A Notional Framework for applying Antifragile thinking to the RMF

Show transcript [en]
The B-Sides DC 2016 videos are brought to you by clearjobs.net and cybersecjobs.com, tools for your next career move, and Antietam Technologies, focusing on advanced cyber detection, analysis, and mitigation. This whole talk came out of 30 plus years frustration of watching the same problems repeat themselves over time. Lots of conversations with lots of friends, hundreds of hours worth of research in the last five years just to understand this particular problem. It's basically a notional framework for applying anti-fragile, and we'll talk about that term, really thinking about the risk management framework and what's working and what's not working based on today's problems that we see. So let's start with a story once upon a time. Probably the first time you've ever seen that in a
speech. It's interesting, the swan itself has always been a sign of purity. In Europe, they have all kind of songs and poems and music associated with them for purity and for many other things. So the whole idea of of a swan, you have the algoduckling, you have all this other stuff, you have all these frameworks of what this whole community, this whole society believed that there was only a white swan, that there was no other swan. Except one day, somebody went to India and found a black swan. Totally destroyed their whole framework. People had to rewrite poetry. There was a social outcry. They had to create separate genus species initially, just to define and classify this, this had social impact on
everything in the society in Europe at one point. Okay, this was years ago, but this is basically the framework that I wanted to start with. So, has anybody seen this framework, the NIST framework? This is the updated framework where we categorize We select, we implement, we assess, we authorize and we monitor. So how many people think we're successful? Okay, yes. Otherwise, we wouldn't have that.
Or that. Or that. Or that. I know. Repeat. So I went back to Google and I said, so how many attacks are actually published in the last month?
We had basically three strategies for publishing this information. One was the vulnerability. One was the research. And the other was companies claiming their product solved every problem. So it was very interesting to get that review because for years it was Primarily about the attack.
So has anybody heard of the book Black Swan? Anybody? Okay, a couple of people. Great book to read if you're into management, if you're into dealing with sudden changes in your environment that disrupts the way we think, the way we work, the way your staff interfaces with you. Three main issues that I got out of this book. besides really good section on math and statistics.
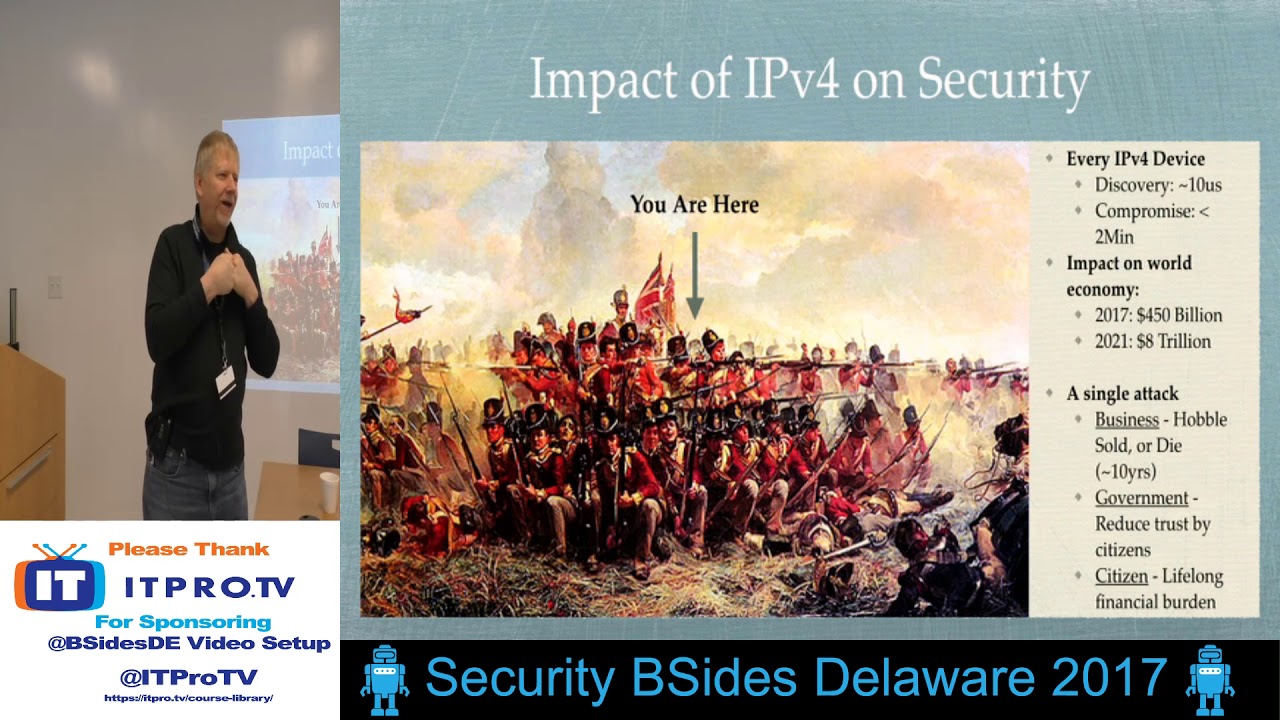
Pretty much that, especially in our domain, we live in an asymmetric world. And that is that the attacker knows all and defender knows little. The attacker knows how they've attacked, what IP addresses they used, what strategies they used, the history of every previous attack, what succeeded and what failed. the defenders always playing catch up. And they're always playing catch up behind this bucket brigade, what we call data into our SIM and our analytics bucket brigade. So does anybody know how long it takes, once you've discovered a system that's vulnerable, how long it takes to exploit with the right vulnerability? Anywhere from a hundred, pardon? No, that's actually, That's actually the published version. Actually, if I have a system and it's vulnerable and I
want to attack it, it takes about 100 milliseconds to two seconds. Computer time is a lot faster than human time. Unfortunately, to detect that 100 milliseconds, it takes 100 and whatever seconds or days to actually find it. And it's kind of frustrating for me. and I think it's frustrating for a lot of people in the audience. The other thing is there's no empirical data. How many people do you know that your organizations have published empirical data? I see no hands. Nobody wants to do that. Everybody's fearful of doing that from a risk standpoint, from a reputation standpoint. The other thing is it's a butterfly effect. One minor change or one minor decision or one minor influence can have long-term ramifications across
a whole bunch of things. We're going to talk about that as we move on.
So I started researching, has anybody seen the world adoption of technology curve? So I started thinking about this and I said, wow, we really have three categories of adoption. We have known and undetected vulnerabilities. We have known and undetectable vulnerabilities, so we know about it, but we can't detect it. And then we have known and detectable. So I started thinking about this and breaking it down a little further, and I went, hmm, who are the players that make this happen? Who are the players that create these standards that we implement and become world adoption? Well, you know, IEEE, IETF, WC3. We also have a lot of organizations that will, you know, closed ITU, IEEE, you have to pay to play for that. And also a lot of proprietary
standards. So these proprietary standards start as an idea. They create a standard. They write code. Eventually it gets implemented and goes into the world. And then we have adoption everywhere. We also have other influence. We have influence from military, government, intelligence and advocate groups. Which I've been to meetings for the last 35 years and there's been players from all of these in every meeting. So during the early period people start asking, well what are the features? What should I be providing? If they get new feedback from the security community it's not added. If they do, they may or may not add that piece if they have time based on their budget. Eventually we get into the academia, the security researchers. They're usually either
paid or for a paper. They start performing an activity to test it, to code it, to validate it and push it into the standard.
And at that point, the code may be available on GitHub. Today, it used to just be available on FTPs, things like that. So during the early phase, IT ignores this completely. During the early phase, cyber defense ignores this completely. So usually sometime when some executive hears, hey, wow, I heard about this really new thing called a Internet of things, let's talk a few years ago. I really want to get into that, we need to do something. And usually they, some IT, some engineering, some manager gets together and say really, we need it, but IT management says look, we've got to control this, we have to have uptime, no. So then we get into the next phase where It starts getting shipped, it starts
getting adopted, it becomes part of our networks. It becomes part of our cameras that cause DDoS. It becomes part of our phones, it becomes part of everything else. Usually IT is told, no, don't deal with it, it's not part of our operational tempo, we have to ignore it, it's not an issue. Security also ignores it by default. At this point, then we start seeing conferences talk about these things. We see academic conferences and eventually we start seeing security conferences, professional hacking conferences and trainers starting getting involved in this.
Suddenly, we get an oh no. Let me give you a good example. Has anybody run Wireshark on their network recently? Did you find IPv6?
been there since 2006. Did your auditors run Wireshark? Yeah, there's the question. How about your assessment people are pen testers? So you have a protocol on your system you have no management around. Interesting. So eventually what you have is security product vendors start getting excited. Oh, we can add this some sooner, some later. Then we have the stunt hack. That could be taking over a car, compromising a bunch of phones. This could be lots of different things. Everybody's seen it. You know, I've seen my favorite one was taking over the car. That was my old time favorite. Very fun. You know, catching a phone on fire, things like that. It's pretty entertaining. So essentially, then the
security product companies start getting involved at this point. Well, it's interesting because at that point, what do you think we're all saying? Yeah, right? Is this right on target, what you see from our domain at this point? So that's when audit and compliance and governance gets involved. Too late to actually make a decision. Too late to actually influence the risk decision. So this for me, This was very insightful and this was interviewing lots and lots of people and they pretty much said this is what they were saying. So I started applying game theory and saying, wow, who are the players in each phase? And as you can see, you can see the design, implement, deploy, operate, and end of
life. The darker lines are those that influence, the lighter lines are those that don't influence. So I started saying, wow, Depending on the influencers, what's the outcome? Well, so far this is where my research sits. Vulnerability times if it's designed into the product or the standards, 3 to 15 years. 1 to 5 for implementation, 1 to 2 because we're starting to exercise those capabilities, 1 to 3. So this is a real problem. If you notice, there's particular groups that are involved in each phase and each component. As an example, say a protocol came out from IETF, say, last year. And somebody developed it and implemented it in all your Unix kernels already. And it's enabled already. And
it's part of your source libraries, language constructs, and linkers. It's already there. How are you going to defend against it? If the vendors haven't seen it, if you haven't seen it, you don't have any policies, you don't have any standards to test it, and your auditors aren't testing for it. It's kind of frustrating. This whole fog is kind of nuts. So one good example of this, and I could go through this whole thing. One good example of this is Keith Cook just put out his paper from Google. He looked at five years of kernel bugs. That's how many there were just on Linux. And as you can see, the left is, yeah, here, I'll zoom in, okay. The left are critical, then we have orange, which
are high, medium, and then low vulnerabilities. That's a lot of vulnerabilities, isn't it? The other thing he did was I found interesting was he classified each vulnerability and which version of the kernel was impacted. So if you're a IoT vendor, if you look at that centerline, those are the version of the kernels that are typically shipping, mostly because they're smaller and they fit within a 32-bit, maybe a 64-bit processor memory construct. Just want to mention that. Maybe they're in cameras, printers, scanners, things like that. Just want to mention that. So here's a big question. So how much time, and this is open source, we have visibility into this stuff. How long do you think it took
to patch these vulnerabilities, to identify and patch these vulnerabilities? Years. Highs took 3.3, criticals took 3.3 years. And then we had to go through our typical push into patching all that. equipment if we could patch it. Some of this stuff in the Internet of Things hasn't even been patched and will not patch. If you're a pen tester you should be going yep I'm writing that one down this is going to be great. If you're a defender you're pretty much going crap and if you're a policy or assessor you're now trying to figure out how do you test this. Yeah pretty frustrating isn't it? Well here's a good question.
How long does it take your closed source vendor to patch this? You had eyes on the open source. How long did it take them to do it? That's pretty frightening. You're basically blinded. How about your security product vendor? There was a study for the DoD and federal government that security products have more vulnerabilities in them than most of the systems on their networks. Pretty frightening. Exactly.
Absolutely, yes. I played the assessor and found major product problems and was told by the vendor we'll get around to it, sometimes two or three years later. So they put clients' networks at risk. How do you insert that into your risk model?
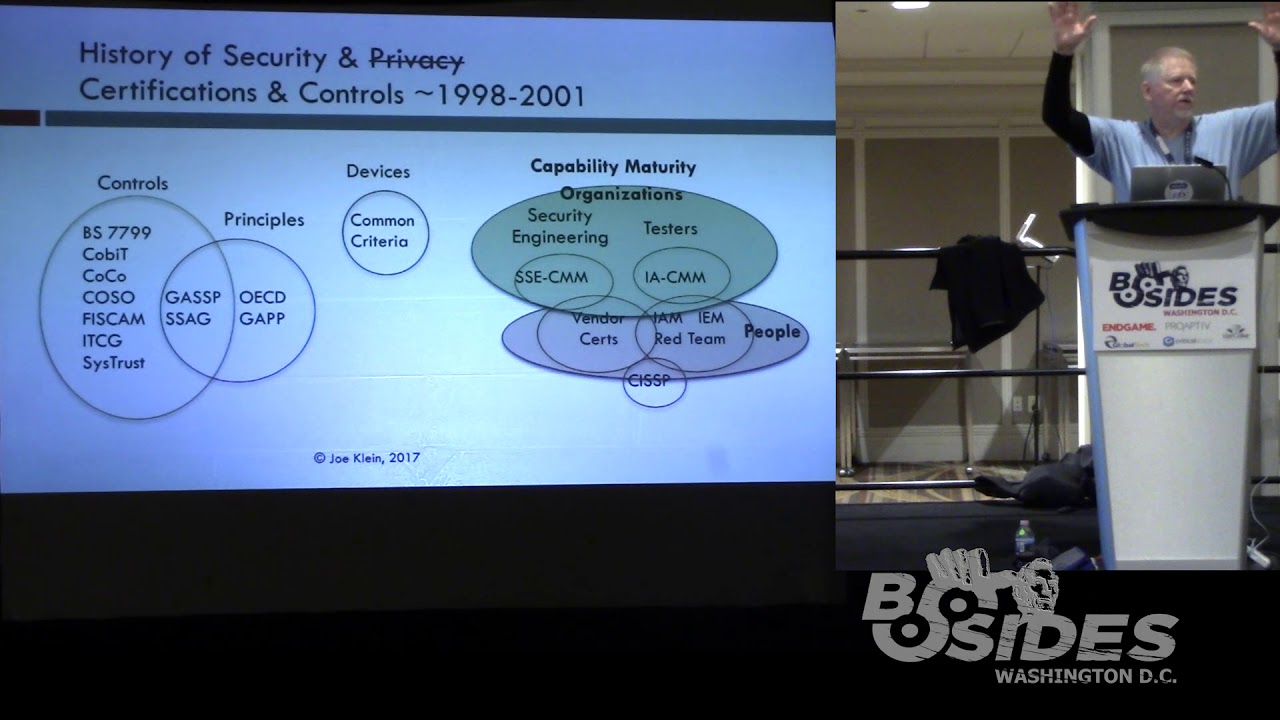
So with all this change, Carnegie Mellon and now MITRE DHS are now promoting this resilience, cyber resilience, it's going to solve our problems because our current risk models don't work. So let's engineer this in. Now I think this is a good idea because what we lost around 98, 99 in this field is we used to have people that learned how to do security engineering. Not only did we stop doing it because we had blinky light boxes that solved all these problems, but, and conflicted with selling of lots of these products, but we also had other problems that came out of it. And that is nobody wanted to do it. Nobody wanted to fund securing these systems. So from a
butterfly effect, what we're seeing today is a butterfly effect of not having real security engineering in our products. That's been a long time, that's 16, 17, 18 years. So this process is amazing. There's some problems with it though. The process itself is meant for creating a secure environment at a specific time with no knowledge of vulnerabilities that exist in the infrastructure or could exist in the infrastructure. Great idea, but it's still a moment in time. And they even have steps on how to get there. Please note that cyber insurance is now included. So you can see this is something that some of the insurance companies really see as a good thing. So has anybody seen this book, Anti-Fragile? Another book worth reading.
Get a laser. I have a
laser. It doesn't. Sorry. Three Stooges, you know. There we go. So this book is really interesting because it not only has a high level discussion for those that don't have the math and statistics, but it has a brilliant section on the math and statistics on how to model risk.
From which domain though? The financial domain, the domain that they make money off of. So they basically have spent a lot of money on trying to look at risk. Cyber security, we really haven't spent a lot of horsepower on that modeling at all levels, sadly. In this book they discuss that we live in a fragile world most of the time. And that's pretty much where we are today. We basically have this sort of Damocles, hanging over our head waiting for the other shoe to drop. Waiting for that, you know, that one vulnerability, that chip, that bad engineering, that code library that hasn't been updated, whatever it is. This is, that's really frustrating. We then have the resilient. It's the phoenix. We
can burn it down and it'll come back. How many people like burning down their network a lot? How many people, how many organizations can afford watching your network and your data burn down and try to recover from it? Okay? Especially after I've implemented it, it's totally secure. So a third model came out, and this is the anti-fragile. This is the Hydra. Cut off its head, sorry it's growing back, it still has others. I think this is the model that we need to start thinking about. Again, recommend reading the book, my contact information. I really want to talk to people about this idea and how to promote this idea throughout the industry. I think it really makes sense. A couple
interesting models here. The fragile is like a wine glass. You drop it at a certain height, it's going to break. Anti-fragile is more like your muscle. The more you use it, the stronger it gets. of makes sense doesn't it? We really can't afford to drop lots of wine glasses because well that would be you know alcohol abuse. So I turned around and I said so what would be the impact? This is just a notional I don't have any statistics on this. So I created an impact based on notional idea of where fragile anti-fragile would be. As you can see from a fragile environment this is I don't know Home Depot and Target and many other things. The costs here, the negative costs are actually the
financial staffing and the other costs. In some cases, companies going out of business. Did anybody see the report from the New York Times today that 60% of small businesses go out of business within six months if they're compromised? It's a big economic impact. Here's that resilience bump. Again, we take the hit. We end up winning as we go up. Now, for those that are in the sales or want precise terms, I've actually created this here for two reasons. I'm really tired of the sales and marketing community using the wrong terms and confusing. I guess that's good, but confusing people about what these terms are. We have things like
robust, which is right in the middle and with any change in technology. By the way, these slides will be available to you, or just email me and I'll send them to you. So these, on the left-hand side, again, stress. There's stressors on whatever the technology is. It will break. On this side, it becomes stronger. So let's take a look at what the real impact is. So as I'm going through this process, I'm really enjoying thinking through this again by myself. So I said, well, what quote would be best to define our industry? Can I use an English accent without offending anybody? When the situation, sorry, I got to stick something to my chin, was manageable, it was neglected, and now it is thoroughly out of hand. Yes, I actually
went and watched this. we apply too late the remedies which then might have affected a cure. Does anybody agree that this is where we are today in our industry? Anybody see this as an opportunity? Yeah. So the last few years And some of you know I like reading IETF standards. Yes, I even read laws. It's pretty boring. I'm not sure how my wife tolerates it. But I read IETF and IEEE and all these other standards. So what I decided was, how do I find and educate people about some of the black swans? Is that interesting for you guys? Okay. Here are the black swans that I see that are gonna impact us in the next two years. These black swans. already exist in our technology
or are being deployed in our technology as we speak or have been quietly. These technologies are really awesome from an operational standpoint but are going to drive us nuts from a security standpoint. For the WC3, has anybody heard of WebRTC? Okay. It's been our browsers for almost three years now. So how many WebRTC protection devices do we have support WebRTC? Anybody know of any?
Basically it's real-time communications. What it allows us to do is video, data and audio point to point or to large groups. It has the advantage of
using your browser to make a voice connection to you. Oh, by the way, either purposefully or non-purposefully. Kind of a bit of a problem. It's great for exfil if you're a pen tester. So write that down if you're a pen tester. This is good. The other thing is HTML5. WC3 was kind enough to include the new HTML5 components. And what does HTML5 do? It allows you to enumerate whatever device it's on and actually look at it. To look at your Wi-Fi and tell who's around you. Is that kind of terrifying from a security operation standpoint? From any other standpoint? This is kind of problematic. Everything on this, the second, we're going to go into more detail. I'm going to discuss these very quickly. Has anybody heard of the dot
onion? So what are you doing about it? You should be blacklisting it. You should have blacklisted it the day they announced it. How about the new TLDs? You know there's going to be a Google TLD? So instead of going www.google.com, it's going to be www.google. Okay? Think about all of your operational systems that you're going to have to change because of this announcement, public announcement, by the way, last week. Have your security vendors updated it? Are you ready to deal with it from a software standpoint? Are you ready to deal with it from an operational? And by the way, if you have a SOC, how is the SOC going to deal with this? They're expecting a three or four or five letter code, not the word Google. Okay?
So this is kind of interesting. We also have multipath TCP. Do you know what that is? I have two physical wires and I have the ability to send packets randomly based on the load on that particular segment as fast as possible. How many people think that your IDS is going to be able to reconstruct if you're only watching one segment and not the other? Okay, how do you find that in your infrastructure? Okay. Do about the new Tik Tok protocol for time. It allows you to better synchronize things. It's really cool. Except it's already in our systems. And you may want to look for that. WebRTC as we discussed. There's a whole new standard from IETF which is the Woot or Internet of Things PNG
stuff. Five standards you may want to read that are terrifying from a security. How about DNS SD? That's DNS on the local segment.
Oh yes, it's great for spoofing local segments and having the traffic go elsewhere. Isn't that cool? Operational package extension header, IPv6 extension headers. You can have more than one extension header. Does your IDS and firewall actually have context over that? Does it know what to stop? Also DNSSEC and DANE, great tools.
Dane is the ability for the last mile machine to validate all the upstream systems without referring to a CA. The problem with it is a lot of code is not done right and it has vulnerabilities unto itself. And then SPF, DMARC, and DKIM, going to be great for defense once it's fully implemented. It's not fully implemented and attackers are actually falsifying this information today.
Okay, so last one is connected vehicles. If you're driving a connected vehicle, does anybody have a connected vehicle or a smart car or anything? The current standards are vehicle to vehicle and vehicle to infrastructure. Do you really want the light post to actually talk to your car as you're driving past? Could you see the ability to say, I don't know, influence your car as it's driving past infrastructure? Just want to mention that. So let's go over a couple of the black swans we're already seeing. Has anybody seen the 3D printed keys? Okay, these are so cool because if you lose a key you can just go and have it printed. Awesome! Does anybody know about this standard from NIST? Is anybody under this standard? It's
assuming that it doesn't take much time and the key itself leaves a forensics mark in the key way so you can at least say, yes, I know I've been broken into but yes, I can confirm somebody picked the lock. These things don't leave forensics evidence. Okay? So, how do you mitigate it? Upgrade your lock. Use non-printable systems. Oh, by the way, here's the links. It's really cool because this first one, you take a picture with your phone of the keyway and you get it printed. It's really cool. And then you go look at Matt Blaze's link right there. Print seven keys and you have a high probability of getting into any door.
all took the blue pill. So let's take a look at another one. Has anybody heard of source routing? Source routing is the ability for us network engineers to troubleshoot and manage the infrastructure and the flow of their components. Hey, I have to take down this router today. Let's reroute it this way. It allows the source to actually do routing. Pretty cool.
It's also used and has been used for almost 30 years for reconnaissance and a way of bypassing the security controls. Because say I'm using TCP connection or your organization has multiple internet connections and I can bypass the security controls by stepping around the security controls and forcing it to route other ways. Kind of a problem. Also messes up the detection systems. To mitigate,
Today, anybody running Linux? It's been included with Linux for the last year and a half, so if somebody turns your Linux box into a router, have a nice day. And by the way, if you're the auditor, assessor, you should be checking for that. Here's some references. This is just with IPv4. Look how long it took from DARPA RFC 791,
to the time that we started seeing filtering. Are you terrified yet? Oh, by the way, there are certain vendors that made claims and still haven't fixed this in their routers and switches and things like that. So be aware that those still exist and you should be testing for that. But that's a new risk that's on your network to bypass your security controls. Oh, and just considering I know something about IPv6, Here is finding and then removing. It took a few years for different companies to remove it from their infrastructure. So if you're running old code on your routers and switches, you may need to upgrade because it allows you to do denial of service attacks with
a few packets. Pretty entertaining. The other thing is, do you notice the spring routing protocol at the very bottom? Sorry, it's little characters. Some of us need glasses. That's why I'm up here, so I have a screen in front of me. This is a rethink of source routing. Because we know that the routing people know everything about routing, and they know everything about security, and they'll tell you. Because OSPF has never been piped down to every desktop in an organization, has it? or BGP sitting on organizational systems, which, by the way, makes pen testing really fun. Segmented routing is a new strategy to put some crypto into the source routing, to simplify the management of it. Well, here's the question. How are you
going to detect that on your current systems? Does your IDS, IPS, or anything detect this right now? High probability no because I looked at the code on the open source products and they don't look at this yet. Okay. Again, these are all black swans that are sitting out there. They are land mines. An attacker can combine these and cause all kind of havoc on our networks. Including doing DDoSs again with a few packets. And yes, IPv6 is on and it's on your network and 14% of the world and 32% of the US is already using it. Woohoo, do you have a phone? It's already running IPv6. Matter of fact, if you turn your phone off and you turn your
phone back on again, guess where you end up from a geolocation standpoint according to the geolocation providers? You end up in Kansas, in a farmhouse in Kansas. It takes them a while to figure out who you are to reorganize that. So if you're depending on geolocation to find attacks, is that kind of a problem for you? Yeah. Let's see, it's enabled already since 2005 on your infrastructure. And yes, by the way, these are the symbols now being published in the IPv6 community, which is you have the old Arcane protocol and then you have the new IPv6. So begin deployment because that's the only way to mitigate the tunnels and all the mess and think about deployment. There are great government documents already prepared. There's great
documents out there from NIST, from DoD, from other people that already have this defined. Save yourself the hassle. Oh, by the way, was anybody impacted by the DDoS on Friday? Anybody? Yeah, I wasn't at a desktop because I was running IPv6 and I was doing lookups A and Quad A across IPv6. And those companies that made a risk decision to only support IPv4 on their front end systems, I couldn't get to. But anybody that had IPv6 provided me a redundant route to get to their infrastructure. Kind of cool, huh? Here's documents. Now. Here's the growth rate and who's there and the size of projected. So we're expected to be globally around 28% in a year. Except stats lie because we look
at this and we summarize the people and the connections and things like that. So North America, here's North America, Europe, and everything else. Except, wow, China's not even on the top list. They're pretty small, aren't they?
Oh look at the carriers that are supporting 100%. How
about Russia? How about Romania?
I have more of these if you would like to find out. So when you hear these percentages that this country only has X amount of percent, as an example, if you're running a Verizon phone today, Maybe about 70%, 75% of people are using IPv6 by default across the Verizon infrastructure.
So how do you defend against this if you don't know it exists? And you don't have it in your sock, you don't have capabilities for it.
Sorry, you're all looking very glum now. I told you I was gonna tell you about the black swans coming. Have you heard about DNS-Prive? It's already implemented in Linux in some places. Does anybody use passive DNS detection in your infrastructure? DNS-Prive encrypts that. If your infrastructure uses this, your resolver just passes on the encrypted request to the root and then all the way down. Are you detecting this? Can you see this today? You need to start managing this. This is great for privacy by the way, if you're at home, if whatever, but if you're in an organization, this is going to be a real hassle. So you see that's kind of frightening. Carry a great gnat. Okay, so
here's a good question. How many of you have had somebody apply an access control list that cut off your best customer? Anybody?
Carrier grade NAT is for all the internet service providers that said we're running out of IPv6. What are we going to do? Let's NAT the NAT. So now they have multiple levels of NAT. Well, from a resource constraint standpoint that means you and you and you and a thousand of your best friends are all sharing the same IP address. You only get so many ports. So if you're doing port session identification, within your security tools to see if it's coming from, I don't know, a DNS query from a 53 to a 53 because it's Linux that no longer exists in this environment. Oh yeah, one other problem with this, it changes anywhere from every minute to every 15
minutes based on how many people are on this connection. So how many defenders are looking forward to blocking every IP address for everybody and then starting to get help desk calls to say, look, I was about to press the I'm going to pay you button and all of a sudden I couldn't get to it for 15 minutes. Or how many calls to your help desk are going to say, my VPN was perfect and then it just dropped off from a hotel. So these are security operational issues that are going to impact us and have impacted us. I did a test against this. I was in a specific hotel and I was messing with a friend. And I was scanning somebody,
but just a little burst of scans. And over about an hour, I blocked 18 addresses and then called the company up that he worked for and said, hey, can any of your people call in? No, the VPN's down. We're not sure what's happening. So you got to have context on where these things exist. And the carriers have been very poor about documenting. We've documented this, but this is a real operational problem. In other words, you can give yourself your own denial of service to your customers.
So, and they lived happily ever after or not.
So I have a request. Again, I'm looking for feedback on this talk.
Again, it wasn't talking about standard RMF because RMF doesn't do predictions based on the standards being injected into our systems and our libraries. It doesn't talk about many of the other things. I'm looking for somebody to help to do some additional research on this. Also, other black swans that you're seeing within your technology. to start protecting, to start documenting, to start identifying this information. Any questions? Please. I knew that you would be the first janitor. Awesome. That's the famous info janitor, by the way.
So what he said for the people, the viewers at home, is, does IoT have the same problem? Is it the black swan that we're dealing with? Yes. It's the black swan for a couple of reasons. Number one, it contains a lot of protocols that haven't been patched because they're older generation systems and that cannot be patched at all, just like our routers and printers and things like that. Number two, some of them are using standards that have known vulnerabilities in them. And also known vulnerabilities that are published in the IETF standards and IEEE standards that haven't actually been visualized yet or haven't actually been moved to a CVE yet. That's the second thing. The third thing is the Internet of Things really doesn't have a set of security
controls. NIST did a great job of trying to motivate these Internet of Things companies to do this. If they actually perform that activity, that's great, but I'm not seeing it. By the way, some threatening little experiments I've done with Internet of Things is I took, does anybody know what Zio is? It basically checks your sleep so you can get REM, the proper REM sleep and light sleep and deep sleep and things like that. And you've heard of the Nest alarm system? Yeah, for one weekend I was messing around and I said, hmm, I wonder, because everybody's talking about internet a thing to IT stuff. And I said, what would be the impact if I connected those two together? Say
every time I hit REM sleep, I made it beep
crap it worked. Okay, I was in a pretty bad mood. So then I did some sleep studies and pretty much after seven days you're dead with lack of sleep or pretty close to it. Psychotic within two days or one day depending on your body makeup. That would be really bad wouldn't.
Yes, wait, wait I had more than three hours last night. Come on, yes, some of us sleep every once in a while. It's really cool. But these are the second class. First, we have the class of products that are going to go after our standard products. We have the using it as a pivot point to attack our standard data systems. And the third class that I've identified is where systems correlate together. to attack each other. I mean come on, our smart car connects to our internet connected car. This is a strategy for car vendors. Is they want it to connect to your internet and download software and videos so your kids can see them on the next time around. And also transmit all the information including
geolocation and altitude and engine and oxygen and everything else back to them. By the way, planes do that too. And other vehicles and other things do that. Could that be bad? Yeah. Did I answer your question? By the way, he put a, Jenner did a really good presentation, DerbyCon 1, which will also terrify you. Any other questions? Anybody see this as a problem? No, no, you have to put your hands up so I can say everybody in the audience put their hands up. Okay, you in the back. Okay, everybody in the audience put their hands up. That's awesome. Does anybody see this as something that we should start addressing in our risk models? Okay, does anybody have ideas?
I'm gonna open a microphone if you have ideas. No? Pardon?
to make silos of excellence. Wait a second, I thought that was General Lord's quote.
Put it on the cloud. Wow, put it on the cloud.
Thank you, Gal.
So we're supposed to admit defeat and publish everything. I think the OPM already took care of that. Thank you. And then Target and a few others. Question in the back. Well, it's interesting because UL, I actually pitched that to UL a few years ago and they said, yeah, that would be great. We have no funding. Nobody's interested in it, whatever. Fortunately, Mudge, who was in DARPA for the Fast Track projects, He's been requested by the president to start evaluating the code libraries. He has a paper coming out either this week or next week. I haven't seen it. To specifically talk about some of the code library issues and the software that we have high dependencies on. So look for that.
So UL has seen another potential income stream, so they are defining, sorry, I added the first. They've defined that they're going to start working with the community. That's a big difference versus DerbyCon 1, where one of the individuals was asked not to talk about half the vulnerabilities that he had found based on the vendor, asking him not to mention their name. So this is a big change in six years, I guess. Any other comments? By the way I've been in this industry for 35 years and it's crazy.
Let me reframe that. Qualified testers, although your language was far more flowery than what I'm going to use, Competent individuals assessing security product vendors so that at least we have secure non-compromised systems. By the way, one of the strategies used by pen testers is go after your compromisable infrastructure for security, therefore they can hang out for a long period of time.
Yes, but I have Red Bull over here. If anybody wants any, Otherwise, I'm going to be drinking more of it tonight. Any other questions? I've got cards.
So let me consolidate down to please read the future. Read the tea leaves. I'm going back and forth with that. We haven't even talked about AI interfaces. We haven't talked about defeating machine language or machine learning systems and what the impact on security of those are going to be. Yeah, I've been thinking about that for a long time. It means there's going to be 100% employment in this community. It means those of us that have platinum hair, because this used to be blonde, will probably still be around for very long. For those of us that actually still have hair, I see you back there. Yeah, exactly. But we're going to see more of this, but it's really going to require
people that have actually been through a couple cycles of this domain to help influence and fix this problem. It's real common to talk to, and you guys probably see the same thing, the new people in the community that haven't been through a cycle of, oh, okay, now we're getting DDoSed again. Now we're getting web attacks. Now we're getting spam or phished or whatever it's called. Now they're going after the desktops. Now they're going after the phones. Well, those are all network-based. But I think that the tax base has increased. Somehow we're going to have to become aware of these evolving technologies and when they come into a system. As an example, would you see the chance of a public vendor actually seeing what protocols they
support? Wouldn't that be handy so you can actually checklist them and say, yeah, we have security controls for this, we do this, and crap we don't have for this?
So I'll reframe that if you give me a chance. When it really comes down to the issue, the risk decision is made by the executive.
I've never heard an executive say no, it's not too risky. Could be why Target had to close a bunch of their stores. It could be why, yeah, that was after the fact. We have a lot of after the fact scenarios. I remember one specific company I said you need to please put up firewalls and there was no requiring to publish or to talk to anybody about it and they lost many of our information about our investments and fortunately that was 20 years ago when nobody really cared and they didn't care either because the firewalls were going to cost them $2,000 a piece. and one week's worth of staffing. So, yeah, it's a financially motivated issue. Any other
questions? Has this been useful? Should I do this with an upgrade at some other conferences? Oh, one other question.
The famous G. Mark Hardy showed up. Holy shit. Sorry. Holy shnikes. For the kids at home. Yes.
GMARC asked, let's see. Do we redefine? Actually, yeah. Actually, there's two things. There's a bunch of new capabilities within IPv6 that makes it far more defensible. Unfortunately, the current large vendors aren't interested in it, sadly. There's also a DARPA project that's been funded to begin asking that question. and there's code floating out there if you want more information about it, get hold of me. It has some capabilities, but it has some real immature problems with it. So as a question, yes. It is a problem, it is a reality,