A Unique Approach to Threat Analysis Mapping
About this talk
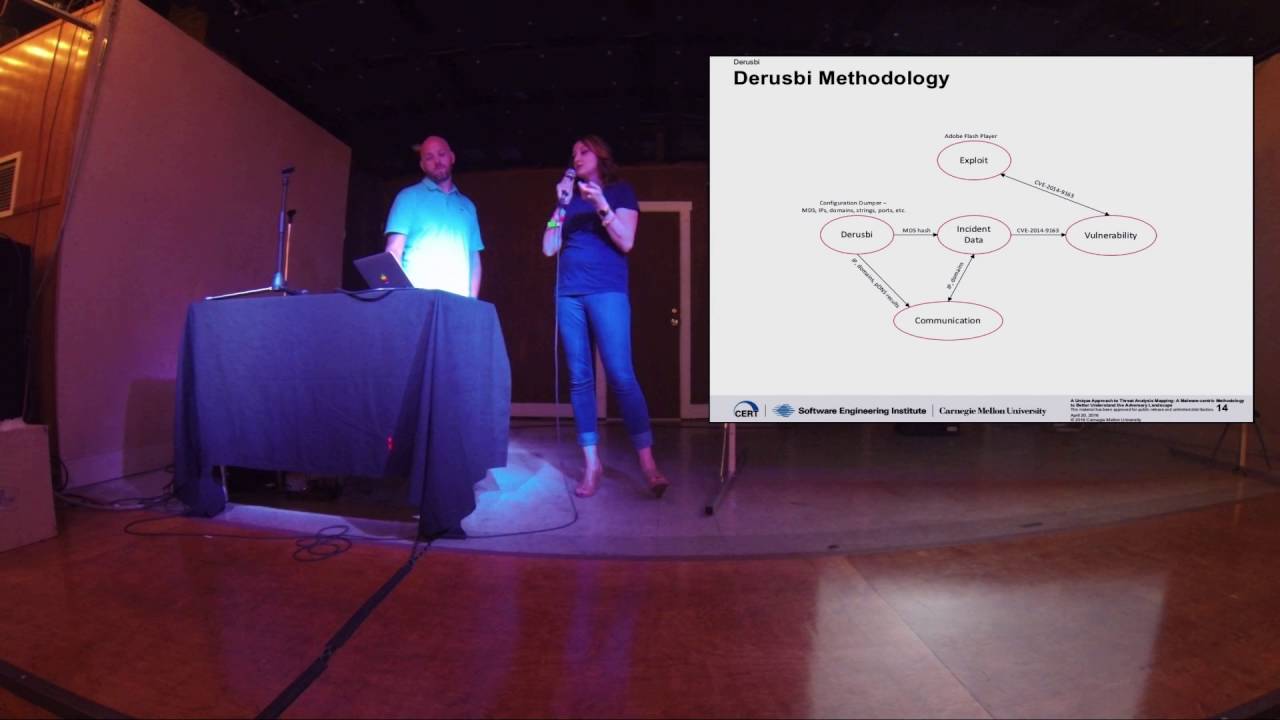
A Unique Approach to Threat Analysis Mapping: A Malware-Centric Methodology to Better Understand the Adversary Landscape Kyle O'Meara, Deana Shick Abstract: Malware family analysis is a constant process of identifying exemplars of malicious software, recognizing changes in the code, and producing groups of “families” used by incident responders, network operators, and cyber threat analysts. With adversaries constantly changing network infrastructure, it is easy to lose sight of the tools consistently being used and updated by these various actors. Beginning with malware family analysis, this methodology seeks to map vulnerabilities, exploits, additional malware, network infrastructure, and adversaries’ using Open Source Intelligence (OSINT) and public data feeds for the network defense and intelligence communities. The results provide an expanded picture of adversaries’ profile rather than an incomplete story. The goal of this document is to shift the mindset of many researchers to begin with the tools used by adversaries rather than with network or incident data alone for an “outside-in” approach to threat analysis instead of an “inside-out” method. We chose three malware families to use as case studies—Smallcase, Derusbi, and Sakula. The results of each case study—any additional network indicators, malware, exploits, vulnerabilities, and overall understanding of an intrusion—tied to the malware families should be utilized by network defenders and intelligence circles to aid in decision making and analysis. Bio: Kyle O'Meara is a Senior Member of the Technical Staff at the Software Engineering Institutes's CERT Coordination Center (CERT/CC). Kyle works on the Applied Threat Analysis team at the CERT/CC where he researches and analyzes current and emerging threats to national security with a focus on exploits and malware. Most recently Kyle was with FireEye, where he was the lead senior threat analyst for the active cyber defensive program called SHARKSEER. Prior to FireEye, he was with the National Security Agency (NSA) for roughly five (5) years. At NSA he had a few different positions as a cyber-cryptanalyst, six (6) month deployment to Iraq as a media exploitation analyst, and a communication signal analyst. Kyle received his MS from Carnegie Mellon University in Information Security Policy and Management. Kyle has also presented at major information security conferences to include DEF CON and FIRST Technical Colloquium. Deana Shick is a Member of the Technical Staff at the Software Engineering Institutes's CERT Coordination Center (CERT/CC). Deana works on the Applied Threat Analysis team at the CERT/CC where she researches and analyzes current and emerging threats to national security. Prior to working at CERT/CC, Deana was an International Trade Specialist focusing on EAR and ITAR regulatory processes. She received her B.A. from Duquesne University in International Relations with a Security Studies concentration. In 2014, she completed her M.S. in Information Security Policy and Management from Carnegie Mellon University. Deana has presented at major information security conferences to include FloCon and FIRST Technical Colloquium.





