Build Customer Trust by Strengthening your Security Practices
Show transcript [en]
okay yay so um this is what happens when you're talking to Omar and he says Hey the next speaker isn't there I'm like oh I have extra presentations like joking around and he was like you're speaking uh so uh those of you who know me well know I like to talk and I I like to share and educate so um this topic is on building customer trust by strengthening your security practices so it's a little different it's not a technical talk but more about learning from your customers and trying to learn from them to strengthen your own practices so I'm not going to do the intro to myself because I've done that but I'm going to pull you first so how
many of you have received the security questionnaire from a potential customer or given one right good amount right uh those are always so much fun um so when I think about things I want to talk about how do you connect the customer and the security um mindset the supplier security mindset and then how do you leverage those inquiries to learn to to push and forward your your security practices and then how do you enable your business to improve their security practices how do we drive those improvements how do we pull those product teams in so uh first let's hear so I've got another poll uh how many of you have a team that actually handles those customer security
inquiries that you get one two-ish ish right yeah um I'm very lucky until um my team actually handles these inquiries um it's it's pretty cool to have this team because we we could tap into that information so I'm going to talk about that in a little bit but um I want to talk about what's changing why is the landscape changing we used to just start with sdl and vulnerability management and think okay we got this and our customers say okay that's great if they even inquired about it in the first place um but think about you now right you're sitting here and you're going to be signing with some vendors what are the things that you're looking for when
you're purchasing them I mean those vendors that we're talking out there right when even even them when you bring them into your infrastructure what what are their security practices how do you know that they're good um and what what would make you feel uneasy what about your own practices that make you feel uneasy that your vendors would have um so we used to start and say okay we do volatility management we're good but now the mindset is changing especially after log4j right I mean it started changing way back with harp lead uh and Specter meltdown you know put us forward again but uh log4j pushed us a whole another level recently um they want to have a multi-factor
authentication right so it used to be something that was a hardening security practice that now is a must-have from some of our customers um they want to know about our security practices and not just a you do scl and vulnerability response but like what is your sdl like what are your controls uh do you do threat modeling what else do you do um and then there's the questionnaires that come in it's sort of like you could go and you could always be reactive to those questionnaires or you could start thinking about being proactive that maybe when you go into sales and and the customer comes to sales right away those sales folks know what's going going on
so that they could better answer those those questionnaires and it's really about building trust way earlier on um and what we're noticing a lot lately is that security weaknesses are top of Mind of our customers so they're like yeah you should be fixing vulnerabilities you should have that already but what about these weaknesses are you fixing those findings um so and then all the regulatory I think we didn't mention it earlier but there's supposedly like 140 different regulatory things that are going to be coming down to us how are we going to handle it how you know our customers are going to want to know are they going to be able to meet compliance with certain
things so when we talk about our mindset here and we think about a customer their mindset is oh my gosh I don't want to get attacked right I don't want to violate any of these regulations I don't want to have reputational damage and I certainly don't want my stock to go down and the way that they measure it is about security policies so they're going to think about what are their own internal policies but what are all their vendors policies and those of you who have gotten recent customer contracts I if you ever looked at them they're not just saying hey you big Corp need to have this they're saying all your vendors need to have these practices in
place also um so that vendor vetting process is really important uh you know to make sure that just the same things that a customer is putting on that big vendor all the vendors underneath that we're using have the same practices too because that's what your customers are going to expect and last are those fun industry regulations how are you know do you have an s-bomb are you going to give me your s-bomb uh things like that so suppliers mindset typically I have a CL I have VR I'm great right I have the basics down it's just unfortunately not not good enough so how do you approach the customers how do you understand what's top of their
mind um so one of the things that it's been a really good practice and like I said I came into Dell and I was lucky enough to to have this team and it was underneath me and it was already pre-established but to me it was really ahead of its curve to think about having that a core team that focuses on customer trust and it's from having an operational team that can answer those questionnaires that come in or inquiries or some product might screw up and not you know have an old Os or a old log for Jay version that one dot X version how do you handle that how do you make sure that those inquiries come in and go to
someone that could speak to the customer and you know intelligently about it how do we enable the business to understand the customer needs one thing the one downside about having a core team do this is that sometimes we're protecting those product teams too well that they're not feeling the pain they're not hearing that customer saying I want this I want that so how do you pull that business in how do you make sure you're educating them and then also we think about our customer engagement how are we making sure that our customers see what our security practices are and that you know we are are partnering with them that they're hearing it and they're not
just hearing it from sales from marketing but they're actually hearing it from like real security folks so when uh when you have a a customer and their security team is talking to you as a security team it really is a good partnership and a lot of the times it's like oh yeah I understand the struggle that you guys are going through West Palm I'm doing it right now too so you know I get it what's your journey and you could really have an honest conversation lastly is thinking about the customer security experience so anybody who talks to a customer account managers or that customer support person answering the phone somewhere they need to know how to
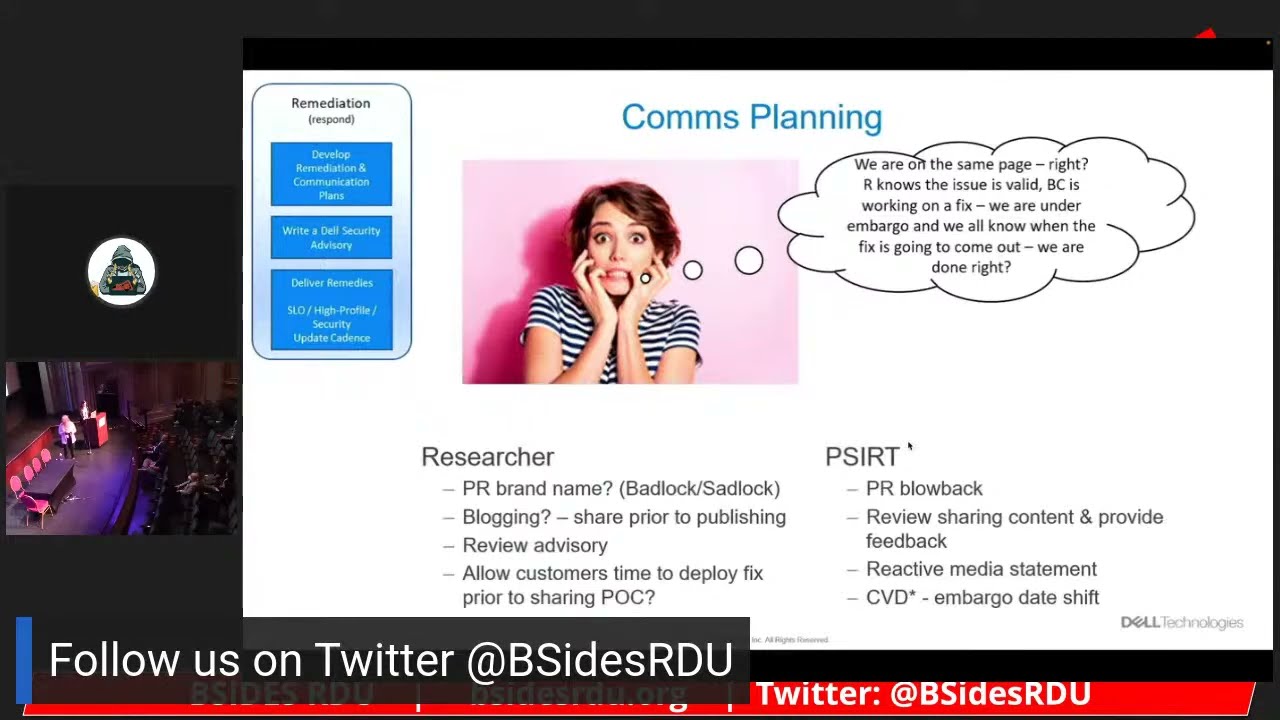
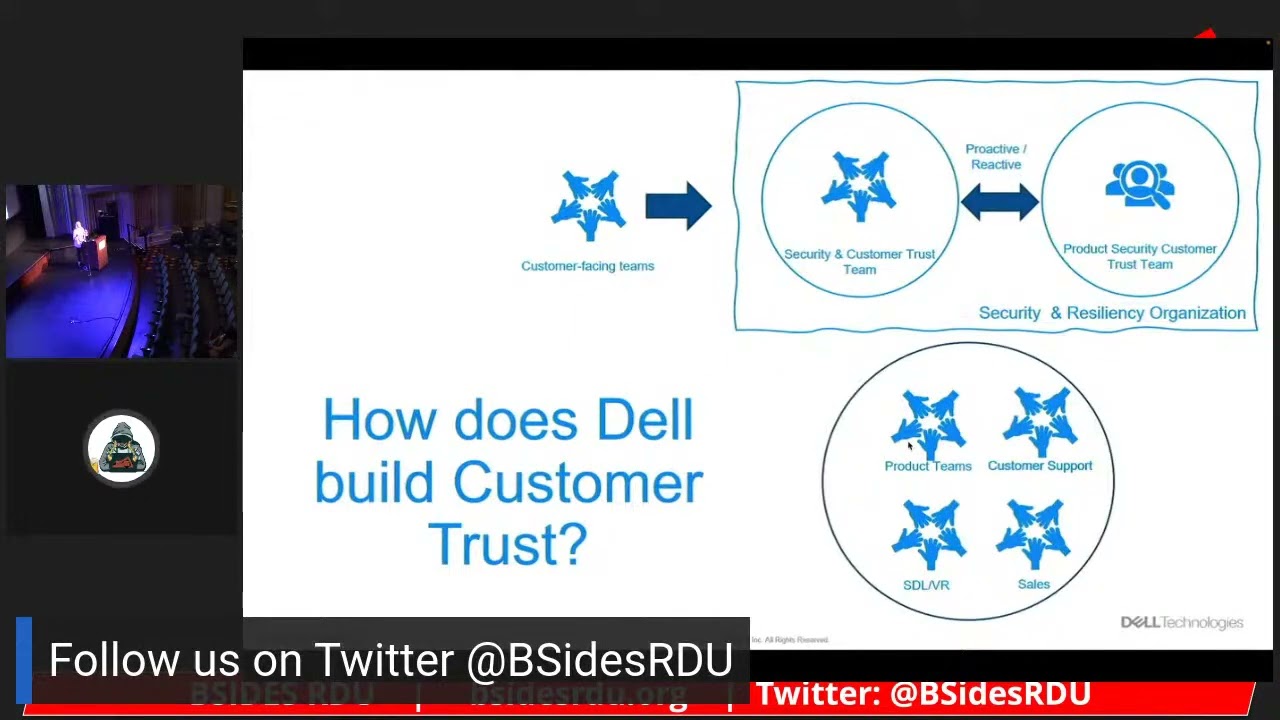
get to this core team they need to even know the terminology when is it that a customer's reporting a vulnerability versus when do they have an inquiry about our practices so in in Dell this is how we have our program so we have our customer facing teams and it goes to what I call like the level one it's a security and customer trust team the questions like sock or what if there's an incident so even Beyond product security we could answer all the security questions but then within my team I have this like level two this product Security customer trust team so this is when those inquiries get really difficult to answer like do you do this do you do that how
was your security design did you design like this the amount of questions that we're getting from our customers are way like way more intelligent than it ever used to be we need to have our act together to be able to answer it with that we work with the product teams we work with customer support we work with sales we work the sdl and VR team so when we think about our journey here with the customers there's some Basics that you just need to have as you start and if if those of you are new into the space or your company's still new at least make sure you have some of the basics abilities assign cves publish the
security advisories don't let your marketing scare you away from being trans I get it only I was in where they were like oh my gosh you you know our customers are going to think that we have so many vulnerabilities everybody has vulnerabilities right everybody has vulnerabilities so be transparent about it multi-channel communication if you can have the API you know the Vex the the um if you could go on to a specific product page and see the security information too besides just your maybe external security advisory page like get it out there and get it out there as much as you can to your customers configuration guides another thing they're an afterthought but there might
be things that you allow in your uh in your product because of Legacy stuff if you're allowing like TLS 1.0 or something like that which is scary um but you know you want that configuration guide to say you shouldn't enable this like or you're accepting the risk if you enable this um how do you handle the choir inquiries and questionnaires how do you make sure that they don't sit in some customer Cube queue for like you know like 30 days that's not good right um how do you handle the scans we get like 400 page scan reports how do you even handle that how do you process that how do you go back to the customer
to say Hey listen I'm not going to process this 400 page scan you need to go through it and figure out what's important for you for us to look at um and then a lot of customers are going to ask for the attestation letters so making sure that you're doing pen testing making sure that you're doing threat modeling some of the basics and then spend the time to train those customer facing roles shift it left let sales know about what customer you know what customer concerns are insecurity let them know about what your practices are so they could build that trust from day one so these are the basics that I think about when I begin
trying to earn a customer's Trust then we need to continue on the journey one of the ways to continue on is to learn about the interactions you've had with customers about the experiences taking it back to the business taking it back to your security team so when we think of log for J log for J was a lot of work right we thought we were doing pretty good we had a security notice we had indicated what was effective what was not affected we had an FAQ that was publicly posted we had security advisories for each of the products that were affected we did this coordination it wasn't enough though we had customers saying how does your products actually
use log4j what log4j version is installed I said this earlier we had customers coming to us saying you need to be on that 2.17.1 we had to go back to the customer and I had to say listen my job as to better protect you and I'm not stopping these teams that are going and right now driving to that 2.16 where that active exploit is um so a lot of time we spent re-educating the customers we had to do all this clarification about workarounds there's tons of work around for log4j thank goodness there were some workarounds and that we could do workarounds before we had you know public fixes out but there was a lot of
clarification that we had to do a lot of hand-holding to step our customers through it and then the remediation tracking so that part was even more difficult because we would have customers and and uh dell has such a huge product portfolio they were like these are my 50 products these are the versions of the products which ones are affected when is the fix going to come so it was uh it wasn't enough to just say hey you know um Power Edge was affected they wanted to know was power as version x dot X affected and all their other products so some of the things that we learned uh with it and the opportunities we saw is
we don't have a clearly defined end of security light so we had product teams that were only fixing the latest version uh if a customer doesn't know that the older versions aren't going to get security fixes they wouldn't even potentially know that they were affected how do we get that right awareness out and the education how do we how do we pull working groups together to help those customers so definitely some lessons learned we had there the other thing that we've been learning from is uh the fun executive order in s-bombs and we have customers coming to us saying we want an us bomb right we're waiving our money in front of you we have this checklist you need to have it
we want a nest bomber we're not going to sign this contract with you so besides in the in the background the processes the tools and things like that that we're working on we learned that we can't let the customer dictate the s-bomb title who would have thought that we had to declare and have an article for our customers to talk about what the title is going to be um how do we handle the s-bomb versions how do we have a consistent response across the company how do we not look disconnected and what supplier terms need to be updated we have to have all these vendor Partners now if I have a customer asking me for an us
bomb I need my vendors to have an s-bomb we just signed a contract with this with with this vendor we didn't put us bomb in there how are we going to go and get that so a lot of learning as we got there some of the other learnings that we've learned um and these are some of the top customer security concerns that we saw with the common practices you know do you do basic VR vulnerability management things like that um do you do false positives we talked about Vex earlier you know indicating if you're affected or not affected if you indicate you're not affected they're going to want to know why uh my scanners saying that you use
openssl how do I know you're not effective so thinking about that the other thing that I've been really trying to drive is predictable security updates so a lot of people heard of Patch Tuesday right Microsoft's um you know trying to get to that our customers want to know when they're going to get the next security update and they want to know that so they could best be prepared to get that update and apply it as fast as they can they also want that update to not be with features because when you have that update with features we all know it takes longer to deploy it along and test it the other thing that we talked about a
little earlier was the end of security life what is my security support life is it the same as my standard support can I really support Security on something for 20 years right let's think about that if we have a version and another version and every year we're doing two or three versions you can end up having 400 platforms on our client side Dell laptops that we now just need to support that means whenever we have one vulnerability we potentially have to deploy it in four 400 different platforms that's a lot of work so thinking about that lastly one of the other things we've been going to ask about is what about our pii does your product
display the pii what customer data is collected what about those log files what's in the log files so learnings and drive the Upstream improvements into security practices how do we make sure that we have these security questionnaires already pre-ready for our customers how do we have that station letters already there how do we do the targeting training for sales and customer security how do we know what the requirements are from our customers and push them in how do we know to make sure that we update our sdl controls because now we have customers asking for these things on a on a common basis how do we figure out what our process gaps are from our learnings here
so basically constantly learning and learning from these interactions when we think about this one of the things that we had to do and we had to continue to do and all of us should do is educating our customers if our customers come in and say to us I'm not going to deploy your product unless I scan and there's zero vulnerabilities it's never going to happen I mean if you that product consumes an OS I mean there's five to seven vulnerability fixes a day on that OS how do we educate a customer that that's not a practical decision how do we educate the customer on coordinated disclosure the reason why sometimes it might take something longer
to fix is that we're working across multiple customers multiple vendors of theirs and we want to make sure that we're not zero daying ourselves how do we make sure that the customers understand scoring and what CVSs means and how they should figure out their risk based on their environmental factors so there's all these fun things that are seen and what are not seen in our space here so we have our little Glacier here and we could talk about what scene is the behaviors the results our actions but they don't know what's going on in the background I don't know about this rescoring that's going on the CVSs scoring they don't know about our vendor practices they don't know about my
practices they don't know about these maintenance releases there's so many things that are not seen that are underneath that you now need to figure out how are you going to explain that to your customers it's sort of like when we did the the thing with the researcher earlier the researcher had no has no clue all the stuff that's going on the background when you're dealing with this you need to do most of our customers so how does this actually build customer trust so we start off with the basics we're transparent we do our security advisories we do cves right that's a good way to start building trust as much as it seems scary to be transparent and
say you have a vulnerability that transparency is really good product pages having that information having security information having a a one-shop security and Trust page key how do you go we have this thing called my service 360. basically if you're a customer it knows what your systems that you bought and therefore it's only going to Target those security advisories for the systems that you care about how do you make sure that you have those advisories in a in a place that's searchable they can search by cve they can search by product they can search by the data was updated continuing with the building the trust is to make sure that you're constantly learning reassessing those controls we
have 62 SEO controls in Dell we take those controls there's guidance there's a maturity assessment with it but sometimes we realize there's gaps right how do we take and learn it how do we get into those governance readouts so we do quarterly governance readouts with all of our execs from the business units we're now pulling that information that customer information saying hey we had this conversation with customer a they want us to have a b and c and if we don't they're not going to buy from us anymore how do you get that visibility to the execs how do you make sure that you're investing with customer facing teams having that transparency that multi-channel notifications out there in
a better way in a in a in think about the apis that we're talking about with Vex and stuff like that that's coming down customers are going to have to handle this very quickly so we need to make sure we're improving that when we think about our customer security needs everything in the threat Landscaping is constantly changing so we need to make sure we're changing with it um so there's just tons of regulations that we have more coming how do we meet them which ones do we meet which ones can we do a phased approach to me how much money is it going to cost us how do we do artificial intelligence to to help our
customers better so many different things to think about lastly I want to talk about the business so when we started some of our uh maturing of our security practices like the security update Cadence and the end of security support we were talking to engineers we were talking to the wrong people we had to talk to product management they are the right business stakeholders now if any of you are product managers or talk to product managers if you don't talk to them in their language they're not going to pay attention to you so you need to think about profit going down about not making money about a customer not buying and bring those examples in you need to push that
customer first mentality that those product managers have and talk about how security fits into it you need to think about your stakeholders and understand the impact right so that they understand that if they don't do some of these product security practices they are not going to have those customers anymore um so the other thing that I've learned about product management is understanding your competitors uh what are they doing what are their security practices if I could sit there and say competitor a b and c is doing this and we're not that it's a solid win if I could say competitor a is doing it but not B and C it's still a good win because we could be ahead of the curve
so think about how aggressive they are with with product management and when we think about the competitiveness the sales opportunity the business impact we need to think about all of these type of things and how to get product management engaged with those customers in those conversations and hearing that pain so in closing understand your customers product security concerns right utilize it find out who handles those concerns those inquiries bring that knowledge in use that knowledge to better your practices we're all here because we want to mature ourselves our company insecurity our customers want that too if you use customers in your arguments in your push in in every conversation you're going to be better at pushing those maturity practices
get the stakeholder buy-in so think about product management pull them into your conversations and lastly don't be afraid to share your journey we may not have security update cadences for every every product right now at Dell but we're on a journey and I'm not afraid to talk about that Journey at least my customers know that I'm thinking about thinking about this are they thinking about that they're going to know that we're on a journey and they're going to trust in the fact that we've delivered a lot and that we're going to continue our journey to deliver more hey yes that was a lot they told me to be a little short so are there any questions
everybody responds to get to Jeopardy oh anyone there you go Jim
um
example of the health y it would be great but that executive order that we all love says well it's already published so we might have missed that but it says attestation and they're trying to figure out what that actually means and how to deliver it I don't know if we're going to win Jim but
yeah I agree I agree so so Jim was talking about the the word at the station and what what was your suggestion Jim what which word do you affirmation instead um but but the executive order talks about you know at the station um it's it's been a common practice but I do understand it's overloaded because it's in in health fields and other areas you have another question understand yeah
it is log freshell the vulnerability was love for shell foreign
I I agree the incident was logged for Shell however it was logged for Jay in the nightmare afterwards when they had the 2.17 the 2.17.1 where we had customers saying hey you need to be on the latest and greatest why aren't you and I'm like that's business as usual we have typical slos of how quickly we address that we're not going to stop everything I just had teams spending weeks and weeks and losing their their holiday break um so it it yes I agree I agree Jim yep
anyone else you're like Jeopardy okay thank you [Applause] I get another gift I'll take it I got one for each kid now with what's in there you might need it