Election hacking defined and how to fight back
Show transcript [en]
so I'd like to introduce Andy Dennis with election tactic defined and how to fight back all right thanks a lot Roman everyone can hear me okay I guess yeah so yeah I'm Andy Dennis and I'm here today to talk to you about election hacking you've probably seen it mentioned in the news recently or at some point over the last two years so let me just give you a little bit of an introduction to myself before I delve into that I worked for a company called motors create it's a DC area consultancy we do everything from full stack architecture through to design I've got 16 plus years experience in the tech industry and in the UK Canada in the US
my role modus is a full-stack architect and also I saw up handle a lot of our cybersecurity stuff and increasingly I can see that that will be becoming a greater part of my role in my career I have degrees in software engineering creative computing and I just recently completed a master's degree in information security which is kind of what was the genesis for this talking and I'll cover that and a little bit more detail I want to assure you this isn't a political talk is to talk about political infrastructure and the threats they face so there wasn't going to be any debates here or telling you who you should or shouldn't vote for I'm gonna
steer clear of that so the origins of this talk so going back to 2016 you should probably guess my accent I'm from the UK originally there was the brexit referendum which was pretty contentious and in the aftermath of that there was a lot of I guess you could say debate in the news and criticism of how the referendum was run and in addition to that that company such as Cambridge analytical a IQ we're using targeted ads to try and persuade people to vote one way or another in the referendum so that was the initial genesis of this then I started my master's degree and as many of you know probably done one you have to write thesis paper so I figured it
was a pretty interesting topic to to cover so following that I went to the corn went to the votin village and saw some of the stalks there and everyone pulling apart the voting machines last year in New York hope there was a really great talk by Matt Blais and the other guys that run the voting village really on how they acquired the voting machines and then also in 2017 Chris Sumner who goes by the name Sagi did a talk at Def Con on recognized propaganda online so all of these things came together and that's how I ended up with that as my master's degree thesis topic the graduate thesis took probably about 16 months to write and research so it took
place between 2017 and 2019 and I mined a variety of sources so mainstream media academia government papers and then other cyber security researchers what they found over the years and in addition to that I used some Python scripts to help analyze that day or I'd pull back so I'm just going to make this caveat at the moment things are moving very quickly if you've been watching the press you probably seen Guardian journalist Carol Cadwallader gave a talk yesterday to the Irish parliament I believe it was on fake news there's a lot of stuff going on at UK in a moment the with the election coming up so this talk can really only scratch the surface
so I'm just going to try and provide you guys with an overview of the subject so with that side let's let's get started so what is election hacking coming up with a definition stuff what counts as election hacking and what a part of a broader category of electoral related crime so say fraud or money laundering how does the press and the government use the term because it would be quite different and you'll discover if you go and look online one person's definition of hacking can be quite different to someone else's and then of course what is the origin of the term hacking itself we use it but it's still pretty nebulous so the first step was to try and figure
out coming up with a concrete term or definition sorry for the term hacking and hacker so when I wrote the thesis you know anyone reading it would would have an idea of what I meant I I looked back at the jargon file which has been around since the 80s I think and probably has his origins back in the 70s and this definition consisted of I think there was eight total ideas there and I took six of them which you can see one one three six here I think most of you probably agree with some of the concepts that are listed here and number six especially you know a malicious meddler who tries to discover sensitive
information by poking around it's a pretty negative definition and it's used a lot in the media but there is of course an ounce of truth to that so having an idea of roughly what we meant by the term hacker or hacking the next step was to analyze you know the zeitgeist around the term what do people in the media mean when they use the term hacking and then what do they mean when they combine it with the word election so I drilled into the Google API it gives you a limit of a hundred results per search I'm not sure if you can go beyond that if you spend money but based upon the small budget I had I basically
mind a thousand links using the term election hacking and then nine other very closely related terms such as referendum hacking once I gathered the data from a thousand links who removed the duplicates which gave me 587 individual articles and these were a mix of different source types coming from news and academia so some of them were like CNN articles others were from OC's of the university's computational propaganda unit research unit and then once I had these two this big set of data I then sort of did another round of analysis the first set of analysis was to take 18 pre chosen keywords and to look at that data and say how often do these appear so those keywords included
DDoS theft crash virus I chose them based upon you know the literature I'd read terms that I thought were likely to appear of course that's quite biased so the second analysis I did was to just look at the articles and say what were the the most common nouns that appeared in Italy the scripts and data set available and github if anyone wants them come give me a shout after and I'll point towards them so the date mining results were fairly extensive said I've just picked a few here for you guys just to get an overview of what I found but there was some you know interesting trends from the 18 pre-chosen keyword analysis so from the period where those
thousand links came which were produced at 587 email and phishing was a term that was commonly found I think that was probably likely due to the the dnc hack which happened back in 2016 terms related to psychological manipulation featured heavily as well which was probably likely due to the Cambridge analytic a scandal which was all across the Guardian and other news organizations looking at the the common name a common noun sorry that were returned obviously voters voting was was pretty common security orientated terms such as cyber security appeared a lot and then nouns associated with Elections such as ballots and referendum and of course finally which you probably would expect attack attacks hacker and and hackers so
so this kind of told me I was moving the right direction you know the term election hacking is likely to mean something to do with a referendum or a ballot or an election and then common terms we would generally associate with you know hacking itself cyber security and so on following this you know I I think it it would be good to look at what the professionals say with regards to the types of things that are considered cybercrime so the UK Crown Prosecution Service guidelines has to two broad categories one which is offences that can only be committed using a computer so you'd probably think of DDoS being one of those and then the second of cyber-enabled crimes so these
are traditional crimes such as fraud and money laundering which then leverage IT infrastructure to be able to you know commit the crime so that is my my foundation I came up with a set of heuristics you know to see if we take a group of Acts and apply the heuristics to it to ask is that election hacking or is it something broader you know is it fraud isn't money laundering and and the four heretics that came up with were can does the attack target and aspect of the election system is it digital a cyber in nature such as a cyber dependent crime so that refers back to the previous slide with the CPS guidelines does it involve a component
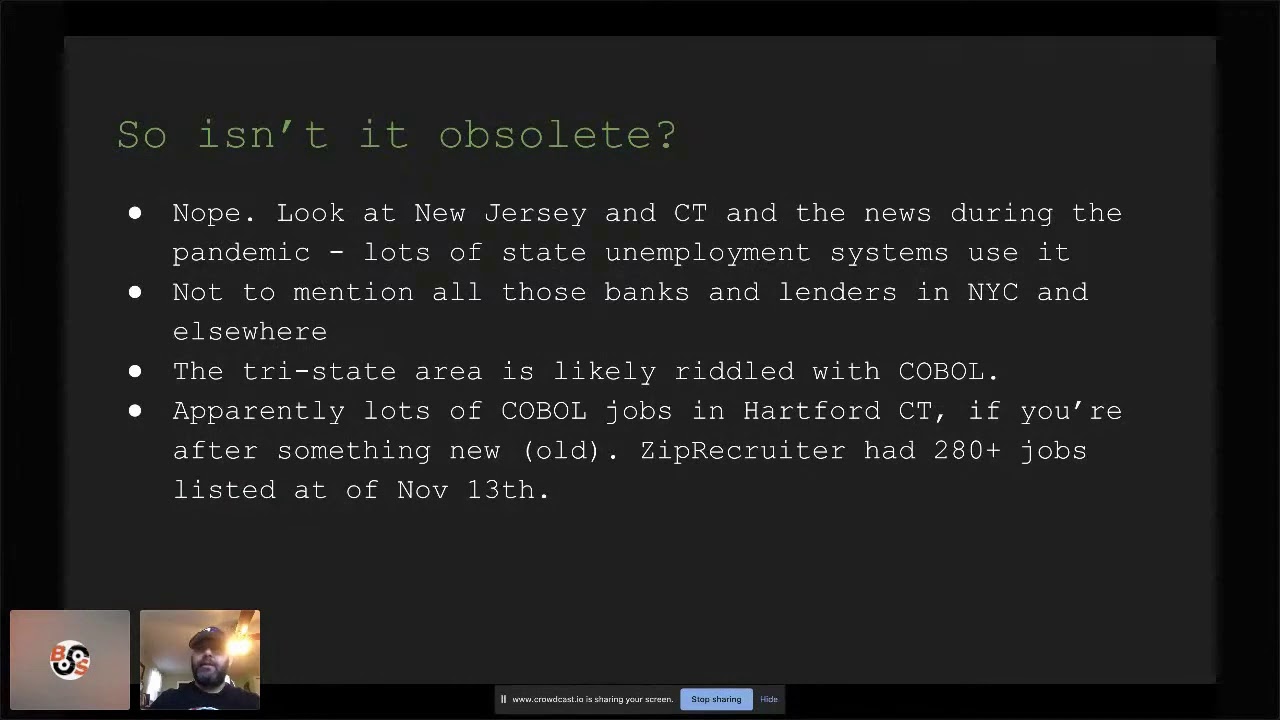
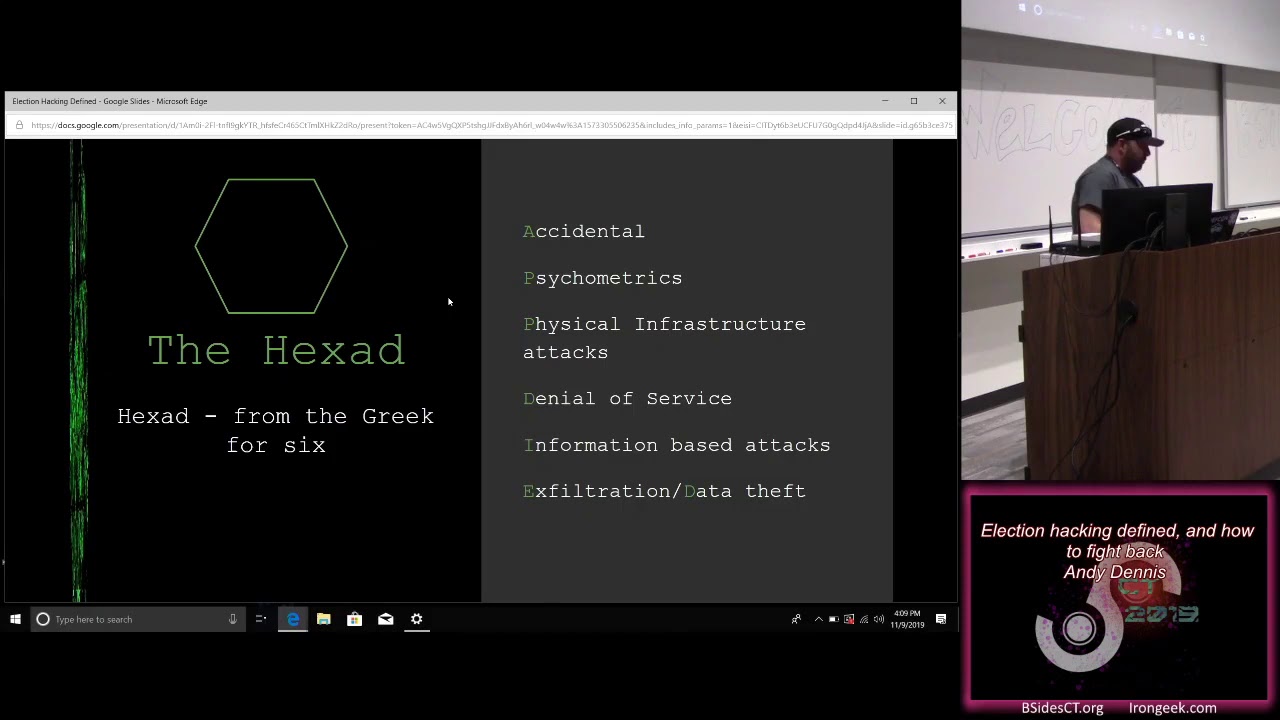
of information security or privacy being breached or broken and then finally it's not a financial crime I decided to rule that out because you know it's it's not solely a cyber dependent crime that often they're cyber-enabled and existed long before we had the Internet as well so based upon those heuristics I came up with a model which I've called the hex ad familiar with the term hex ads the Greek four six and the model has six edges one for accidental one for psychometrics one for physical infrastructure attacks one for denial of service attacks one for information based attacks and then finally exfiltration slash data theft which actually spells app died if you look at it so having come up with this model it
was like okay I need to define these attack vectors in more detail so I merged the results the data sets to come up with 15 attack examples and then I applied the heuristics to them to filter out anything that I didn't think fell within this now defined term election hacking and the heuristics led to the following the attack categories you know things like hitting vote tallying systems intellectual electoral infrastructure such as denial of service attacks against websites stealing emails of political candidates through phishing attacks flipping votes on voting machines so if anyone went to the vote hacking village it at DEFCON you will have probably seen plenty of examples what people were doing with the machines
targeting individuals via online ABS in propaganda so fake news using stolen data and then leveraging that as Cambridge and analytic over-leveraged alleged to have done through taking data from the Facebook API dumping stolen data onto the web so there was a lot of that in 2016 3 2 an eighteen period WikiLeaks is one that we think of but there's plenty of others which I'll touch on later and then spreading fake news via fake news websites so due to the overlap and broadness of some of these definitions these were refactored into their hex ad which I a previous issue and on the other slide which is really just a set of meta categories for describing describing things so this is the model
which I showed you before and really the goal is to reduce this attack surface so we want to we want to try and knock out some of these vectors or at least shrink them so I'm going to go through each of them now briefly and just sort of describe what's involved in each one so this is a quote from the peacock report on lesson learned from the EU referendum when the original voter registration website crashed I think any of you who've worked in architecture or software engineering or DevOps will understand that you know the things crash and if you don't take a board the the recommendations through testing then they're probably going to crash when you
get into production and that's what happens here and then there's you know multiple things we can group together under this accidental category so I've put system crashes in here just failures are no two coke coke flowed and then just general infrastructure failures and and you might think well why does that count as election hacking that's accidental that could happen any time and it's really the the problem is what stems from it so it often leads to a loss of faith in the process of the system which is handling you know whether it's very telling or actual the votes themselves and it conditioned franchise voters so in the case of the UK voter registration website and I'll
cover that in a lot more detail there was all sorts of rumors started after that including from MPs and in the press to really muddied the waters to understand what was going on there and as I say hey you know these types of things can be then leveraged by bad actors to spread further discord on social media or and you know other other realms and yeah there we go so the voter registration website in UK is is the example which we'll look at in a bit the next one I want to go to is psychometrics and for some reason the graphic has screwed up so Marshall McLuhan if anyone's familiar with him he was a big media guru and I picked his
book cover here oh sorry Rebecca second um because this is an example of actually but you can't read of something that went wrong where they printed the book and it should have said the medium is a message and it said the medium is the massage so no one proofed the book and I promise you this is not a targeted ad to go use the mental health hackers village massage chair so psychometrics is commonly known as targeted advertising or micro targeting it's efficacies really controversial and disputed I don't think there's probably been enough research into whether that it really works or not there's an article that came out and the correspondent earlier this week and it
was about the the new dot-com bubble is here and it's online advertising and then the whole article really went into do online ads work for companies like eBay because it was somebody just gonna go to the website anyway are they paying lots of money to click for people to click on an ad for something they were already going to buy in addition to that Ethan her shoes I think you still at Yale he wrote a book called hacking the electorate this I came across this actually because there's a guy in the UK called Dominic Cummings he's a adviser to the UK prime minister and he was involved in one of the leave campaigns during the EU referendum and he was
criticized a lot for using micro targeted ads and he turned around on his blog and I believe he said no I didn't use that I actually use more the mechanisms mentioned or not mechanisms as such but it the approach he took was derived from from what was in Ethan's book if I brought that correct so it's worth worth checking out I bought a copy this week to read through but I haven't had the chance to do it yet because I had a production failure yesterday and wiped my whole day out so so the the big one which you've probably all heard of is Cambridge analytic and big scandal Chris Wiley who was one of the employees at Cambridge analytic here
in London he's brought a book it really provides quite an interesting background into the structure of the company and the sub companies and what allegedly they were doing as I say we don't really have any metrics in the public for how successful they are a lot of people are going to say they were some people say they weren't I'm pretty sure Alexander Nick's the guy who ran the company told everyone they were super successful because obviously you wanted to make money but I think you know as it's more comes out from from that scandal we'll probably get an idea of exactly what they were up to up guard if anyone's heard of them Chris Vickery he did a lot of research
and this he actually uncovered some quite fascinating details about aggregate IQ because they left their get get lab account publicly accessible I think it was and he was able to get into it without having to do anything illegal and and see what they were up to and found some links between them and different parts of the leave campaign which were certainly in a legal gray oh and then Carroll Cadwallader and channel 4 UK they did an under port undercover report on on Cambridge analytic and channel 4 sent guys in undercover and they recorded them talking about some of the definitely illegal things that we were planning to do to help throw a hypothetical election so if you're
interested definitely go read Carroll's work because she she goes into quite a lot of detail about what she found out when she was investigating Cambridge analytic in that their targeted ads and then finally I'm just under the sea a scandal if any of you have Netflix which I'm sure many of you do there's a great documentary in there called the great hack which interviews song called Britain Kaiser she worked for Cambridge analytical and she goes into detail about what our role was and what they were up to but I'm just gonna reiterate is to say certainly I'm not not a psychologist so I can't argue you know academically whether the ads work or not but it's it's a controversial area and
it should be something everyone's concerned about because if the perception is that they work then every time we have an election or a referendum or something along those lines then people are going to immediately start saying well someone used targeted as it threw it so so it's something that needs more I think investigation and additionally probably needs a little more attention from the platforms that serve the ads to make sure that everyone knows exactly what they're being served and from whom it's coming the final part that I on the psychometric slide I want to talk about is the Russian Facebook Ads so if anyone's seen those you can go find them online they're definitely not
sophisticated is the Micra targeted ads but there's a quite interesting backstory around those Rene de resto G if you're interested she did it anyway I think it was with Sam Harris this year she talks about how the ads were basically memes and over the course of a year the group that was deploying these memes would change from using Simpsons means to to other like cartoons until eventually they would hit something that worked and got traction and then they would keep pushing those graphics on Facebook into certain groups to try and sow discord between different groups of individuals so for all I know there made me more successful than Cambridge America oh no here we go that's
certainly worth if you're interesting interested in subject check out and then finally just to go back to Chris Sumner which I mentioned earlier he's got a fantastic talk called rage against the weaponized AI propaganda machine it's on YouTube it was at DEFCON 25 I believe definitely go check it out go watch it he's done some other work as well which is more like academic in the sense that you can go download the white papers and read them if you're interested and then finally on the subject psychometrics Oxford University's a computational propaganda research project is a really fascinating website it's a comprar pax to a co uk have a look for you there they have like a junk news aggregator on
there and some other pretty cool stuff that they've collected off the web whoo there we go it's bad babe might be able to read the slides a little better thanks me so so the next area that in the next edge on my hex ad was physical infrastructure attacks so to quote Ted Koppel the internet among its many many virtues is also a weapon of mass destruction if you're not familiar with Ted Koppel he wrote book called lights out a cyberattack a nation unprepared surviving northa mass is about what would happen if there is an attack on the u.s. electricity grid it's frightening stuff so check it out if you get the chance so physical infrastructure tax what do we mean by
this so voting machines are vulnerable the DEF CON voting village is shown shown that if you check out there it takes a village to hack a voting system talk at hope there's a lot of background around the subject Matt blaze Harry hasty and Margaret McAlpin's works really fantastic in that area so there's a lot of questions around how voting machines are deployed you know what visibility is there into how they work is anyone really you know taking the time to make sure they're secure before they're deployed so it's an area certainly that's very very hot at the moment and I think if you go read mats Matt's work and so many others there's there's a lot of those machines probably
should not be deployed in any kind of production instance if you know what I mean the next thing is the electricity grid another infrastructure could be attacked so I'd mentioned lights out so really I mean you have to get to the the voting booths if you can knock out the electricity or something like that which thankfully I don't believe happened you can disenfranchise a lot of votes because you could shut down the ability for them to actually go and vote and then the vote of Italian registration websites at DEFCON they the team their roots Asylum put together some example website so base them upon some existing ones and let people loose on on and they've hit them with sequel injection
attacks and similar so the concern around this is if you can break into a vote tally and website or a website that communicates the results of an election you can change it and even if it gets fixed by that time people are going to start rumors on Facebook and another social media platforms and you're going to have a headache on your hand and of course yeah infrastructure taxes also mean data from modification and corruption and removing voters from the system if you can sneak in and you can delete voters you know you can try and sway a system one way or the other so that was the the physical infrastructure attack vector the next one is the denial of service attacks so
I'm pretty sure everyone in his heard of denial of service if you haven't I'll explain a little more detail so a DOS a denial of service attack crashes or denies legitimate access to a target so spam actually you you know you could consider a denial of service attack because if you fill someone's inbox with junk it becomes very difficult for them to actually find the legitimate email amongst the noise so what would especially interested in is the distributed denial of service attacks so the pings of deaths boost packets syn floods so this is where you can have basically a botnet or compromised IOT devices and then the person that controls them can point them towards
perhaps some you know very registration website for example and just flood it and knock out offline which once again results in you know disenfranchising people because they can't sign up it doesn't really require physical access IVA or any sophisticated technical skills with regards the infrastructure attacks because a whole bunch of you know compromised machines can be just handed it and let loose and the individual behind it could probably get away with it for quite a long time a verse is trying to you know go on site to say a vote in precinct and break into a variant machine and you know you can knock this software infrastructure offline as I mentioned voter registration sites even even hardware if
it's connected to the internet so so it's definitely a concern the next category is the information based attacks so a couple of quotes here which I thought were quite good [Applause] so what do we mean by that so so we're really interested with information based attacks which have an origin in digital and social media is this often unregulated and it's difficult to trace the individuals behind it and it's often unaccountable with a traditional news organization they have an address they have you know TV station so some countries have press oversight independent like press oversight organizations so if someone defames you can write to them and ask them to work on your bath to have the comment
retracted with fake news you don't know where it could be it could be in Macedonia could be in Russia it could be in Idaho the fake news you know can involve plagiarizing modifying other material legitimate material and reusing it fabricating stories and and you know include deceptive and misleading stories so whether you take something that's true and alter it just enough one thing that we saw back in 2017 was I think it was a Belgian news site the whole site was copied by nefarious actors and then tweaked to present some different stories and looking at it you wouldn't necessarily know it was wasn't the real real thing and once you have you know fake news
sites you can use data dumping to then feed information that you've stolen through to the public one example of date and dumping was micron leaks they hacked an email addresses in the 2017 French election and then that information was dumped out onto the web to try and you know persuade people to vote one way or another and it of course it's picked up by the media and fake media and circled around becomes a big feedback loop bots and fake social media profiles can then be used to employees messages and so don't sow discord so if you end up with a site that's posting fake stories on it then you get BOTS online that will take it and regurgitate
them and I've mentioned for the Oxford News junk news aggregator definitely go check out there's some really interesting material on there and then coming to the next category is the the ex tration and data that attacks so how are these conducted the first thing is a lot of them come from phishing attacks so I think the DC leaks happened the RNC leaks happen through phishing attacks so you get the email someone clicks on it and next thing you know they've compromised the system and someone can get in and download their email and then dump it out onto the web or use it the game you know access to the system and move laterally through it
of course another threat is insiders do we count whistleblowers - I mean that's certainly a controversial subject the previous slide mentioned Chelsea Manning and Edward Snowden and I'm sure you know a lot of people have conflicting views on whistleblowers in that context at any rate and and what role they have to play but if they dump data because they're concerned about something during an election period and it has an effect is that something you know we should be concerned about there's certainly a question I think that's contentious and exfiltration because who happened through you know breaking into systems unpatched security holes so it could be using Metasploit or similar to get into the system and then
don't up the database and spread it then as I mentioned previously that can then be combined with fake news sites or social media bots to then spread that data so you dump a whole bunch of say emails from someone's account you make up a few fake emails put it in there and then spread that and it becomes very difficult then to pull out hey what was the fake email the attackers put in with the real legit emails and and it was it goes viral trying to try to rein that back in is incredibly difficult and on top of that sometimes legitimate media outlets of course are the ones that are the recipients of that data that's been
stolen so the Snowden leaks for example he met with the Guardian journalists who believe in Hong Kong and then the story picked up from there and of course you know they started to share that information that he'd provided to them and then you know cats out the bag damn and then we've got sites such as WikiLeaks DC leaks and similar Chelsea Manning stuff I believe ended up on on way he leaks so you know how do we treat them and they treated as a press and they treated as a whistleblowing organization or as I believe recently they were dubbed a non-state aligned Intelligence Service so it's a and you know we've got the accusations against
Cambridge analytic here for example that they exfiltrate data in a gray area from Facebook and then used it for psychometric targeting so that's another potential vector once you've got the day of what you can do with it so having said all that and sorry I had to go through those fairly quickly because I know I've got only up to an hour here the that gave me an idea what do we mean them by election hacking we've defined this heck sad we've looked in what we mean by all these different factors so I came up this it's an attack failure or breach of data related to or upon the electoral system that involves an electronic or cyber element so that
would be my definition of election hacking based upon mining data from the press and academia to see how it's used looking back in history the historical uses of the term hacker and then trying to come up with a set of heuristics and a model for for what we mean by the term and I think I think it's a pretty good definition I'm sure you know does academics out they would probably take umbrage with some of the stuff in here and be great I'd actually be interested to hear where they differ with my my opinion on it so real-world examples in fighting back so examples from the recent past I mentioned brexit I'm sure everyone in
here was familiar with the 2016 election the Netherlands their election was in 2017 and France was in 2017 as well I think the key difference between the Dutch in the French elections were because of everything that happened in the UK in the u.s. in 2016 going into the beginning of 2017 people were perhaps a little more cognizant of the risks they faced in 2017 started to be more proactive at preventing them so the UK one so the Vario registration website this this was a special interest to me when I was writing my master's thesis I actually ended up going through my mp in the UK up to the Cabinet Office level two to get a response from them on it
and effectively what happened was on a night I think it was a Sunday night before the registration closed there was a flood of traffic which took down the voter registration website and it was largely blamed on a television show that had happened a debate right before I guess midnight it was around midnight when it crashed so a debate it happens shortly before that result that was a lot of people went on and signed up and it just the spike in traffic caused it to collapse digging into a report that Parliament put out on aftermath of it you know there was there was talking there of Facebook rumors told people all you need to sign up multiple time so had
that contribution contributed it to crashing certainly there was poor infrastructure planning I mean that's just going outside of the realm of cybersecurity you know that was obviously not load testing done there and then was there misinformation and fake news after the event which then said when the website crashed oh it was the result of BOTS so digging through reams and reams of quite boring documentation and reports and what have you my general impression is that the website was lacking in certain areas of testing the television show contributed to an increase in traffic people on Facebook do to perhaps poorly put out information on how you register and start signing up multiple times and then once it crashed there was misinformation
but I'd actually argue some of that came from the report itself that the MPS didn't really understand what happened and so there was these you know accusations or it could have been a DDoS attack from Russia or similar none of the evidence seems to point that way but then of course they aren't necessarily going to release that the Cabinet Office of the Foreign Commonwealth office or whoever whoever owns it but I think that does make me you know it reminds me that even people who would consider with the best of intentions can end up accidentally spreading rumors which then can undermine people's belief in you know the system and and how well it works so if you're interested it's on
it's on the UK Parliament website it's the the peacock report on the the voter registration website crashing so the next one is the u.s. so the internet research agency in the GRU these are both Russian organizations the the internet research agency I've heard it referred to as a combination of a marketing firm and an intelligence organization and the GRU is is a Russian branch of intelligence minute a Vegas tied to their military intelligence um June of 2016 election my graphics aren't lighting either there was obviously a lot of talk around Russians attacking the the US election system the result of looking at like the indictments that came out from the mullah report and all the research that was done around like
the date of theft of ence guseva the folk they faked protests organized on social media I don't know anyone in here's familiar with that but um Renee's work who I mentioned earlier it looks like there was those fake news organizations that were running on Facebook we're creating rival groups and then trying to encourage them to protest in the same location at the same time hoping it would all kick off thankfully it didn't it didn't seem to have been as bad as they would have hope so I guess you know from that perspective we can be thankful but certainly looking through everything that's come out of the Moller report and the related indictments there's a lot of things and now that we
would probably consider election hacking certainly the day of theft the exfiltration the fake news the bot networks so so that's why I included this one over here the the Dutch elections which happened the following year they as I said there are a lot more on the ball base scrapped vote tally tallying technology to do two security affairs and in addition to the election at the time there was also a bit of a diplomatic spat happening between the Netherlands and Turkey and all simply Germany in Turkey at the time so sites providing information to Dutch voters were targeted by DDoS attacks allegedly from Turkey so that was definitely an example of from from the hex adder the
DDoS angle and then the second one which I thought was quite interesting was WikiLeaks ocean of previous leaks targeted at the far-right PVV party so what happened was in the past WikiLeaks had got hold of information and believed there were emails on guard welders who who's a dutch politician and had leaked it and then when the dutch elections came round wikileaks started to promote that information again so we could argue that that was a another example really of election how can even though the event had taken place previously it was they were able to use that and amplify it during during the dutch elections [Applause] next one is is France so Mekons on marsh party was attacked
the email infrastructure there was attacked the French actually dropped plans for French overseas voters to vote electronically in legislative elections due to concerns that had been raised over the previous years you know and the risks that such systems face there was a DDoS attack on said exes which hosts major French media outlets like Lomond in La Figaro so they I guess said exes hosts multiple media organisations so they were kind of a single point of failure when they got here when there was a huge fake news and disinformation campaign launched against the 2017 election interestingly enough the the French have a window between when the campaigning ends and the Election Day itself whereas kind of a
news blackout so anyone dumping fake news in that period might actually find it's more difficult to get leverage at last minute as compared to other countries now I don't suppose you could probably do that in u.s. because they'd be first and when questions around that but the French I guess you know at least be able to new to some of the effects of it due to that to that rule around how they run their elections quite interestingly Huskie in and back mo did a 2017 report and this is what they know it you know there was republishing news from russian sites such as russia today and Sputnik - those two are traditional media organizations in the sense that they
have an address and a physical location but some of the content on there has been accused of being biased they've drawn conspiratorial and anti system tropes they promoted a hard right French identity during so that would be if you think of left for national and marine lepen who's the the french far-right candidate they circulated our anti-muslim material and they pushed hard left in anti imperialist content certainly if I remember correctly in the 2017 election period in France Mellon Sean was running who tends to be on the far left of French politics so you know this whole pushing people into the to the extremes was I think part of the the plan that was conceived here there was
hope New Hope's news sites so I meant to Delhi at the Belgian you say who is less well so they had they literally cloned it and then ran faking whose off it until they got shut down that's pretty clever hacked and then I there was fake polls as well in order to undermine the credibility of opinion polling ran out it's really coming to second part the title my dog is you know how did the authorities fight back so there's a number of defensive techniques so remember we want to reduce the attack surf is so my graphic on the right which did load this time you know we've got a large hex out here and then we sort of
reduced the surface and if possible we'd like to remove some of the edges during an election so that we can reduce the overall attack surface the way we can do that is a few honey pots and fake email accounts the French did that and I'll cover that in a second we could make sure we just have good infrastructure hygiene so patch our equipment and software load test it and pan test it so after all you know if someone had done proper load testing and taking that information on board during the UK referendum there's a good chance that website wouldn't crashed which wouldn't have resulted in the fake news being spread and wouldn't resulted in MPs then saying
something probably in good faith which then escalated the situation even more we can use you know standard techniques for harboring infrastructure and cleaning the operating system access control mechanisms another thing which is great is is mfa if people have got MFA on their accounts so you know there might not be technically minded individuals they might just be people working for a political campaign it does add the actual layer of difficulty in breaking in and stealing their emails especially if that individuals been part of a previous data breach and had a particularly weak password and every used across sites which of course none of us ever do yeah MF 18 at least hope to mitigate that you
know on the infrastructure side there's other tools as well web application firewalls DDoS mitigation techniques and then logging as well to help do an analysis after attack encrypting your data at rest and in transit so that's always a good good practice training staff on you know social engineering so how not to end up in a situation where you give things away to someone you shouldn't because they're acting as somebody else and then finally this one's probably going to be a little more controversial is regulating advertising or Terms of Service I Twitter just last week decided that they were going to ban political ads starting I believe at the end of this month you could make depending on where you sit on
the political spectrum you could even argue okay we want the government to regulate ad ad platforms and ads or you could say if you're on more towards the other end well perhaps the terms of services are good enough you know if facebook says don't do this who can it's their platform at the end they can just kick people off regardless of whether they think is free speech or not so as to say a little more controversial but but there whether you take a government approach or a private industry approach I think there are mechanisms that can be used there too to at least dampen some of the fake news and in the bot networks and what have
you so the the French just come back to the French election they used a can call cyber blending or cyber blurring strategy which was really a case of training staff to be alert to phishing attempts implementing like fake email accounts so if they get hacked into there's just junk in there or responding to phishing emails with with specially crafted accounts so you can then start to track where these emails coming from so you could do things like basically counter insertion them always you're turning the table on the attackers to try and figure out where they are the implementation of honey pots filled with fake documents and using low level encryption I thought that was quite a
clever idea the hackers then waste time and cycles you know and you've got to only gotta find them out the time before the actually election happens trying to crack that encryption to find out that what they found and I was junk or just disinformation so just one last point on on that one as well just the counter insertion the wall where I would imagine and I don't know if there's any legal scholars here there's probably some question around whether that is allowed I don't know a French law so I can't tell you ever whoever it's permitted under under their legal system but I would imagine that counter insertion of malware okay perhaps the people attacking you aren't gonna go and turn
round to the authorities and say hey I got hacked when I was trying to hack him but you know if you picked the wrong target to count a hack and and it's someone who's legitimate I can I could see that being a problem so it's gonna just add that caveat there so thoughts on the future what can we learn from other success stories be proactive not reactive I think that's true for any area of cyber security when you're defending systems you know don't wait to be a victim know your enemy so gathering use intelligence there's plenty of open-source intelligence out there and then of course there's companies that specialize in it use diversion allusion to your favor so
the use of honey pots something which I came across wild backwards from the Snowden leaks and it was published on the intercept was GCHQ the British signals intelligence organization had talked about you know using this idea of Volusion and magic on the Internet so if you think of it like you know basically how do I deflect people's attacks and how do i push them towards something that looks like it's legitimate but it's just going to waste their time don't be afraid of pulling vulnerable equipment and reverting to manual means if something's broken don't just leave it in production if you have to pull vote machines and revert to using pen and paper you know it may be a pain but it
probably is the better solution in the long run and as I mentioned turn the tables on the attackers there's some interesting legal and ethical questions around that and then learn from your failure failure is in remediate so I think regardless of you know which country you look out over the past three years there's a lot of lessons that can be taken away by any country that's running in elections and use those two to be proactive so what other strategies might work this is kind of a shameless shout out for myself using the hex ad can be a good mechanism for looking at risk and signing it to a category once categorized an agency or individuals can
then be assigned to address the problem by breaking the risk down to small the problem areas we can attempt to address them whilst also providing overall coordination on the effort problems flowing outside of the hex ad can then be assigned to agencies and bodies responsible for tackling them for example money laundering fraud and so on and that allows us not to muddy the waters you know for those responsible for defending infrastructure or tracking botnets whatever it's really about you know understanding the domain and then coming up with mechanisms to take other problems and hand them off to them to people who are better suited to investigate them whilst you concentrate on your own your specialty so in
conclusion my final thoughts democratic systems are increasingly at risk and failure to act and - the public's trust so even if it's hack is unsuccessful if the press reports on it it's gonna immediately start to raise questions and people's minds free speech will be leveraged against democracies so as we've seen with fake news on social media or fake Facebook groups individuals are going to use that and they're going to push it so really what we can do is just to be better educated in critical thinking when we look at something ask is this really a true source or is it you know some dudes blog in you know some 400-pound dude sitting on his bed in the
basement so I and then something really thinks quite interesting is deep fakes and other emerging technologies they're going to add another dimension so we really need to think about how we counter that now or not wait until there's a fake video of the next president of the u.s. saying something which they didn't say and then you know we have to think about it political infrastructure faces advanced persistent threats so in the case of the u.s. elections we could say that the giu and the unit's associated with those whether it's fancy bear and so on you know that's that's just the nature of the beast and on the final point if you're still waiting for the capture the flag
clue hidden in my talk you've missed it so if you sell all the way through to this slide you've already missed it oh no no no just as sources of interest just to reiterate some of these Chris summoner's talk go dig thou Chris Wiley's book is quite interesting obviously I can't prove his claims in it but I think if you're just interested in the subject please go read it the Oxford uni comp prop Department which I mentioned fantastic there's also online now the Guardian has lots of articles the Mueller report the memos indictments you know a lot of information around the the Russian operations and what they were up to you back in 2016 so thanks
for listening and thanks to all the b-sides team here for your hard work
and I realize we're running really tight in time so we have two minutes for questions or if you want you can grab me right after at lunch and I'll be more than happy to chat with you