Sean Weiss: Designing an Effective Security Operations Strategy with a DevSecOps Mindset
Show transcript [en]
so thank you everybody for attending today um so my name is sean weiss uh systems engineering manager at fortinet for western canada um for those of you who don't know me um i've been at fortinet for about 11 years um which is uh seems like forever now i was employee number 768 and i think we're somewhere around 8 000 people now so it's been a long interesting ride previous to fortinet um i've had experience working for uh mrv which was uh uh basically an uh mpls optical startup company uh back in the old days the good old days i was also used to work at hp and uh and mcafee so i've been around all right so today what we're really
going to look at um is we're going to talk a little bit about designing an effective security operations strategy uh with dec devsec ops so we'll talk really about integration automation and especially how it can be applied uh to infosec today so we'll talk a little bit about some of the limitations that we're being faced with in today's it security environment how integration and automation especially can really sort of help us overcome some of those limitations so here's the agenda we'll do a little bit of a lesson back in time we'll have some fun with that one maybe um we'll talk a little bit about the state of security today we'll talk about what devsec ops is and
isn't um and then we'll we'll kind of take a bit of a different path and maybe take a left turn at that point we'll talk a bit about um a security strategy and whole in a general sense and how we can apply dev sec ops to a security strategy um and then hopefully we'll have some time left over and we'll do a bit of q a towards the end all right so let's talk a little bit about automation oh i don't think my slides are moving in a sec here guys just notice that all right here we are all right so if anybody can pop their their uh their their hand up in the chat
um um i don't have a prize today but i promise i'll get you one and so here's the question for the prize and i'm gonna um i'm gonna put it out there um automation um i'm going to attribute the earliest prediction of automation to this gentleman right here so so for for for the million dollar question for the grand prize at fortinet um can anybody tell me who this gentleman is that's the question i'm looking for the name of the guy in this photograph and uh don't say david mitchell for those of you who know david mitchell at fortinet uh he's also got a great beard um worthy of anyone's powerpoint but it is not dave mitchell this is somebody
much much older um than uh than that so can anybody guess who this guy is i'll give you guys a couple more minutes so first answer this question uh gets the grand fortinet prize and what you can do is send me your email in the chat and uh i'll be sure to follow up with you with uh with the prize all right so i'll give you five more seconds all right this is karl marx right so at a time in the light bulb hadn't even yet been invented um karl marx is basically in in in the mid 1800s um again before the light bulb is even invented predicting things about robotics that would um that would replace humans in the
workplace and so karl marx has a quote that's pretty interesting and this comes out of something that wasn't translated until the 1970s from german but he had written something that was very futuristic and he had written something along the lines of once adopted into the production process of capital the means of labor passes through a different metamorphosis whose culmination is the machine or rather an automatic system of machinery the workers themselves are cast merely as its conscious linkages so really what marx was trying to get at um was really the earliest predictions of automation and the effect that would have on human labor um um karl marx if if nothing else i mean we all know him
as a socialist and the father of socialism um but really for me when you study karl marx he was all he was really a futurist um he was really all about predicting um how capital and labor um were interacting with one another uh during the industrial revolution and and there's some similar overtones uh to to today with devops um as we see automation kind of taking over um you know what used to be very manual i.t processes all right now another stat that had just come out from the world economic forum this is a prediction about the job landscape um as it's going to look in 2025 and what the world economic forum put out um with some numbers
uh was this interesting step what they predicted by 2025 was there there would be an 85 million job being displaced by machines so what they're basically saying is 85 million jobs are likely to be at risk by 2025 jobs such as data entry clerks administrative people accounting bookkeeping payrolling clerks auditors factory workers assembly workers and the one thing all of this has in common these are very manu manual very processed very very repetitive um mundane if i can use that word type of jobs we'll talk more about this on the flip side in a minute so let's kind of go into cyber security or the state of cyber security today so a couple stats i want to throw out
there that are going to have some relevance here as we kind of go through automation and integration and devops 197 days this was done by the ponemon group last year 197 days was the average time to discover a data breach 69 days is the average time to contain that breach and 81 of those breaches weren't even discovered by the victim they were discovered either by law enforcement uh other partners uh research companies somebody other than themselves so there's some pretty telling stats um that shows a pretty sorry state of affairs when it comes to our ability to respond now here's a here's a famous quote from gartner so gartner will claim breaches and attacks are
inevitable so gartner's um um have this quote um um you've probably heard it before and and they're probably right um not to sound defeatist but everyone is going to be breached at some point and what really separates the adults from the kids in this business isn't so much your ability to just stop that breach because we're all likely to be breached that's how do you deal with that breach after the fact how fast are you at responding to that breach and minimizing the impact of that breach for me that's really what separates the professionals uh from the wannabes in this business a couple other stats to throw up there they're gonna have some relevance uh to
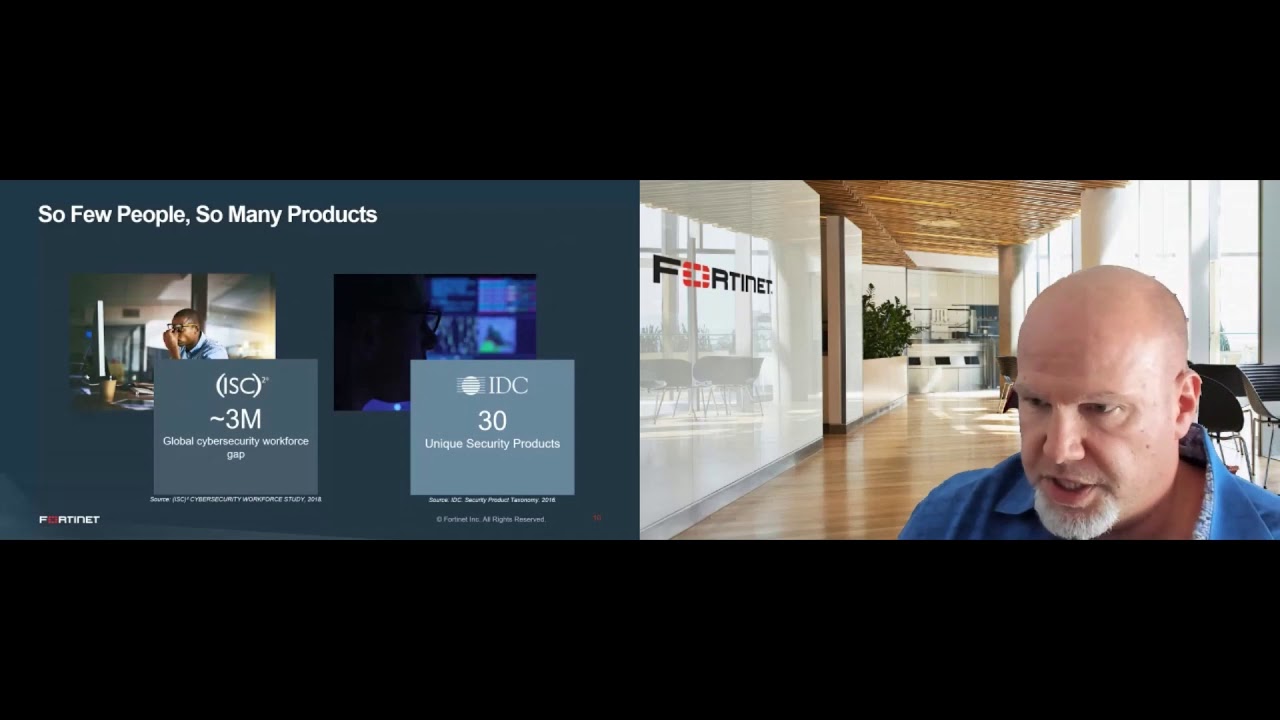
our discussion um there's about a three million shortage or shortfall of trained cyber security professionals today in in the workforce um really what this is pointing to is the fact that we can't even hire all of the people that we need from a cyber security perspective even if we wanted to there's just a shortfall of trained um people to do the job another interesting stat from idc was the average customer will have over 30 different unique security products now we as vendors and of course i come from the vendor space so i'm i'm i'm all about throwing more more toys at you but um it really seems like you know every time there's a new threat
vector out there we want to throw some new shiny whiz-bang toy at you um and and that's why we've gotten to the state of things where you know your average customer has got 30 different cyber security toys um at any one given point in time that's a lot of things to worry about a lot of things to be trained on a lot of things to try to integrate um or when hits the fan trying to go through some sort of triage process between all of these different different products and trying to figure out uh what console do i need to go into and how do i cross-reference um you know the sim console versus the endpoint console
versus my firewall and so on and so forth so there's a lot being thrown at security operations people today the other stat that i want to talk about is these two right here so a stat was done this was done by esg research what they found is that 80 of organizations that were polled um were basically complaining that their digital innovation was being slowed down by cyber security um so essentially the business was not able to move at the speed of business because because security i.t security specifically um was too often in their way the other stat um um in this uh in this research uh 71 of organizations believe that their team lacked basic devs sec
ops practices so basically saying things like integration and automation were lacking in their organization so we got a long way to go and that's really what we're talking about here today right the use of automation and integration it's obvious that we need to do something different um technology has to catch up um with where the business wants us to go and at the speed that the business wants to go um and just to do a better job of cyber security um uh as a whole and that's really where automation and devops are going to become even more and more important now on the flip side of that stat that i showed you from the world economic forum
those 85 million jobs um that um that were that are essentially being lost to automation is actually created 97 new million jobs that are going to be centered around people that can take advantage of a devops mentality so things such as data scientists machine learning specialists data specialists or big data specialists i should say and then process automation specialists so those jobs that are being lost to automation somebody in the back end has got to create that automation um and there's actually more of those jobs that are going to be created than the ones that we're actually losing all right so let's go through some devops definitions so i think through some of those slides
that i just showed um you know really the crux of the problem here um we've got too many vendors or at least two you can never have too many vendors of course because i come from a vendor space but no seriously we've we've got too many products um too few people to manage too many products we're getting overloaded with alerts we've got processes that are too slow or too manual and we just have too few people to manage and operate this whole thing so this is why automation and integration is becoming so important and that's really what devops is if nothing else it's all about automation and integration it's about reducing repetitive tasks right it's the
ability to program and automate the remedial things in your day-to-day activities leaving you as as a an operator to do things that are maybe more strategic um so rather than you know manually pouring over logs uh trying to search for an ip address or a domain or a url and then going into the firewall and hand bombing into the blacklist um wouldn't it be nice if that was all automated and you could leave you know you could use your time um for maybe threat hunting or you know more strategic um sort of things rather than hand bombing in ip addresses mac addresses and other mundane type of things and this is this is all built
around trying to increase efficiency right trying to contain a breach faster right so when things are integrated and automated and you're doing things less manually um we're going to be able to get to a process or to a state of security where you can contain things much much faster than if you're trying to do this manually now the other point i want to make here too is devops and devsecops if i can use those interchangeably isn't just about scripting it's not about infrastructures code and in fact i would even argue that that you know your your script kitties your programmers the guys that love python um that job in and of itself is likely to go away to some degree as
well a lot of devsec ops capability is actually being put into what i'm going to call normal language you don't have to be a script kitty you don't have to be a python expert to take advantage of this mindset now it can help um but um but we'll talk about about that as we kind of go through uh other parts of the uh of the presentation all right another little uh stat to throw up here top reasons for dev sack ops so what is the primary reason your org employs or plans to employ dev sack offs and really it's all about security right so if you look at some of these stats and i won't go through all of them
in the interest of time but number one the yellow guy there in the pie chart again this is done by esg research it's all all about the ability to allow us to improve our security posture by making sure cyber security controls and processes are tightly integrated um with our business the other big one um number two from the top there making us think about security proactively right so that's really speaking to the automation piece of devops um you know containing a breach without me having to wake up in the middle of the night and log into the firewall or log into the endpoint console and try to figure out if this is really an attack and who's being breached
and who's being who needs to be quarantined wouldn't it be nice if that was all just automated so the alert you actually get is that hey guess what uh joel blow downloaded malware but we put him on the quarantine vlan or we've taken that server offline um et cetera et cetera that's really where devops for devsecops is all about that's where it's providing value so let's take a bit of a left turn let's talk a bit about um security strategy and how devops falls into that now i'm going to kind of talk about fordnet security fabric um and i'm trying not to be overly salesy today so so i'm not necessarily pitching fordnet here but i'm going to use this as an
example and there's there's others um out there today that that'll have a similar um concept and strategy in fact when i used to work at mcafee years ago um i would i would i would venture to say and hopefully hopefully my boss is not on the line today but i would say mcafee was a very early adopter of this back in the day maybe ahead of their time in fact where they saw the benefit and you know the need for the industry to move to an integrated automated approach um and so again you know just giving a plug to others here that have the same sort of mindset but really what we're talking about here
is a strategy for a holistic integrated concept of i.t security not having things in silos and there's a reason for this and and just kind of bear with me here as i sort of go through this at a high level so in terms of a security fabric the first thing that we're interested in is trying to create this broad um visibility of all the different ways in and out of your network data can flow so firewalls mail gateways web gateways um visibility into your cloud visibility into your your sas apps endpoint um iot all of these different what might look like point or silo products we need these covering all of the different doors and windows
and ways in and out of your network because if i can't see all of the different ways that data and users interact in your network i can't fully understand the risk that's involved in your business so that's why your strategy needs to be broad you need to be covering off all the different ways in and out of your network that data can flow and we do that for a couple of reasons and the first one is going to be to integrate these things together right so integrating endpoint with sandboxing and sandboxing with the firewall um and so on and so forth at the end of the day we want to integrate these things together um
so that they can share data and more importantly that they can share the ability to enable action when something goes wrong somewhere else that's how we get to a point of protection faster and the ultimate point of protection is automated so the the the holy grail of this whole strategy is to automate all of these things together so that you're not having to do these as a manual process so again giving you that example earlier where in the middle of the night when you uh look at your phone because it's buzzing like crazy and blowing up um your the alert that you get is hopefully the one that says hey um joe blow uh downloaded some malware
but it's okay he's being quarantined um and you can go deal with it tomorrow morning or he's automatically being um scrubbed we've uh we've ripped out all of the traces of malware the registry whatever it was done or we've gone back to a known good that's a much better email in the middle of the night than saying hey um your world's on fire uh go put it out okay let's talk about carda so i don't don't know if you're all familiar with carter but garner has a model a security model called the karta model and really it's all about not to be glid but it's all about keeping out bad stuff um and letting in the good stuff right
so what we mean by that or what gartner means by that are a couple of key points here so card card is all about continuously monitoring and continuously assessing risk and trust so as devices come in and off the network um what we allow those users and those devices uh to do is all based on whether they are clean and safe enough for us to let them uh touch the resources that they want to touch and of course authentication goes hand in hand with that are they are they also authorized right which which speaks to trust but this this process isn't just a one-time thing we have to continuously monitor um their behavior we can't just
because they came in this morning uh all honky dory doesn't mean by four o'clock this afternoon that their uh trust level um and risk uh to the business is is is the same so we need a process of continuously monitoring and looking at these users and devices the other point carter tries to make is enabling adaptive responses and this starts to speak to integration and automation a little bit then they talk about baselining existing systems and this is really talking about user behavioral analysis um you know talking about users and devices doing things today that maybe they haven't done before um things that they maybe don't do normally and then anticipating threats and attacks that's the other piece of
gartner's carter model so we kind of put this in perspective um carter lays this out in seven seven different imperatives if you've ever read their document it's all about replacing one-time gates with context-aware programmable platforms so programmable being the key word here we talked about continuously discovering and monitoring performing risk and trust assessment instrument infrastructure for comprehensive full stack visibility um utilize analytics automation so number five that's another uh big bullet point um that's really again speaking to the devops mindset in this model it's all about automation orchestration to speed up detection and response so number five is a big one again speaking very much to um how the carta model um very much has an eye towards this
whole devops devsecops mentality number six architecting security as an integrated adaptable programmable let's use the word orchestration system um and so yeah so carter you know the point i'm trying to make here is that gartner also feels very strongly about a devsecops mindset and and you can see it in the in the carta model here and the imperative these seven imperatives where where this whole idea of orchestration automation is really throughout the whole model so fortinets um has something called the dynamic adaptive security architecture this is really very similar to to the carta model i'm going to kind of flip through this uh interest of time these last sort of two sections these are these last two steps
of this five-step model or architecture is all about rapid response um and it's all about you know after we've sort of built out a model of you know web application firewalls and next-gen firewalls and mail gateways and you know protecting sas apps with casbies and web gateways and whatever else you know we might have sold into that network and put into that architecture at the end of the day is we're getting threat intelligence as we're getting alerts as we're getting information um into our security operations we're then at a point where we can use tools to start remediating quarantining um when we see these threats um or cleaning up um right so it's not always just about
quarantining something and you know shoving it in the corner or in the closet and forgetting about them but automating even the cleaning up of that endpoint or getting that endpoint back to a trust or a state of trust um that's really step number number four in this in this dynamic adaptive security architecture using tools like soar which we'll talk about um using the apis um using some of the built-in gui based automation tools um that'll be available all right let's get back to maybe more of a devsecops conversation so some some key use cases and and number one the auto deploying of services and resources this is probably the the the um the real low
hanging fruit um from a devops perspective and this is the ability to auto deploy security at the speed of business we kind of talked about this as a problem earlier on let's do a bit of a time check um where you know maybe the business and their digital transformation um story um needs to deploy things up in the cloud as they you know spin things up at lightning speed um you know security needs to come along for the ride but not as an afterthought it needs to be done at the time of deployment so as web servers are being configured as cloud infrastructure is being deployed gateway next-gen firewalls and gateways web application firewalls um whatever it
might be that's offering maybe some micro services um um sort of segmentation to maybe a kubernetes deployment all of this needs to be done simultaneously and so this is being done with with tools such as maybe terraform or ansible um some of the built-in cloud scripting tools with with amazon and azure but that's probably the the main um the low-hanging fruit behind this whole concept i'm not really going to get into that anymore though i really want to shift more to the next two or three for that matter so the other low-hanging fruit um or other main use case for devsecops is the ability to or auto-quarantine infected endpoints and users and devices right so what we can do with the dev
secops mentality automation and integration is when intrusions are discovered or a breach or a successful breach is being detected malware is being downloaded and executed and you know we can go on and on with the example the ability for the infrastructure of the network to auto quarantine the things that have been infected or the things that are at risk away from what's healthy and then being able to take that intelligence that it's learned from this breach whether it's source ips mac addresses urls hash values of malware then being able to share that data um with other systems where we can then go do some further threat hunting to see who else has been infected and then adding these iocs these
indicators of compromise we can add these to various gateways to blacklist any further communication or attack from these sources or destinations so that's really the other two sort of main use cases where we're seeing devsecops being used today and then the fourth one um is unlimited uh because a lot of this is api uh driven um um it's programmable um at the end of the day these use cases are only limited by your imagination there's literally nothing you can't do um if it's available as a command um so if your api is basically a mirror copy of everything that your product can do from a future perspective there's really nothing stopping you from from developing your own use case
um other than your own imagination so we talked about this one already i'm going to skip this one so let's talk a bit more about automating security so some of those those use cases that i just mentioned and we'll kind of go through some of the building blocks and some of the some of the details so we really have a concept of triggers versus actions and then these actions can be automated um as i've kind of mentioned throughout this whole conversation so triggers are gonna be things such as system events so a system event can be literally almost anything that's logged um you can create a trigger from from that event but some of the big you
know the low-hanging fruit ones would be malware detected or an ips event has been detected um or someone has gone to a bad website um and we'll go through some other examples um user and device status so this could be another trigger um new device has been detected that we've never seen before or a you know a new user logs in from a place they've never logged in from before or a device logs in who's just failed his vulnerability scan or has exhibiting too many uh critical severity level um vulnerabilities and there's other millions of other examples this is just some low-hanging fruit uh from a from a trigger perspective but on the flip side of that we have the
ability to define actions so if we don't like the fact that some devices just showed up on our network that we've never seen before or that it has too many vulnerabilities that we're just not comfortable with or that he's got malware or downloaded malware whatever it might be we then have the ability to do things such as notify send a report quarantine the user and we'll talk about what that means because that can go in a million different directions or we can adjust configuration we'll talk about that so triggers so i kind of talked about these already so let's talk about a few more so we talked about compromised host whether however you define that
someone with vulnerabilities ips events downloaded malware um another trigger could be something that we've learned from the cloud itself so the cloud's sending us um information uh whether that's something from azure uh google depending who uh who it is we can also enact uh we can also absorb data from those systems as we're building out um a whole response sort of playbook and that could be that could come in as an incoming web hook so we'll talk about what web web hooks are in a minute and then actions would be things such as uh quarantining at layer two right so taking the mac address or taking that user throwing him into a special kind of vlan
where where you know he might only be getting access to um remediation capabilities right like being able to update his malware uh engines um or um you know having a system um uh cleaned or what have you um same thing with quarantine in the client so rather than putting this this user on a vlan we actually could take that user and quarantine them completely off the network um without having to put them on a vlan we can actually enforce that right at the client side um so some of your some of your various clients uh edr endpoints out there um can do that as well so we don't necessarily have to put somebody on a special vlan for this
purpose um we can do all we can also do things such as banning ip addresses on the on the firewalls and we can take those ips and share them across the infrastructure so if you've on you know a gateway in calgary um you've got uh you're being attacked by a certain source that's source intelligence you can then propagate that to your cloud infrastructure you can you can send that ip to all the other gateways throughout the rest of your network all of your branches because maybe they're going to attack a branch next maybe he'll attack the cloud um but you know if you share that source information with all of your infrastructure um hopefully you can make things a lot
easier for yourself things like that an action could also be another web hook so web hook is really just another instance of programming it's an incoming web hook might be somebody talking to one of our systems so talking to a firewall for example um but it could also be us sending a command to somebody else as a response so maybe again it might be something like assigning a tag uh to azure right so we see something in the cloud that's vulnerable um or something communicating something in the cloud that's vulnerable or exhibiting some sort of cyber security event we can tag that with uh with cloud tags in fact there's one uh built into the box today with
with vmware for nsx and then vmware would then have the ability to then say hey anything with this tag we will do this and so you can kind of see how these things will play off of each other
do a quick time check okay um and this is perhaps an example of how some of this would work um so let me just sort of uh show you a bit of an example here of how um you know an automated integrated solution from a malware point of view could work and we'll talk about this from from both um a fordnet perspective where everything's kind of the same vendor where of course automation becomes easier but we can also talk about this and how it would work with third party um so we've got some gateways of various um um kinds on the left we've got next-gen firewalls we've got some mail firewalls we've got some web application firewalls
load balancers um and then a web gateway on the right side we then got our edr clients um um next-gen av agents whatever you want to call them maybe protecting servers and endpoints and so the whole idea here um as we sort of add this technology with malware analysis tools such as sandboxing um um is we can then you know maybe maybe there's an endpoint um he downloads some malware today never been seen before it's a zero day as he downloads this file off the web or from his email that file is then thrown over to a sandbox a malware analysis engineering tool file analysis tool this tool takes a look at at uh the file
and determines that yep this is malware there's a url in here we don't like there's some ip addresses uh for command and control channel uh there's some registry settings uh that are malicious um that that are gonna be used for encrypting the hard drive so on and so forth um it takes a snapshot of the file creates a hash value and basically all these iocs and threat intelligence that the sandbox now has that at its disposal from this threat intelligence um um scenario that's that it's carried out within a couple of minutes of getting the file he then can share this with all of that infrastructure all of the firewalls that might exist throughout the network whether there's
some in the cloud up in amazon in azure at a branch office in your own data center which you can share with with the mail appliance so on and so forth and then of course with the endpoints themselves that endpoint or a sim this can also be shared out with with a some somebody's sim and then maybe that sim tool you can then use it or the edr tool you can then use it to say hey maybe we've seen this ip address before maybe we've communicated um to this url before maybe this hash might live already within um our asset inventory and then we can use threat hunting capabilities based on the threat intelligence that we've learned from
some of these other tools to then go hunt from what we've just learned from this one one endpoint having downloaded a piece of malware and at the same time this endpoint who perhaps detonated the file would then be quarantined um put onto a vlan perhaps for remediation and cleaned up before he's hopefully infecting anybody else so very automated very complete sort of a to z strategy that's made possible through automated through automation and integration um and in the case you know this is all done easier when it's vendor um when it's all the same vendor not always a realistic um um uh sort of undertaking most customers are going to have multiple security vendors in their network
and that's where the apis become important so there's no reason you can't do this with practically any vendor as long as there's apis that that vendor is publishing and creating and so a lot of this can be done you know from vendor a to vendor b even though there's no official sort of integration between the two just by using these web hooks that i showed you earlier by essentially taking advantage of api calls on how to move iocs and enact actions from one one device to another this is what a web hook might look like from a ford net perspective from a fortigate perspective to be exact so this is just showing some json commands um uh being put into a
russell api call essentially um so one of them here is basically just showing us uh showing you how to log in with a um with this web hook into a 4d manager um so this would be at the beginning of a script that you might be doing all sorts of different um things with after the fact um and in fact the other picture that we're showing here on the bottom left this looks like it's showing a web hook that is taking a source ip and a mac address and probably putting this onto a quarantine list with with a web hook so you can see the url that they are using that they're calling up there's a concept of an api
admin key uh for security so this is just a quick example of what a web hook would look like uh we talked about this already so probably in the same time i'll skip this one um but really this is all about you know let's not forget about the cloud especially um um as we talked about devsecops because you know so much about devops is about the cloud um and and there's so much about the cloud that can leverage devops but really we're talking about here is more from security perspective in terms of the ability for us to interact with the cloud and quarantine things in the cloud with these various integration api calls that are that can be made possible um
right so let's let's not forget about that as well it's not just about quarantining or or taking action on our own infrastructure on prem you can also do this um with whatever we have in our in our cloud infrastructure some other triggers that um that we can also talk about these ones in the middle so security rating summary so what security rating is this is a bit unique security rating is all about the ability um um to take action upon a security audit so security rating is a service um that will run on the fortigate for example and it'll look to see what the configuration looks like maybe you're using weak passwords maybe you're using des instead of triple
des or aes or maybe maybe you don't have profiles with antivirus and ips maybe your admin account has got a weak password things like that as the result of this security rating becomes known to the to the network or to the infrastructure we can use that as a trigger so maybe your security rating sucks today you you've got you've gotten to a particular score that's pretty bad showing that your fortigate is is misconfigured we can have an action as a result of that maybe somebody's changed the configuration and you want to be notified of that configuration change or um you want to revert back to a different configuration we can do that and these are none of
these actually would require any python any scripting these are all pre-built out-of-the-box automation integration capabilities so none of these are going to require any sort of specialized knowledge and that's kind of key to my message today is that don't think of devsecops as necessarily um you know somebody who's just writing scripts and and has to know the api backwards and forwards a lot of this is being built into the products um so that you don't have to be that guy necessarily now it's going to help though it won't lie and we'll talk about that in a minute but again um h a failover could be an event maybe av or the ips database is being updated
a lot of customers like to get notified when an av or ips data database is being updated they want to be able to be able to see an alert so that they know that if things hit the fan a couple minutes later from a bad update they'll be able to go oh you know what i just had an av ips update five seconds ago let's go look at that high cpu or memory uh overload or uh memory capacity issues you can also use these as triggers um for doing things of course they can all be scheduled right so again it's just getting back to um the different ways that you can think about devsecops and automation and getting
back to that one bullet point i had on use cases where really this is just limited by your imagination so you know what there's a lot there that we've pre-built for you um really you're only limited limited by your imagination okay now let's close off with soar try and do this a little bit quick i'm going to run out of time in a few minutes um so soar stands for security orchestration automation and response if there's one tool in the security marketplace today that's about devops devsecops it's sore right so this family of tools is really all about automation and orchestration for security operations right so these are tools systems applications with an organization that really enable any team to automate
incident response workflows um they're really trying to take the the devsec ops or the traditional approach or definition of devsecops out of this picture that's why they cross it out here in their um you know good little slide here they're really trying to say hey you don't need to be a python expert to make this work um if you want to automate if you want to triage you want to threat hunt um don't think this is this has to be done with a whole bunch of open source tools um like lego without a manual and a whole bunch of um you know scripting and and and programming uh sore tools are trying to take away all of that
so that they can try to make this a much easier quicker um um solution to put into place from day one hope that makes sense so a quick little example of how a sword would interact with the world um so think of swords different from sim don't get them confused everything in your network would probably still flow to something like your sim right so so your sim is still going to be your central place of all of all logging um of all reporting and then what your sim does is it's going to filter up the important alerts maybe the higher severity alerts depending on your use case but the sim is then going to forward
this data up to your sore tool and your sort tool is basically going to be where you're going to research threats you're going to execute the remediation of threats um you know maybe you're getting a phishing attempt that the sim is throwing you alerts on you can use the sore tool then to figure out okay exactly who's gone to that website how bad is this website um and then because you're going to integrate your soar tool with your firewalls and your web gateways and your mail gateways and anything and everything else you can think of with connectors the sort tool is then going to be the place where you remediate you will enable automated actions where
the sore tool will then take that domain that url and he'll he'll put it on the blacklist for um um for this phishing website you can put it on the next gen firewall you can throw it into the sim uh as well you can throw it into whatever tools web gateways um but whatever tools that you you need to automate with that's what the sword the sword is all about so it's about opening tickets case management um standardizing investigation and response uh to security incidents that's really what a sword tool is all about a quick few snapshots of the gui um in a store just to sort of show you this looks like um and there's gonna be some pre-cam
playbooks of course that are done out of the box um but you again limited only by your imagination this is showing you the ability to drag and drop different um variables um in building a playbook out no coding required at this point just the ability to drag and drop if you've got a mouse you can build a playbook uh in the sword um and again this is just showing you sort of the start of the whole process some of the different um steps and different variables that are available to you so again you might build some for phishing responses right when you get a a uh a phishing alert um how do you want to
build out your response do you want to build out a response that says hey let's go to the firewall and block the url let's take the source ip and put him in on a quarantine list build a playbook that would show exactly that um drag and drop once you've added your connectors and your devices it's just a drag and drop scenario on how to play that out maybe you want to add a few things to it so maybe as part of your fishing exercise you want to go to buyers total or you want to do an ip reputation lookup or you want to go to the fortiguard web filtering database to go um um add
him um or or request that fortigard um or any other sort of threat intelligence uh web filtering solution um uh uh who hasn't looked at that as a phishing url maybe re-examine that on their own so they can add it to their own their own threat intelligence so a whole bunch of different sort of things you can add to these playbooks on your own um i'm probably going to leave it at that um i'm going to run out of time i think we're uh about three minutes over um um so i think you get the idea here guys so i just want to kind of again basically just close off um with this whole concept of
integration and automation um um let's call it devsecops um but really it's all cyber security today if we're going to do a better job if we're going to do a better job of deploying tools we're going to do a better job of of protecting systems um it has to be done with a devsec ops mindset it's got to be done through integration and automation because there's really just no other choice there's no other way to scale today without thinking about it security operations in that context thanks for attending today guys take care





