V For Vedette (A Warning From The Frontlines)
Show transcript [en]
okay so um V for for videt so um let me start off by just saying I was really desperate for a title and I just had to pick another VW um but a videt does stand for a century or an outpost so um so the reason I kind of picked that is because I've probably had my head above the parit either investigating or or defending uh against cyber threats for a while so I picked that but um but videt is also uh a French term for a lead show girl um so it's might be pick your own adventure and we'll see where this one goes but um so let me kind of kick off then so on on that note that's not my
weekend uh normal outfit but um my background is um essentially now I'm a I'm a contractor working for the working for the home office I'm the head of the the Seck there um so uh can of protecting all the stuff that that they do kind of join them as um to do some maturity work and then ended up in there kind of position that M um but previous to that I worked as the kind of lead and or um head at the end of um of NHS digital for for their sea sock um I foolishly uh joined the sea sock um to to lead it six weeks before covid which uh now seems like quite a bad idea um so
as you'll imagine kind of during that period we we went through some growth uh and obviously quite of quite a stressful period um and we built what was a small team into into a large one by the time the left so some really interesting stuff there um background before that then I was a police officer uh for 14 years uh and essentially um that was um doing all sorts of technical stuff foot patrol in Bradford at a start which is uh which is definitely um a kind of uh way to introduce yourself uh to the world some uh some life experiences that uh that's probably another talk in itself But ultimately uh ended up in a
regional organized crime unit so doing cyber crime investigation towards the end end of that career before um yeah doing a doing a masters and uh wanting to continue doing cyber outside um early experiences kind of in the in the workplace um I worked in a in a in a in a bank doing internet banking support so I don't want to give away my age but it was 56k modems uh and the business ones were 128k uh so you know real real fast stuff um learning on Netscape and doing all that all that kind of thing so so it's definitely felt felt like um we've moved on slightly from from those days so what I want to do in this talk is really kind
of talk a little bit about really about kind of cyber crime and just some of the incidents and things that we've come across um during during the kind of last sort of decade and a half or a couple of decades really um so let me just start off with with saying I will refer to kind of us investigations or kind of you know dealing with incidents and I'm going to use that in kind of like a royal Wii Just for the sense of this so at no point am I saying that any of us have been affected in any the places that have worked by any of these incidents you know if we have or not is
a different question but um I'll talk about Royal Wii um so we've um been exposed kind of to uh to various different groups and incidents as we go through um and clearly you know I've worked in in a few different places so but want to talk about we I mean like security industry as well just so um it's just easier when I when I kind of talk about it but um criminal gangs basically um want to make money that that is that is how they that is how they work and certainly kind of pre um uh pre- ransomware World um it was carding so that that was where most of the money uh or or most of the financial
interest kind of came came from if we just stick to kind of pure pure cyber so people were dropping databases and they were sharing credit card information um you know across that period so in kind of early kind of 2000 you had some of the Big Data dumps like Yahoo in 2014 and then you had other kind of peaks of Interest so obviously Snowden kind of dropped out um during that period um but but Cardin with their kind of underground kind of hackers is probably where they made made most money um and probably before PCI and that's why I think we've kind of seen that kind of transition into into other other types of crime not that carding doesn't exist
but it's just not as popular so on that note then I'm not going to talk extensively about andon us cuz clearly you know you all you all know about their background um but I think you know some of the activities that they kind of came through you know they were kind of um challenging uh and hacking for for aange there was extradition attempts of of Lor love um for the uh activity um that he was accused of against us uh government and Military but these were the headlines so back in those days you know the the headlines that were kind of hitting for uh for cyber were were anonymous because um they had really good branding uh to be fair you know
that's an iconic image that kind of has resonated through and what it spurred was additional groups uh and kind of people of that time you know that were into that suddenly realizing you know that they had technical skills that they could apply um and some of that you know they wanted to apply for good causes Etc um you know and they would they would kind of be pulled into that sphere so out of that kind of lul SEC kind of dropped Direct out of anonymous um you know and they were responsible in 2011 for uh for knocking over um or or stealing X Factor contestants from the US they targeted Finn Fischer um they weren't necessarily financially
motivated you know they were there kind of for the cause Etc um but then like another deviation or derivation from That Was Then u a group like lizard Squad so some of you may or may not remember them but certainly for a couple of Christmases they've ruined kids Christmases by by um knocking over Xbox and Playstation so all the kids immediately could come and play the games and they got got got dropped um but they were also uh responsible for um sort of League of Legends uh and and allegedly North Korea internet takedown they took responsibility for um and they defaced Malaysian airlines with a 404 not found so they gained um kind of quite a lot of headlines mainly because
they were you know pretty much a trolley group and there was a couple of other groups that kind of came out in that period that kind of um you know were quite quite similar and there was like beefs between them um but not necessarily kind of financially completely financially motivated um also kind of headlines around that time was uh Mirai botnets um and then the stresses that that were um readily available so why why this is important I mean certainly kind of Investigation wise there was quite a lot of activity you know NCA and uh and Etc and other kind of Partners we worked with europol and that kind of thing where stress is you know pretty
rubbish now dos is not necessarily on the headlines for everyone but back then you know you could take a stresser you could pay for it using some crypto or um or whatever um and knock down a company and and there was certainly a period of time where you know dos defenses were just not good enough uh and you were able to kind of take take things down notably s of the D dos in 2016 was probably like a real big Benchmark for that um they took down kind of Facebook and Twitter for a period you know and these were kind of quite quite headline things and probably kind of rocked people's kind of confidence around you
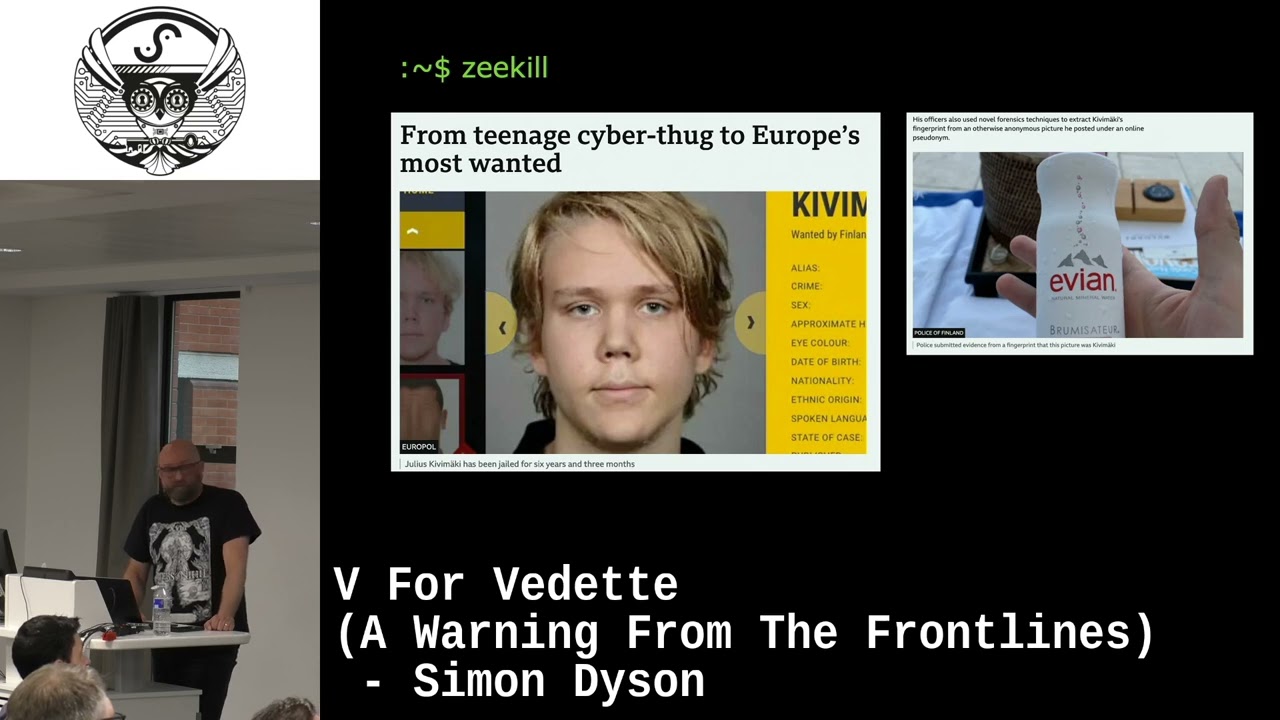
know what was what was possible with that type of Technology um so one of the reasons I wanted to kind of bring up U lizard Squad is that recently um zekel who was the alleged leader uh has recently being caught by um by uh Finnish Finnish police um and it was an investigation that was uh in relation to um hacking that they U he took took part in against a Psychotherapy um institution stole those records and then basically started to kind of blackmail people um so ultimately you know went from a um a group that were trolling to certainly kind of you know nailed on cyber crime so he was charged for 30,000 crimes um
and uh yeah and he was actually caught in uh in Paris now the reason that I kind of like this is it down to like some proper investigation work so you see the picture on the right hand side is um is an image that he posted on a sudim account um they actually took the fingerprint um from the image and were able to resolve that to a point they could identify him and then that's how you know basically he was caught um and brought in so I I do genuinely genuinely love that um so this was another leak there a bit of documentary on it on it at the moment but why why this why this
is important is um this is probably one of the first hacks that isn't just Financial this this has and had genuine um impacts on on on people's human lives so you know you're probably aware that people took the lives out the back of this certainly destroyed people's marriages uh and people's lives um but also if you think about that data set and what's available in there if you've got someone that um wants to keep their private life prate um you might be able to kind of put pressure on them so there's quite a lot of dog addresses there was quite a lot of military addresses within that data set so certainly kind of becomes something
that's a bit more uh bit more of interest you know a bit more of interest and really you know those kind of data set sets still exist um we haven't had anything quite quite like that for for a while but you know that kind of material you know could always always
reappear okay so um cryptocurrency so one of the things that's made uh the ability for cyber crime to to to flourish is cryptocurrency I I like cryptocurrency and blockchain I'm certainly an advocate and the criminal element is only you know is only a small part of the of the overall um overall kind of uh transactions that run through cryptocurrency um but I can't deny that actually you know the ability for um for people to kind of trade in what they thought was uh iously uh kind of laterally you know they they're probably aware that that's not the case um certainly kind of made a boom so there was early um dark market so Silk Road
Etc that kind of Spun up during that time um ethereum was kind of introduced there which introduce kind of a different type of cryptocurrency so not just transactional not just digital gold or the ability to kind of just transfer money you were able to kind of you know basically have a um a computer network that you could run uh you know you can run smart contracts um and um and that that brought on various different crimes so at that time there was some huge um divisions between cryptocurrency um people that that that that ran those systems so people were kind of probably from the the kind of anonymous type era where um code is law um and there was a
couple of um there was a dow hack which was millions of pounds and basically that split ethereum into ethereum classic and uh into ethereum um as it is now but it but it resulted in you know in huge losses um and there's still kind of decent hacks you know that um that are targeted against smart contracts that result in you know from time to time some uh some reasonable thefts it was Peak boom so everybody was talking about cryptocurrency you knew that because you went to the pub you know your dad was talking about it and uh their mate etc etc um you know or even your grand started to mention cryptocurrency so you you know you KN
you know it hit peak time um so that meant loads of scams obviously um but also kind of uh a rather large peak in crypto thefts so certainly at that time Hardware wallets had barely come in so people if you wanted to steal someone's wallet you needed access to the machine uh find the seed code and that was enough for you to kind of take over a wallet and to uh and to to get hold of that cash um so certainly from an investigation point of view you know there was a there was a significant number of of incidents that that we were involved in at that period um the other thing then is um privacy
Focus so this probably comes back into Ransom where which we'll kind of touch on in a little bit um but there was a peak in in privacy focused coins so Bitcoin um isn't anonomous um it's it's literally the worst the worst thing to be anonymous because it's um all those transactions are detailed online so once you've got someone's account you've got their entire banking history it's worse than you know having to go and apply for you know a warrant or or what ever to um you know the records from a from a bank um so what we found was there was uh misters and Foggers in which case you know you're just going to try and uh
make it more difficult for law enforcement so if you took a coin in at the top splits it into lots of different ways Roots it all over the place and then pops it out the other end um not foolproof you know done quite quite a bit of work around um around sort of investigating cyber crime and a couple of papers kind of in that in that area um but what it meant is privacy um came in so there was Monero and zcash which is um giving the ability for someone to trade uh trade a coin with someone that um that you don't know and you can't trust um but to be able to share that
coin in a way that's non-traceable um and that was kind of the focus of of Monero um so what we found is uh some of the some of the ransomware groups took hold of that they did use it for a period but they're pretty much just gone back to um to Bitcoin now mainly because it's actually hard um Z cast I think they used for a period before they realized um they'd been using it wrong all that time uh so it made no difference at all okay so ransomware um technically uh 2008 um some of the first bits arguably there's probably bits before that um but certainly the um the start of ransomware you could pay
your Ransom in PayPal um and you could pay by other things I don't know if um postal orders were quite quite quite used but but not too dissimilar so you could um and there was a couple of small strains but it wasn't it wasn't hugely used um 2013 was crypto Locker um and I think you know kind of based on the timelines you know that's the first the first real um point where cryptocurrency is is used and utilized um between that period and pre wry um there were some significant groups and that's definitely the rise of organized crime and you can see kind of the ransomware groups starting to build in that period um certainly investigated a
couple um which um you know which always kind of just say you know is basically before Ranson where was cool those investigations and and there wasn't the pull and there wasn't the drive which is why when wner Cry came um and I was sort of police side then and supporting the investigations from from that side um it was a game Cher I'm not going to cover one a cry because everyone knows about it but what what it was um from um from a cyber crime point of view it made people aware actually the desperate nature of how it can uh damage your business operations which has an ultimate kind of cost View and that's a
leverage and that's why kind of post 2017 there was obviously not Peter um but from that period kind of I guess running uh up into um early 2000s and obviously you know ransomware hasn't gone away but the but that that peak time kind of uh Gan crab ryak and emit um and and the lock bit groups um it's it's huge money I mean looking at 2023 1.1 billion in Ransom uh you know was taken so that that's larger than kind of small uh small economies so yes the state sponsored thin Gray Line Between that ultimately it is driven by money you know not none of those are kind of sat um sat on on small wages they're
doing it so they can so they can buy Yachts um and sit around and take Instagram pictures um but the ecosystem that developed around that time so it's not just the rant somewhere um it's um your initial access Brokers um it's Crypts in order to kind of sneak past um the uh detections on boxes obviously ransomware but it's exploits you know they're going out and buying exploits in um you know obviously the dropper ecosystem so um so ruk and Emet um using trickbot for example and qbot laterally um ransomware as a service obviously developed so you can kind of get it in a whole package even you know they' even kind of create Elite site for you um
there's a couple of really big kind of hits kind of across that period kind of colonial pipeline kind of being one of them um so Colonial pipeline was um was the us-based one shut down their operations and that was a legacy VPN with a single Factor password um that was that were hit by dark side um and then a fishing base attacked by Cony which hit the um Health Security executive in in Ireland so um some huge stuff there um and Co strike and and the post um kind of um exploitation Frameworks all kind of used across that period you know and Cobalt is still you know still used quite heavily now so third party supply chains so
solar winds um obviously kind of made its name I'm going to hurry through some of these maybe um but third third party supply chain is is a real issue for us um and continues to be one um so we've seen solar winds which was you Advanced pist IST threat using a golden Sam attack um that really um obviously Supply chains happened before Target and etc etc but I think that was um probably a real shift change for those groups and if you see the kind of activity that we've seen after so there's been kaer Mage carart at lassan um it's a shift change move it for example that that came in in 23 took out
BBC and and ba and Boots um you see that the reason why those actors want to go for it management software is um you know you pop one box and you get many and you get the ability to kind of reach to many so you know VMware was really popular for a while in terms of as soon as you get something from VMware and we'll we'll cover um some of the edge devices in a second um the other notable thing was log 4J which absolutely stole everybody's sleep um and I'll apologize for people in the room who uh who had their sleep stolen uh by by me um it was mainly the bosses the NHS you know Etc
or whoever else you know um but um you know many of us will remember that but the difference with that is just how difficult it was to to to to uh to find the the um items in log 4J so clearly it was inbuilt open source software for a start so you're not going to one vendor to find to find your items it's bundled into many things so if you're looking across large networks um then you know and large Enterprises leg networks just to find where you have that stuff is really difficult um okay so Arcane door um is um there's a Talis white up on Arcane door um this is um basically an attack
against endpoint devices so I'm not going to say too much about this but from the tals report it says um Arcane door is a campaign that is the latest example of State sponsors actors targeting perimeter network devices for multiple vendors um covered by those actors perimeter network devices are the perfect intrusion point for as Espionage Focus campaigns so if you do not treat your Edge devices as precious as your ad then I suggest you know definitely go and look at that um I know it's really difficult to uh update those Edge devices because they're all over the place they're black box there's not one patch that patches them all um but that needs to be a shift change across you
know across um all Industries really um okay so Verizon um and breach data so I want I just wanted to really quickly just touch on this so if you're in a defending position um and you're kind of following this this probably won't be a surprise to you at all um credentials is still the easiest way to get in and um you know we've had some of that covered um earlier with where you can find credentials just laying around um but no MFA Etc you know is always going to be one of the first ways of getting in colonial par line as an example um fishing is always um or is still popular um I would suggest that the controls
around fishing are getting easier with people kind of adopting 0365 it's more difficult to get fishing landing on boxes not impossible the ones that do land on boxes pay more attention and do some more work so they don't get back on um but I think it's getting more difficult for for fishing attacks in General right now um but exploit vulnerabilities has risen by 180% over the last over the last period uh from the Verizon report that's a real step change and I suggest the beginning of this year is probably going to uh only increase that um so the cesa known exploited vulnerability list uh is something you know that um that is definitely worth looking at so if there
is an item on the known exploited vulnerability list um it will be scanned from when it's announced from that day to um a cve scan within five days so in a very short period people are scanning and looking at that that detail um 68 days if it's not on that on that Kev so I would suggest you know really kind of prioritize anything that hits that hits that c of Kev as something that you would um progress really quickly um lapsis already mentioned earlier one of the reasons I want to mention lapsis is um it's been a while since we've seen a group which is you know a smaller group of skilled individuals it's probably the
best way to kind of put it um that are not really associated with organized crime and they kind of came out of nowhere um a little bit like anti-establishment so they were hitting higher education and government initially kind of in um um in South America um but they've got you know they had a global global uh imprint certainly an individual kind of UK based um what it matters is they did become financially motivated you know perhaps they were pure of heart at the beginning and then and then switched um so they used VPN in desk and Citrix and they were rolling things over but they hit people like Microsoft Nvidia Samsung and they were hitting Healthcare Financial
um Rockstar you know that kind of leaked a lot of the S source code um what was interesting for me for this group um is they were using social engineering um so they were doing things that was not the norm and I think it surprised people I think probably surprised people that had not experienced that before um a lot of the things were pretty basic we might talk about social engineering but you don't actually see it uh a significant amount um and they came in and were really really effective um and I think it just shows you know that people can kind of spin up out of nowhere when you make something hostile so the better
technical controls we get the more criminals are just going to circumvent and just do whatever they don't need to do so um I often have ation around projects and user management you've got really good controls you've got MFA but if your password reset is just bring a help desk and they just reset it without question then what's the point um so evolving deception so a lot of the time we spend um a considerable amount of time looking at the new the new shiny technique that they use uh in order to kind of um to get us through um so if that's quing um you know that's kind of coming through at the moment the QR codes and and fishing attacks um one
of the more recentish ones was interplanetary file system so that was moving from um uh from URL uh and then crossing over onto web 3 Technologies so hosted on blockchain so you can't take it down you can't really can't really block it um but one of the things is you have to go through a Gateway so if you monitor the um ipfs gateways ask yourself do we have a a a real business need at the moment to allow any of our people to push stuff out to web 3 CU if not then just shut the door um also Wayback machine um so there's a few recent attacks where um they were hosting malware on Wayback machine um
bizarrely uh you can just get around and use it also there's material on way back machine which is probably not compliant with your acceptable use policies so again you know maybe just have a look at you know what people are using way back machine for um and if you don't really want it then maybe think about moving it off um so AI I'm contractually obliged to say I during this talk because uh it would be remiss be not to um so um I am scared of AI because I think basically it's just clippy just kind of dressed up with uh in his Terminator guys um but ultimately um I think there is a risk of
AI uh joking a joking aside um but I don't think necessarily the thing that's going to hurt us straight away is is all the things that probably we're predicting um I think what's going to hurt us most is when we adopt it really quickly into our environments because um everyone's heard about Ai and the boss has heard about it and it's really important we have it cuz uh if we don't have ai then we're not doing our jobs properly um so I want to introduce LOL Lun which is live off the land large language models so this is where we give the attackers all of our corporate data that we've decided to put in our large
language model to make it easier for all of our employees so now we can say um what's the corporate password policy so we don't have to kind of try and work it out ourselves we can just find out what how we would make it up or um what is the email for the head of Finance so we can fish them a lot easier um but there's a number of kind of other issues that we will have with large language models um for example um over permissive with apps so what can we do what are we allowing people to do can you reach out to the internet can you create code are you going to allow people to you know uh
spin up poers shell um because probably because someone's got a business business need for it somewhere so we just left it in um there there is um an a wasp um top 10 so if you've not seen that there's there's a number of different things and it goes back to all the basics like uh validating what we put in ETC so really quickly just to conclude then um so lapsis raised out of nowhere a little bit like the activists of the old days um and and were really effective um that can happen again um so again you know that that's something um that I predict will probably mean that we're just like we were before um dos um
although it's not prevalent as much um we have just had one of the largest bot Nets taken down um and marai variant so you know harking back to the old days um has recently kind of hit two terabytes a second um it's not hit anything massive or taken anything down um but I will guarantee that there'll be some point where dos will will make its uh make its way back to our uh to our headlines um supply chain so talked about solar winds but we've also seen mod and the NHS recently impacted you know by some of that supply chain uh impact Microsoft recent runin where they had the key thefts um from uh which was basically a
pivot from Legacy kit on the development Network um we've seen iced ID in a recent infection using RDP in order to laterally move and and jump all over the place um and essentially yeah criminals still want uh boats and cash and they're going to adapt to whatever controls you know that we put in place um so I don't think anything's massively changed and I think some of the attacks that we've seen you know over the past couple of decades are just replicated in a slightly different overlay um you know and basically yeah people are going to keep trying to take your money um so protect yourselves yeah thanks [Applause]





