The Adobe Guide to Keyless Decryption
Show transcript [en]
U we've been we've been hanging out for for many years although he's he's uh rejected me as of late and has not been hanging so I'm just we're just very fortunate that he would come to Augusta here I I have a pretty good idea of what Tim's going to talk about so let me just point out that the fail guys they've got some really cool stuff over um now but seriously uh if if uh you see something if you're there's a talk that interested in this one um although Tim's talk is going to be it won't hurt my walk out the fail guys who got the lock picks over there and those they're over in uh 170 in the the areas
right in front of the um the blue teamers you know get the blue teamers picking the locks and then they like oh this is really fun and they come over the red team talk it's it's like a Gateway Dr right that's what we're doing with but with that um welcome Tim toes thank you I love I love a don't let Mark give you guys a Mis deception about how I feel about austa I spent a lot of time here actually about what six or seven years of my career career has spent in austa a lot of time before Bard anyway before before I jump into mine I want to cave out something that Chris runer said in his last talk real quick
and it's about mentorship right I'm a firm believer that mentorship goes both ways and at everyone at all times is is two years behind someone else in their industry and two years ahead of someone else in their industry so you should simultaneously be mentoring and being mentored at the same time at all times okay that is defin will provide maximum growth to this industry I encourage that to all the folks that I Mentor right and I'm constantly seeking those above me like Mark right that have been doing this a lot longer than me constantly seeking their mentorship as well uh because like I said it goes both ways and that's the that's the best way that
we will uh people will enhance our industry okay so earlier this summer I got an email from the guys at bide hey Tim you going to talk to bsides this year I said I don't know you know Recon get kind of old you know I'm sure most people have heard of it by now if not seen something online me tweet about it and frankly I don't think it's all that cool to be honest with you I've had people disagree with me when you stare at the same code for 2 years it's not cool anymore all right as for Chris can verify that right it gets old after a while right so Rec I wasn't cool to me
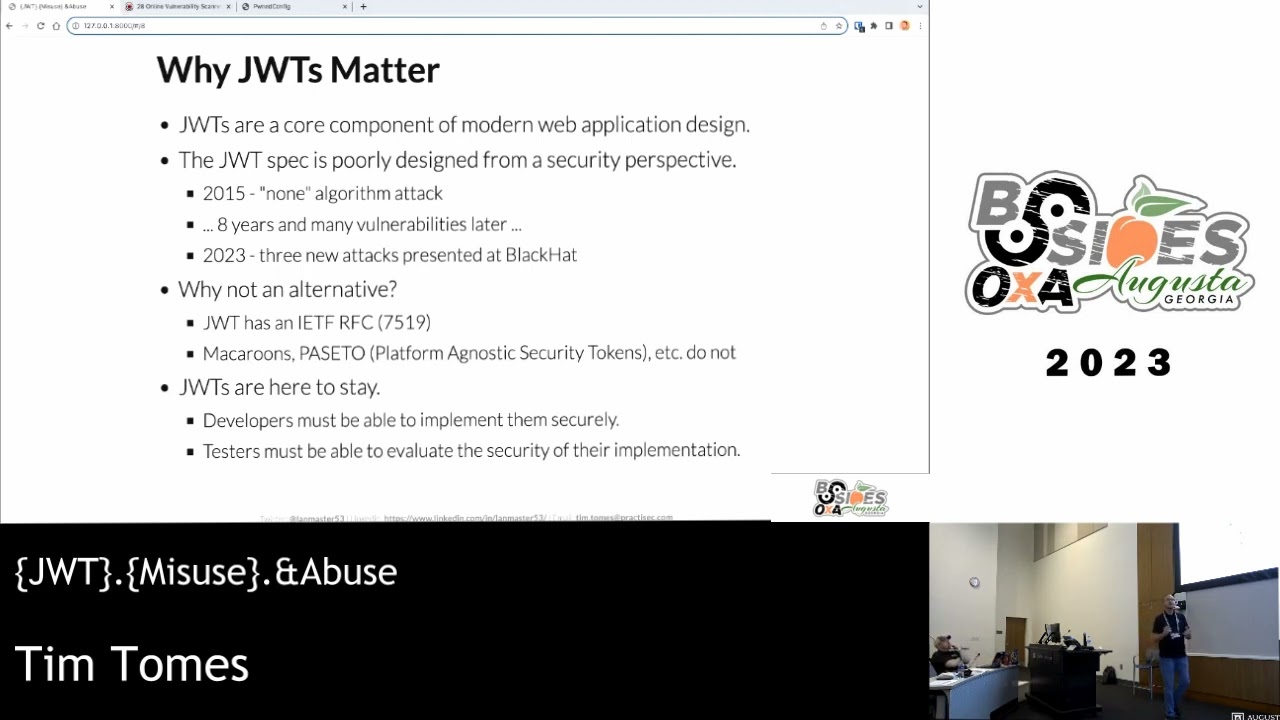
anymore but I was starting to play with uh with the Adobe breach data that came out last year and there was some kind of fun stuff there nothing new nothing groundbreaking nothing that no one's seen before read any articles about it but I was tinkering around with it and I said you know there's some lessons to be learned in here I'll talk about this put the slides together have about 15 minutes cont there like well this is not going to work this is after the cfd was accepted right so I went back and uh started thinking about it and you know week after week we see these breaches come out all this data being dump you
know Troy hun is constantly tweeting about it there's other folks every week There's information being dumped by hackers that are breaking into websites and stealing credentials right I got to thinking well this is a huge problem why don't I just give a talk that addresses this issue and then maybe somewhere I'll turn a light bulb at somebody's head we'll start to turn this problem around so that's what this talk is about we're going to talk about store pathw for security and we'll also talk a little bit specifically about the doy dump some of the work that I've been doing there that's okay so who am I well I'm not going to go into any detail just
know that all this middle stuff I'm doing to achieve this bottom bullet and I'm hoping while I'm doing that that I'm glorifying the guy here in the upper left hand corner so I want to give a quick shout out to my buddies at profs hackers and hack forers while I do that all right the agenda you want to spend a whole lot whole time a whole lot of time talking about the agenda because we're going to hit all this while we're in it so we're going to talk about some misconceptions here about these three atems at the top we'll address the problem and then we'll break the problem down into different sections here um as
you see we've got five different iterations we're going to go through we'll talk about different implementations of T password security talk about the individual problems that lie there talk about some solutions and hopefully by the end of the end of the day we'll all be much much better at storing passwords in our backend databases okay so disclaimer I'm not a crypto guy I don't know anything about crypto the reason I Rec G is because it's simple it's easy and I'm not complex all right so if you see something that's inaccurate here okay that's fine come forward please correct me afterward don't be please don't be a crypto snob on me I can't stand crypto snob I'm not going to call you out on it
but just be nice about it because I don't know much about crypto and I'm admitting it to you right now but the beauty of this thing is is you don't have to know a lot about crypto to do to do to store passwords properly right you don't have to know a whole lot about crypto to identify when somebody else has done it wrong as a pentester and exploit that flaw okay so that's first disclaimer second disclaimer is offensive material as possible for any of you that have seen a Recon talk before when we start dumping password you start to learn stuff about people you didn't want to know all right and so you may see some things in here they're
slightly offensive please big big boys big girls we all know what we're getting into here um please don't send me any emails or hit mail I appreciate it okay so misconception here encoding is not encryption is not hashing okay now you're right in saying that hey every single one of these transforms data they all have something in common you're absolutely right they have something in common they transform data but have very very different reasons for transforming that data and I'm hoping that everyone in here as a precursor I had to script like 15 minutes out of this talk I was going to break each one of these down I don't have time so I'm hoping everybody
understands these but basically encoding transports data so that it be consumed by alternate Information Systems okay encryption transforms data for what confidentiality to prevent E dropping right prevent someone seeing it that wasn't intended to the it and then hatching is for validation right we want to validate a piece of data in two different places we can use hashing to do that right so these concepts are extremely important but the problem is is developers are still applying these Concepts wrong when they're implementing stored password security or secure stor stor password storage systems okay how many CPS do I have in here you should see a whole lot of scenario spe because we're in a fairly heavy government area and that's kind of
one of those regulations right with 50 it's been a while so I don't know what it is but anyway this is CP level stuff this is entry level security okay and the simple fact that developers are still doing this stuff wrong means that they don't have even the basics of security and their development practices okay and that's a huge problem and when when we break ASC down all the way to this root level this is the problem no secure coding practice is training for a lot of our developers okay huge issue second problem is when our when our developers create a system that stores pathes in securely these guys step in and moop it up anybody know who these guys are you
seen these folks before breach alarm is a fairly new name uh have should I Chang my password.com rebranded the breach alarm Okay homeless and this is have I been tone by website by Troy hunt what these folks are doing is is when the hacker breaks in your network and dumps your password to the internet these folks are going and collecting them now they all have a knowable calls right they all provide this pretty little form that says put in your email address and we'll let you know if you think all right but in the background I'm convinced that most of these guys are storing that data and using it in other places right I know for a fact Troy Hunt
is storing it he's not selling it he's not Distributing it and he's doing it because he doesn't want to be the guy responsible for that I trust Troy hunt because I know him well and he's a really good dude bre alarm don't know these guys at all they say that they don't store that stuff I don't believe them all right homeless does store and they'll sell it to you okay homeless is selling that stuff it's ridiculously expensive for those of you that have ever gone and looked at what it cost to gain access to their API but it's not cheap start about $60,000 a year right and that's for a million requests which goes really really fast right especially
since it's 10,000 requests dumping into the domain for the data so all right so these guys are going out storing that data and then making it available which means now you have all this information that's being harvested and possibly sold off to what third part third uh countries that are adversaries right or maybe some uh adversaries with some some funding right some sort of sponsorship there yeah it's expensive but it's accessible and that's the point so we've got a problem now what I want to do is I want to go into a couple different password store systems that I encounter while I pent test and I want to talk through through each of them independently kind of show you an
example of what they look like and then we'll dig into some of the problems specific problems and solutions and how we can fix this Stu the first one I want to talk about is encoded or plain text uh and implementation of storage password security I call this storage password insecurity okay and basically it's real simple here's our user table we got a username and we got a password and the password's in L text so was literally like here you're going to see some pseudo code under each of these diagrams that I do typically we're trying to create some sort of protected form I refuse to go protected for this because it's not right it's just
straight up clear text really simple so where's some characteristics of this well man you got a really simple password recovery system right all you have to do is say hey I off my password here's you know the answer here's my name my first pet and well here's your password they can give it right back to you you don't even have to change it you don't have to do go through a complex emails email swapping system or any of that stuff real real simple password recovery system these folks are typically folks doing this get caught real real how many of you have seen a password in your email before your straight up password sent to you right
those people should be on PL Tex defenders.com if they're not submited because that's what they're doing right if they can give you your PL text password they have to have access to the pl text password so it's functionally simple yes but incredibly unsafe the next thing is because of this we have unpredictable resource requirements and this leads to length restrictions well what does that mean what if I create a 10 GB password you going to store all that and what if you don't have 10 gab space within your storage okay can I can I conduct a dial service attack against your database or against that server because I fill up the hard drive by slamming huge passws in there so what
happens is is these folks go in and say well we're going to Institute a length requirement okay and what does that end up being about eight characters yeah ends up being about eight characters right and then we say oh by the way you can't use exclamation points single t double post or anything which streams unal injectable right so we have this problem here that we' got unpredictable resource requirements now and at least length restrictions which what weakens our passwords okay and then the major problem with this implementation is there's absolutely no effort required to get to the clear text password once a breach occurs when a breach happens B CLE clear text factors are out there so who's here
who knows who Cuban media is okay the first person that's brave enough to raise their hand get this book all right that guy back there you're an online dator aren't you it's right here on this on this chair right here okay so yeah Cupid media they uh they run about 35 different Niche dating sites well in 2013 November 2013 they got breached and 42 million clear text credentials were done through the internet D just like that we got passwords right and a whole lot of people were dating people they shouldn't been da right so let's see what this looks like let's demonstrate the risk of this type of storage system right using Recon NG so Mark lied I am
going to use Recon NG today we are going to talk about it because I'm going to work it in every talk I give for the next several years probably right so let's go in here to Recon NG who do I like to pick on all the time when we do when I Recon demos NSA the NSA let's do it all right so we'll create a workspace call it NSA let's add a domain what's what's nsa's domain yeah N I go right so the first thing I do how how do we how do we get access to credentials Recon ngy I'm going use homus right there's lots of different ways to do it you can go out
and mine it yourself right you can talk toy hunt and giving it to you which he's not going to to that's righty right there's a bunch of different ways you can do it but since I develop and I've got a relationship with pone list I have access to the API so I use Pon list to do this so I've got a module I got a couple of modules that do this you've seen me Demo before but the first one I use is is a is a module called is pone and basically what it does is it queries pone list and says hey do you have any credentials for this particular domain so let's load the is phone
module and run it and it tells us yes I had 284 phone accounts. go and the last time it was seen was August 26 2014 which was like three weeks ago right so this some pretty recent pretty relevant data in there right so I want to go ahead and dump that by the way this was one query this next one I'm about to do is worth 10,000 of those 1 million tickets P 60 Grand form all right so let's load domain CBS let PR this we are pulling down for there is my email address I wouldn't be surprised in fact if any of your employees at the N we can look you up right now make fun demo okay so looking
through here right we can already see that we've got clear text threads right that's it PL simple no more work other than that we've got passwords and all we did was clear their API and pull them down and there's quite a few of them here we can scroll up here we see those we still we got some hashes and some other stuff going on we'll get into that here in just a few moments but what I wanted to demonstrate here is there's a lot of risk in that because all Fone did was go out to the internet probably past bin download them pars and put into a database and now I've got this information okay so some serious risk in
using in in storing your passwords is clear text so what are some solutions well a solution I've seen is to use encryption all right let's encrypt our passwords in fact I saw somebody wearing a shirt any is the person here that wearing a wall of sheep shirt can you stand up for a sec read the back of your shirt what does it say somebody read it says encrypt or you'll regret it in the end that's a lot it should be used adaptive hashing functions or'll regret at the end and we'll get to that here in just a few minutes but encryption will get you owned we'll talk about that all right so what about encryption you can look
somewhat like this this is an example I seen in a mobile assessment that I did about a month and a half ago okay hey 120 bit the algorithm here the key is secret okay quick mention something real quick most of the time when I see encryption implemented in stor credential or credential storage systems it's using symmetric encryption rarely ever have I seen like I can't name this where I've seen asymmetric encryption used here which means we're dealing with an algorithm and a key right one private key and an algorithm okay so here we've got AES 128 and there's our key secret that is the actual key that was used as well right is that even is that less secure
than actual word secret it's the same it's close all right but you see here we've got our our pseudo code here we passing in our password our key to the encryption function it encrypts it and then encodes it and it sends it in protected now the reason why it encodes it right you don't have to do it this way like you can store binary data you can store binary data in your database however most of the times I see it's stored as plain text it's some sort of barar field within the database and so in order to do that they've got to encode it into something into a different form that is consumable by a plain text field and in
this particular case it's B 64 so here's an example of encoding versus encryption the encryption happens here all the encoding does is change it so it can be stored there but that's easily reversible back into its binary form okay so here we've got our binary belog encoded and stored in the database so what are some characteristics of this once again real simple simple path recovery system only slightly more complicated the fact that now you just have to reverse with key but they own the key right so you say hey I forgot my password the name of my first pet was uh like bear okay and it theyes s you your password your email so once again this
is still unsafe this is almost the equivalent of storing it in plain text from a from a from a protect on the server side standpoint we'll get to that here in just a moment okay so other characteristics here is you you have to be concerned with encryption key storage okay which have about that war here just a few minutes once again we got unpredictable resource requirements leading to L prescriptions because in most cases our cyer text is in some way related to the length of our plain text okay when we're dealing with encryption so we still have that problem that we have to deal with and what do we do we end up we end up loosening the
restrictions and creating weaker passwords as a result right something very very important about using encryption systems there are four elements to this okay your your security is based on both the algorithm that's used the cipher mode that's used the key storage system and the key itself the strength of the key itself and those are four items that we're going to revisit every time we talk about encrypting path password for for our for our database for our storage systems okay so what are some problems with this well you got the key you can do crypto credentials this depends on the level of access the level of compromise of the Target right so if I compromise the
server and all I have is SQL injection against the user table I may be able to pull the credit but I may not have access to the key but if I'm coming in through the network I'm looking for the key and I'm going to try to find out word store I'm going try to gain access to it if I've got access to the source code I'm going to try to find it hardcoded there a lot of different ways to approach that if that's not an Avenue of attack then maybe we can take advantage of weak algorithms or cyer Okay so let's let's jump over the solutions to that now let's talk about a case study anybody remember
this yeah largest largest data breach from a single Source in reported history now person some say uhuh Russia know released 1.2 billion last week well or last month that was 420,000 different sources of passwords okay single Source Adobe still the largest who who has a username that was in this Dum okay you get a book everybody was in this D right I know that he's not the only one there's only two people that raise their hand there probably about 90% of his room is in that um so huge huge huge password on okay and so what we're going to do is don't used encryption right they used encryption to store their passwords all right we're going to go through we're
going to break it down according to those four elements I talked about on the first slide and and kind of break down their their uh their issue and find out where it happened so first we want to look at the key components remember there's four of them key storage mechanism key strength the algorithm and the cipher mode well in terms of key mechanism and key strength they're unknowns to us okay now one thing that's really really interesting to me is that adobe claims that it was a sophisticated attack on the Netflix right and then it led to access of customer information and source code if I had that information I got the key if I if I got
this much access I'm not leaving without the key so either they didn't release the key or they didn't bother looking for it they just wanted to they just wanted to uh find Adobe all right which they did a pretty good job of okay so storage mechanisms unnown here because it wasn't disclosed kind of the same thing with the key they didn't disclose the key with ite didn't tell us what the key was and to my knowledge nowh at this point has actually cracked the key I'm not working on cracking the key what we're going to talk about is is kind of a different approach to cracking password Foria I'm not cracking the key if somebody wants to go for it that's
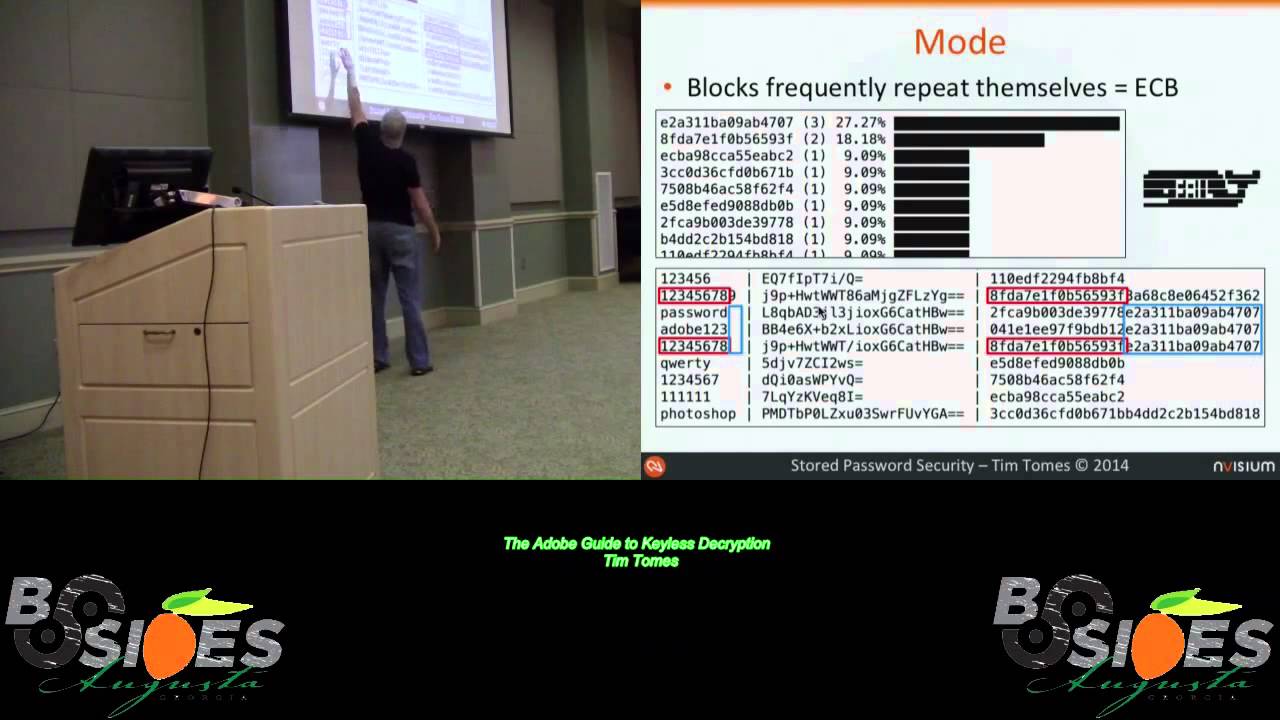
fine but at this point in time it's not been cracked we don't know about it so I'm going to assume it's a strong key so these two particular areas right here adob is doing all right we assume they're doing okay okay we've not found the problem yet so what about the algorithm okay well let's start to break these py Texs down to try to determine what the algorithm is you see right off the bat there's definitely some pattern here of recognition right the first thing we want to do is we want to break it down into heximal form and when we break it down in HEX decimal form we immediately see we got 16 looks like to
be 16 character blocks right in this particular case 16 characters is eight B because it's t a decimal Okay so we've got 8 byte blocks right 8 by blocks equal 64 bits and we have a couple of options when we talked about 64 Big Box fers Ida Dez and triple Dez so this is where we were at in determining the which algorithm was used when ad doe came out and said yes we were using triple death okay is it triple de is triple de still approved for use on the United States government absolutely it is right this approves in some cyppher modes not all of them but in some Cypher Cipher modes it is approved for use by
the United States government so what do I say this is not a Do's problem the algorithm is not an issue for a dope so they got three out of four right at this point okay they're doing okay so before we jump into what mode Adobe was using let's talk a little bit about modes all right so this is thing called electronic code book and then there's everything else all right electronic codebook is known as the raw mode or raw Cipher mode and the reason why is because there's absolutely no chaining involved and there's no initialization Vector you don't have to be a crypto person I'm going tell you where initialization Vector is it's Randomness that's
introduced to the encryption process to prevent information in the same information in appearing the same when it comes out okay so if I have random data going into all these kind of like salting a hash for those of you that we'll talk a little more about that here in a little while but it's Randomness going in that affects how each block along the chain looks okay right so it's completely wide open which means if I had the same separate cyer text in the first block different in the second and the same in the third right or plain text I'm sorry going in plain text in the first and the third and not the second well the cipher text of the first
and the third block are going to be the same and so I can start to see patterns in this right and if any of you seen um ECB mode uh encryption done on an image and what it looks like after it's been encrypted anybody look at an example of that it's wicked tool you can still see the image because all the patterns are still there the colors just change right so it's really really interesting this is bad okay so let's look at what adobe's doing doesn't take us long to find out that we've got repeating blocks this is the top 10 the top 10 uh passwords in the dump right here the top 10 most common typ in the dump broken
down next to death point and I broke took the blocks out and sorted them we can see we've got repeating blocks already we can actually look in the cyer text right here see 1 through eight is exactly the same block and then here which is our our M character padded out to eight to eight bytes is the same okay so we definitely we're working with ECB here and this is where we're going to bust Adobe in the forehead okay this is where their problem is so how we're going to crack this knowing you're using an ECB one out a quick note on this real quick Defenders got to be right 100% of the time right
attack is only got to be right once and this is our whole you did 75% of the way right this is why encryption is not the answer because there's a lot of moving parts you've got four different things that you're concerned about here and these these are just the the the upper level things when you start digging out each one of these you got to really know your stuff okay so here you've got four things that can go wrong it's more complex than it needs to be and we'll see moving forward but this is the problem this is how we're going to craft first you just select random CER Tex that you want that you want to attack or
doesn't have to be random could be your CEO right could be a Target at the NSA anyway then you go in and you analyze the hints well wait a second where do these hints come from guess what this breach included all the hints everybody's passwords Okay so we've got additional information baked into this particular breach that really helps us in attacking this Cypher text you can analyze hint in a couple ways you can look at the full cyer text okay we can just search the the dump for the full cyer text and look at all the hints associated with that full cyer text and try to break the whole thing at once however there's some Cipher text that
don't have hints right some some people just didn't put in there and so in order to break those what you can do is you can break them down into the individual blocks and then look at the hints for other password that use those blocks and then start to break apart chunks of the clip text all right and so you're going to see as we go through this demonstration here in a minute we have bits and pieces of passwords a lot of different passwords we have some that are full and then some that are bits in pieces and we can start to build this thing all right so as you guess when you look at the hand you start to guess the
plain text you start you go back in there you take all those new blocks you apply into all the passwords in the list you start unlocking chunks okay think of it as a huge Sudoku puzzle right or the world's largest Crawford puzzle as the uh as the famous cartoon like often put it all right I think see password so what does this mean right here first thing I did at enisum um was I like I was sitting one like I wonder if's get stuff out there pH this you know just foring around dumped it one credential one CR was the CEOs and it was was was in this one right here I didn't have any
blocks unlocked to to grip any of his to reverse his life point at that point so I went back Ed some of the hints from other people he did not put a hint in there was able to crack his password it was 12 characters emailed it to him and got an interesting email back the next day but you my line work that kind of stuff is somewhat encourage especially since I was already hired and I wasn't sending a mess said you need to hire me you're I'm going to Blackmail you you know it was it was fun and then for those of you that Know Jack minino who is the CEO here really cool guy but he
was good about it but that's how this attack goes down and so let's go ahead and run through a demo real quick of what that looks like so the first thing I want to do is let's go ahead and open up new terminal window s python inter let's import Adobe this is a python library that I wrote and I'll be open sourcing it after today as well I want to create an instance of my my class which does all the work for me can't do that without giving the name of the
database all right this quickly what what this particular uh Library does it allows you to crack hatches using uniper block so you give it a a Json dictionary cyer blocks o bracket um you can create a block database uh a Json block database based on all the stuff you've already uh all the pl Cy Tex you've already cracked within the database you can do the same thing to create a list of those hashes all right so you can see I not hashes but the cyppher text and the pl text you can create a list of those Jon list of those um you can get the hints for particular cyer attex you can also get the hints for pieces of it
I'll show you how to do that here in just a minute you can run a statistics Gathering method against the database itself and then of course you have the ability to update has you actually crack the pl text so let's go back now and let's pick a let's pick a Target and I need to find out I actually picked somebody already and I need to know who this is give me just a second because I went through and found one that worked out well okay his name is Haans or that's at least what his uh email address start to show credentials let's go in here and let's scroll up to Mr H HS where we at okay H there we go right
here this is the got all right here's his base 64 encoded uh password so what we want to do is we want to reverse this thing here okay this is what we're interested in let's go back over here and we'll do our C.G hint and we'll type in the entire Cypher text and hit enter and it's going to go into the database it's going to pull out all the hints that are related to that particular Cypher text and there's 3,277 hits there okay so we start looking down the hint what do we notice immediately right and and I know that I went through and I kind of cherry-pick one but it only took me four tries to
find this one literally about 50% of them are this easy to crack right 1 2 3 4 5 6 twice 1 through six two one through six twice that's the top of the list let's go down to the bottom and see if the hints get any better right 1 2 3 4 5 6 * two if you speak Spanish please prob these probably says the same thing memo 1 2 3 4 5 6 1 2 3 4 5 6 do you know how often the actual password is the hint like pretty often I actually want to go through and do some statistics on that because I had found in most cases there are multiple hints
within the hint list that actually are the password themselves so it's pretty interesting so we're guys has 1 2 3 4 5 6 1 2 3 4 5 6 right once we know that we can do c what was it I can't remember name method was C do update hash see
update put that in there 1 2 3 four five six 1 2 3 four five six that looks right doesn't it update hash now once I've updated the hash the database is now that Cypher text is cracked what I do now is I run the the G blocks database and what that will do is is that will go in it will take every single Cipher Tech that's been broken down in the plane text it'll separate out in the heximal characters it will take that block assign it to plain text and write it to a Json file and so I now have a Json file once I do that it take about 15 minutes to run it
here so I'm not going to do it but once I did that you would have a blocks. Json file right that's got all those blocks in it so what did we do with that well we wrote a module for Recon NG that takes that Block's database right it goes through your credentials table fills out all of the Adobe Cipher text right and then it takes the block database it applies it to it and TR passwords okay so let's go ahead and look at that now so if I go here to Recon NG I'm going to load adob show info block database is already there I distribute this with Recon NG I've been kind of quiet about it but I
added this about a month and a half ago and I've been updating the block database as I crack more passwords all right and so let's go ahead and run this and see what it does right so we see right off the back most of these you see a lot of as here I'll talk about that here in just a second some of these were not cracked those that were partially cracked you'll see blue um with some information like here you see a unknown block a ped block plus a nine and then down here you see we actually have some of the clear text ones at are crack really really really basic ones so what does this mean here
uh the eight asps means that I can confirm I can confirm that that the length of the password is eight characters even though I don't know any of the plan Tex within that block because it ended with that no bik and then padded it out to that second block and that's common throughout the entire database so it's really easy to determine when I have an eight length passw a 16 length password a 24 car length password so on and so forth all right so I'm starting to track passwords now because they use the wrong mode okay that's all it takes one little slip up and now you got somebody busting busting up the passwords so let's go back over here to
the uh the presentation now and continue on with this so what are some solutions to this one use a strong key right Adobe did that didn't work out so well for them number two store the key in a secure yet accessible location this is really really hard to do has anybody tried to do this before I mean were you successful no and I'll tell you what it's I I only I only say it's not impossible because I'm I I don't believe in absolutes in security I just simply don't every time you say it's impossible somebody does it right and then they rub your face and it's I'm not going to do that I'm not going to
say it's impossible but I will tell you that every single mobile assessment I do they try to hide something on on on the phone they try to hide a key somewhere you can put it in the key chain you can put it anywhere you want but if I jailbreak that device I own it and I can get any piece of data I want off of it and I've never seen a a key stored in a way where I couldn't break it if I was able to escalate privilege okay this is hard to do it doesn't it's not as easy to sound it's top okay next thing is use cryptographically strong algorithms and cyer modes together okay if you can do
all four of those things you might be in decent shape but it's difficult why not just hash your passwords hashing is so much simpler okay still off the B it's simple here my stud code I pass the password a hat algorithm I got a protected form bam I slam it into my database it's that simple okay but is it really that simple let's talk a little bit more about the characteristics of this storage system okay there is no password recovery system remember hashing is irreversible cryptographically irreversible I should say cryptographically irreversible because we can guess things right we can guess plain Tech hash it compare it and try to crack it that way but cryptographically they're supposed to be
irreversible which means you cannot use the algorithm to unhash it okay so therefore we can't recover the password and we have but we can design a reset system and this a little bit more complex than a recovery system because it involves you someone authenticating themselves in some way in order to reset their password okay but there is a way to do that it's just a little bit safer because now we're out recovering the original text predictable resource requirements finally we have some predictable resource requirements and the reason being is because hashes have what fixed length output right no matter what you cram in it's always going to be the same length on the output so now you can have
10 gab passord guess what US sh one is going to be 4 so you know you got predictable length out output here so you know what your resource requirements need to be based on how big your user table is going to be and therefore you can allow limited like passwords any character you want as long as you're you know not vulnerable to objection right be smart about how you develop the system but basically unlimited length passwords here this is a much better solution in terms of password strengths here and once again the results should be cryptographically irreversible so what are some of the problems we have well all I got to do is create one lookup table for the hatching
algorithm you're using and then I can track passwords with I can try to reverse those not cryptographically but I can just create this huge table that takes every possible value between zero alone and you know whatever the word is at the end of a 50 character rainbow table right create this huge lookup table and then apply it to your hatches and reverse them that way okay the other thing is these types of hashes are likely indexed by search engines or collected by hash collectors and we'll talk more about that here in just a moment what's a good example of this right here strap four December 2012 they have their password 860,000 of them were to Clos were just closed to the internet
do you think there was any risk in those being reversed absolutely there was I'm going to show you right now all right so let's do it what does this look like going back into Recon NG I want to show actually let just do this so we got four module actually three additional modules other than the Adobe module that works on cracking credits all right booc cra.org and Le DB all right booc anybody heard of P booc it's python script that came out earlier this year that says hey you know what's really funny you can like search Google for a hatch and then take every word in the HTML response hash it compare it to what you search for and Google will tell
you it knows about the solution to that hash great idea but you're only implementing nd5 I took that and I implemented I implemented every single hashing algorithm that python supports it goes through it searches Google for that hash it takes the HTML it parses out every single word in the response hashes them all and Compares it and tries to find out if Google knows about about that particular hatch the what the plain text is right so we got that one that does it that way search engines and then hashes thator and Leb are hash collects so when people crack hashes they can submit them to these resources here I'm pretty sure these guys are also
doing some hash cracking in the background on their own right and since there's no salt involved it's going to if we hash it locally or they hash it there the uh the output is the same right so we can go and we can look at their we use their API to act to actually look up the cyer or the hash and sorry look up the hash to see if they know what the plane text is so let's run a couple of these modules uh first one I want to run is the boo track
module this one takes a little bit longer because it's having to do all that hashing and comparing for every single word that in the result so we'll let it find one of the results just to kind of show you that it does work and then we'll move on to some of the other modules there we go right found one there pretty cool right we got one way we can reverse these hashes and by the way these hashes are all coming from that the credit database all right it's pulling all of those all all everything recognizes as a hash from that credit database and it's now using those as input for this particular module so let's load uh let's do week DV
next on this one these are much much quicker the API are a little
better IND all right so Leb about one additional one let's load hash.org on this one this API is really good it let's you submit 20 at a time bam he busting these things open what does this tell you right here when you start seeing results like this that tell you anything randomly generated password probably on on behalf of the user but this guys probably cracking hatches in the background these are all short enough that he's probably got a look up table and he's looking up your hatches I would almost guarantee it yeah either that or there by some off chance these are all collisions which I highly doubt right but it's possibility that they're all collisions and they're using some
sort of salt right some sort of Sal attachment but I doubt it's probably for them and the user use random password so this is the risk you might have passed your passwords but I can still find the plain touch with some of those okay so we still have a risk here we're still not we're still not uh we're still not to immune from Attack so let's continue moving on here out of time so what's our solution here let's try salted hashes salted hashes a little bit different we're introducing some Randomness into the hashing process um to solve a couple of problems this is what the pseudo code looks like for that so what are some characteristics of
this well it shares all the same characteristics as your as your previous hashing as hatching does except it adds some new some new things to one theoretically safe from repon and G so if I'm hashing right if I'm salting my hashes there's probably a decent chance that no one else out there that's creating hash tables and making them available is using the same exact salt that I am I've not encountered any API that says hey so me your salt and the hash we're doing all this in the background I've never seen any of that so theoretically it's safe in the Recon NG style attack that I've been conducting okay the number two it conce it conceals identical passwords and we
call this parallelism so what does that mean remember hashes same input equals the same output so if I crack a data if I break into a database and I dump and I dump the contents of it and I see this person uses this hash and his password is this I can look for all the instances of that same hash and know that person's password well this prevents that now as long as we're using unique salts because you can have the same password but as long as your salt is different when it gets folded into that hatch the result is different and therefore we have no parallelism in terms of what the clear text of the password is so those are
really important distinctions okay what's the problem here well you have one look of table per per salt used so if you're not using unique salts this is a problem how many people here have seen this implemented where the where the where the developer used the same salt for password is that more or less the same as hat same right the same thing if I got the Hat that's super easy right also algorithms such as sh1 N5 the ones we see typically used here those are designed for Speed right as has are designed for Speed which makes the offline attacks much more effective against those particular algorithms so an example we have here I have no idea
how to pronounce this I didn't even looked it up I can't figure it out right but they're the developers of the Cydia project for those of you that have deal with iPhone jailbreaking you're probably familiar with Cydia 2014 this particular this year a couple months ago they got reached 100,000 accounts were dumped and I've not found an instance where that any of those pathwords were were cracked right any of those Su hatches were cracked however it's still possible it's still possible because we can still conduct offline attacks against them so what what are some solutions to this problem well make sure each salt is unique right and make sure this salt is cryptographically random right that's
one solution to this particular problem and if we're doing that we're in pretty good shape but we still have that speed problem so the solution to the speed problem is using adaptive hashing functions so what does adapting hashing functions look like okay well we got some once again we got an algorithm we got a salt so we're we're preventing that uh that parallelism by using Assa salt right and then we introduced this new this new uh this new Factor called rounds rounds okay and this is where work Factor comes in I'll talk about work Factor here in just a minute as you can see our hashing function it takes the B takes us off takes the rounds and
it gives us this nice uh this nice uh clear text value we can store in our database and it does it slowly right which is really really nice what we're after now how do we break this down you can see there's definely some information in here we can pull out of this the first bit um the dollar sign is delimer here the two a that's the version of BCP that was used so version two alpha of BCP the number of rounds here 12 and then the first 22 characters of the hash itself is the salt and then the remainder of it is the actual result of the hashing function all of this information it's okay that they know
that it's okay that they know this right because of that salt you're still going to have a more difficult they still going to have to have a separate lookup table for every single one of these hatches but because we're using um a slow hatching function an Adaptive hatching function as 12 rounds it's slow enough where it makes offline attacks unreasonable okay what are some characteristics of this well the dynamic thing increases the work trer so the rounds thing is extremely important okay every all of our web servers or wherever you're storing this information wherever this wherever these hashes are being uh where this hashing function is actually running right it's going to have different resources than say another
server so what you have to do is you have to tune these things so that they take just as much time to make it a problem for people that are trying to hack these things offline right so you make it slow enough that it affects those people but fast enough that doesn't mess with the user experience so if you go to log in you click submit and it takes a second for it to go back do the hashing function and respond does that bother you as a user no that's thought it's fairly unnoticeable to a user but to somebody that's trying to crack ashes that is all day right that just I mean it destroys their ability to
conduct an offline attack against this so you have to tune the the number of rounds based on the function that you're using because there's three different adaptive hatch functions um and I encourage you to go out and research those you have to tune it so that it does it works optimally on your configuration okay but that's that's the main difference between the hatches solt hatches and now the Adaptive hatching functions so what are some problems here well support not all of our not all of our programming languages support this support these uh readily so um that may be an issue for you depending on what language you're working in or perhaps you could write one right and if you're
not a crypto guy don't don't don't don't do that at least um dictionary attacks against passwords so the thing about this is every single every single method we've looked at thus far is still susceptible to offline taxs so we've gotten slower and we've made it harder but offline attacks are still possible because even though it's slow I can take a reasonably decent dictionary I can use your VP with your 12 rounds or whatever it is and I can still try to crack passws and I may or may not be successful but it's still a valid attack right well there's only one solution to this and that's ball and chain and I'm not going to tell you what ball and
chain is today because two weeks two week from now Deron a guy named Benjamin dony and myself are going to release a technique that's going to change all of us it's going to make offline attacks against F completely impossible and we're hoping that revolutionizes uh information security from an apte standpoint so if you can be there awesome if not it's okay check out the video if you don't go because this is some serious stuff it's all B Benjamin non only came up with the technique I'm just helping them Market it but this is going to be the solution moving forward if you're not until until two weeks from now do this okay until two weeks from
now use your D hatching functions and then two weeks now you Vol and chain okay but the point is the point here is there's still not a perfect solution but we're working on it and we're trying to get there okay so here's some statistics about what is I went in po I said show me all the information about all the dumps you got I want to run some stack on it so that's September 4th um this is what this is what it shows me in terms of the types of uh the types of storage that's being done against the pord databases and so far we can see that these obsolete fast hatching algorithms are used a lot right I mean look at all
these mv5 and the Shaws those are fast hatching algorithms and they're being used quite frequently which tells us what that people don't understand the purpose of those hatching functions those hases those hatching functions are are designed to be quick we want to slow the process down so we can prevent offline it fast right and so then we go look say well who's doing it right then well there's two people in thousands of them there's two people using B no one's using script and no one's using the other one which is a couple different letters to start with PD I think but anyway I can't remember the name of the function itself I never can but there's
three popular ones there's only two people that are actually applying that and if you look at the thousands of blanks like you see the one dash up there you see the blanks you see this na right here of those thousands those fall either under the sulfate category the plain text category or unknown and I don't know what unknown means but I think an unknown means probably PL text okay and so I did a search of all those thousands to find out how many times Salt showed up in the description and it was 30 times which means most of those thousands of dumps are clear test right this is still a problem it's not getting any better this was a couple this is you
know just a week ago or so right so this is a huge problem and and we've got to fix this moving forward all right to summarize all right encoding is not encryption is not hashing got to teach your developers this stuff and if your developers you got to go and learn this stuff all right this is critical because it's going to come it's going to factor in how you implement these systems okay use a different random Sals and slow hatching functions when you're storing credentials okay until next week this is the way you need to do it all right and then if you don't feel likeing ball and chain continue to do it this way because
it's the safest of our other available options right help me reverse Adobe cyer blocks I'm going to put the database on USB stick all right if you want it it's about nine gigs if you want it I'll provide that database to you so you can help me start cracking these things all I ask is that you run that create blocks DB method and shoot me the block blocks that you crack all right um so we can talk more about that addressing individually if you're interested in doing that um attend Geron if you can for the release of ball and chain that would be really really cool and always design your password storing systems assuming that it's eventually going to
get compromised all right always do that if you're doing that then at least you're approaching it with a right mindset okay so that wraps it up for today thank you guys for coming and