job this is a nice hacker that's awesome right dlp right i work tons of dlp incidents right tons of dlp incidents involving involving folks exfiltrating data using images right whereas most of our dlp software doesn't have an optical character recognition so they ship the same data out right instead of shipping the word
document out they take a picture of the word document screenshot of the word document and ship that away better believe we're going to add this to our list of stuff to follow up on what about bulk extractor and so in this case what we're looking at is we're actually use bulk extractor and we're giving it the word list i love this feature because fault extractor will go through and build a list of unique words grabbing all of the ascii string or all the ascii strings as well as all the unicode strings and create a word list that we can then use with offline password cracking now i don't care what your password manager told you
i mean i don't care what your password manager told you about the fact your passwords are never anywhere in memory they lied to you right don't worry we zero them out okay well you do a best effort right none of these password managers that all run user space have anything to do with the kernel space activities that are going on while windows in the background moves that memory around we find passwords all the time right now unfortunately they don't label passwords right but by giving us the wordpress option we got a full word list and now i have a good idea of where to start i can remove all the common things that are normal for a given
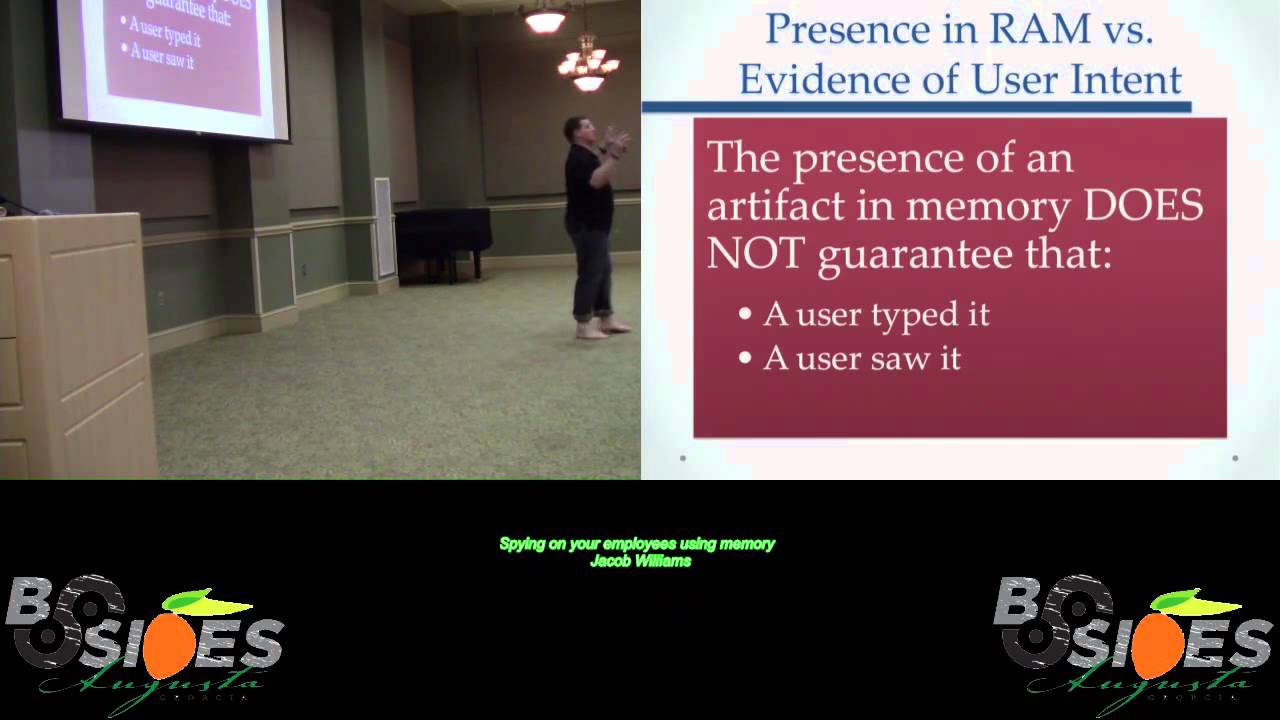
windows 7 image right and then we can move forward with a move forward looking for things that are unique to a particular user right what else can we look for i want to point out here that the presence of an artifact in memory does not necessarily guarantee the user typed it or even the user saw it right so and i've been harped on this for years i've been doing memory forensics since before memory forensics was cool uh some of you know me uh my days uh going back to a good old hb gary kind of both supported hp gary how many people have heard of hp here before they got hacked yeah see that's that's really now i have
to tell you that i was not in charge of security or did anything with security hp gary i simply did malware reverse engineering and built most of their courseware for uh for their memory forensics and malware reversing but we used to tell folks this we're like look you know our product would actually go pull out urls from memory and we tell people be very careful whatever urls you see here do not necessarily indicate the user or the user actually went to the url or even visited it or typed it or anything there's all kinds of all kinds of explanations an interesting consulting call uh about six months after i found gentlemen uh toddler gentleman's class and they sent
us a memory image and they're like dude this guy's been he's gotta be looking at all kinds of form and i'm like okay cool like we have at least ten porn sites right and then i get a follow-up email as image is popping up to our server right we've got like 100 form sites like wow this guy's busy on a work computer seriously right i'm like wow you have like in like corner office way back like through a locked door no windows kind of thing right by the time the memory image is done uploading because i'm waiting for the themed upload they're like there's more than 500 porn sites and i'm like this is unrealistic by any by any expectation of
right so we take a look at it it turns out that a antivirus product an antivirus product who i won't name mcafee that was there had loaded the entire black list of urls right that they didn't want people to look at into memory and so these folks now are looking at these urls and like this guy i mean anybody ray charles could have seen this one coming right looking at the uh looking in memory because they were all like one after another they're separated by you know by some uh by some string separate it was like i don't know f delta or something whatever it was it wasn't i mean it was fairly obvious what
was going on except not to these books right so i want to highlight again even though i said it i dedicate a whole slide to it it doesn't mean when you see it the user saw it or the user even typed it but but hey you know what let's take a look at this so we we're able now to search for search for keywords this is a neat little tool called bulk extractor viewer it'll actually go in and view the cool thing about bulk extractor i'm a command line junkie absolute command line junkie if you see me in a gui there's a reason for it right alt extractor viewer will now go and parse those uh parts those files has
a convenience of having a hex editor that vectors you into right factors you right into the memory image or disk image or doesn't even matter what it is bulk extractor doesn't care right uh but it'll vector you right into that and he would search for sharan because well we saw the user downloading sharan and now we're finding new songs that we didn't uh we didn't previously know about so we found additional additional evidence here and for those who aren't aware of this file zero here is actually an ntfs ntfs file header right so this would be out of the master file table right so so now we're actually backing up what does this indicate maybe the whole master file table is
loaded into memory okay well that's good to know as well all right so so we can take a memory image and take a memory image and actually actually use that memory image to enumerate all the files all the files on the user's machine yeah i think that's useful at least on the root drive right and any other drives in our map sir what about the case of the key at that point in efs so the case of an efs folder that's an excellent question it turns out to still be able to list the contents of it uh providing that the user has entered the ef-s key all right so uh essentially uh what you're looking
at there is providing it's been it's been opened in memory you'll still be able to see that uh see that data if the machine hasn't been booted or sorry if the user hasn't entered their efs key if it's a manual process if they haven't entered the efs key since the time the machine was booted then you won't be able to see the contents so in this case of course we're not seeing the file contents necessarily uh we're simply in this case uh simply in this case able to see uh able to see the actual file record but that's still that's still something i'm liking this again a whole lot more here turns out again the bulk extractor is pulling
packets out right and now we're able to actually go look at some of that traffic from we saw the closed network connections and of course you know some other guy did it we have to be sure about this right how many folks are running a dedicated packet capture your peripheral yeah like one or two folks at the network boundary start go buy a cheap server and just start doing it you know there's a tool for that sounds like a security apple or no a security onion that's it that you can use for free all you need is a cheap server off ebay or or a cheap workstation honestly that you're getting ready to rotate out of service right
something is better than nothing right even if you have a one day school if you have a 12 hour school again that's better than nothing right that's okay again we can pull packets out of the uh packets out of the air traffic as well that certainly helps you can actually go in and look all right we can actually go and look at the packets here we did the follow tcp stream we see the url yep that's the email update server right again all the evidence is coming together not looking very good for not looking very good for the user it turns out we don't url searches here right it turns out that we see a search
a search and bing for e donkey now this is where you know this is where you know for sure that this particular scenario is contrived because nobody uses bank okay so we can even go a little bit further we can parse the ie history the internet explorer history and go find url's visit by the user again i want to point out that we're not grabbing all the files on the disk we're grabbing memory all right so so again think about the power of this right again we're parsing all this stuff out using in most cases your singles will uh volatility although i have to put in a plug for recall which is a portable volatility
that i'm actually involved in now uh it's it's going to surpass i'm positive we'll surpass where volatility was at uh you may have known michael cohen a very very smart guy who works for google uh he had been working on what they called the volatility technology preview branch uh or some folks knew this gudet branch could add as his handle and when it was clear that that was never going to be reintegrated into the volatility he broke that off last december officially forward the project and so recall is pushing forward uh we're working to make it a bigger battery faster most importantly faster and more flexible but in this case here again we see the
parsing out we have the same evidence just just pulled from a different uh ultra different angle here we're doing it off the command line and volatility here we had a bulk extractor viewer i'll take it either way all right so what about registry analysis turns out our registry highs are mapped into memory as well so what do we want to look at well you know this makes really makes my system triage you think about this it's faster you have to do hard drive imaging i regularly tell people from a forensic standpoint right i'm done with my investigation before you finish imaging the drive this is the reality right i mean it is that quick and if you think
about this particularly we're trying to get law enforcement how many folks are law enforcement and we're trying to get like law enforcement to you know to go grab seeds evidence you know we need we tell them we need like 12 different things everyone's telling you one thing right any one thing press the button get this one thing and hand it over to me and and whether it's whether it's law enforcement whether it's help desk right whether it's our hereto or whatever it is uh systems administrators they seem the one thing right makes it just that easy uh keys sub keys and values it says can be cash but most of the time r and d
cash uh in memory because they're being actively used by the system right so maybe i want to look at maybe i want to look at my shim cache that means shim cache so mark baggett actually did a uh i did a presentation last year derby pond called owned by default it's called owned by default and he talked about the built-in micro software kit all right so windows uh windows since xp has actually included a rootkit with every copy pre-installed always loaded right with every copy windows in fact you contacted that microsoft you can talk to mark rusinovich of system journals fame says oh i turn this off i said you can't right there's no way to get it out right
you break the system and so basically what's happening here with this uh with the shin caches so that you can have application compatibility and some folks refer to this as compat right so you can have application compatibility you essentially build these shims and those shims then will automatically load special dlls into whatever process you tell it needs a shim well because processors may need shims windows actually checks to see if those things need shims and build a cache of the shims required for each executable executed on the system this is good news for us because now we have another place to go to see if an attacker right or my suspect right executed something on a machine right
i've been seeing some of my uh i'm just going to call my little chinese friends right i've been seeing them recently as they execute stuff on machines actually deleting other evidence of execution but for whatever reason i think it's because they don't know about this i hope they're not watching the presentation uh it turns out that uh turns out they forget about these and these registry keys now if you do a plain text search through the registry uh these are kind of hard to find you know they're having any code these right so that's okay again uh we know how to do it it's as simple as running the command on the screen all right so shim cash
shows us indeed in this case uh shows us in this case uh that emulsifier was executed and were able to identify precisely when that was first when that was first executed so we can even go a little bit farther and we can say that mark lucas mark lucas on january 24th 2014 executed the installer out of their home directory so i'm going to go ahead and ratchet this up from somebody else did it right right on to probably mark lucas i feel like i have enough mail mark to the wall at this point but why stop there right so maybe we want to go look at shell bags right windows spies on everything you do
you open up a folder and explore and you go look at files the actual names of the files that you look at inside of the folder even if they're efs even if they're truecrypt even if they're bitlocker get reported all right now this is somewhat non-deterministic in cash 100 deterministic shell bags not 100 deterministic right so it doesn't always doesn't always show up but that's okay again when it does couldn't be any happier we're able to look at some of the files included inside of particular folders right and so that's good right then we actually parse the dmft pull the mft out of memory and go look for some of our creation times again to get an idea of when precisely
mark lucas did something dumb like install peer-to-peer file sharing software on a corporate machine right so we have evidence of email executables we have lots of cool uh user behaviors we saw snipping tool don't want to forget about that because that's a possible dlp issue all right if not i i'm dying to know what mark was sniffing right let's talk about another bad user right i like this one way better henry henry is an evil insider all right he got around his laptop we have his uh we have memory images at this point from that uh from the high-rendered laptop uh we need to know whether or not henry was trying to do something stupid like steal our
corporate secrets right you guys are going to laugh at this case all right i created this uh gosh probably it was april it was in april two weeks ago i worked this case right two weeks ago i worked this case for real so the guy's name wasn't henry and i mean almost almost verbatim about half of the evidence in here actually winds up and it is every bit that stupid right let's walk through this right so we open up we look at the process list and i see notepad i mean nobody uses notepad come on man right not my end users i know my admins do right if you use notepad plus plus right it's not real
you said hey who said hey like you actually use notepad i want to introduce you to notepad plus plus so we can move on okay so so anyway right it just clearly superior replacement uh we have a user of the command prompt open this immediately makes me as suspicious as well and tons of browsers and i have to suspect that these browsers are one or more of these browsers are in private browsing mode now i don't know if you've ever had to explain something to a jury before anything you've ever been deposed besides my law enforcement friend anybody ever been to pose before okay well so depositions are awesome but jury testimony is even cooler and this is not
to knock the criminal justice system or the jury selection process and the point of view fine folks has served on a jury thank you for doing your civic duty however applause for effect a brewery of 12 people are not a jury of your peers right the reality is i'm guessing that the jury of 12 people we would see assembled for a trial are 12 people who find nothing better to do and have no excuse to get out of jury duty i mean that's the reality and you go try to explain something i'm not knocking this right but the reality is you go try and explain something to these folks about technical concepts and it is very
difficult to do right now i'm trying to explain about memory forensics disc forensics is hard enough for crying out loud it's at least deterministic memory parenthesis is non-deterministic i can take a memory capture i cannot do anything on the machine and i can immediately take another memory capture and open the same memory captures the machine kept running all right so this becomes difficult right people don't like processes that aren't repeatable it feels very fuzzy right it's difficult to explain to them and then i introduce a screenshot right now this isn't a traditional screenshot it's just a wireframe screenshot we're going back into the graphical display subsystem all right going back into the graphical display subsystem saying where are all the
windows positioned how are they aligned and what was the window text associated with them right this is better than nothing and this is something you can put in front of a jury that makes sense and i feel like i can put this in front of a jury and be okay right because it turns out that our user works for better widgets and he has our competitors web page open internet explorer not by itself isn't bad okay well it's kind of bad but it's not 100 damage but but then this the google search right corporate espionage for dummies how to post stolen data on pastebin and this is the part of the case that i kid you not right i kid you
not i worked two weeks ago i worked two weeks ago where i had a user googling for instruct from the corporate network googling for instructions on how to conduct corporate espionage and you can go ahead and say right the gene pool there was about three inches deep right uh but regardless right this stuff happens right okay we see uh this is something here with henry and we see stolen for debt i don't know what the rest of that is okay so let's go ahead and continue uh continue on here we see several closed network connections i'm scanning through memory looking for looking for network connections we find some closed uh connections if i want to look at these
ips here i'm using bulk extractor we located credit card numbers in fact i didn't have to go search for these bulk extractor highlighted them for me and said hey now we found a bunch of credit card numbers go go check those out when we do uh we see that it looks like we have some html dumps here credit cards and addresses and passwords and this looks all kinds of ad this is classic corporate that's classic corporate espionage right looks kind of bad right already i'm thinking that this guy is bad but but then we go look at the urls i'm gonna go look at our searches and we see selling confidential information to the highest
bidder uh my user two weeks ago was not quite that stupid they weren't worried about the actual bid prices of the uh the actual bid prices uh they already knew who they were going to sell the information to so they weren't worried about the bidding they were curious about how to get it out and how to get it out without being caught right you want to talk about sealing the tent and nailing somebody's butt to a wall that's a great way to do it right say look you just search for how to do it without getting caught for crying out loud i think we're set right anyway so so how to sell the confidential information to the highest bidder
selling confidential information again ray charles can see what's going on here let's go fire the guy right so we look at the command command.exe remember we have a command.exe process running and even if that command has been terminated we still have the opportunity to go parse through memory and find the data structures associated with that command prompt now some folks will remember the good old days of dos key okay actually i'm looking around here and i think maybe like four or five people in the room here old enough to remember that that's okay all right it's okay in the current windows command prompt though you know you can up arrow some people thinking f7 right and see that see the list of
commands that are there that has to be stored in memory somewhere it turns out we can go find that and parse it out but wait there's more right it turns out that uh remember when you right click inside the inside the command prompt and ask how many lines of scroll back you want yeah it's doing that so we can allocate enough memory to store all those lines of scroll back and it turns out we can pull those out as well right i really like it when my admins right once one of my admins that i'm investigating because by default i only get 300 lines of scroll back right with an admin it's always 99999 right so you get a lot more
evidence there right from your admins than you do from a regular user i'll take what i can get all right so we can see what's that oh seven scrolls yeah no dissolves that scroll back to one exactly right unfortunately then you can't see anything in your command prompt either but but hey whatever i mean usability who cares right okay so so our user our hapless user here pops open a command prompt says post data to paste in and post secrets to text now look this guy's a total pace eater right he looked the window on the way over to work this morning but hey right clearly all right clearly though this this definitely definitely feels intense
and i don't know for sure that there's not a post.exe all right if there's a post.exe on the machine uh this command may well have succeeded i don't know it's a secret stuff text although i'm guessing probably that giant credit card address password etc dump that was there right again trying to follow up and make sure that that's that that's not totally uh there's no post dot exe we can parse out again uh ultimately the uh the command the command history by the way here now we're seeing the consoles right we see without any shadow of a doubt again it isn't henry's home directory all right we can pull out the sid associated with the uh with the
command prompt because this one happens to still be running but bear in mind there are times we're going to pull this data out and the command pump is going to have already exited right well this is unfortunate for us because because now we're not necessarily going to know who owns the command prompt but we can still go back and grab the data i'm liking that so what about contacts right so we looked at bulk extractor and we're looking for email addresses and facebook ids dead end right bulk extractor actually pulls these out right what about twitter well unfortunately there's no bulk extractor plug-in for twitter yet you want to use the right one all right or
maybe i'll write one it's hard to say right in any case it doesn't automatically come out and say here's twitter but it turns out strings strings come to the rescue right so i'm gonna look for i'm gonna look for http i'm gonna look for twitter i'm looking for twitter links like embedded twitter links because if you go on twitter and you actually look at the twitter webpage all those tweets that you look at are all links right they all are embedded with links and may show you your contacts or your private messaging or dming on twitter let's look at that right so uh in this case i see that i've got uh i've got 1537 entries okay i like that right i
want to make sure that we're looking for unicode and ascii very very often folks forget right folks forget about about unicode and ascii unfortunately windows under the hood does everything in unicode everything in unicode if you simply run strings on a linux machine you only get ascii alright so there's an encoding l strings minus el will actually give you all the unicode strings you want to make sure that you examine both all right okay we've examined both and we're looking at 1500 entries i i can manually examine those i might do some rep or too many more than that uh we take a look there unfortunately stuff out there someplace that kind of sucks right so i actually did not free
populate that as i was doing the examination i'm like great all right so we created the memory image and anyway i gotta stop there so um but we look at this lenny zeltzer guy he turns out he's in the image too right he's actually my co-author on the sans malware uh sans malware reverse engineering course uh all around all around great guy now i'm thinking that henry actually knows or follows lenny uh lenny might be a person of interest so we start doing a little bit of uh certain a little bit of gruff foo in this case right we're looking to see uh maybe do we have these status updates we're gonna do some rep foo and we
decide to go and get rid of money all right and this is all we've got left and so not a lot all right so there's a lot of money and not a lot else right so 927 entries uh total and nine without money's name in them i'm thinking he and money are like this right these guys are now collaborators right and this is not looking good right i don't want to get sued by lenny by the way so this is just a fabrication right well you know our job as investigators when we're doing an investigation right or if you're into that christian is an action group and you're trying to force somebody with like fake evidence or something whatever
the case is right in this case it wouldn't be fake this is real evidence right now you want to make sure that you've covered all of your bases right so we don't want to walk up and try and leverage them with lenny and find out that that's not going to work out very well well it turns out and i don't know how lenny has such awesome seo but when you google how to post stolen data on paste then i kid you not lenny comes up he is the number one search result and i have got to figure out i have to figure out how to get some awesome seo like that for some really good black cat
activities right you know like for instance i don't know how to how to hide a body right don't you want to be number one for that now sure enough when you when you google how to post stolen data on facebook money's site actually pops up number one so it's awesome seo explains this we can actually exclude him as a person of interest i would go investigate the page when we finally invented his twitter feed embeds his twitter feed and his webpage that now explains the 920 somewhat entries that we saw so we'll exclude them as a person of interest how about the notepad well it turns out that we can actually dump the memory all of the memory from the
notepad.exe and we can confirm those credit card numbers that we saw earlier are actually open inside of the notepad the notepad.exe i running an experiment recently is this being videoed and distributed yes
can you pause it i can't pause it i can stop it though oh bail yeah i'm gonna hit this after what's that anything after the talk yeah we'll do it after the stop will remind me so please just all for good okay so anyway i've been doing some experiments recently and anyway it's awesome okay so mem dom right so awesome in fact how about that right okay so we've got number and so uh in this case uh you know we're using metadata to dump out all of the memory are able to recover biopoms this is pretty darn pretty darn interesting right so pretty interesting we see in this case that we're grabbing now these credit card numbers out
foreign explorer well we can go through and dump all the internet explorer processes as well dump their memory and we can actually recover the web page contents that are currently in the web browsers as well as those that have been accessed since the browser open even if right even if in private browsing mode is turned off because in private browsing caches for the session right our private browsing caches for the session and then deletes when you close the process this is a huge huge win good question
that's a great question so in this case we're dumping the entire memory memdump is dumping the entire memory space right the entire memory space for the entire memory space for the process that includes all the executables all the dlls all the heap segments all the stack segments everything for the process this is really what i want procky i see them all right rocking a c-dump will dump out an executable and it will realign it according to according to the pe all right so according to the pe header it'll actually realign it the way that it would have been originally on disk proc mem dump which is different than mem dump by the way proc mem dump will
dump only the executable but does no makes no attempt whatsoever to realign it according to the pe head respect and so there are times when you want both of those all right so those that's the difference those are the three uh three different plugins
well they're technically correct they are dumping slack space but what they mean is they're not trying by slack space what they mean is uh that they're not trying to realign the file was originally found on disk so okay okay so so in this case here again we're dumping all of right all these internet explorer process memories in fact we're gonna go park or uh we're gonna go card for images i always see a twitter image we see some other uh some other pngs i've done this before and i've seen some images that i wish i could i mean if there was a toothbrush for your brain i'd be using it right so just want to throw that out there that
there are definitely opportunities here to uh see some stuff you don't want to see all right how would they open files well we can go through and find and this is actually pretty interesting here uh with this file scan i actually find good good evidence for this even after a user for instance let's say i have a user that plugs in their usb drive and then and it pulls it out and we don't have access to that encrypted usb drive anymore with file scan if the files were open i thought they were just sitting there if they were open we may still be able to recover those even though the drive is long gone right
so hibernation files crazy lucrative source crazy lucrative source for evidence uh great for doing uh forensics great for uh great for finding uh finding those little golden nuggets all right those little golden nuggets as it were as for uh as we're working through a pen test uh but look i mean if no hibernation files are present you just win pmap all right take a lot of memory capture and parse it on the target you don't want to bring that thing home man that's sometimes that's three four eight gigs right parse it out there on the target bring your data home all right we can use volatility as a standalone executable you can get into volume shadow copyright
sometimes you've got seven eight ten of those things hanging out right that's a ton of data it's a ton of data it's crazy lucrative right that's all i've got any questions sir no it's obvious that you can get a lot of data the windows machine what about mac and uh systems oh absolutely mac and linux systems the question was great a lot from windows in my safe because i use a mac and i know that apple wants you to think differently but the answer is no you're not safe by using a mac without a doubt we don't have hibernation files explicitly on the map but again you do save state and we were able to pull i remember an
amazing amount of data out of the map i would even go so far as to say uh that because the source for a larger number of the mac uh large number of the mac programs is well known and well understood we're actually able to get better data from a mac than we are from windows machine i hate windows because you know what's talking about spying on employees and nobody issues their employees maps so and nobody issues their own voice linux machines right any other questions i was told i have like two shirts to give away for awesome questions so i guess i'll ask you would you like an xl or uh oh one trick you're away follow the next
l or large large there we go so i apologize if i have two well there we go it's all confusion all right here we are thank you sir the awesome question about max right i can tell you're an apple fan okay so look again that's all i've got uh i really appreciate your time uh i apologize this wasn't like a hardcore red team talk i swear when i submitted this i thought i was in the blue team and i think i got moved right but that's okay what demons oh it wasn't so much of a demo thing but





