PW - Password Privacy Keystroke Dynamics - Per Thorsheim
Show transcript [en]
coming later on I don't have the script so I'm just going to say uh you know have fun andjoy and do ask lots of questions for our anything else I should say that I have got mod already no I was exced so again okay I'm 44 years old and playing with computers since I was 10 uh I've been researching having fun tracking trying to improve the security passwords for more than 16 years and as years passes by I think that I'm learning more and more but are still incapable of understanding why passwords still haven't improved in all these years uh a long time ago I was actually military police in Norway so uh again you know there's nothing you can say or
ask me that would offend me you know give you Me Your Best Shot go ahead please do ask questions and the way I do only have 25 minutes I can talk usually for 4 to 8 hours without stopping at all but I will try to keep down to 25 minutes that I have a lot for myself uh this is something that um came about to me many years ago um there's a u there's a university college in Norway at place called Yik um they do a lot of research into Biometrics and what's called Behavior uh Dynamics and B Biometrics and there are two professors there pck and and kof and they have pretty much uh challenged
me earlier you know on the topic of passwords being dead passwords doesn't work anymore and we have all these great uh biometric solutions that we you know really want you to you know learn about understand and you know feel free to try to break them crack them circumvent them byp pass them and so on and I've been thinking about that for quite a few years uh you may have seen this uh know like during the past couple of days uh there have been media reports coming out stories coming about about some really nice research from France and these guys have been looking into using canvas information from your browser to look at the battery status of your
laptop and specifically they've been using uh Firefox on Linux and they have found that based on that uh they can on the server side they can see the battery status of your computer and basically use that as a very crude way of tracking you and separating you from other people visiting the site even if you have turned off ad blocker and ghoster and other uh you know anti-tracking uh mechanisms that you might have in place so it's kind of fun and this really have made headlights but still this is still this is you know tracking your computer tracking your browser tracking your device what I'm going to talk about is Biometrics where we are tracking you the
human being typing on the keyboard uh walking running singing speaking with your voice stuff like that and basically Biometrics are put into two categories now you have the physiological Biometrics which can be your face fingerprint hand ey SC even DNA which should be uh I guess pretty well known to to everyone um if you have seen the announcements for Windows 10 if you have installed Windows 10 already you know that Windows 10 now also supports the use of face authentication you can actually just sit down in front of a Windows 10 laptop be identified automatically by the camera and be load de and not only that but latest technology here in Windows 10 is actually using two cameras on the laptop
one of them being infrared so with two cameras you have a 3D picture so you can no longer hold up a picture in front of the camera and get load in and using infrared they will also see that you have no heat in your face proving that you're a human being so what we have to do to defeat this is of course to build ourselves a latex Mosk and put in some electricity into it as well put it on your face and heat it up and suddenly you may look like you know something like that to L on you have a traditional fingerprint which is used everywhere you know iPhones uh you have hand recognition and
this is not logging patterns but this is you know just the way your hand looks uh you have the iris scan and if you talk to researchers into biometrics will say that well the main problem with using Iris scan is actually Tom Cruz that's the main problem with Iris Dan and why because people have been watching way too many Tom Cru movies where they will in the future use a Prett red laser to stand and swipe over your face to recognize your iris and everybody who is say to their brain will understand that put a red laser onto your eyes can actually be dangerous so Biometrics professors they will say that iris is usually by most of
them considered something that cannot be deployed with normal people because they are afraid they are going to get their eyes scanned with a red laser but what you're actually doing is is to use a normal camera to take a picture of your eye but that doesn't look cool in a science fiction movie and then you have DNA and my topic is in the behavioral part of Bix which is basically you know how you behave how your voice sounds like and in this presentation keystrokes how you type on a keyboard and this is pretty cool uh there are many things you can do with this as an example when you set up an account for a
website you could be using behavioral Biometrics to create a biometric profile of how you type in your username and password and that could be done using as an example JavaScript cide JavaScript in your browser and they will build a profile and send the data over to the server andore that and using small threshold values each time you log in you will be typing in your username and your password a little bit different from time to time but not exceeding the threshold values so basically you have to two Factor authentication but the only thing the an user sees is typing in username and password one factor authentication if you want this also identifies you the human
being not the browser using Tripes as an example and you can even use this to you know identify people visiting your website even without them having to type anything because you can also do behavioral biometrics based on how you use or move the mouse across the screen and these professors in Biometrics they will also tell you that as soon as you have used a finger to swipe across your screen you know your picture gallery on your phone four or five times they already have enough data to start creating a profile on how you actually swipe across the screen four or five swipes across the screen they have a basic profile so you have the keystrokes you
have the mouse movements you eventually also touch on a screen with Force touch from app now you know they are kind of detecting you know how hard are you pressing on the screen that can also be used to identify and I also learned that when we do touch time we can essentially set up a keyboard in another room here tell people to go in and start typing on the keyboard and without knowing anything about the people going in there we don't even know the gender as soon as they have typed Seven 8 nine maybe 10 keys on the keyboard we have sufficient data to tell you whether it is a male or female typing on the
keyboard because here is actually a distinct difference between how men and women type on a keybard we can do an enrollment process of this you know like you know we're now going to build your you know biometric profile and you will do that on account setup and for the demo sites where you can try this out yourselves on the internet the process is going to be like you know 8 to 10 minutes to finish but you can also create this profile over a longer period of time just by registering how people do you know normal stuff on any kind of website it takes a little bit more time but you can build the profile that way
as well and even cooler you can actually turn this into continuous authenication if you use a fingerprint it's basically you know you authenticate yourself now and one second afterwards we don't know if actually you behind the phone or the keyboard or whatever you're using but with behavioral Biometrics like keystroke Dynamics we can continuously check to see if it is you typing on the keyboard so if you hand over the keyboard to somebody else or for some reason you start just typing everything using your pinky finger on your left hand then suddenly the computer will lock up you can't do that the software already exists now how can we do this use this for bad purposes well basically you know look at
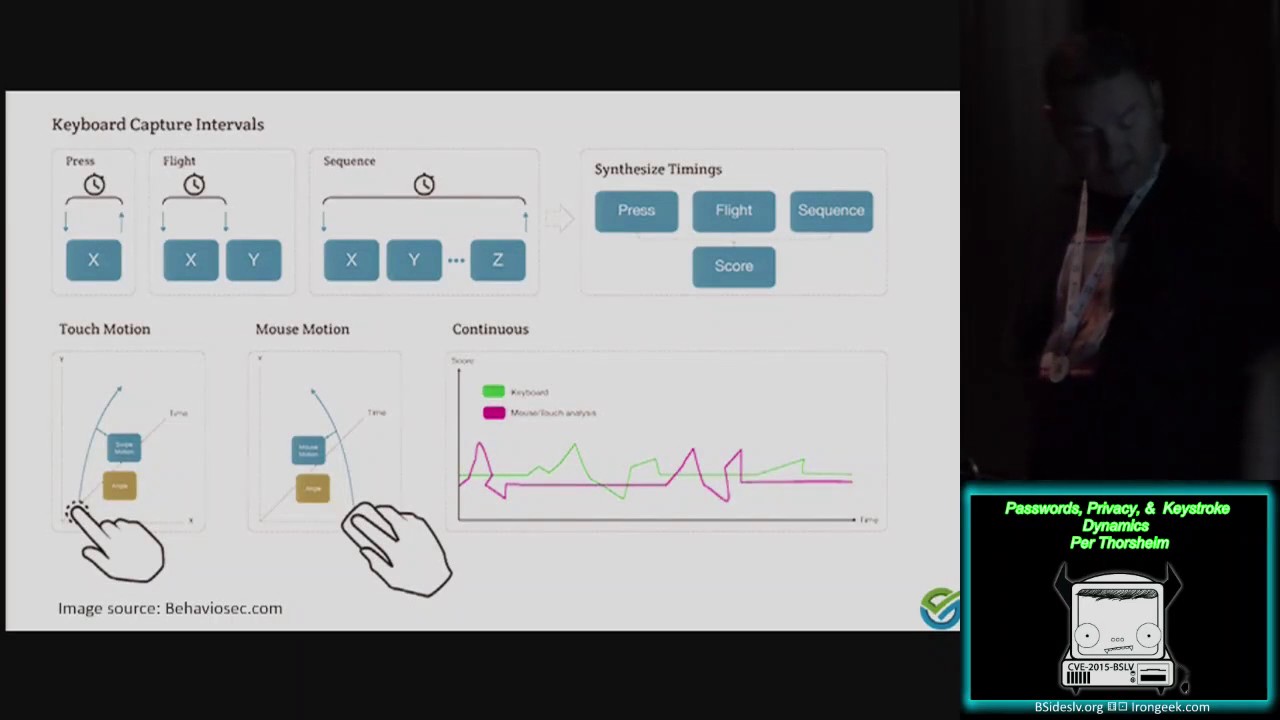
the left column and you know use your imagination here I will get back to you examples on this basically for KYR Dynamics and this is from Behavior site it's a Swedish startup company and their software is good I know I have no problem recommending their software because I like this technology Back At passord Con in 2012 in Oslo I had a professor from Ancon in France talking about this and I specifically asked him can you can you can you set up a website for me where I can set up an account for myself and try out this technology you know I would just type in a US name and a password and you will use that to build a
biometric profile and then I can you know give away my password to somebody else and see if they are able to log in and most probably they will F because they can't take F the exact same way as I do so we are looking at you know how for how long do you actually keep uh one button pressed we'll also look at timings between key press one and key press 2 you can also look into a sequence of keypresses and there are all selling as well that may be used um at this laboratory at in France you actually have a piece of software that you can download and try out for free I do have the link on the bottom and it's
like you know it's it's a demo software where you will set up password as or whatever password you want to try out and you will type it
in here I have
selected on this one I'm using password and here you can see the normal pattern and I did on purpose put in very short time period between two key presses and it's like milliseconds still you can see the graph don't no completely Haywire I do have the software on my computer afterwards somebody wants to try out and see if they can type exactly the same way as I do you know uh feel free to come up the TR and give us a
dve so examples of how this can be used for purposes one of the challenges that we see for you know forensics for governments government agencies as an example police is to identify identify people that are trying to stay Anonymous as an example using the tool Network and what we could do if we want to identify somebody on the tool network is basically basically to set up a website that we will low people into they will use most guestures maybe they will type something into that website register for an account uh search for you know wees or or drugs or whatever and we will build a basic biometric behavioral profile of how they type on a
keyboard and then we will also set up a website on the normal internet where we are able to identify IP addresses domains ASM numbers you know the use tracking could be browsers so on and we would put that that up as well as a fake side trying to see if we can get the same people that registered for an account on our you know fake tool server to also set up on this server and based on the biometric profile nothing related to IP addresses the use of tool any specific browsers anything like that just based on how you type we could be able to identify people across the tool network and noral internet as an example
now this could be useful if you work for the police as an example this could be really really dangerous if you are based in some kind of oppressive regime and you know you know you want to do good in the world and the government wants to identify you stop you eventually prosecute or kill you this could be really dangerous I have to say that when we this story came out last week in the media uh uh the response from the tool project as an example they were not too happy about us releasing this information because I'm got to be honest we we didn't actually think about uh uh telling the to project about this before
we release the information Behavior Biometrics can also be very interesting for the advertising people out there basically because as an example instead of identifying the drower which is become increasingly hard because we're using aders they could be looking into uh how you behave instead how you type on a keyboard can easily identify whether it is male or female trying to do a search on a search engine as and there's also the insurance claim and only Recreation problems of this somebody watch the time for me please um it could be something as simple as the bank or the credit card company will tell you that you're not allowed to share the PIN code or your Visa no
called with your wife your spouse kids number I don't know that would be a violation of the ual license agreement but today it will be very hard in the court of law for the bank and insurance company to prove that you actually share that information with somebody else with behavior Biometrics they will be able to see if it is you or your wife or your kids or somebody else logging into your account of course for man purposes that can be a good thing if somebody's logging into your bank account and you didn't give them access this is a really good way to detect thr attacks and to block them but it's basically also like saying
that you know you have bought a car and you have car insurance and one of the license agreements uh there says that well uh you're paying a very low premium for this insurance because you have agreed never to allow anyone the a below the age 25 to drive your car now if for any reason one day you should happen to do that imagine then what could happen if the insurance company suddenly was able to prove that yeah we know somebody else drove the car it could be a good thing but this can also have great implications for privacy and then there's the issue of password paste as many of you have seen especially those really interested in
passwords we have seen over the past year at least we have seen more and more cases where people like you know me and others it's not Troy hon Australia just to mention a few uh Paul Mo Chris M in UK have in many many cases went online on Twitter and asked asking companies why do you prevent us from using a password manager why do you prevent us from pasting in our passway into the passway field and response from every single one has been complete BS didn't make sense at all stupidity from one end to the other here you go could this use how they actually doing his dynamic for your password there are companies that are specifically making software to
harden password privacy by adding behavioral Biometrics to the password and only through the password because that doesn't change that could be a reason for why they block password P but what is the problem to us then with you know blocking password PA well there are waste circumvented of course but the point is a very important point if your password is constructed the way it should be like 70 plus characters all randomized I'm pretty sure you don't want to type that in manually for the bank or insurance company to be able to build a biometric profile so basically you will be pretty much forced into going back into you know using re crap passwords that are as short as possible
that could be a consequence of applying this specifically to passwords as an
example we uh together with Paul Mo in the UK um I conted I've talked to Paul for a couple years and this is actually two weeks ago I was sitting up late in the evening talking to PA or Skye and I do as I do a lot of my time in late evenings I talk to people and since I can't do any programming at all I can't even do Hello World 5 minutes excellent I can't even do Hello World in basic anymore 64 I tend to ask people you know would you like you know would you like a fun side project that you can play around with during the evenings and I I can't pay you any money but you know
if we ever meet up I can you know I could get you a Cofe or maybe a small saw something and and and and Paul said oh yeah that would be great thanks so I said well here's the challenge I have these you know biometric professors back in Norway and they are like you know in a in a good way seriously pissing me off with this behavioral biometric stuff and I going think you know how can we defeat this and my initial thought is well I have to type in you know my password in the exact same way all the time so it won't be able to you know they won't be able to build a know a profile
of me and even better I was actually thinking about you know H I have to build a Lego robot to place above my keyboard and I would connect a second keyboard to that Lego robot and I will type in something that I write on my keyboard and the ler robot will type that down onto the keyboard again at a constant pace so there will be like 30 milliseconds between each key press period so anyone typing anything will look completely equal and that's the basic principle of using a tool browser as an example all the browers look completely up the same way and I talked to Paul about this and he said well what if we
randomize it every time instead so it won't be it won't be possible to build a profile and it won't they won't be able to build a profile and they won't be able to verify a profile ever so that makes that's basically what Paul did and the proof of concept Chrome plugin for this was one line of JavaScript and that plugin which you not can find in the Chrome Store is called keyboard privacy it's completely for free and basically what the plug in does it will receive all the key strokes you sending into the computer and then it would cach them for like couple of milliseconds the default Wes on to do randomization between 0 and
50 milliseconds before passing the keystrokes onto the do into the web page that you're typing it into and based on that at the different websites we have tested we have seen with our pluging that we have gone from 99.98% certainty of me typing down to 0.01% certainty of it being me talking on my keyboard the plugin is available now it's been for out there for a week There's a new worship most probably coming out today or tomorrow I'm going to talk about Paul he's also working on a Firefox version of the plugin and we have per site uh possibility of you know disabling the plugin because in many cases you want to use his Dynamics if
you are using Cognito mode in in cognito mode in chromas example you may not want to do this uh if you're using the tool network if you're using the tool browser obviously you want to stay Anonymous and I'm really hoping a tool project will incorporate something like that this into the Brower CRI quick name uh keyboard
privacy and that's basically what I wanted to talk about in this presentation um is it's really fascinating the behavior SEC and most of the other windows doing this stuff are using JavaScript if you're using a tool browser you have to enable JavaScript for this stuff to work but basically there are quite a few websites you cannot use at all without enabling JavaScript as well and detecting whether web page is actually using this technology according to PA looks very very hard to do if not impossible because there are so many way St and as soon as we put this out on Twitter we also re receive world again from the guys in France that also did the battery
research telling us well in HTML 5 their options available that allows you to do this biometric profiling using only HML 5 so if you want to block it like okay so what are you going to do so you talking about the end of of privacy here but we most certainly have some challenges ahead of us so the next information of password scone is going to be at University of Cambridge in the UK uh it's going to be three full days it's going to be part academic meaning we are looking for academic research academic pays to be submitted uh the cfp there ends actually in less full weeks on September 1st and for normal cours like I done now you
know without an academic paper to go uh the CP submission date is October 15 so I'm really hoping to see lots of submissions for page as well um I've been told that um we will most probably do an evening dinner one of the days at Trinity College which is the university college in the world with the highest number of Nobel uh Prize winners in the world and we're going to do it at Trinity College which uh as I'm told uh will remind you quite a lot about Harry Potter that's going to be really really and that's basically what I had to say uh contact details and everything uh is up here uh video recordings will
be online hopefully in couple of days maybe a week or two you can find me on Twitter you can find me on LinkedIn on Facebook I I even use phone uh still if you want to call anything yeah it's old I I I don't do faxes anymore but that's basically it uh thank you for coming to listen to my talk and we'll have a very short break before the most wonderful guy Jeff from AOG bits the uh PR one password is going to do the next talk so thank
[Applause] you go get





