PW - We removed passwords, now what?
Show transcript [en]
all right let's do this uh can you hear me okay all right uh thanks everyone for being here thanks to the bid team and uh the passw scone team uh for having me here um for second year in a row and for second year in a row also I am the one opening this track which is very good uh I said this last year but I'm going to say it again because it is still true it's very good to be the first one because there is no pressure so even if if this stock is terrible uh all the following talks are going to be amazing so um you're you're welcome to all of the following talkers so speakers so um
my name is Aldo I am the application security lead for hyper uh I apologize because I have a lot of content so I may go a little bit faster so feel free to catch me afterwards if you have more questions or if you want to go deep on any of these topics I'm going to skip the agenda and I'm going to do a quick pasis recap so as most of you know uh paskis has been growing a lot in the recent years uh just a couple weeks ago Google announced that they have passed the 1 million authentication Mark in just one year so over 1 billion authentication using pasit uh which is huge uh and as you can
see more and more companies are using pasket every day and when it comes to pass Keys we have several options to store them uh the first one being security Keys which I'm sure a lot of you are familiar with uh and then we have platform authenticators platform authenticators work very similar to to security keys in a way that the private key used to uh authenticate you never leaves the device uh this is this is amazing to me because nobody has access to that private key besides me so they have they need physical access in order to use that authenticator and lastly have we have sync paskis they work almost exactly as as platform authenticators the only
difference being that now somebody else is restoring those pasket for you uh this is great for adoption might not be great for everyone uh because some of those vendors may be protecting your pasis with a password so um you may be using these amazing pass keys that are very secure but you are protecting them with a password which uh is not ideal and of course this has some resistance um if we go back to the first two options you cannot log in from everywhere I that that is a fact so a lot of us are traveling today and if we didn't bring our pasis I mean our jikis we're done we not log in and that is a
fact uh and very similar to this point uh if your device is stolen or you lost it or for whatever reason uh is not available you're done you cannot log in but for the tier option and I'm sure I'm not the only one but some people don't want their pasis being stored by somebody else uh for the reasons that I mentioned like um this at the end of the day these are private keys and you're using private keys to uh sign a challenge so uh this again it's great for adoption but not a lot of people are in favor of doing this and we also have developer resistance uh a few months ago I ran
into this post uh which is is very good I recommend you checking it out uh it's from a developer company and they mentioned that how implementing paskis is very hard uh it's a 100 times harder than they expect it to be uh they made some good points some not very good but uh they do have some valid things and one of the things that I that they mention is that for the Eng user perspective there's really no difference uh when you use aasy and when you use Biometrics to unlock uh a username and password so to them they are simply providing Biometrics and they are authenticated to a website so they to them it's transparent right so they
don't have any incentive to move uh away from password to a pass key so if you have a chance please uh you can check this article it's has some very good points so going back to the original question did we actually remove passwords and I mean this in our company and uh well the the answer is yes we from day one we have been the passwords company and now we are the identity Assurance company but yeah we don't have any corporate passwords at all and as you can imagine this has some uh challenges when it comes to account recovery so how are you going to recover those accounts if you don't have a password if you're not using email to
recover those accounts right uh and when we look at the traditional recovery options uh I'm sure most of you already know this but uh you can use SMS you can get an email you can get a onep there are many of options you can use to recover your accounts one of them being uh calling it support and again as I'm I'm sure you know uh this could be abused by social engineering and it's it's very fun and all of these options have something in common right so they are not very secure they could be uh or not as secure as we could have hop so right so this is why now we have idb uh idb is kind of a new term but
essentially means identity verification right so uh you know it's a process of identifying or making sure that the user is who they say they are and this may sound familiar like isn't it this what we have been doing for the last several decades uh but it actually isn't because we in the past we have been using just a password right so now we're actually verifying that the user is actually the user right and what is the main thing that we're trying to solve here well verifying the user identity of course uh this could be for a number of things you know just creating a new account uh logg to a website getting a loan getting a
credit card uh we need to verify your user right something really interesting to me I didn't know and I didn't think it was possible is uh using it for interviews funny thing uh we had a customer saying that they they had a job posting and some somebody applied for this job they went through all the interviews they got got accepted uh this was person a and then on the first day of the job person B shows up and they had no way of knowing that they were different persons uh several months pass and they were not aware that the person they hire was not the person that show up for work uh so that is a very good
use case for uh identity verification making sure that the person that you hire is actually the one that is working for you and you know the the traditional uh ways of doing this uh like account recovery on boarding new users new devices and if we do a a quick Google search uh we're going to learn that there are many many vendors that do identity verification this is recent I mean uh until recently there were not many vendors that did this um disclaimer uh hyper also does this and Hyper is not even here so uh I'm sure there are even more vendors that can do identity verification for you and some examples of identity verification uh you know probably you
have been asked to provide a selfie or a video submission or even an ID like a driver's license or even verification by human uh you know just having a video chat with someone and they can verify that is you uh I don't know who's staying in this hotel but if you are and if you were asked to do online checkin you were actually uh asked to provide an ID so even now in this hotel we we were asked to provide to do some sort of identity verification and and now I'm going to give you an example so I'm I'm from Mexico in case that wasn't clear uh but uh uh we have this uh tax agency and is
the equivalent of the IRS here right so when the pandemic hit they were trying to do things a little bit faster and they were uh they set up this website which was used to identify users and then um once you were identified you were able to do the thing that you wanted to do right uh so here's the thing they were asking you to they were send you a challenge and then and then you had to read that challenge back the funny thing about this challenge is that it was coming usually from songs or poems so the end users were saying something that was very very funny and I'm going to give you a couple examples
of this uh one of them being uh I don't know who loses more in this farewell so that that is so deep uh can can you imagine this like if you're trying to log into your email and then Google is asking you to record a video saying something like this in order to verify your identity that that's very bizarre and we have one more uh the last one that desire for nothing less than you that's that's so beautiful uh again this is so weird to me and and the worst part is that this wasn't an automated process somebody was actually reviewing those videos and making the decision on whether that was you or not uh as you can imagine this
good in scale and this actually didn't work so idb has some challenges of course uh the first one being pii storage what are you going to do with all of that like where are you going to store those videos selfies IDs what's going to happen with all of them uh we know that people love to store stuff in S3 unprotected so who knows where where my stuff is going to end up right of course it's subject to fraud uh people trying to identify Pro prove that they are somebody else you have to get a new credit card a new loan stuff like that but of of course this has user friction users are being asked to do
something else that they wanted to they are being requested to you know record themselves to provide more data and do things that they usually didn't have to do uh if we have time I'm going to go back to an example but for now I'm going to skip it and again just privacy uh when you are recording videos you are you know providing where you are to these companies like if I wanted to log into some of these websites right now I would have to show them where I am like all of this environment would have to be recorded and again that has a lot of concerns and of course we have to worry about AI uh there are some websites that you
can create videos in so they can make you look like for instance right now somebody could take this video of me and then they can feed it to this Ai and then make it say something as if were as if we're me so idb has to be that challenge they have to make sure that they are not dealing with AI when they are doing some identity verification of course and in general I think a lot of companies are not taking users into consideration like uh again users really well at least me I don't want people you know having videos of myself you know with the background like I don't want them to have access to my house I don't
want to have access to my job simply because they want to verify who I am right so that is I think that is something that companies are not taken into consideration uh and I have one example for you uh this is from rer app think of it as as if if it were Uber so this is what the drivers are seeing um I want you to take a really good uh really good look at this picture because it's very subtle so you may miss it uh what's what's the issue here so again please take a good look at this picture and let me know if you if you see something wrong with this profile so um this is what was provided
to the to the drivers uh if you take a look uh it says that the security verification is good bid photo has been provided and the credit card was verified so to the to the drivers this is just an amazing Rider right they have been fully verified or maybe it's just me but uh either the person looks exactly like that or this is some sort of Fraud and they have very good rating too 493 that's that's a very good rating and one more challenge uh there are some websites that are actually selling data so you can bypass these controls so this is not AI these are actual people that are selling their data so you can bypass these controls so
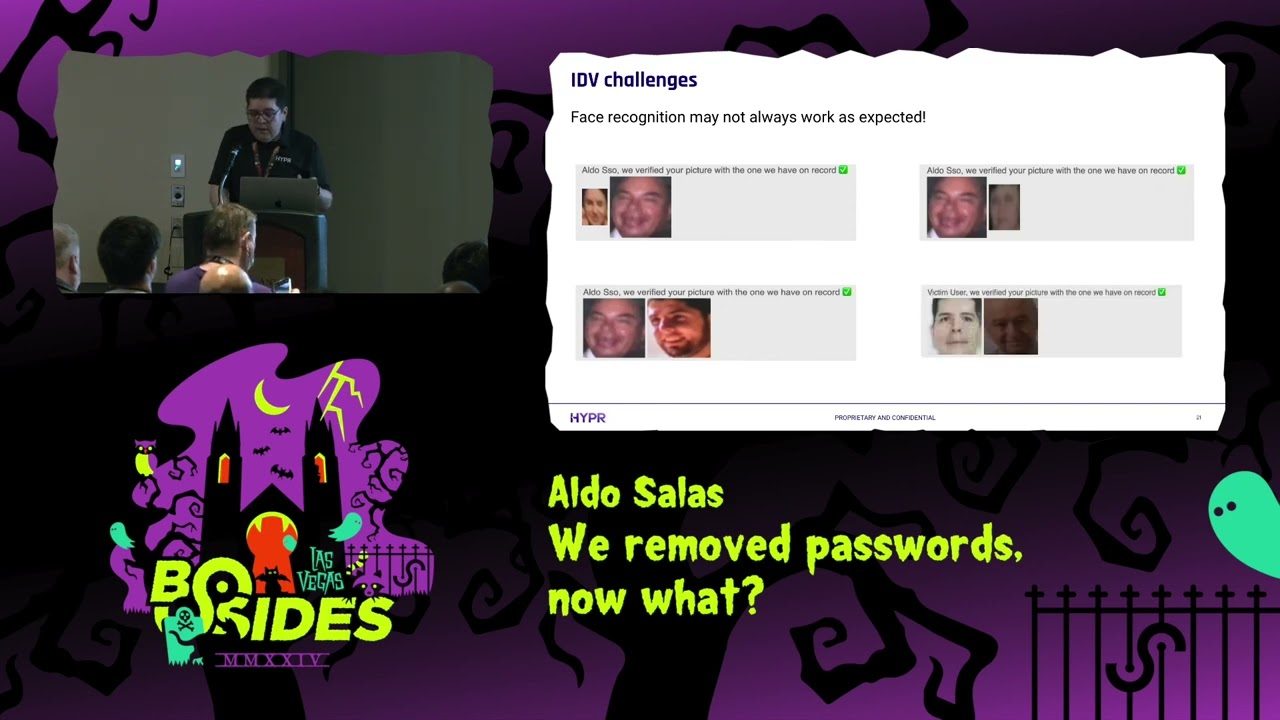
if somebody has a site that is asking you to uh provide a selfie you can go ahead and purchase a selfie instead of providing your own and of course um face recognition doesn't always work as expected uh I was testing this website some time ago and uh they were uh they had an image of you and they were asking you to provide a selfie to basically match that you were the person that you were trying to authenticate as uh and of course uh that didn't work and because clearly those those people are not the same uh but I thought that maybe I was using some pictures that were not as good you know they have bad quality so uh I try a few
more and the application was always saying that the the person was the same then I try using one of my pictures I say well I'm going to try mine maybe one that is not so blurry and as you can see I am an old person I was verified to be this same dude uh so I think what happened here is what the application was not doing negative testing right so they weren't doing some matching and for some reason they were always saying that the person was verified when it wasn't so now I'm going to give you a quick example of what we're doing uh just so you know what you can be doing with idb so what we're doing internally is
that we start the recovery Flow by asking the user to provide a valid uh username right so you need an username then we ask you to provide your phone number and then you get an SMS code so I know that I said that SMS are not secure but this is not used for authentication this is just this is just a data point right and then we ask for location check uh you can decline it of course but we're just going to show at the end that you didn't do a a location check then we ask for your ID and then we do some facial recognition and if all of that weren't enough we also get you in touch
with your manager so you can do a quick chat and make sure that uh the manager reviews all of this information and then they can ask you more things if they want they can say uh they can approve it and uh I think if somebody is able to actually pull this off like if an attacker can do this uh you earn it like have it you know you can have my ju if you want like if you can actually bypass all of this yeah you did a great job so um this is just one option that how idb could be done and of course this is configurable you can remove things if you like or add
more so what is the future of idb right uh I think it's safe to assume that it's safe to assume that idb is here to stay uh just as I mentioned when I was checking in I was asked to do some sort of identity verification and last year uh that wasn't the case and I think one of the drivers is just moving a lot of physical teams to the digital world and it's very convenient because you know checking into the hotel took me less than one minute you know I just I just pick up my key and that was it so uh it's very convenient but it has a lot of challenges of course um but you have to do it uh in
some sort of automated way uh as we saw in my previous example if you don't automates um it's not going to scale it's not going to work and uh it's not going to be good and I don't think this is going to end completely end social engineering but I think it's going to help uh again if we go back to this example uh if somebody can pull this off you know uh you earn it go for it dude uh and lastly I have some main recommendations for you uh I I think the main recommendation would be to make an idb part of your account recovery process uh you know it doesn't have to be as uh you don't have
to ask all this many data points but at least right so if you do this you're going to uh help reduce the account takeover uh percentages and you're going to make your account recovery process more successful one thing that I do want to mention is that doing idb is really hard as you have seen uh so if you're going to do this uh I recommend going with a partner and I'm not saying hyper you can choose whatever partner you like but there are countless legal issues you know there are specific regulations uh for not just for pii but there are lots of rules and legal issu isues so if you're going to do this I think it's
going to be best if you find one of the many partners that are there uh that already provide this and do this in very different ways and also do negative testing right not just the happy pad uh in the example that I show um on the face recognition part uh they were not checking the bad face recognition so always do negative testing and of course go passwordless uh if you can uh doing going passwordless is going to reduce your account cover by almost 100% so it's always a good idea even with the challenges that I mentioned at the beginning uh I still have some time so I'm going to go back to my example just
to uh let you know what I meant by the user friction there we go so uh I have this Bank uh this credit card that uh requires me when I change phones it requires me to do identity verification again uh so it was the middle of the night I wanted to purchase something from AliExpress in the middle of the night uh I could do it because my credit card was blocked because I had to do an identity verification one one more time and that's something I'm not goinging to do honestly like it's the middle of the night everybody's asleep I just want to buy a $2 phone phone case from China I I don't want to have to do this in the
middle of the night right uh so I again I think banks and you know companies in general are not taking users into account uh they are adding a lot of friction so in order to for this to be successful they have to do it uh more gracefully you know making sure that they are not adding friction to the users and I think that's it uh yes that's pretty much it uh thanks everyone for your time uh I do believe we have time for questions so yeah if you have any let me know thank [Applause] you questions raise your hand
hi I was curious um how is this uh the facial ID and the the video voice any of that stuff how's that with with the continued advancements in deep fake uh technology how is that safe from those things right so um let me go back to that slide so you're talking about this step right here right so that is a very good challenge um idb companies have to be you know it's going to become a mouse and cut game so the idb compan is going to have to be they're doing what they call a liveness check to making sure that it's you and yeah I agree it's a challenge so idb companies need to stay
on top and need to be constantly evolving to identify those things that is a valid concern yep all questions uh do any idv companies like have like an audit Trail can you will they talk about the accuracy sensitivity and specificity of whatever set of these steps they put together um well I I cannot speak for other uh but we do so so yeah I I I cannot speak for other companies but yeah any else so just a quick question uh you mentioned about Pass Key storage and uh you talked about a lot of the password managers um and how they're protecting that with a password which is kind of counterintuitive yep what would you say is a solution for secure
password storage or pass key storage excuse me um you know particularly when some of those vendors use like multiactor authentication and such I think that's going to depend on your on your use case so for me I use security Keys that's that's for me like I know how I am storing them I know where they are for me that is what I do so that's going to depend on how uh convenient and how secure you want them to be right so you have to put things into a balance so if you want to go with sync passys and you want to be able to log in from everywhere uh you're going to have to accept that you know uh you're going to
have to accept that that can be accessed from somebody from some other location so right now that's that's the best thing that you have so you have to make that decision for yourself okay thank you Aldo and a round of applause for him of course thank you





