Hacking Rants (from an almost old guy)

Show transcript [en]
good afternoon everyone look excited this is right after lunch okay this is the rantings of an almost old guy because you know none of us are ever going to be old not in this field this is basically 30 years plus of my experience and as we get to the end of this you'll realize that nothing's really changed nothing's really new but actually understanding some of the core values we have in security and why again things haven't changed might help you with your career and i also have some career recommendations towards the end and also some futures that we're going to look forward to to maybe hack so who am i i'm an asker of questions and a question
of answers yes i i when somebody has a question i'll answer it but then i'll have additional questions and that becomes very interesting um i've explored physical psychological virtual and spiritual spaces yeah okay i've never talked about the last couple um consumer of hardware software wet wear standards and interpretation of standards code documents and presentations what i'm saying is i do deep dives on technology a couple nights ago i couldn't sleep so i started rereading the ntp standard and then found some really cool reference documents and then spent the next three hours doing this and my girlfriend tolerates this i don't know why but you know that's how it goes um i've actually been part of ieee
standards creation uh ietf standards military standards blah blah blah so it's pretty interesting and also in a gather of a lot of information knowledge interpreting that's one of the fun things that somebody has a long view like jack and i as you can see trends occur not just today but things that happen tomorrow and the next year and the following year and things like that which by the way all makes me a hacker at least according to current definitions so in the beginning i have been interviewing people that are my age group and i said so what got you excited to get into this field did you know most of us did magic mitnick says magic was the one thing
that he thought was pretty cool especially as he started implementing or playing with technology he realized it's magic too because nobody actually uses understands it um most of us got code and cipher crackers if you talk to anybody's doing crypto early in your life they did that most of us got access to this kind of stuff and started playing and this kind of stuff and then this stuff to actually ask us to teach about photography and other things this was you know 50 60s and 70s kind of technology that we were looking at so i was motivated by two television shows back at that point one was called it takes a thief and one's called wild wild west and
during both of them they actually showed that people could get through doors and you know being nine years old i went nobody could get through doors but they had these little pieces of metal and they had these little pieces of plastic so i went after a door that looks very similar to this and i wiggled and i wobbled and you know several hours later i got in i went hmm this is pretty cool is it repeatable can i do it again at that age and yes i did i went this is pretty cool so i started looking at other doors and started questioning other doors um again figuring out how to do it with these based on these video
presentations that really didn't go into the details of them but i started you know inquiring about this and yes i learned about running around different spaces i probably didn't say do not enter but probably shouldn't have been there lessons learned um if you have enough time you can get into anything and you can figure out what the tools are you can get into anything does anything changed today nope um security is only good as as the specifications the installation and the interest of management and the maintainers to maintain that security has anything changed since then no um and really this is something i actually does anybody have kids am i planning to have kids everybody
practicing to have kids no just kidding um so one of the things that now i teach kids i've been part of hack kid and some of the other events is to learn how to lockpick why is that we create this mental barrier about what that magic key means to us we can't get in the house without that particular magic key once a kid actually is taught that there are no limitations except for your time and effort they start thinking like a hacker which becomes very interesting because then they will get involved in technical and learn how to program and they just start you know doing some really amazing things but i teach this on a regular basis when i
get a chance to sit down with kids and even adults i had a friend of mine she's almost my age and i had a two pin lock and i showed her how to pop the lock and she went no this is impossible so i get a call from her that she got locked out of a house that she had rented in alabama and she just basically picked the lock and got in and her sisters and stuff were locked out too so she got in and they went your magic you're amazing things haven't changed in this technology they really haven't so my first hack a primus computer yes i had to play with these these were really cruel
hanging chads were just not a problem because it was a lot you basically had to make sure it was poked in and this was the terminal or equivalent to the terminal that i used and this was the gear that i ended up playing with well there was this game there was this television stoke called star trek and i went this is really cool and i got to they loaded the software on this computer this computer by the way only had a whole 16 meg worth of hard drive and that was really really expensive and it had 32k of ram okay so i started mucking with it and i realized that i was losing i don't
like to lose so i started mucking with a little bit more and i found out that i could change the code which was an undocumented feature and i changed the code so i had dot ethereum crystals every time so i pressed a button i had extra power life was good i beat it well then i went to the system admins and i said look what i did this is really cool have you ever gone to somebody and told them they have a vulnerability that first look on that face is you know amazement and then they're appalled that you mess with their system and then they're angry that you mess with their system well they were the
whole thing and then they made me responsible for the security of the system no good deed goes unpunished so some of the lessons motivated people can compromise systems in this particular case i found the application was running as administrator because there wasn't any concept of administrator and non-administrator on the system how many people still run their operating systems with admin privileges as a user it's a big problem nothing's changed and also the application had a back door apparently some kind person from the university that created this put it back doors so they could get dilithium crystals that was after reading the rest of the code so again things haven't changed okay the ex-girlfriend i won't go into
the details but she became an ex-girlfriend and i realized that at that point again this is years ago anybody want to figure out the year 78 1978. so um i was really young i had hair then it was anyway we won't go into that i had not all this extra padding you know it takes some time to get um so i realized that we all had presentations to give and they gave us the default pattern for passwords and i went oh this is pretty cool oh crap everybody can use it so i figured out the pattern that was kind of cool and then i said you know it would be far more fun to collect
passwords if i just wrote a script that said login password and then i died so i went around all the little screens and did that and i collected everybody's password including the ex-girlfriend and then i realized that there's login scripts does anybody use linux login scripts and logout scripts scripts i realized i could do things i was kind of angry with her because i caught her and everything else with somebody so every time she logged out it took her code and modified her code okay that was not really nice of me but i was kind of young and stupid and things like that so anyway she dropped out of the class i don't understand her none of her
programs seem to work so lessons learned again default well-known passwords can be compromised have we solved this problem today anybody anybody no we haven't okay um startup and shutdown scripts can be evil can't they anybody if we fix that yet um how about backup do we back up our software to a backup manager or offline any you know do we still do that do we have policies to do that do we make sure our people do this and not quite so things still haven't changed then ha ha i started working for a company that did these and did these and did these and did these and i went these have got to be secure they're
physical systems they could hurt people right so i got access to a couple of these and i realized the coding was only eight bits 256 potential options wow that would be really hard to flip the little switches but what if i took some electronics and took a 555 chip and a serial to parallel 8-bit converter and now i could press a button and actually would count all all of those bits it would count up and it would send enough signals to open everything right well it worked really well sorry um it worked really well i was able to open these and open these and open these and these two i went and talked to all the vendors
they had the same response which was interesting we were able to solve some of the problems i also at the time i also found physically these card readers had relay switches that nobody ever thought if they took their hand and went pop the relays would close and the gate would open okay so they had to remount them and change the the chipsets and things that the relays and stuff like that um the same thing with with the stops here and the stops here so physically this stuff hasn't changed a lot yes okay now they have some crypto code here so that's solved but have they solved the rest of these internet of things problems i don't know have investigated them
since 1981 has any this changed now some lessons learned access to radio transmitters should be restricted well anybody use software to find radios okay uh when applying uh radio receiver problems uh you need to look at safety and security you shouldn't basically just throw wireless on something if there's safety and security involved how many systems involved today safety and security have you taken a look at the car to car communications enough said okay security cards because they have to be secure too because we know that somebody took the time and the effort to make sure that nobody could actually open any of this stuff okay well i got a call from a customer and the customer said
we've got this card it didn't have the little dots on it and we don't know because they had taken off the little badge thing here we don't know what the code is so we can order these cards to let people in and out of this well-known building that maybe be managed by the federal government you know can you have somebody take a look at it this is 82. at that point they were so cool with the technology these were actually embedded magnets so i took a plus and a minus magnet and i flipped it around to figure out and put a little magic marker on each to figure out what was plus or minus and then i punched them out and i um
figured out where all the dots would have been and i created all this magnet thing so i was able to actually take this card and create any type of to replicate any type of card available even found another card that had a minor change and i found out was a facility code was able to do it and the customer was kind enough to thank us because they paid us and they were able to get their cards okay anybody see any change to this with say bar code or any of the other reader technology we have today so obviously indicators the security lead to questions each of the places on the card had bumps and i went there's bumps here there's
something's got to be hiding in here so after taking a couple cards uh away we flipped around we found problems um also the cost of technology is becoming less expensive therefore tackings attacks are increasing we're seeing this with everything today apparently there is no model that currently exists unless somebody knows of it when i implemented technology when's the estimate of the cost of that technology going to decrease to the point that every consumer has access to it there is no system currently automobiles anything that moves any of the other technology this is a this is a big problem this isn't even part of when we specify the system when do we estimate this technology is going to become
cheaper so again more lessons we haven't learned okay then i got to play with physical security again with another company i got to learn how to muck with these and these and these and these and yes those too learned a lot of about these systems many of the systems had coding problems that they had never tested they had back doors in them that nobody actually found until you started reading the documentation we also found these devices didn't have the accuracy that they expected if i had 60 numbers on something and i was turning it it was 60 plus or minus one digit okay that's kind of disturbing when you're expecting six to a resolution of sixty and you find out
it has one sixth for one third that resolution when i remember the numbers okay again no expectations or you're supposed to have expectations of what the security means but it doesn't and yes i went to several banks and this is what i found okay they were big tube monitors but basically cameras behind tube monitors this actually exists in in nature well in our buildings so oh yes and this the one of the installers of one of these systems was kind enough to put the electrical box here and leave it unsecured okay and one of the installers of this use scotch tape to connect everything okay um so from a security standpoint the product guides contain default
everything maintainers have little time you're supposed to go touch x amount of products per day or x amount of customers per day you don't have a chance to actually spend time and clean this stuff up so after generations and generations of just plugging this stuff in you find all kind of problems and the maintainers and companies don't control access we keep on seeing default passwords for physical security systems discovered in every product that's out there okay again things haven't changed is this useful for you guys to actually see that this uh this technology ah mainframes yes indeed they were fun this was 86. so i was doing a cobalt program and we were supposed to play with
recursion which means that you know you're supposed to go so far and have an end point well i asked the question what would happen if i never stopped when i was calculating that's when i learned about ddosing cpus they were very unhappy they had to reboot they were very unhappy um apparently the way it was configured there was not a default endpoint that it would put in there was no there was no end point for this and every user was running as trusted user it wasn't actually a non-trusted user space so that was a real problem so lessons learned yes any language can do recursion including cobol and yes you can ddos if you allow the
trusted space access so then wow i found out the mainframe had networking what the heck was that we had sna we were connected to the global s a network well i received an email i went wow this is pretty cool and it's not even from our facility and i opened it up and it was a challenge it said if you're a male or you're a female please take this test we're doing data collection well this was pretty cool and they had some really obscene obnoxious questions yes or no yes or no yes or no and then you would press the send well yes malware i learned about malware and that year the result of this malware is a ddos the
receiving systems email server which took down another facility's email server that was really bad because it filled their storage and anyway so yes malware exists on all systems and can be used for ddos this was 85. mainframe again wow so after doing all this stuff the professor said you know you're going to have to knock my socks off to get a really good grade after which you've you know what we found so far you're going to have to knock my socks off and i went okay so i started looking for books and manuals trying to come up with a new idea of what i can do well i found this set of codes that allowed me to walk memory
from the very top to the very bottom and i realized that they were all producing their finals on the computer at that time this can't be a problem right so my deliverable was the code to walk memory and what the finals were for three of the um professors programs again they were a little bit angry but what they ended up learning was again non-trusted memory um yes and i got put was responsible for the security of this system too again unpunished again this there was no laws at this time so we had unauthorized access to memory space causes disclosure and yes i really hate x edit although i use vi today so i'm not sure
what that says about me so uh in 86 we found that guess what there was this 3b in there i'd been playing with fortunes at home somebody actually dropped off a fortune computer an old bsd and playing with it and having a great time and yes this is what it looked like yeah this was visicalc anybody remember visit calc okay we know you're old well this is what a 3b look like well after discovering some things the power button actually did an init six it actually rebooted actually press it called the script for a knit six and i went that's pretty cool what other init levels are there so i started exploring that and then i found the etsy password
file that point the etsy password file wasn't encrypted there was no shadow file so i didn't look through the passwords i went i wonder if the password patterns were guessable and yes they were guessable real big problem and then i got early access to internet in 86. i was hooked okay so i've been on the internet since 86 learning exploring looking at the networks trying to get people to fix things very interesting so yeah the algorithms that we create still are guessable i'm sorry five characters are eight characters one upper and lower case you know use a word that's easy to remember we have dictionary attacks that we've been using for years nothing's changed we have to change this
process the only thing that's changed by the way remember i told you about the primo system where i was able to put a script up to look for logins on unix this year we were able to hold down the control alt delete and it forced a reboot of the system so i could kill all the actual applications the the console so if any programs were running instead of me having direct access to a login screen that changed so that was that was really really cool ah yes defcon yeah i started doing defcon well somebody put up a wireless sniffer this was 2000. yeah there was a lot of things that happened in the 90s i won't go into
those things like capture the flag on our own computers which led to things like people finding a vulnerability in solaris box that allows you to run sounds to somebody else's solaris box so as a joke these guys um started doing this as i'm sitting there coding but they send godzilla stuff to it so i'd hear i get up anybody you know what's going on at the same time they thought it was funny because they took my lock and they turned it backwards so i had to knock on the door to get out okay so you know hackers do interesting things we also played capture the flag based on the core wars um code that came out so we'd basically
try to destroy a system again these were our systems that we were using and we made them unusable you'd have to reload them which took a lot of time at this point okay so um there were a lot of crazy antics and things like that that we learned about computers we've learned um x windows had back doors has anybody looked at the x windows back doors that still exist there's a lot of them okay we saw shell shock at this point i was creating websites in 92 93 and as one of my capture the flag things somebody went into that and changed my variables my environmental variables and got access to my system that vulnerabilities existed for years
okay and it's existed in every shell the problem with it is my big mistake is i didn't validate variables coming into the system okay there's a lot of those things that the old guys like myself well almost old guys wait a second i think you're older than me so i can call you the old guy just kidding so this has existed for a very very long time for the defcon things early on 2000 2001 we started seeing people sniffing traffic well these guys were sniffing traffic and they said hey this is kind of fun but we need to document this some way and get their pictures so i ran over and grabbed a whole bunch
of paper plates and we started taping paper plates up and writing the username passwords and where they were going on these and then we were running around and trying to find each of these people so we could get a picture of them clear text wireless remember i said wireless is bad if you don't understand it um and we were running around and doing this we had a ball doing this okay so again wireless can be you know kind of dangerous we also saw this van that had apparently cameras and stuff in it that were facing out to watch people we found that yellow sticky notes all over that van made it look like a big canary
okay so you know that was kind of interesting and uh another strange story does anybody know fx the felix okay again a strange hack we went to a hotel a hotel similar to this and we walked in with 24 packs of beer and we sat right down in the lobby what do they do when you have 24 packs of beer in the lobby they say sirs you can't have that in here so with fx and a whole bunch of us sitting in a lexus park we checked them as if they were baggage then anybody wanted a beer would have to go check our bags they would take a little slip so we had the bag guy being
our bartender okay so again out of the box thinking is real important i was also at pool three and this young lady decided that she wanted to go for a swim but she didn't she only had panties on she didn't well anyway so we use the badges we turn it into a bikini top and again defcon is a good place to it's a security conference that allows you to be real creative meet a lot of people challenge yourself i'm just not giving you the code stuff that i did or the other things i'm trying to give you the social engineering stuff because it's been kind of cool and yes so you have to really challenge yourself
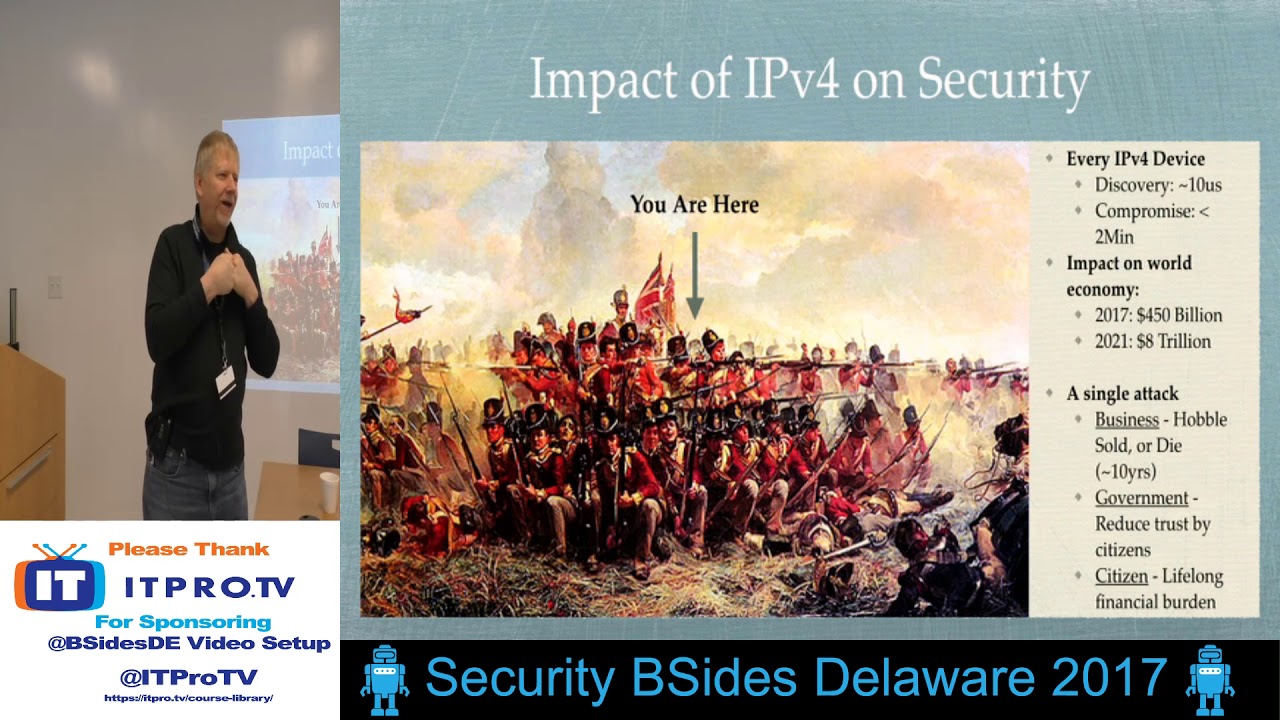
with this technology you have to ask questions you have to you know go beyond the biggest question i learned was these two guys had this thing called ipv6 and you've probably heard me talk about ipv6 before and i had yeah shut up um i've been focused on this for 14 years i've been focused on is because these two guys challenged me we were sitting at dinner and they were saying we can do this with ipv6 i said well i broke that let me show you how i broke that and after three four times what they said is hey joe you're evil really um so i said so what do you propose he says why don't
you figure out how to fix ipv6 so the last 14 years i've been spending my time i have done almost 1500 presentations during that time a lot of them in the last four years i've taught classes i've written rfcs i've done all kind of crazy stuff i thought i actually could make a difference in this domain with this technology i'm not sure if i have but i learned a couple lessons and again this still touches what we do today the ability to fix a technology no matter what the technology is um is at odds with management goals for the corporations that you are in and the products that are being sold until somebody is embarrassed
okay fx talks about this in a recent presentation is that we went from full disclosure which embarrassed the company to fix things to responsible disclosure which gave the vendors the capability of waiting in some cases up to 13 years to fix vulnerabilities can you imagine how long we were all at risk from a network attack for 13 years this vendor hasn't told you they fixed it two years ago okay that now we have gone to the third mode which is the vendors these billion dollar vendors are going please help us for free or pittance but on the other side a lot of people are now saying you know these are billion dollar companies they should at least pay you
know comparable rates to do this stuff some of us are now turning around and actually just selling these vulnerabilities so we've actually gone down a really bad road in this domain right now to protect people from corporations from being embarrassed you know so be aware that we're seeing a lot of fighting and arguing in this field some people may believe that one of the three will happen or it's best for whomever but if you spend 150 hours finding a vulnerability and then you get a call from a vendor hey can you come in and for your time and free can you tell us how this is fixed does that have any return on investment for you guys
okay especially if maybe they only give you 100 bucks okay and they don't pay you for your flight or anything else so this is a real frustrating thing for for many of us at this point so this is basically a lesson i guess we as an industry still haven't learned is some of us really want to fix this stuff you know how many have actually gone to a vendor to try to fix this stuff yeah uh the current cost of a vulnerability if you're a researcher and it's embarrassing it could cost you ninety thousand dollars in legal fees if you disclose this or you can get a hundred dollars if they find out that you know they like your
vulnerability so anyway this is this is a disturbing lesson that i'm still dealing with also your future gmark's a friend this is actually a card that gmark put together about this field about your career in this field and i just thought it was a good thing to reflect to he spoke at this at tor con five six years ago but you know ask questions you're expected to ask questions in this field no matter who it is ask me questions i mean challenge me please on whatever i know i get better you get better um don't wait for perfection put technology out and have it tested by people that are trusted do something write something just go out
and do it i'm sorry it's probably trademarked sorry erase that piece um become a master at something find something you're passionate about my ipv6 stuff go out and challenge yourself to become you know it may be knowing the 853 where i can actually say you know n23 or n12 and you'll actually know what it is and you can actually solve that particular problem you know have the solutions for that um visualize everything never disqualify yourself if you come in here and you see a wireless challenge you've never done wireless go to the wireless challenge try it out this community is very supportive of you guys learning stuff you know no matter what it is go learn
it go try it you may find it's a passion you may find it it's kind of cool when you can have a discussion with people about what some of the problems are just go out and do it i mean who knows maybe you could car hack um let's see challenge your limitations have a vision write it down go go forward with it speak at every chance you get one of the big things i do it meant for my mentoring for people that i've chosen to mentor is go out and teach them how to speak support them how to speak if you find if you're somebody that wants to mentor this is really important have friends that are
now well known in most fields and csos that have basically poked at them for a couple years to finally speak to to actually challenge themselves to do this and now they're well recognized you know so and also for yourself go challenge yourself go take a friggin um a toastmasters class get comfortable with it people want to kill themselves to get up on this stage it's kind of fun look you get all this space you can walk around um and you can talk and rant it's good so go challenge yourself to do that um be flexible and high be passionate about it obviously you can see i'm really passionate about this stuff um i actually gave a what four-hour
presentation last friday on minimal sleep and people said how do you get all that energy it's coffee you know 20 minutes of sleep coffee um choose between tech and management i've i found that as a mistake that i made for a while it was management and then i realized that they get rid of management managers get rid of other managers but they never get rid of techs so be aware that you have trade-offs you have to make do something bigger than yourself go get involved in one of the hacker spaces nova labs is doing some really amazing things right now same thing with hack dc go go get involved in those and learn some things
have that vision don't save the less for the best i am a little bit older i'm still out there doing really fun things with kids to kids and younger people and things like that to learn i mean get out here and continue doing this and enjoy life i mean this is fun stuff so that's career recommendation one career recommendation two here's your challenge if you choose to accept it this is the internet of broke things all of these things are already broke i've tested a lot of these things i've said holy crap to what my findings have been each one of these and by the way this is just i t this is what all we've been
doing up to this point most of us each of these technologies have major problems we've seen presentations that on and on for the last four years five years on scada devices of compromises that are available in all of these things go out and challenge yourself become a subject matter expert on this stuff learn how to protect it learn how to attack it learn how to protect it we've got to actually fix this technology because you know transportation health systems industrial these are all people's lives not just one of us but all of us okay go challenge yourself lastly defense in depth it's such a cute wonderful little thing for the cissp but honestly insanity is called doing the same thing
again and again and expecting different results we put up a firewall we get attacked we put up anti-malware we get attacked the technology ages very quickly so essentially the turtle yeah it's your network and systems it sits still it doesn't move it's got all its things in hiding you know the the um guillotine operator that's the attacker they always win right now i'm tired of doing that okay so i've been red team and it makes it too easy to win i actually want to see us win on the defense for a change the guild team is really a lot of automation we're now seeing things that we used to 30 years ago somebody would sit at a console
now we're automating those scripts typical compromise how long does anybody do anybody know how fast a typical compromise before an x-fil can start about a hundred milliseconds think about that if your sim responds in 20 minutes how much data can be transferred before you can stop it okay so these are things to think about and yes gravity is the inevitability of your compromise defense and death was actually a biological strategy work really well when we were mammals trying to get through the uh the ice age we just kind of hunkered down we knew that there was a bunch of us that were going to die okay that's where we are right now with defense and death we need to change
those strategies we need to start learning from biological systems to defend ourselves from this stuff because currently we're not winning i don't like to lose did i mention that i don't like to lose i don't like to lose from a defense standpoint either okay that's it again this is a rant to kind of provide a history that we're still we haven't moved a lot in the last 30 some years we haven't made a lot of improvements we've had we've made little tiny improvements but really haven't made the big improvements any questions oh yes and by the way this was all old enough that it doesn't impact any of my other work that i've done recently in the last 12 years
any questions comments please
just like you a little bit crazy okay i see you at every conference too okay you get up in the morning you go hmm i think i may have an idea i just had an idea on a new way to stop ddos attacks that i didn't i just went and did a article review and i didn't see any way of using this technology to do that i thought that was pretty cool now i'm going to investigate how i can actually make it a little bit of a difference at this point but this is fun technology and let's be honest we all get paid pretty well with this technology so you know the the payment and the
possibility that we may be able to find some of these solutions they may be point solutions but you know we're still actually making a little bit of a progress at this technology any other questions please
no um i did know that i like challenges i like puzzles i like magic i like challenging myself this is the most challenging field you can be in there's actually been studies in the last year this is the most intellectually challenging uh career you can have period okay that's pretty amazing if you think about it that you guys are actually part of something that is that just incredibly difficult and challenging um no i started as a double e stars electrical engineer and they killed my program for electrical engineering i had to go to computer science and i went okay this is kind of fun i get to play with the bits once they've come out of the electricity
yeah so um no i didn't know and a lot of these things have been conversations with friends hey have you considered looking at this um presentations from gmark presentations from uh jack you know show up and watch these presentations uh show up for conferences you're gonna find a lot of things something that may just percolate with you and go oh yeah i want to solve that problem that's cool or hmm i could bring that back and do something interesting with it so no it's it's not been a defined path that you know it's not like being an accountant where you know your defined path this is you guys get to make your own path seriously
does that answer your question okay just be passionate about it anybody else i know there's people in the back with hoodies on dude you're so bad i've seen pictures of you with the hoodies um any other questions sir
wait a second do you have any ideas about how to reconcile that issue given the frequent focus on meeting this quarter's numbers funny you asked i was just talking to some people actually a bunch of us were chatting our challenge right now is we need to fix this stuff long term not short term on a quarterly basis the other challenge like i presented um on friday is certain management is now my age or jack sage and they're expecting to retire soon they don't want to rock the boat they want to get their bonuses they want to walk away unfortunately we're seeing some organizations failing did you hear about the law firm up in um how many minutes
before did you hear about the law firm up in new york it got hacked they're out of business nobody wants to even hire the lawyers that work for them because they felt like you know they lost all their customers information all their clients information they can't trust any of these individuals we're seeing that with target we're seeing that with a lot of other people i think we need to get over the embarrassment side of it the the stages of grief and we need to start taking action on it currently what i i do with some management is i try to educate them that it's better to get ahead of the problem instead of getting attacked by the problem and also
understand that every technology you have you put in you have to put maintenance on it you have to put somebody looking at it ntp servers has anybody updated your ntp that's usually been sitting out there for 15 years no way patched it you know your dns servers you know your database servers all that stuff needs main insult you know people have to check it on a pretty regular basis now because we're seeing attackers go after this
be more stuff a biological biology and response now when i think about this now that you said we need to fix stuff this is exactly not how constant a biological system works right correct
that's where we are right now right so why actually should we try to fix all this stuff if i look about the last 20 30 years or so yes
so we did over the last couple of years amazing things over the last 30 years and the things that are actually not working so much and come on the girls a law firm broke who actually cares in the big scheme of things so i wonder if this idea is that fixing it and also trying to be more like a biological system is not really comparable to do um first we're going to have to down and fix some of these stuff but we start to need to start implementing biological protections right now we see very few products of candy products we're actually out there reviewing the biological defenses offense and methods right now we've seen recommendations from mitre
carnegie mellon people like that we need to move into this particular domain we need to know how to respond instead of stand here and take an attack and get people down so unfortunately we're forced with doing both but we also have to have products that are ready to do this we can't just have a product that makes a change every once in a while to look for regex that's only on the wire or on a computer or a white list somebody can get past i mean we have a lot of this stuff happening you have to start using behavior-based systems instead of regex we need to start you know looking at how he attacks the next step the attacker is going to
take when we have when we're putting a protection in not just trying to fix this problem but deal with the next one and the next one does that make sense you need to start pulling we need to start playing chess with these attacks i just got cuddled if anybody has a question i'll be outside thank you for your time
you